
hashp4
369 posts


hashp4
@hashp4_
🇫🇷 - Threat Research @Sekoia_io • Previously @WithSecure • I like malwares, forensics and CTI :)
Pologne Katılım Ocak 2019
463 Takip Edilen242 Takipçiler
Sabitlenmiş Tweet

Over the last week, I managed to complete the Waifu University APT emulation lab (IR on AlphV/Blackcat ransomware breach)
Thanks to @XintraOrg, @inversecos & the lab contributors for this great experience ❤️
You can find the investigation on my blog 👇
hashp4.fr/xintra-lab-wai…
English
hashp4 retweetledi

We were contacted by a journalist at Le Parisien newspaper with this prompt:
> I am preparing an article on the use of your secure personal data phone solution by drug traffickers and other criminals. Have you ever been contacted by the police? Are you aware that some of your clients might be criminals? And how does the company manage this issue?
Absolutely no further details were provided about what was being claimed, who was making it or the basis for those being made about it. We could only provide a very generic response to this.
Our response was heavily cut down and the references to human rights organizations, large tech companies and others using GrapheneOS weren't included. Our response was in English was translated by them: "we have no clients or customers" was turned into "nous n’avons ni clients ni usagers", etc...
GrapheneOS is a freely available open source privacy project. It's obtained from our website, not shady dealers in dark alleys and the "dark web". It doesn't have a marketing budget and we certainly aren't promoting it through unlisted YouTube channels and the other nonsense that's being claimed.
GrapheneOS has no such thing as the fake Snapchat feature that's described. What they're describing appears to be forks of GrapheneOS by shady companies infringing on our trademark. Those products may not even be truly based on GrapheneOS, similar to how ANOM used parts of it to pass it off as such.
France is an increasingly authoritarian country on the brink of it getting far worse. They're already very strong supporters of EU Chat Control. Their fascist law enforcement is clearly ahead of the game pushing outrageous false claims about open source privacy projects. None of it is substantiated.
iodéOS and /e/OS are based in France. iodéOS and /e/OS make devices dramatically more vulnerable while misleading users about privacy and security. These fake privacy products serve the interest of authoritarians rather than protecting people. /e/OS receives millions of euros in government funding.
Those lag many months to years behind on providing standard Android privacy and security patches. They heavily encourage users to use devices without working disk encryption and important security protections. Their users have their data up for grabs by apps, services and governments who want it.
There's a reason they're going after a legitimate privacy and security project developed outside of their jurisdiction rather than 2 companies based in France within their reach profiting from selling 'privacy' products.
discuss.grapheneos.org/d/24134-device…
Here's that article:
archive.is/AhMsj
English
hashp4 retweetledi

