23pds (山哥)
14.2K posts

23pds (山哥)
@im23pds
Dad/@SlowMist_Team Partner&CISO/#Web3 Security Researcher/RedTeam/Pentester/Ai安全猎人 #bitcoin

⚠️ Running an AI Agent like @openclaw with root/terminal access is powerful but inherently risky. How do we ensure controllable risk and auditable operations without sacrificing capability? Recently, we released the OpenClaw Security Practice Guide — a structured defense matrix designed for high-privilege autonomous agents running in Linux Root environments. cc @evilcos 📖GitHub Version: 👉github.com/slowmist/openc… 🛡️ 3-Tier Defense Matrix 🔹Pre-action — Behavior blacklists & strict Skill installation audit protocols (Anti-Supply Chain Poisoning) 🔹In-action — Permission narrowing & Cross-Skill Pre-flight Checks (Business Risk Control) 🔹Post-action — Nightly automated explicit audits (13 core metrics) & Brain Git disaster recovery 🛠️ Built around four core principles: • Zero-friction operations • High-risk requires confirmation • Explicit nightly auditing • Zero-Trust by default 🚀 Zero-Friction Flow: 1️⃣ Drop the guide directly into your #OpenClaw chat 2️⃣ Ask the Agent to evaluate reliability 3️⃣ Instruct it to deploy the full defense matrix 4️⃣ Use the Red Teaming Guide to simulate an attack and ensure the Agent correctly interrupts the operation 🚨 Honest limitation: this guide is intended for human operators and AI Agents with foundational Linux system administration capabilities, and is particularly designed for OpenClaw operating in high-privilege environments. As AI models and their underlying service environments vary, the security measures provided in this guide are for defensive reference only. Final responsibility always remains with the human operator. Please assess and execute cautiously based on your own environment and capabilities. 🤝 If you have new findings, lessons learned, or improvement suggestions from real-world deployment, we welcome you to share them with the community via Contributions, Issues, or Feature Requests. Special thanks to @leixing0309 for the professional contribution. As we continue unlocking #AI capability, may we remain vigilant and clear-headed about risk.🫡
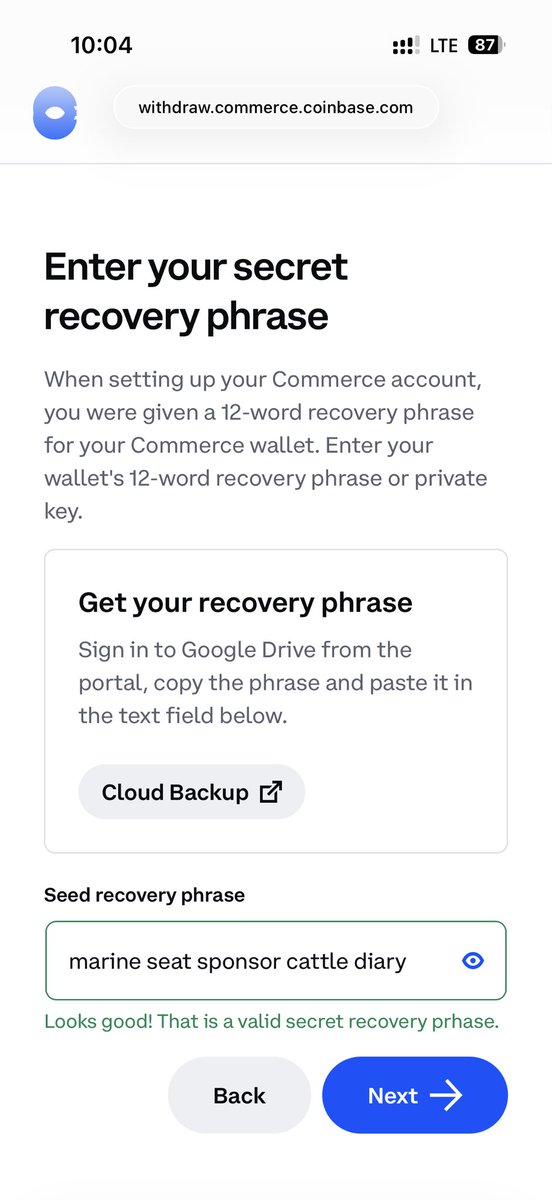
March 1st incident report On March 1, 2026, Bitrefill was the target of a cyberattack. Based on indicators observed during the investigation - including the modus operandi, the malware used, on-chain tracing and reused IP + email addresses (!) - we find many similarities between this attack and past cyberattacks by the DPRK Lazarus / Bluenoroff group against other companies in the crypto industries. The initial access originated through a compromised employee laptop, from which a legacy credential was exfiltrated. That credential provided access to a snapshot containing production secrets. From there, the attackers were able to escalate their access to our broader infrastructure, including parts of our database and certain cryptocurrency wallets. We first detected the incident after noticing suspicious purchasing patterns with certain suppliers. We realized that our gift card stock and supply lines were being exploited. At the same time we found some of our hot wallets being drained and funds transferred to attacker-controlled wallets. The moment we identified the breach, we took all of our systems offline as part of our containment response. Bitrefill operates a global e-commerce business with dozens of suppliers, thousands of products, and