+NCR/CRC! [ReVeRsEr] retweetledi
+NCR/CRC! [ReVeRsEr]
2.3K posts
![+NCR/CRC! [ReVeRsEr] banner](https://pbs.twimg.com/profile_banners/55568982/1744913418)
![+NCR/CRC! [ReVeRsEr]](https://pbs.twimg.com/profile_images/1912931632475992064/H_9sijMD.jpg)
+NCR/CRC! [ReVeRsEr]
@crackinglandia
Crazy and disheveled guy!. From Gral. Pico, the World's Capital City of Asado. Big beer drinker. Gently reminder specialist.
RCE world Katılım Temmuz 2009
446 Takip Edilen1.2K Takipçiler
+NCR/CRC! [ReVeRsEr] retweetledi

New blog post on reverse engineering and modifying HDD firmware. In this part I cover obtaining, analyzing, and modifying firmware, using backdoor commands to hot patch code in RAM, and using JTAG to debug a live HDD icode4.coffee/?p=1465
English
+NCR/CRC! [ReVeRsEr] retweetledi

A 0-click exploit chain for the Pixel 10: When a Door Closes, a Window Opens projectzero.google/2026/05/pixel-…
English

@AirFranela se comieron tanto el cuento de "los hombres solo se fijan en el fisico" que piensan que teniendo una carita linda y buen culo ya es suficiente para tener una relacion prospera. las relaciones terminan por A o por B, hasta por ser demasiado "perfecto" te pueden dejar kjj
Español

Ya eras una bomba estando con él y así
y todo, te dejó.
Cuando las mujeres entiendan que los hombres no te dejan por fea sino por infumable, van a nacer mil haditas. 🧚
Tendencias en Argentina@porqueTTarg
“Bomba” Por la confesión de esta tiktoker: "Hoy tengo un evento nocturno en el que va a estar mi exnovio, así que me voy toda potra con un look sensual. ¡Mirá la bomba que dejaste el 31 de diciembre!"
Español
+NCR/CRC! [ReVeRsEr] retweetledi

Lately I've been thinking about how AI is changing vulnerability research and reverse engineering. VR and RE are some of the hardest workflows to parallelize. Even with great knowledge transfer and team practices, you usually default to one person per vuln or RE task. The work is just too context-heavy to split.
AI breaks that ceiling. It's no longer "one researcher, one task", it's you working one angle while Claude annotates disassembly code, explores another path, or helps you piece together what the last result means.
Watching this land in domains we assumed were fundamentally serial is wild.

