Alex Hanley
1.8K posts


Alex Hanley
@ap_hanley
Hang gliders and high explosives. Bitcoin power tools at @FrostsnapTech and @HardBlockBTC



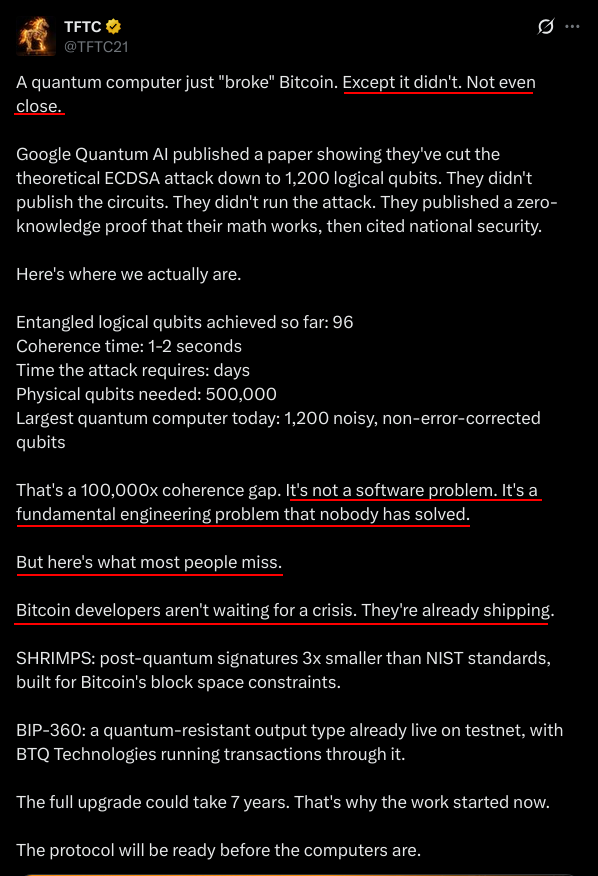
Trying to manage a potential bitcoin price crash by introducing spending restrictions (Hourglass) is such a ludicrous idea. Bitcoin routinely crashes 85% Including all the wash trading and shitcoing fuckery global trading volume is 1-5 million BTC per week Assuming only 10% of that is legit fine its 2 months worth of Bitcoin sell pressure. Even if a quantum attack was somehow going to market dump the stolen/unlocked/cracked/whatever bitcoins on exchanges (LOL GOOD LUCK WITH THAT) it wouldnt be a big deal







Today, Google Quantum AI published a research paper that might boost the post-quantum migration. Their team has tailored Shor’s algorithm to solve the 256-bit Elliptic Curve Discrete Logarithm Problem. ECDLP is the hard mathematical problem that secures ECDSA: the signature scheme underpinning most blockchains, TLS certificates, and countless authentication systems, using fewer than 1,200 logical qubits and 90 million Toffoli gates. Translated to hardware: fewer than 500,000 physical qubits, executing in a few minutes. A few minutes. Less than a Bitcoin block time. Less than two Ethereum epochs. The long-standing argument that public keys can simply remain hidden is now moot (In fact, it has always been x.com/P3b7_/status/1…). What exactly changed Shor's algorithm has been known since 1994 as a generic quantum approach to factoring integers and computing discrete logarithms. But "known" and "practical" are very different things. The real progress is in the engineering: how many qubits and gates you actually need once you compile the algorithm into a fault-tolerant quantum circuit. The last breakthrough by the INRIA Rennes team required ~2,100 logical qubit count for ECDLP. Google's engineers optimized the full circuit stack to ~1,200 logical Qubits. The recent algorithmic trendline is clear: every 12-18 months, the resource estimates drop significantly. And these are pure algorithmic gains: they compound on top of hardware improvements, which remain a major challenge. However, as of today, we're still far from having such a quantum computer. This didn't change. Zero Knowledge Proof Here's where it gets interesting. Google chose not to publish their optimized circuits. Instead, they released a zero-knowledge proof that their circuits achieve the claimed resource counts. We have no doubt they know how to do it, but no clue how (sounds magic ;-)) The reasons are likely multiple: competitive advantage, national security implications, or simply not wanting to hand a blueprint to adversaries. Regardless, it establishes a powerful (and elegant) precedent. What’s ironic: Google's ZK proof is not itself post-quantum secure. What’s next? The good news is that we already have the tools: Post Quantum Cryptography, now we need to migrate. A few days ago, Google announced it is targeting 2029 for full post-quantum readiness. NIST plans to deprecate RSA signatures by 2030 and disallow all legacy algorithms by 2035. Most organizations haven't started their cryptographic inventory. Major blockchain protocols are currently discussing the path forward. Cryptography exists to create mathematical trust in the security of systems. That trust is now being eroded, not by a working attack, but by the increasingly credible prospect of one. In security, the moment you start doubting the foundation is the moment you should be rebuilding it. What this means for blockchains For blockchain ecosystems specifically, the threat is central. ECDSA on secp256k1 (Bitcoin) and P-256 curves (broadly used elsewhere) is the cornerstone of security. Unlike traditional systems where you can rotate certificates behind a corporate firewall, blockchain migration requires coordination across decentralized, permissionless networks. This process will likely take time. I'll be diving deeper into the concrete challenges and strategies for PQC migration on blockchains and secure systems at my keynote this Thursday at EthCC conference.