multiple payment methods across many countries. Safely switching all these things off and bringing them back online is not trivial. Since the incident, our team has been working closely with top industry security researchers, incident response specialists, on-chain analysts and law enforcement to understand what happened and how we can prevent it from happening again. A sincere thank you to @zeroshadow_io, @SEAL_Org, @RecoverisTeam and @fearsoff for their rapid response and support throughout this ordeal. What about your data Based on our investigation and our logs we don’t have reason to think that customer data was the target of this breach. There is no evidence that they extracted our entire database, only that the attackers ran a limited number of queries consistent with probing to understand what there was to steal, including cryptocurrency and Bitrefill gift card inventory. Bitrefill was designed to store very little personal data. We are a store, not a crypto service provider. We don’t require mandatory KYC. When a customer chooses to verify their account - e.g. to access higher purchasing tiers or certain products - that data is kept exclusively with our external KYC provider, with no backups in our system. Still, based on database logs, we know that a subset of purchase records was accessed and we want to be transparent about that. Around 18,500 purchase records were accessed by the attackers. Those records contained limited customer information, such as email addresses, crypto payment address, and metadata including IP address. For approximately 1,000 purchases, specific products required customers to provide a name. That information is encrypted in our database. However, since the attackers may have gotten access to the encryption keys, we are treating this data as potentially accessed. Customers in this category have already been notified directly by email. At this time, based on the information currently available, we do not believe customers need to take specific action. As a precaution, we recommend remaining cautious of any unexpected communications related to Bitrefill or crypto. If this assessment changes, we will of course immediately inform those affected. What we are doing We have already significantly improved our cybersecurity practices, but vow to continue to draw learnings from this experience to make sure user and company balances and data remain maximally safe. Specifically we’re: -Continuing thorough cybersecurity reviews and pentests with multiple external experts and implementing recommendations; -Further tightening internal access controls; -Further improving logging and monitoring for faster detection and more effective response; and -Continuing to refine and test our incident response procedures and automated shutdown procedures. The bottom line Getting hit by a sophisticated attack sucks (a lot). We’ve been in business for over 10 years and it’s the first time we’ve been hit this hard. But we survived. Bitrefill was designed to limit the impact if something like this ever happened. Bitrefill remains well funded, has been profitable for several years and will absorb these losses from our operational capital. Almost everything is back to normal: payments, stock, accounts. Sales volumes are also back to normal, and we are eternally thankful to our customers for your continued confidence in us. We will continue to do our best to continue deserving your trust. Thank you!