English
+NCR/CRC! [ReVeRsEr] retweetledi

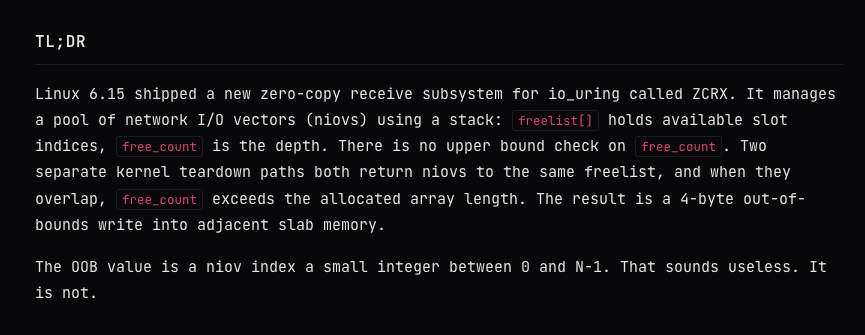
I just reverse engineered the YellowKey BitLocker bypass
Microsoft shipped code that checks for a flag called "FailRelock" in every Windows 11 recovery image. When it's set to 1, after recovery unlocks your BitLocker drive, it never relocks it. All you need is a USB stick.
This code only exists in the recovery environment. Not in normal Windows. They left an entire debug testing framework in production.
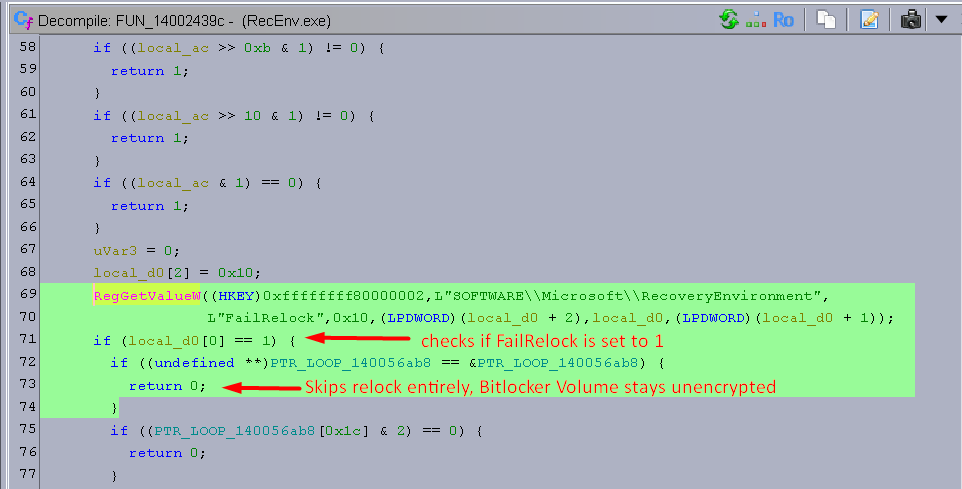
impulsive@weezerOSINT
The userland demon is about to drop again.
English
![+NCR/CRC! [ReVeRsEr]](https://pbs.twimg.com/profile_images/1912931632475992064/H_9sijMD.jpg)
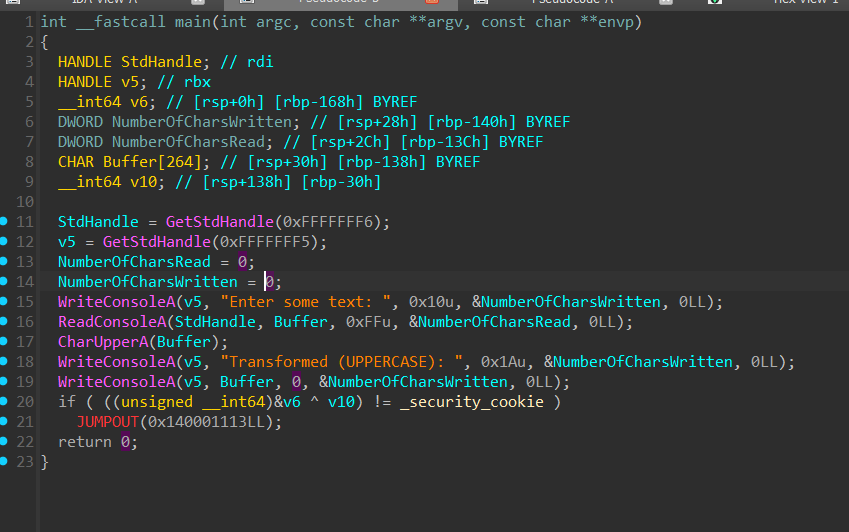
Soluciones al reto 2 y 3 de CLSMalwareRE: github.com/crackinglandia… y github.com/crackinglandia…
Español
+NCR/CRC! [ReVeRsEr] retweetledi
+NCR/CRC! [ReVeRsEr] retweetledi

+NCR/CRC! [ReVeRsEr] retweetledi

Static Devirtualization of Themida/CodeVirtualizer. The techniques in this article apply to pretty much every virtual machine obfuscator with minor modifications.
back.engineering/blog/09/05/202…
Original Program & Devirtualized Output
github.com/backengineerin…

