Erika Noerenberg [email protected]
9.2K posts

Erika Noerenberg [email protected]
@gutterchurl
malware and kittens, basically. she/her
Katılım Eylül 2009
2.8K Takip Edilen2.5K Takipçiler
Erika Noerenberg [email protected] retweetledi
@patrickwardle @jbradley89 3️⃣ "Practical iOS Reverse Engineering"
reversing.training/obtsv9/
Join @naehrdine for this hands-on training covering iOS app reversing, Frida, Ghidra/IDA, XPC, kernel & firmware internals, & the latest iOS security mitigations.
From beginner fundamentals to advanced iOS internals
English
Erika Noerenberg [email protected] retweetledi

Our macOS VR training is coming to OBTS!! 🤙☀️🏖️
Objective-See Foundation@objective_see
@patrickwardle @jbradley89 @naehrdine @Helthydriver 6️⃣ "macOS Vulnerability Research" macosvuln.training Taught by @theevilbit and @gergely_kalman, this *new* training focuses on macOS vulnerability research (VR), with an emphasis on logic flaws and understanding Apple’s unique protections and attack surfaces.
English

@thomasareed We will come take a tour with you! Good luck and have fun!
English
I've exited from tech and am doing guided tours in and around Yellowstone.
backroadsbear.com
Thanks to everyone for some great years! This will be my last post here. 🐬
English
Erika Noerenberg [email protected] retweetledi
The 2025 @volatility #PluginContest review is complete! We received 8 submissions from 7 different countries that included 20 plugins!
We will be highlighting each #Contender & the winners will be announced on Friday!
#DFIR #memoryforensics

English
Erika Noerenberg [email protected] retweetledi
Erika Noerenberg [email protected] retweetledi

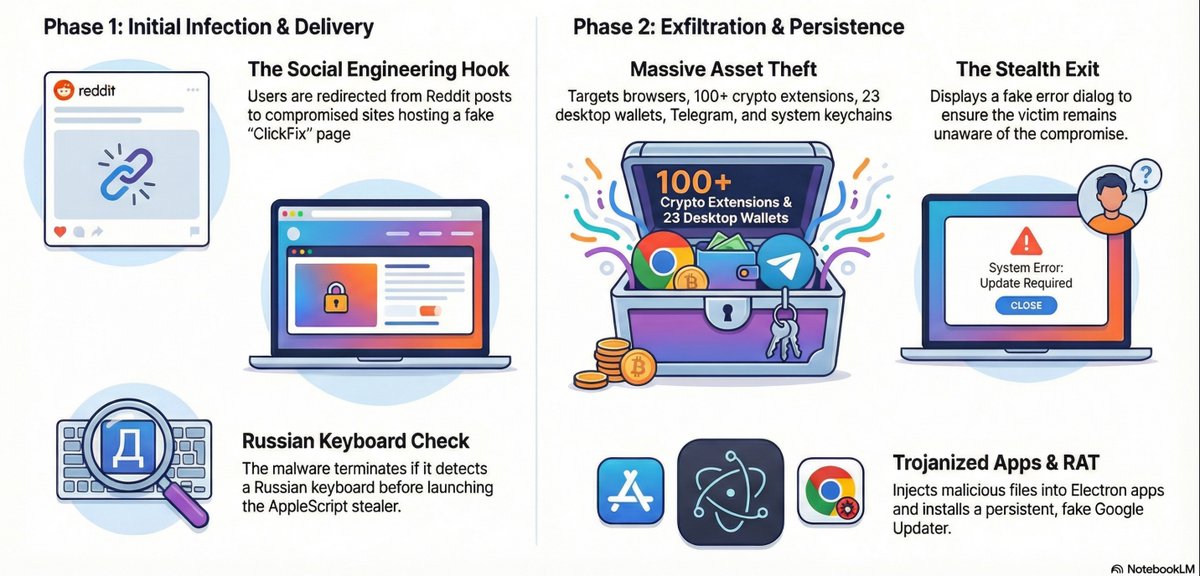
🧵 1/ What a funny story how @g0njxa and I decided to start trading and download TradingView Premium for FREE! (freaking AI is gonna replace us, so...) xD
Check this macOS stealer campaign that is using @Reddit karma-farming, allegedly compromised Indian tech company as a redirect, and a ClickFix trick to deliver the SHub Stealer that steals sensitive data, trojans your crypto wallets, and tries to persist disguised as Google Updater.
But don't worry - if you have a Russian keyboard, it won't touch you :3
English