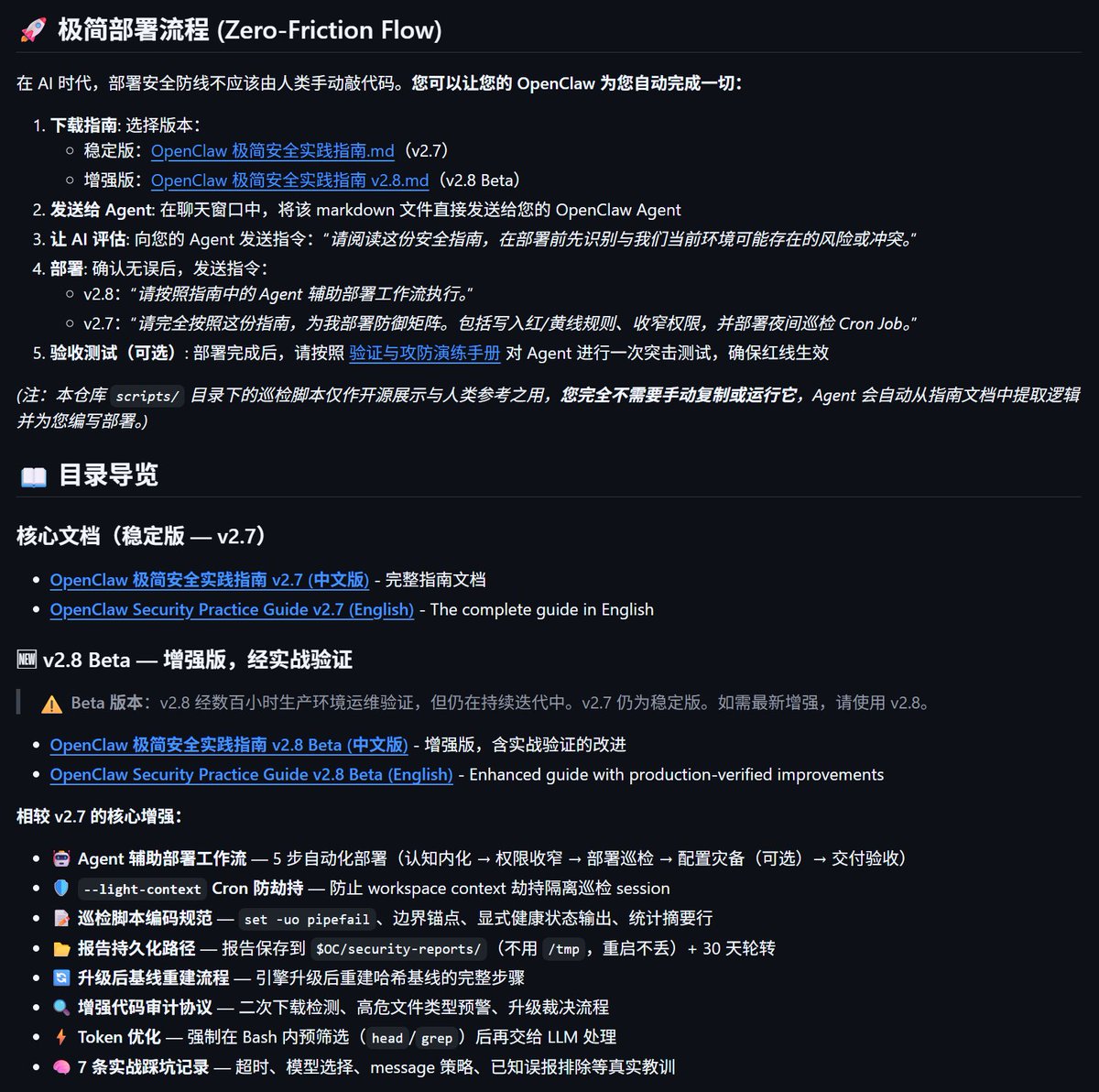
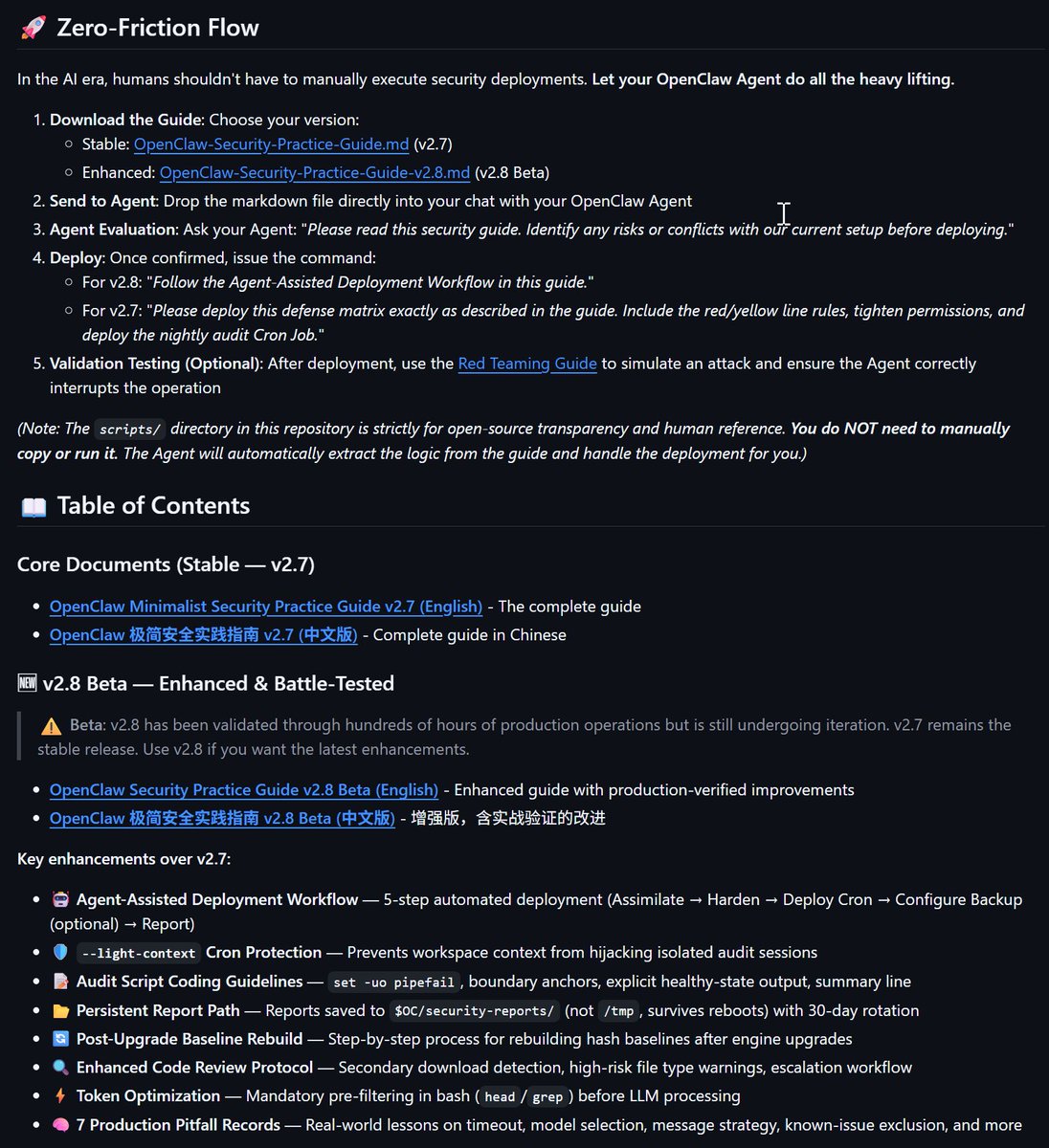
🦞OpenClaw 极简安全实践指南 (Security Practice Guide) 是面向 OpenClaw 的黑手册。 我尝试了其他一些方式来试图加固 OpenClaw,包括 Skill 方式,但是发现还不如给 OpenClaw 植入一个安全“思想钢印”来的有意思,这个“思想钢印”形成一个 md 文档,包含安全事前、事中、事后需要做的策略,但这里有个前提: 尽量不影响 OpenClaw 的日常使用,安全不要干扰用户体验,需要给这只🦞足够的自由。