English
+NCR/CRC! [ReVeRsEr] retweetledi

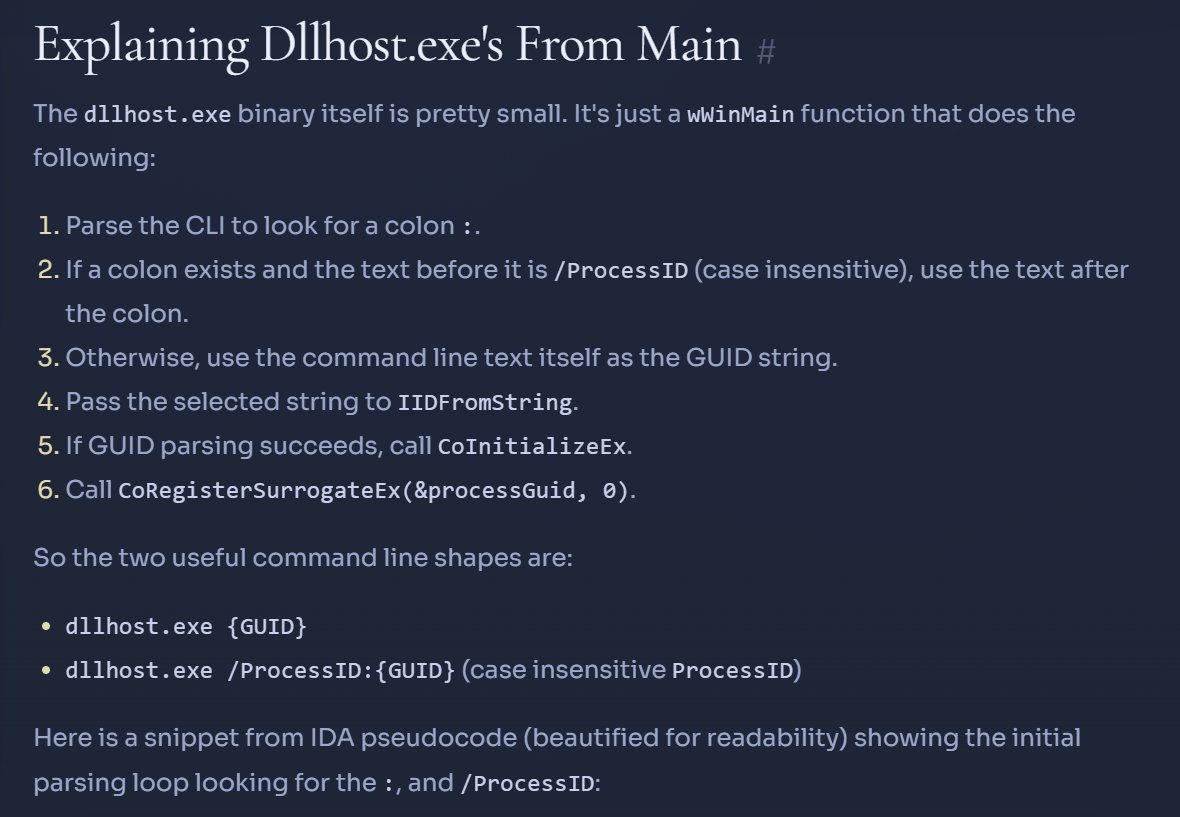
A couple years ago I wrote a blog on Dllhost and what it is actually running. I decided to revisit it this time around from a RE perspective and answer that conclusively. From CLI to the registry value.
Read the research - research.nasbench.dev/research/windo…
TL;DR - Dllhost is just a wrapper around CoRegisterSurrogateEx. It register but does not execute. Thats a job for combase.dll. Hence why it cannot be used as a LOLBIN directly.
There are also additional fun facts in there. Enjoy!
English
+NCR/CRC! [ReVeRsEr] retweetledi

When practicing on a VM crackme recently, I created a devirtualizer which lifts the virtual machine to LLVM to defeat the protection. LLVM-based devirtualisation is a lot of fun and I wrote down my experience and lessons learned on my blog:
eversinc33.com/2026/05/07/llv…
English
+NCR/CRC! [ReVeRsEr] retweetledi

MorphKatz
MorphKatz rewrites x86-64 machine code inside PE executables and raw shellcode into semantically identical but byte-different equivalents
github.com/0xMohammedHass…
#forensics #evasion #pentesting

English
+NCR/CRC! [ReVeRsEr] retweetledi
💥 Introducing "Dirty Frag"
A universal Linux LPE chaining two vulns in xfrm-ESP and RxRPC. A successor class to Dirty Pipe & Copy Fail.
No race, no panic on failure, fully deterministic. ~9 years latent.
Ubuntu / RHEL / Fedora / openSUSE / CentOS / AlmaLinux, and more.
Even if you've applied the "Copy Fail" mitigation, your Linux is still vulnerable to "Dirty Frag". Apply the Dirty Frag mitigation.
Details:
dirtyfrag.io
GIF
English
+NCR/CRC! [ReVeRsEr] retweetledi