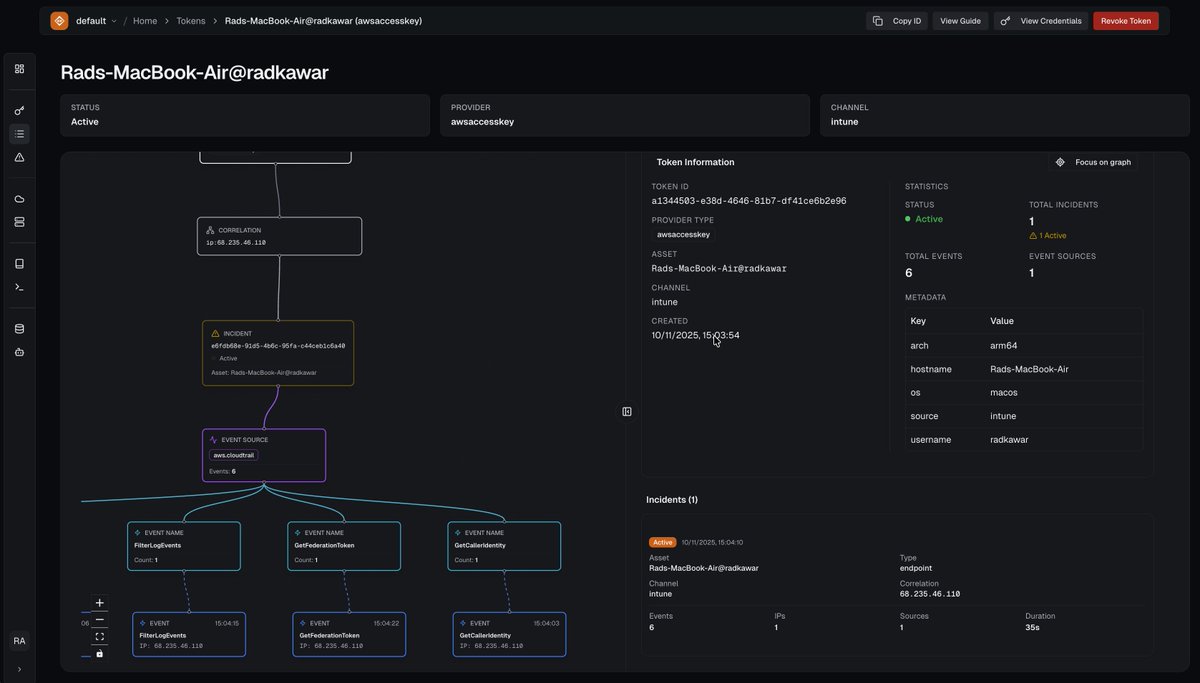
Once in a blue moon as a red teamer, we encountered environments with canary technology deployed across their infrastructure. The tables flipped. Blue teams caught us immediately.
Canary technology uniquely detects adversaries by exploiting their behavior - digital assets with no legitimate use that trigger immediate, high-fidelity alerts when interacted with.
However, most organizations struggle to extract these benefits. Existing canary solutions don't provide the primitives, token catalog, automation, and tooling needed for deployment and management at scale. They require dedicated security engineers to own and maintain.
As a result, high-fidelity detection has remained reserved for the most mature security teams.
For organizations already utilizing canary technology - did it catch your last red team engagement?
Today we're launching DeceptIQ - the cloud-native canary technology platform built from first principles.
We looked at enterprises who successfully deployed canary technology - what they did, what worked, what they wanted. Coupled with our experience as adversaries, we rebuilt the tried and tested concept from first principles. We spent eight months researching how to fingerprint our own tokens, then doing it again and again.
The result: the most comprehensive, configurable, scalable canary token platform available. over 15 new canary token providers designed to exploit adversary behavior - including 5 ephemeral that each scale to over a million an hour, and 10 new persistent canary tokens.
API-first deployment integrates with custom canary channels to enable visibility and deployment of canary tokens across Kubernetes, CI/CD pipelines, MDM platforms, and many more - at scale!
Our success metric: would we catch ourselves on a red team engagement? With today's launch, we believe we can.
We built DeceptIQ to be what we wish every organization we compromised had in place.
English
hashp4 retweetledi

I’m turning 41, but I don’t feel like celebrating.
Our generation is running out of time to save the free Internet built for us by our fathers.
What was once the promise of the free exchange of information is being turned into the ultimate tool of control.
Once-free countries are introducing dystopian measures such as digital IDs (UK), online age checks (Australia), and mass scanning of private messages (EU).
Germany is persecuting anyone who dares to criticize officials on the Internet. The UK is imprisoning thousands for their tweets. France is criminally investigating tech leaders who defend freedom and privacy.
A dark, dystopian world is approaching fast — while we’re asleep. Our generation risks going down in history as the last one that had freedoms — and allowed them to be taken away.
We’ve been fed a lie.
We’ve been made to believe that the greatest fight of our generation is to destroy everything our forefathers left us: tradition, privacy, sovereignty, the free market, and free speech.
By betraying the legacy of our ancestors, we’ve set ourselves on a path toward self-destruction — moral, intellectual, economic, and ultimately biological.
So no, I’m not going to celebrate today. I’m running out of time. WE are running out of time.
English
hashp4 retweetledi

