i5nipe
199 posts


i5nipe
@i5nipe
Cyber Security Enthusiast | OSCP+ | eMAPT | eCPPTv2


Meu ultimo post esse ano. Vou sair de todas as redes sociais pra focar na minha OSCP :) Devo voltar em 3 meses, se nenhum imprevisto ocorrer rs. Bjs.




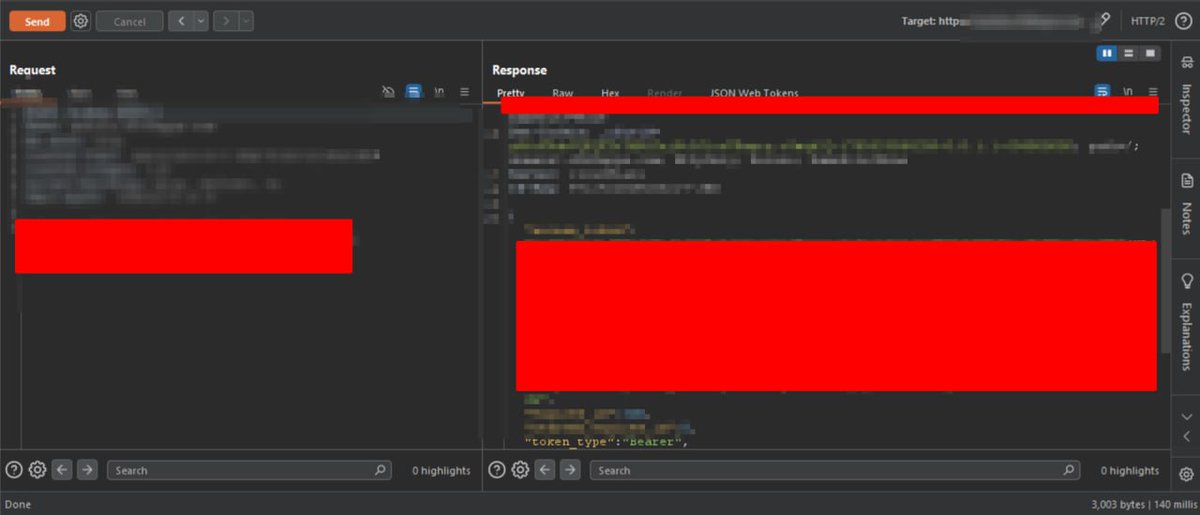
Did @Cloudflare just defeat @Burp_Suite and @CaidoIO? Cloudflare protection is becoming very common. This is the third app I’ve seen using it. Changing the user agent doesn’t help, and Burp TLS-fingerprint bypass plugin didn’t work. The app blocks any request when it detects traffic interception My target mobile app might be using a dynamic certificate based on my friend analysis. Back in Nov 2024, I tested a web app with Burp, but it blocked all traffic. Switching to Caido worked, maybe its signatures weren’t detected at the time. Can anyone share insights? thanks #BugBounty









Passed the OSCP+!



My RCE report just closed as internal duplicate:( Whitout any excerpt from duplicated report. But, lets see how communication works😭 P.s; i wrote an article and soon i will publish it.












