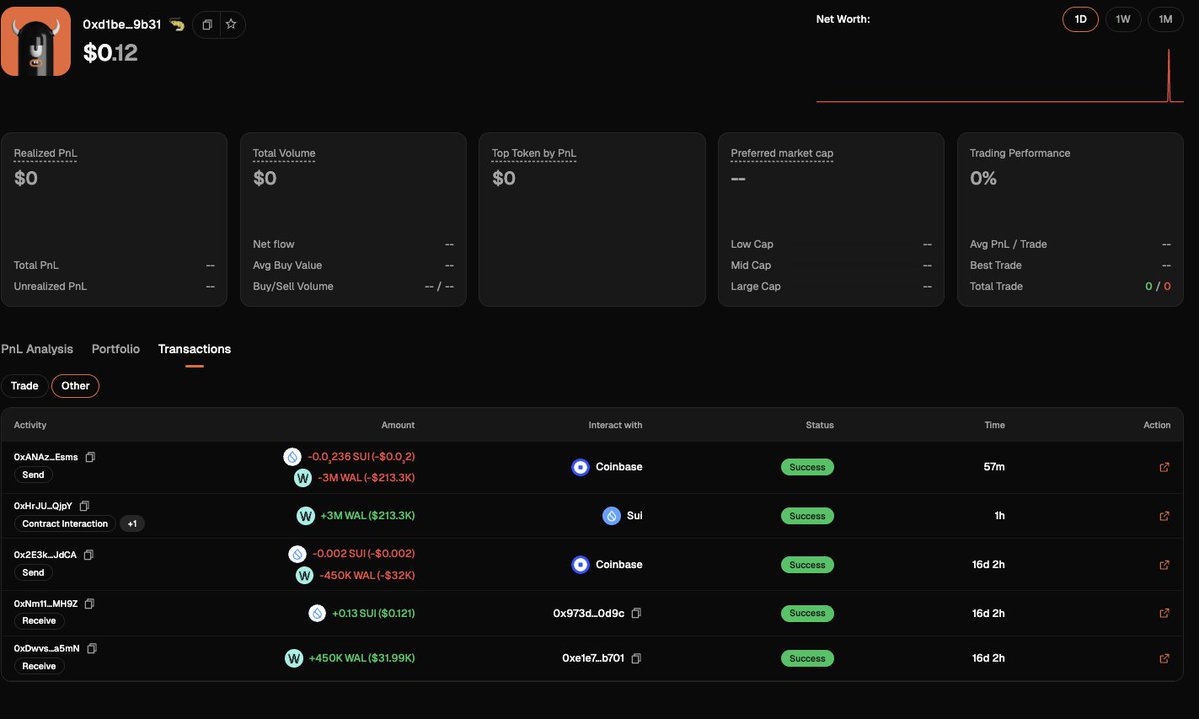
Introducing getTransfersByAddress A new Helius RPC method that returns parsed token and SOL transfer history for any wallet in 1 call - Filter by mint, amt, time, direction, counterparty - Cover token-2022 fees, wSOL wrap/unwrap event edge cases - Cursor pagination, 100/call