Nothing but love for a blog post with summary conclusions of competing hypotheses.
Transparency around how we weigh the diagnostic value of specific evidence lays the foundation for better collective understanding in the long-term.
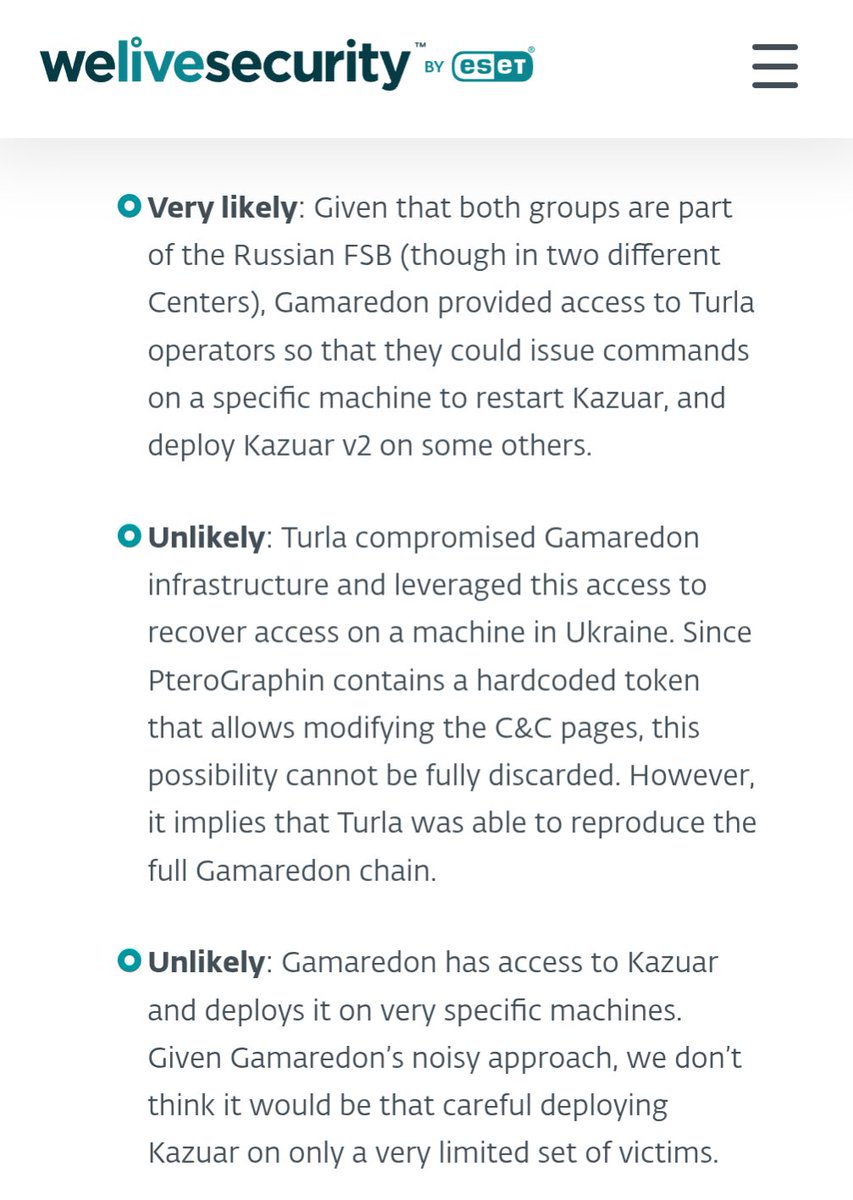
ESET Research@ESETresearch
#ESETresearch has discovered the first known cases of collaboration between Gamaredon and Turla, in Ukraine. Both groups are affiliated with the FSB, Russia’s main domestic intelligence and security agency. welivesecurity.com/en/eset-resear… 1/3
English
hashp4 retweetledi

The full technical report details how we took down the C2 infrastructure of Block Blasters drainer malware that @valvesoftware allowed on their platform. We spoke to the threat actors who had no remorse for stealing from a terminally ill cancer patient
docs.google.com/document/d/1vI…
English
hashp4 retweetledi

Excited to share our latest research on APT37(a.k.a ScarCruft, Ruby Sleet, and Velvet Chollima)’s new infection chain and C2 operation:
1⃣ Initial Access: Leveraging LNK and CHM files to deliver Rust-based and PowerShell-based malware.
2⃣ Post-Recon: Deployment of FadeStealer via a Python loader using Process Doppelgänging, followed by hands-on-keyboard activity.
3⃣ C2: A simple yet highly effective C2 script orchestrating the entire operation
Please check this out: zscaler.com/blogs/security…


English
hashp4 retweetledi
hashp4 retweetledi

Just posted my @defcon slides (talk #1): "Mastering Apple's Endpoint Security for Advanced macOS Malware Detection"
Writing 🍎 security software? You should be using Endpoint Security! But its advanced features are rather nuanced & often misunderstood 🫣
speakerdeck.com/patrickwardle/…
English

This year, I'm delighted to have had the opportunity to join the @x33fcon #crew and contribute to the smooth running of the conference as a volunteer.
I had the chance to meet a lot of great people during this week. It truly was an amazing experience.
See you next year! 😉
/ˈziːf-kɒn/@x33fcon
🚀The 9th edition of the #x33fcon conference is behind us! ♥️Heartfelt thanks to all participants, speakers, trainers, sponsors, partners, and volunteers! 👏Thank you so much, and see you next year!
English