但是吧,江湖险恶,一只有 Root 权限且诞生才一个多月的🦞,安全不让人放心… 于是,这份面向 OpenClaw 的极简安全实践指南诞生了,目前是 v2.7 版本,此前我们内测了许多版本,也踩了不少坑。现在公布出来,大家玩之前务必仔细看这份指南的 README⚠️: github.com/slowmist/openc… 注意里面的说法。我相信你会很有收获。里面还推荐了我们实测在 OpenClaw 场景下聪明的模型,如果你有自己的感受,一定要和我们反馈。 一切都很新,一定有不完善的地方,请大家多指正! ⚠️最后,务必认真阅读 README,也务必肉眼扫描下你将喂给你🦞的“OpenClaw极简安全实践指南.md”,相信我,会非常有意思。


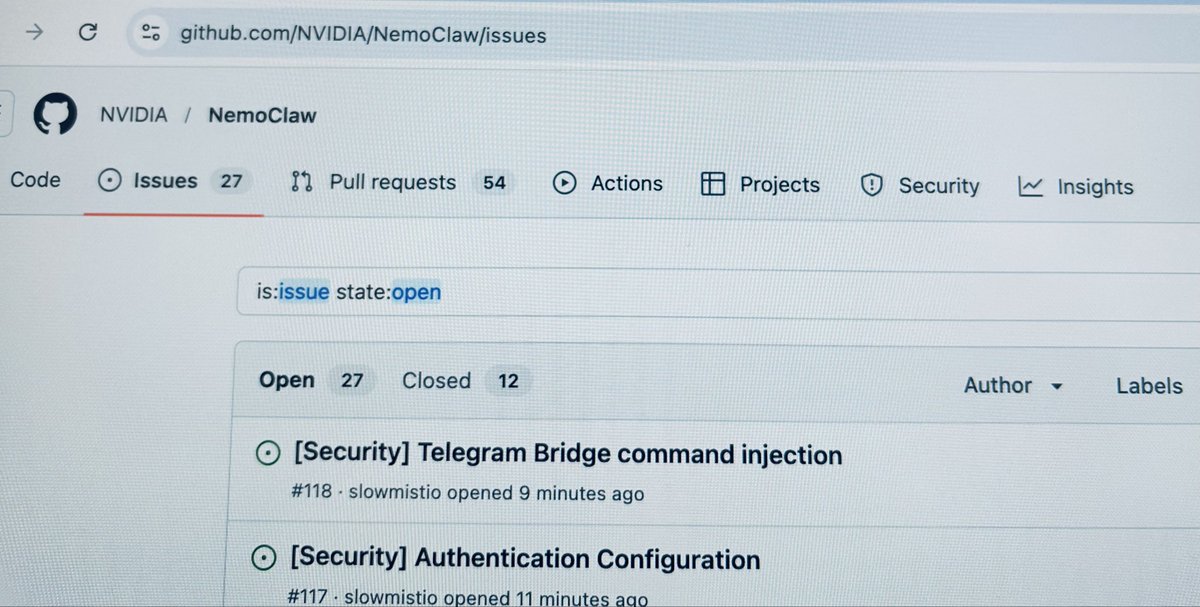
#NVIDIAGTC news: NVIDIA announces NemoClaw for the OpenClaw agent platform. NVIDIA NemoClaw installs NVIDIA Nemotron models and the NVIDIA OpenShell runtime in a single command, adding privacy and security controls to run secure, always-on AI assistants. nvda.ws/47xOPqQ
大胆预测下,随着AI、AI Agent 普及度、使用度越来越高,未来 GEO(AI搜索营销)投毒、 AI 搜索偏移 将会给用户带来新的挑战。🧐