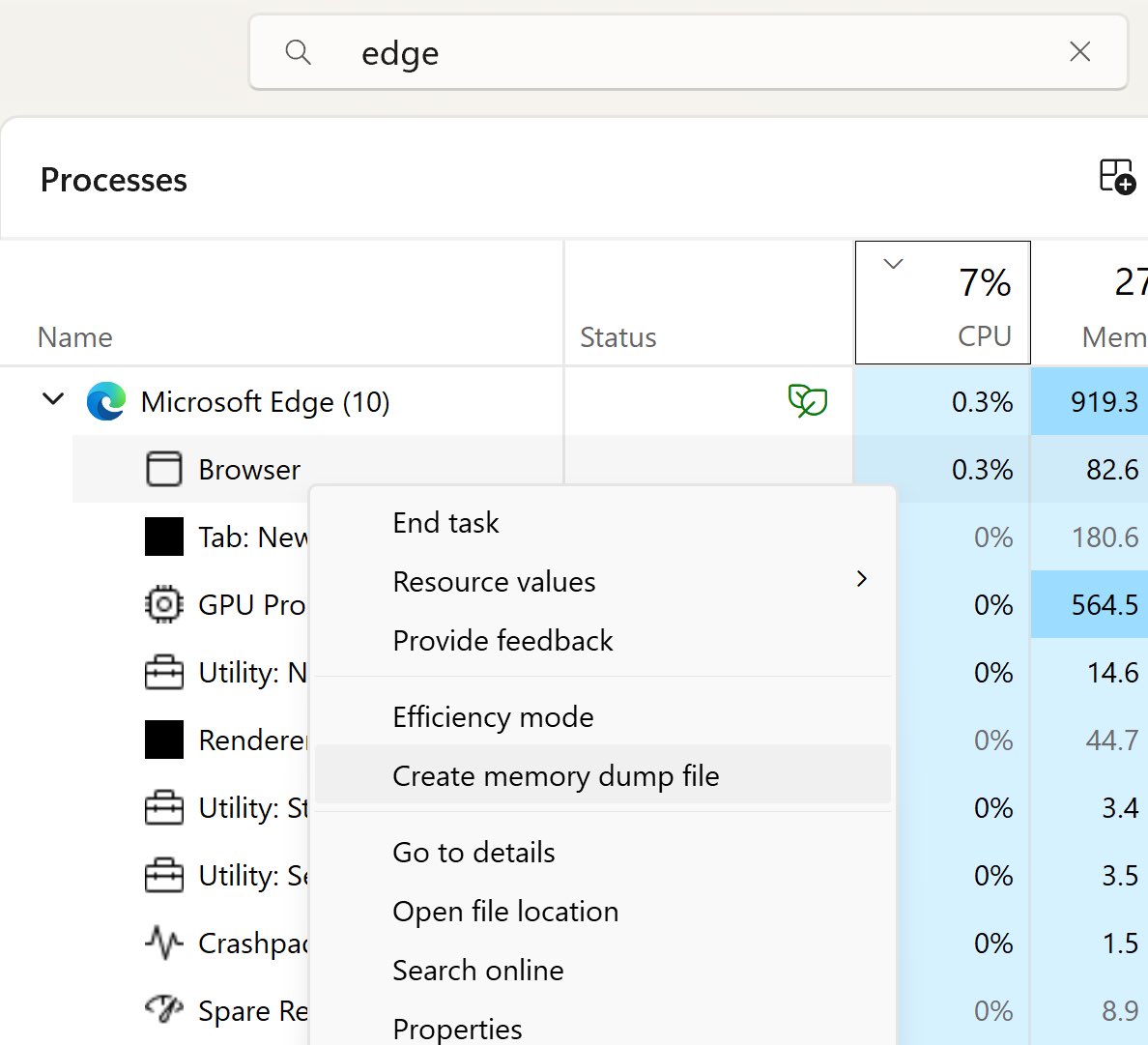
‼️🚨 Microsoft calls this "intended behaviour," so here we go.
How to dump the credentials of every user stored in Microsoft Edge:
1. Open Edge. Don't browse anywhere, just open it.
2. Flip to Task Manager, find Edge, expand the task.
3. Highlight the "browser" sub-task, right-click, and choose "Create Memory Dump."
4. Open the dump file and look for credentials.
The logged-in Windows user can dump every stored Edge credential with no additional rights. Which means any malware that user executes has those credentials for the asking.
Thanks to Rob VandenBrink at SANS: isc.sans.edu/diary/32954