@HackingDave I definitely agree to your point with a lot of meds - I had the same experience. but a big part of it is having good nutrition and routines (which you’ve obviously already nailed 😹) and a lot of folks need to get on meds for a time to settle the noise and figure out those habits
English

Erika Noerenberg [email protected] retweetledi

Motivated by @moonlock_lab’s recent findings on ClickFix attacks surfacing via Google Search results and even LLMs 🤯, I’ve added basic protection against most of these attacks to BlockBlock 🍎🛡️
Read: “ClickFix: Stopped at ⌘+V”
objective-see.org/blog/blog_0x85…
English
Erika Noerenberg [email protected] retweetledi

A Christmas Miracle?
The tiny piece of jewelry was so small it was easy to miss.
It’s a small, silver ring, but engraved inside is the wedding date of June 6, 1953, and the couple’s initials. That would be 72 years of marriage this year. An amazing and loving story told in one part by this traditional symbol.
We think it means a lot to that couple and we’d like to return it to them if possible so we’re asking for our community’s help.
It was found in the Gondolier restaurant parking lot off of Baseline and Foothills on Nov. 8 by a community member who tried in vain to find its owners via social media. Having no luck she turned it in to us on Nov. 17.
You can see it here. If anyone has any information about who this ring belongs to, we ask you to contact our Property and Evidence Unit by calling 303-441-3340. You will have to provide proof the ring belongs to you.
We’re hoping for a Christmas miracle. Can you help us make it happen Boulder?

English
Erika Noerenberg [email protected] retweetledi

Recon recon.cx/2026/en/index.… Conference: June 19 to 21 2026. More announcements coming soon.

English
Erika Noerenberg [email protected] retweetledi

Join us for another interview this Friday at 4pm ET with Tim Blazytko! As the instructor of Software Deobfuscation Techniques at RE//verse 2026, we'll be picking his brain about the role obfuscation and deobfuscation play a role in today's cybersecurity scene. What would you like to know? Reply with your questions! youtube.com/live/GQtX7S_oX…

YouTube

English
Erika Noerenberg [email protected] retweetledi

Wanna know how cool @patrickwardle is?
Not only did he give an amazing workshop today, but he also gifted us both of his books 🙏🏼
Don’t miss his talk tomorrow on the main stage at @ekoparty

English

@iamevltwin @l0ganbr @patrickwardle @andyrozen Your challenges were amazing and I hope we can do it again next year! Thank you for all your help ❤️
English

@l0ganbr @patrickwardle @andyrozen @gutterchurl Thank you for your help this year! It was lovely to see you again!!
English
Erika Noerenberg [email protected] retweetledi

Congratulations to everyone at the #obts organization, especially @patrickwardle @andyrozen also a thank you for the opportunity to help at the CTF @gutterchurl and @iamevltwin! See you next year!! mahalo \0

English
Erika Noerenberg [email protected] retweetledi

The slidedeck to our talk, Crash One: A Starbucks Story - CVE-2025-24277, with @gergely_kalman from @hexacon_fr and @objective_see #OBTS is available from the link below.
It was a macOS vulnerability impacting the crash reporting process where we could achieve LPE and sandbox escape.
theevilbit.github.io/talks_workshop…
English
Erika Noerenberg [email protected] retweetledi
Stoked for this #OBTS talk (and congrats on the CVE @malwarezoo)!
...but phew, Apple cutting it close on the patch!⌛️😅
Ferdous Saljooki@malwarezoo
Excited to be presenting again at #OBTS to share my research on how Apple revokes ad-hoc signed malware. Just in time for my talk, CVE-2025-43296 fixes a user-assisted Gatekeeper bypass allowing revoked ad-hoc signed malware to execute. Be sure to check out "Revoked, Not Dead: When CDHash Revocation Fails to Kill."
English
Erika Noerenberg [email protected] retweetledi

loved watching @birchb0y and @stuartjash present at @objective_see today! they even got dressed up for the occasion 💙
English
Erika Noerenberg [email protected] retweetledi

Today (4:00 PM GMT+2) @objective_see: Paweł Płatek shows a user-to-root exploit on modern macOS by chaining bugs in mDNSResponder and traceroute6. Learn new libmalloc exploitation techniques and PAC bypass methods.
objectivebythesea.org/v8/
English
