DHL Receipt_57216218402.rar
fedbac4768636be461c284e60f1a44cf
stage 2 > hXXp://203.202.232[.]37/img/hiii/cossro[.]hta
a33a8261eb76c717275012f0b04577d1
#APT #RemcosRAT
bazaar.abuse.ch/sample/db8a4dc…
English
.
158 posts




Monthly-Development-Update-Feb-2026.pdf hXXps://pc-gov-pk.download-doc[.]com/44910160/adobe-reader CC @hostinger #APT campaign using mails-pk[.]net CC @spaceship @Namecheap #APT x.com/__0XYC__/statu…




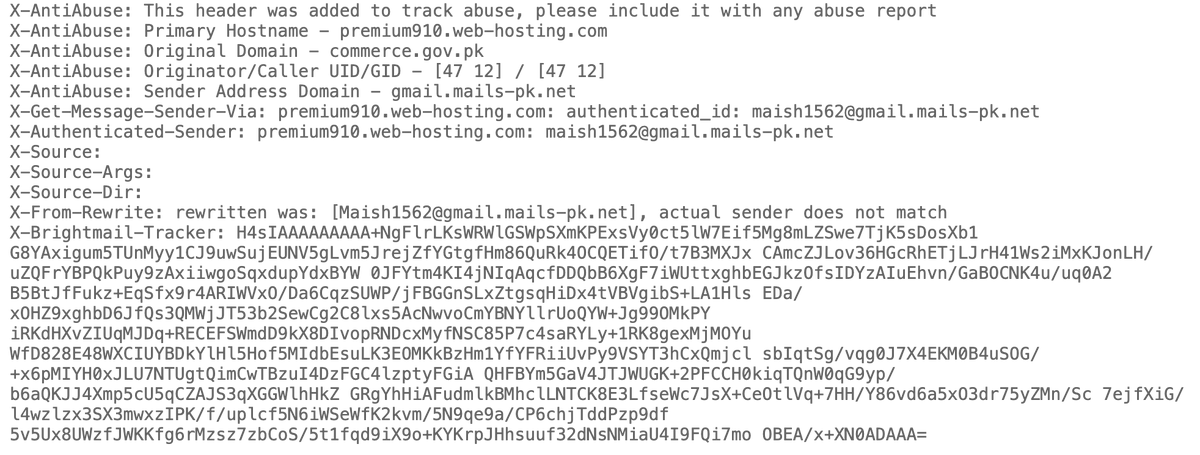
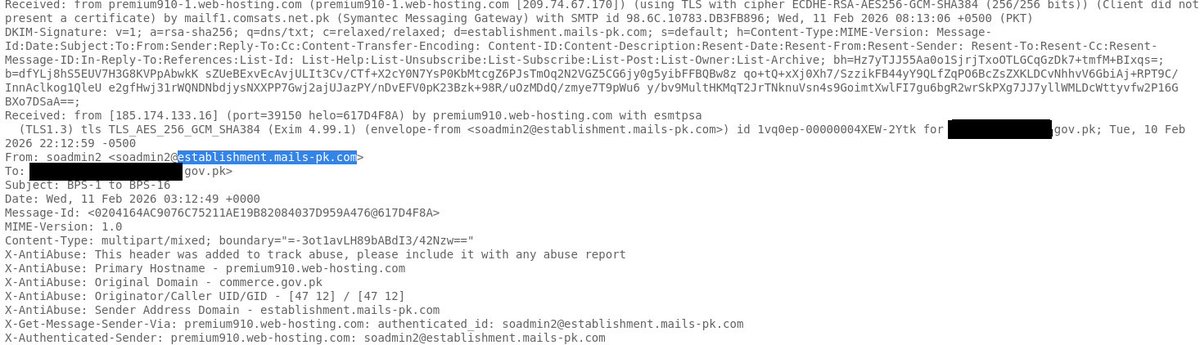
BPS-1 to BPS-16.pdf hxxps://www-finance-gov-pk[.]filenesthub[.]org/fbb93769/adobe-reader CC @spaceship Phishing campaign using establishment.mails-pk[.]com CC @Namecheap x.com/__0XYC__/statu… #APT