@x33fcon talks and workshops start on Thursday! Who’ll be there? And most important, who will be on the pirate ship?
GIF
English
hashp4 retweetledi

Stop talking about doing things and just do them.
The incessant theory crafting about how to learn something, what the best books are, what courses to take, where the best place to learn etc... is tedious dithering.
If you actually wanted to do it, you would be doing it.
Endless talking isn't a strategy. You don't need another reddit thread, youtube deep dive or curated book list to get started.
You are not researching, you are procrastinating. If you actually cared about doing the thing, you’d already be doing it.
You romanticize the idea of doing something so much that you forget it actually requires effort. You are stalling because deep down, you know you won’t follow through.
Now prove me wrong and actually start learning how to hack, or whatever it is you never shutup about wanting to do.
English
hashp4 retweetledi
hashp4 retweetledi

Very proud to announce that the Windows Subsystem for Linux is now open source!
blogs.windows.com/windowsdevelop…
English
hashp4 retweetledi

Thread Execution Hijacking is one of the well-known methods that can be used to run implanted code.
In this blog we introduce a new injection method, that is based on this classic technique, but much stealthier - Waiting Thread Hijacking.
Read More : research.checkpoint.com/2025/waiting-t…
English
hashp4 retweetledi

Getting code execution in a process that cannot be located using traditional kernel APIs and is untouchable from usermode? All while staying PatchGuard-friendly?
Sign me up: archie-osu.github.io/2025/04/13/pow…
English
hashp4 retweetledi

TeamViewer - @whynotsecurity
TL;DR: TeamViewer stored user passwords encrypted with AES-128-CBC with they key of 0602000000a400005253413100040000 and iv of 0100010067244F436E6762F25EA8D704 in the Windows registry.
whynotsecurity.com/blog/teamviewe…
English
hashp4 retweetledi

Had a lot of fun digging into COM stuff with @bohops recently! We ended up finding a way to laterally move without dropping a file.
ibm.com/think/news/fil…
English
hashp4 retweetledi

I’ve trained many analysts over the years - inside my own teams, in SOCs, CERTs, and various internal security teams. And lately, I’ve been noticing a trend that deeply saddens me.
There’s an increasing number of young professionals who struggle with the grind of our work. They get simple but necessary tasks - tasks that transform indicators, rework detections, or retrieve and process data - but they return flawed results, late and incomplete. Some even let AI do the work without checking if it's correct. And when I ask why, the answer, directly or indirectly, is often the same: "I want to do the exciting stuff."
But the truth is, 97% of what we do in cybersecurity is not exciting. It's slow, repetitive, and requires patience. We grind through logs, extract data from reports, and refine rules. Most of the time, we don’t see the direct impact of our work. A signature written today might detect something crucial in a customer’s system six months from now, and we’ll never even know. But every small piece matters.
What saddens me is not just the impatience, but the lack of care. The unwillingness to put thought and effort into something seemingly simple. The failure to reflect on how to make a task better. This goes against something deeply ingrained in my upbringing - a principle that I believe is also deeply rooted in both German and Japanese culture.
In German, my grandmother would always say: "Mach es gescheit." It’s hard to translate precisely, but it means: Do it properly. Not just complete a task, but do it in a way that is solid, thoughtful, and more than just "good enough." It doesn’t mean perfection - it means putting care into what you do, even if no one else will notice.
The Japanese have a similar philosophy, one that I greatly admire. There is a word, "shokunin" (職人精神), which means more than just "craftsman." It describes someone who dedicates themselves fully to their craft, always refining, always improving. Even in the smallest tasks, a shokunin finds a way to do things better, not because someone told them to, but because they take pride in their work.
I was reminded of this when I thought about my uncle, who was a carpenter. When I was a child, I watched him finish his masterpiece for his final exam - an intricately crafted dresser. After days of sanding, polishing, and checking every tiny detail, he wasn’t done. He took out a small, hand-carved wooden rose, which he had made separately, and carefully placed it on the dresser’s ledge.
It wasn’t required. No one had told him to add that ornament. But he did it because he cared. Because he wanted his work to be more than just acceptable.
And this is what I want to see in young professionals today. It’s not about making flashy things, or chasing after excitement - it’s about taking pride in your craft, even in the smallest details. Because in the end, that’s what makes a difference.
So my advice is this: Whatever you do, do it gescheit. Do it like a shokunin. Put care into your work, even if no one else will see it. That’s how you grow. That’s how you build trust. And in the long run, that’s what will set you apart.
English


