@yrschrade @Arcium Cool! You might want to consider using TurboSHAKE instead of SHA-3. Same round function, but only 12 of them instead of 24. rfc-editor.org/rfc/rfc9861
English
Gilles Van Assche
40 posts

@docgcrypto
Enthusiastic member of @KeccakTeam — cryptographer at ST — professor at Université Libre de Bruxelles ad interim


We’re excited to announce the Arcium v0.4.0 release. This update brings new features, performance optimizations, and developer experience improvements. We encourage all developers to migrate to v0.4.0 and leverage these updates for more efficient development on Arcium. Details below.




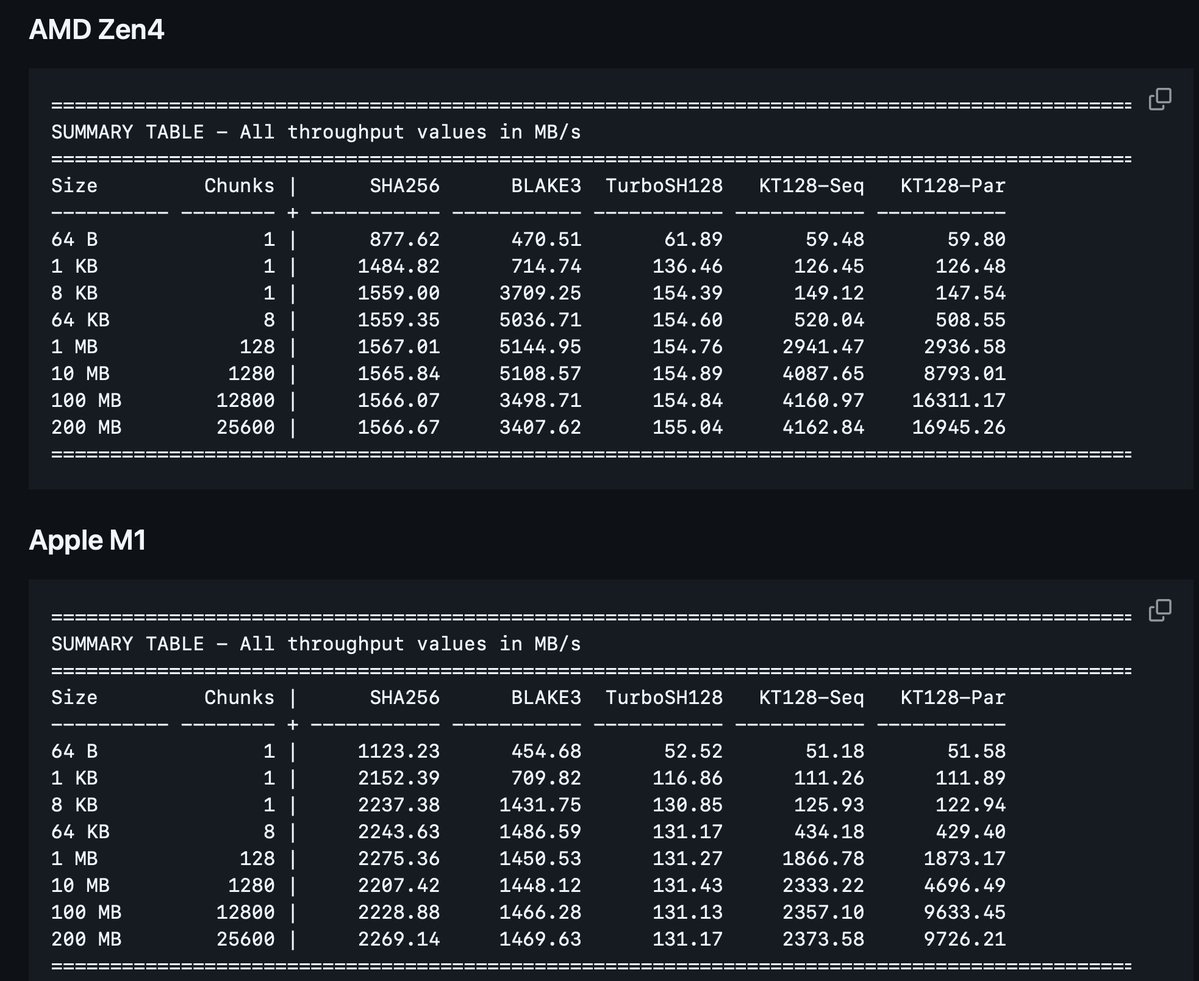



#ePrint TurboSHAKE: G Bertoni, J Daemen, S Hoffert, M Peeters, G Van Assche, R Van Keer, B Viguier ia.cr/2023/342