alexmiller.eth
4.1K posts



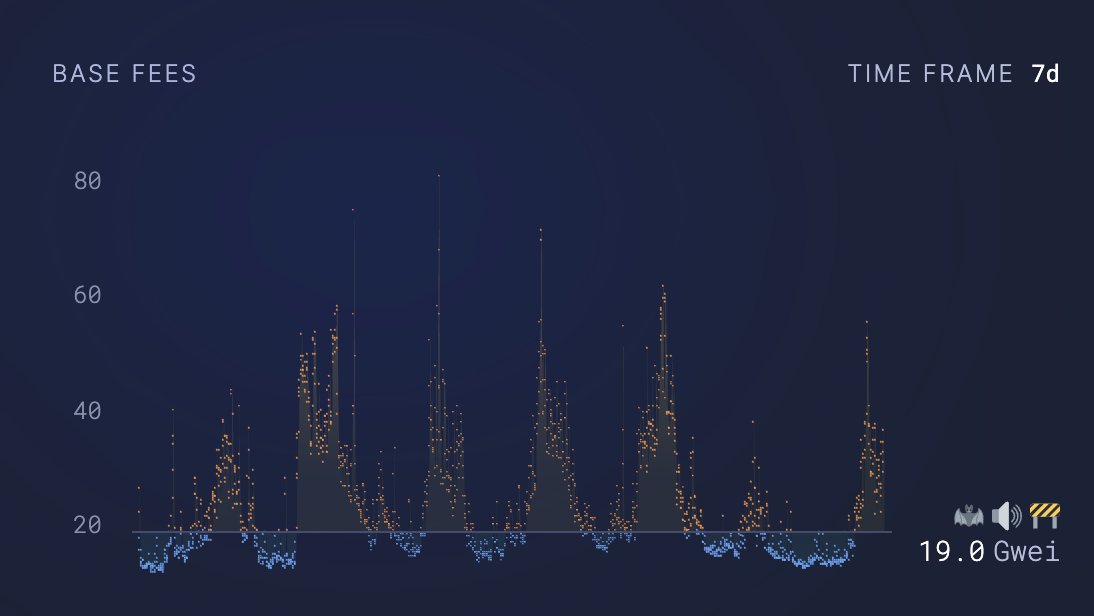
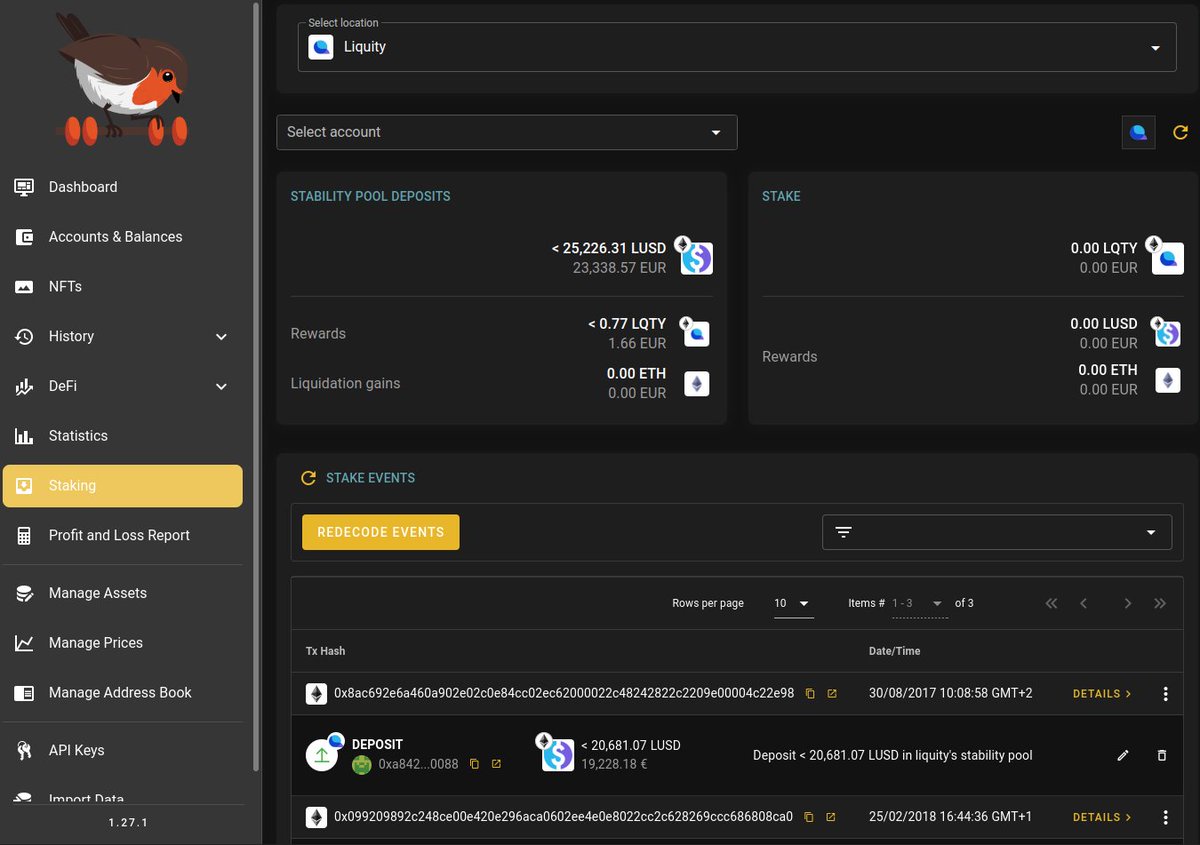
Today we reduced the memory requirement of Geth during snap sync from 14GB to 2GB (benchmarks still running, numbers might change a bit). #golang #Ethereum Behold the epic change that made it possible...

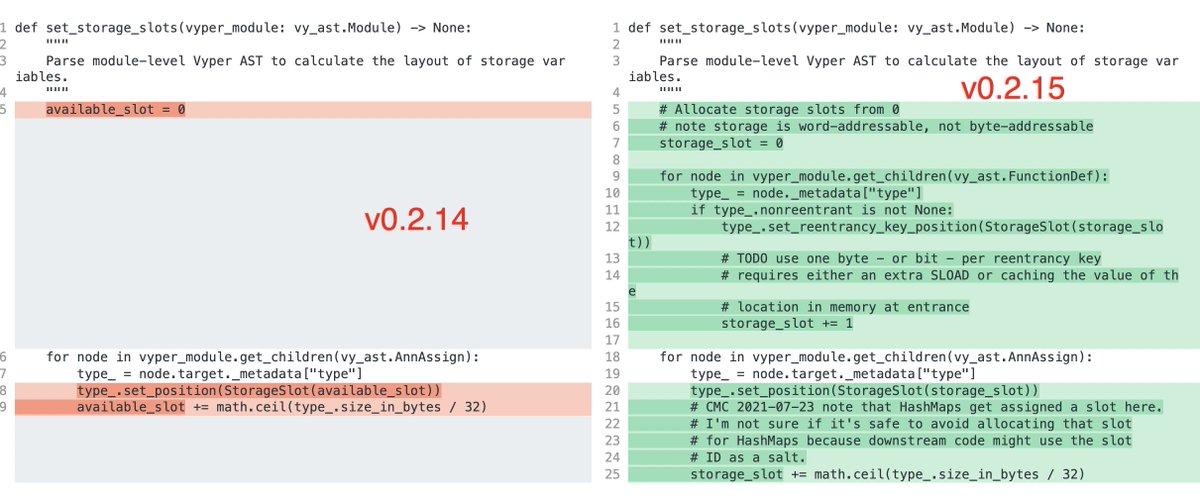
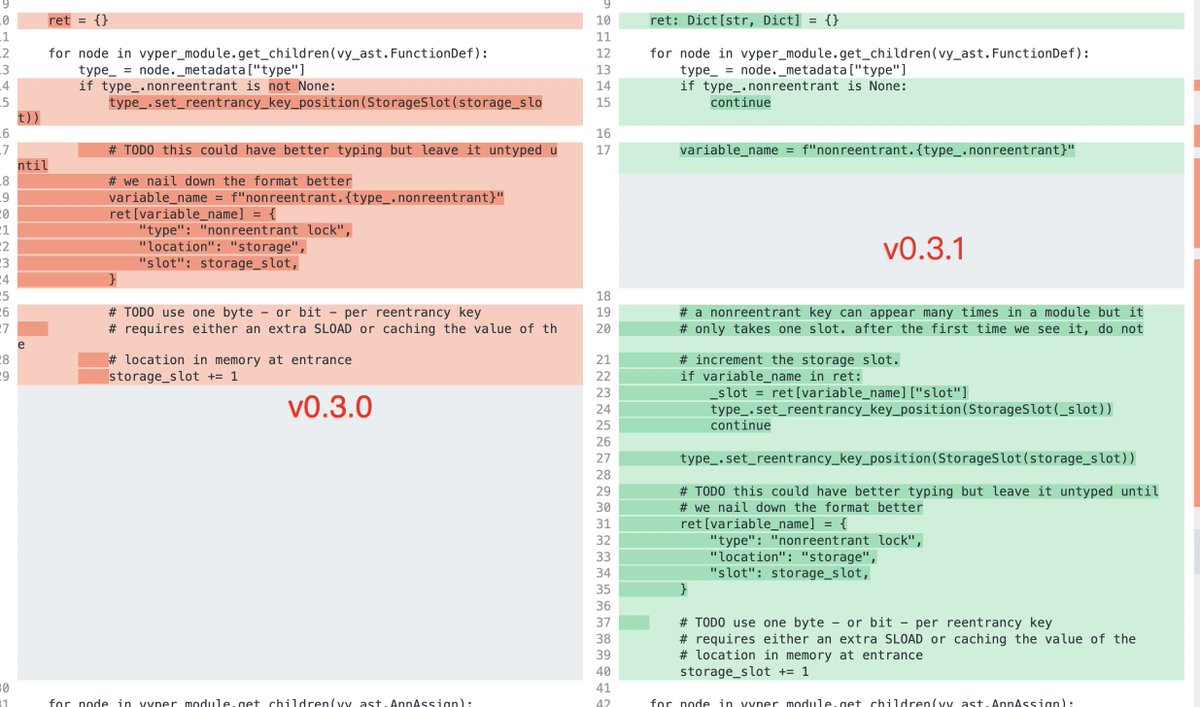
A number of stablepools (alETH/msETH/pETH) using Vyper 0.2.15 have been exploited as a result of a malfunctioning reentrancy lock. We are assessing the situation and will update the community as things develop. Other pools are safe.

Thanksgiving, November 22, 2001: Creed does the halftime show at the Cowboys game
gm Starting from today, this is how much interest you'll be paying on a $10K loan.
Effective June 19th, at 14:00 UTC. major changes are set for Stability Fees and the Dai Savings Rate (DSR) on @MakerDAO In our blog you can find all the information and suggested steps if you own an affected vault or want to deposit in the DSR. blog.oasis.app/major-stabilit… Read on 👇


So our community noticed that @uniswap may have plagiarized @shellprotocol. I’m not mad, just disappointed. Uniswap’s actions point to a looming problem in web 3. I’ll explain what I mean, but first, let me go over some evidence:
in uniswap v4, you have to mine a specific hook deploy address that contains your desired config stored as bit flag at the beginning of the address. even though it saves on gas, this design sounds a bit cursed.