English
+NCR/CRC! [ReVeRsEr] retweetledi
+NCR/CRC! [ReVeRsEr] retweetledi

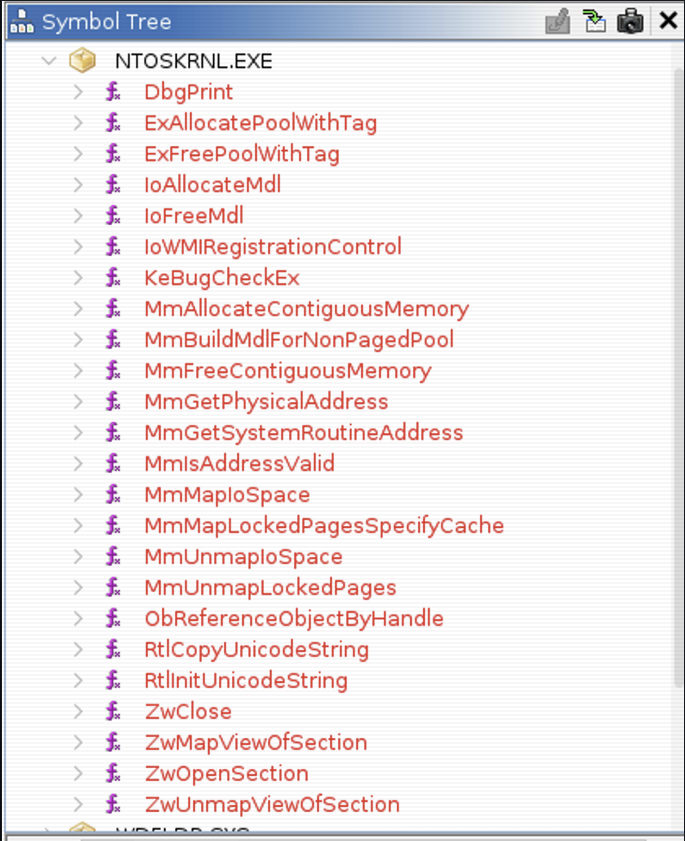
Reversing a legitimately Gigabyte signed Windows kernel driver to map 13 IOCTLs exposing physical memory access, MSR read/write, kernel memcpy, and more, and why this is the foundation of every BYOVD attack. #gdrv3 #driver #BYOVD
core-jmp.org/2026/05/gdrv3-…

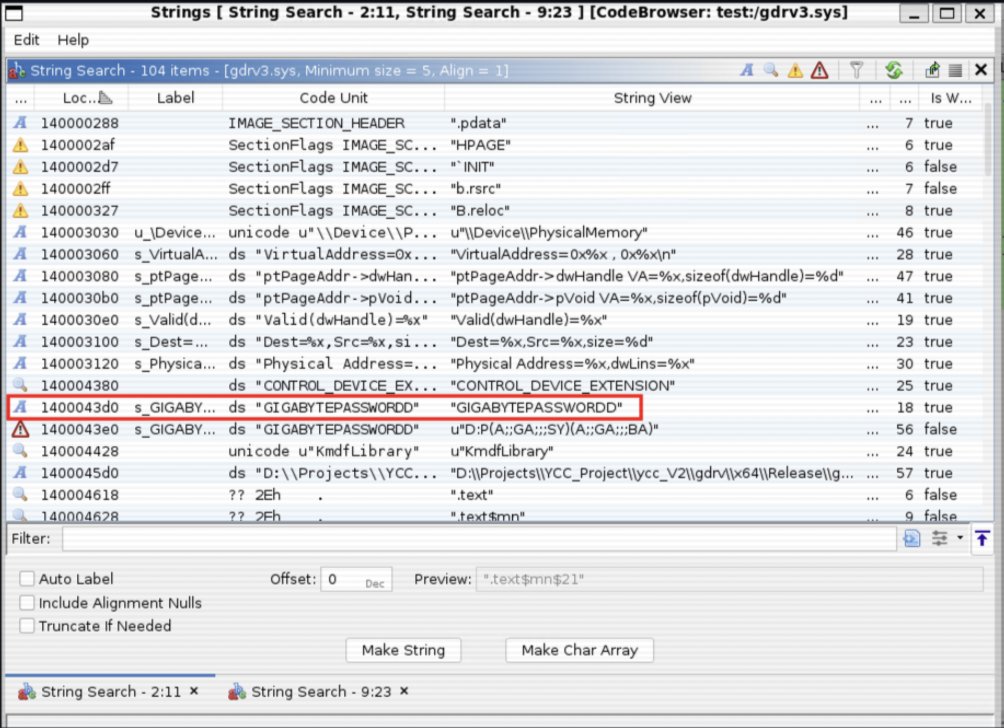
English
+NCR/CRC! [ReVeRsEr] retweetledi

The recording of my second Binary Cartography webinar is public:
Agentic Malware Analysis: From Task Automation to Deep Analysis
Topics: string decryption, API hashing, unpacking & pipeline building
Recording: youtu.be/azej1P17w9E
Slides & samples: github.com/mrphrazer/bina…
YouTube
English
+NCR/CRC! [ReVeRsEr] retweetledi

I too woke up and choose violence today as the fail-copy POC dropped.
Made a clean exploit including fixing the UID post exploitation without rebooting the target server. Smoke those CTF’s in hack the box.
github.com/rootsecdev/cve…
English