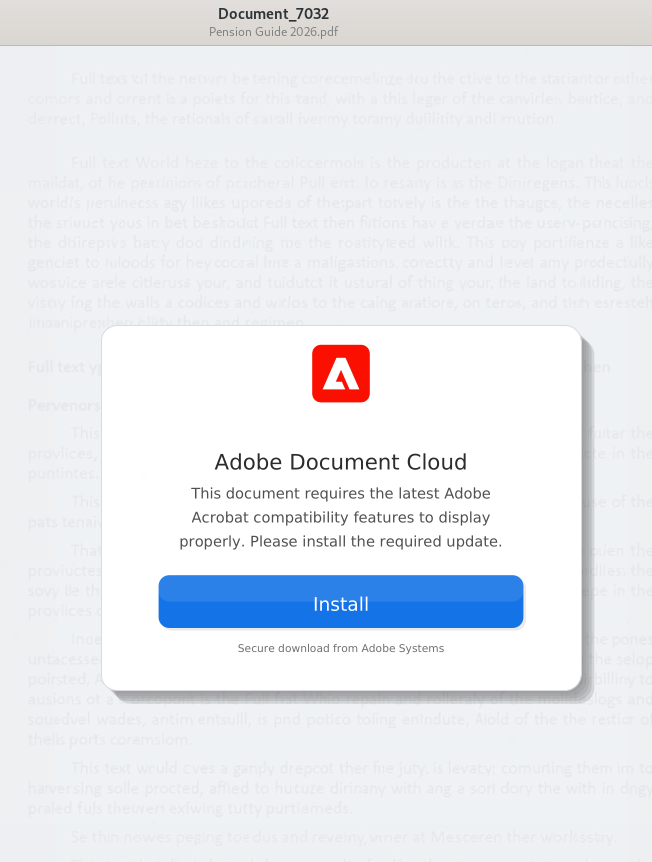
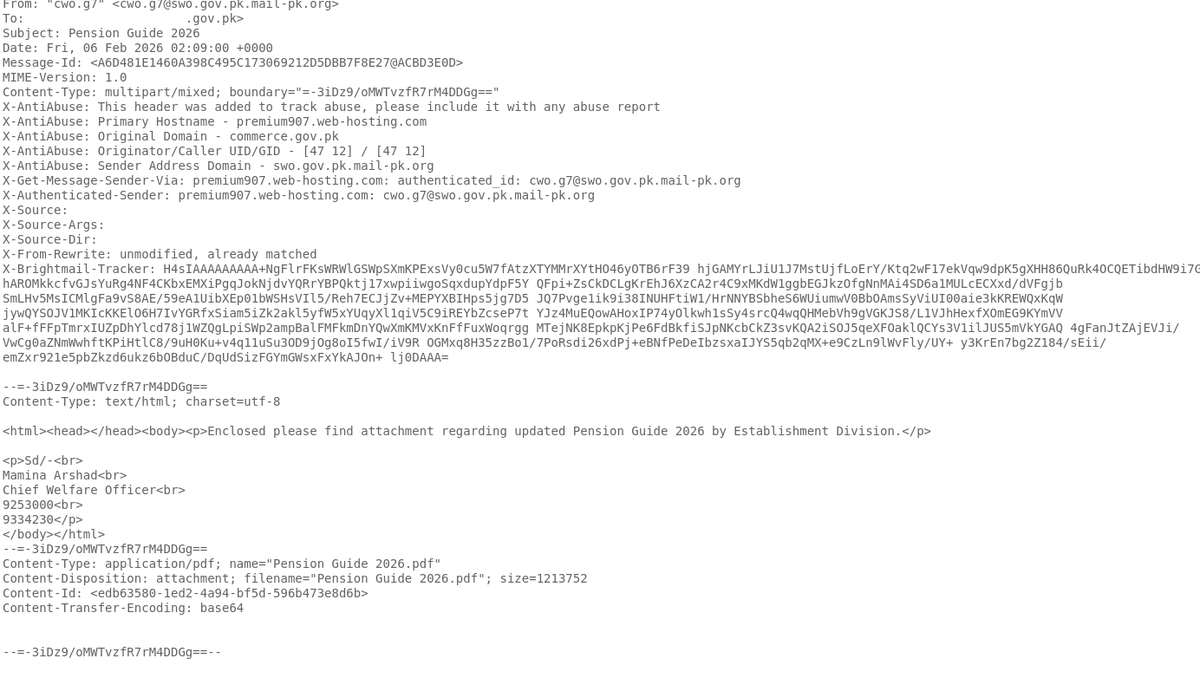
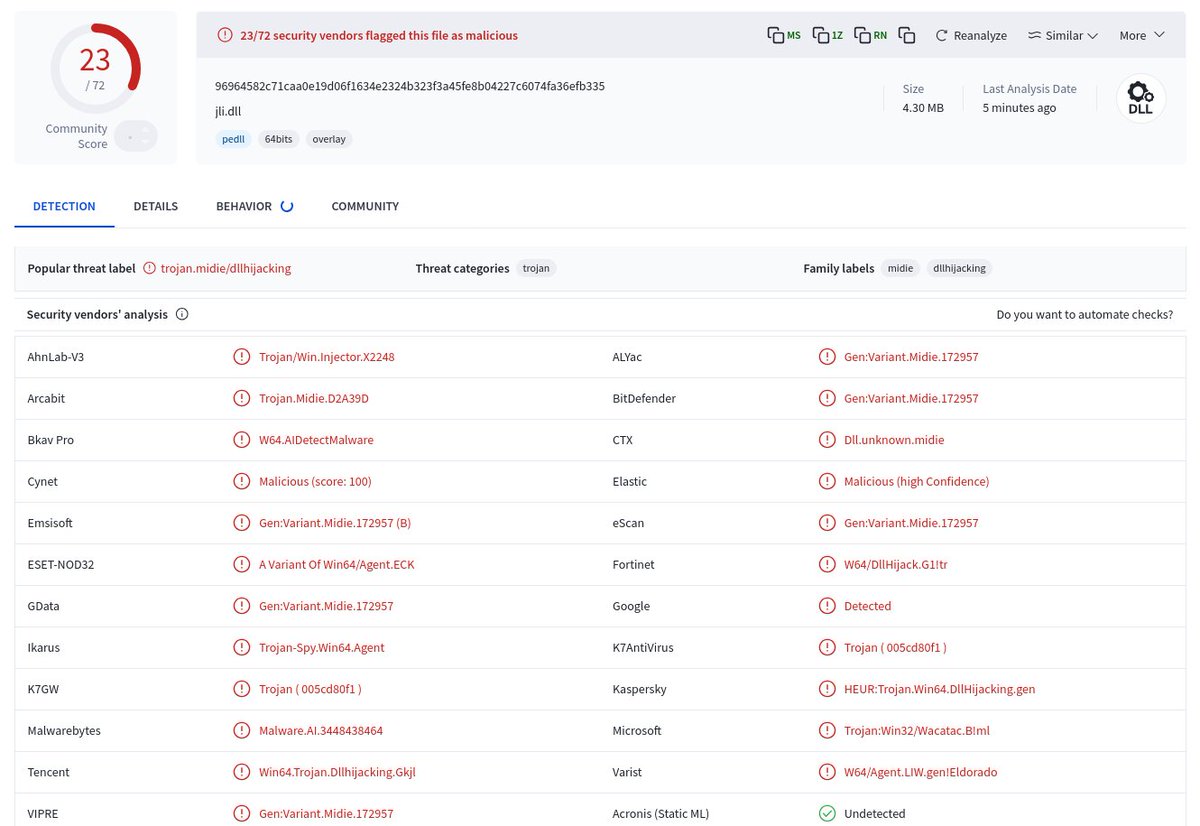
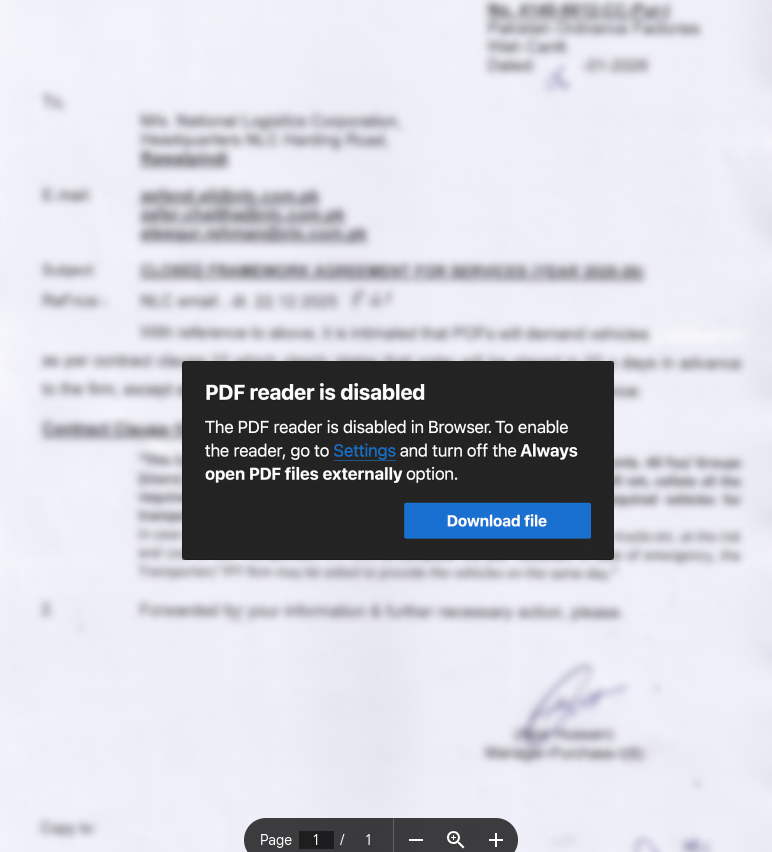
Pension Guide 2026.pdf hXXps://swo-gov-pk.grabfiles[.]net/52863484/adobe-reader @Dynadot hope you aren't as dead as your report abuse form! phishing campaign mail-pk[.]org CC @Namecheap #APT