Brendan Chamberlain
492 posts


Brendan Chamberlain
@infosecb
Threat Detection Engineer | detection & response | automation | macOS security | awesome-detection-engineering, LOOBins, Rulehound
Katılım Şubat 2016
715 Takip Edilen1K Takipçiler
Sabitlenmiş Tweet

Today I'd like to share a tool I recently wrote called Rulehound. It's a detection ruleset catalogue and search engine containing over 7,500 rules from 5 distinct sources. More details in thread.
rulehound.com
English
Brendan Chamberlain retweetledi

Google Threat Intelligence Group is dropping our latest AI Threat Tracker report today, which covers several threats we are watching through a variety of means. The report includes some details of the first 0day exploit we've found developed with AI. 1/x cloud.google.com/blog/topics/th…
English

A great articulation of the effect of AI in knowledge work:
nooneshappy.com/article/appear…
English
Brendan Chamberlain retweetledi
Brendan Chamberlain retweetledi
Brendan Chamberlain retweetledi

Everything is detectable, I’ve built detections for these but the cost on SOC is high. For some of them, even with baselines/low signals, filtering or AI triage, the workload remains significant in large environments. Realistically, very few teams will detect these anomalies
mthcht@mthcht2
👁️ LOLC2 Collection of C2 frameworks abusing legitimate services to evade detection Major update: new projects tested, enriched data, and deeper insights. site: lolc2.github.io github: github.com/lolc2/lolc2.gi…
English
Brendan Chamberlain retweetledi

Security Detections MCP 3.0 is LIVE
What started as a detection search MCP is now an autonomous detection engineering pipeline.
Agents now run a full workflow:
CTI → coverage analysis → detection generation → SIEM validation → PR staging
Pipeline example:
• CTI Analyst → extracts MITRE techniques from threat intel
• Coverage Analyzer → checks 7k+ detections across Sigma / Splunk / KQL / Elastic
• Detection Engineer → generates missing detections
• Atomic Executor + SIEM Validator → tests detections
• PR Stager → prepares them for review
Multi-SIEM support:
Splunk • Sentinel • Elastic • Sigma
Open source 👇
Repo
github.com/MHaggis/Securi…
npm
npmjs.com/package/securi…
Pulse MCP listing
pulsemcp.com/servers/mhaggi…
Watch the full demo:
youtu.be/03ZmD5cdfHI

YouTube
English
Brendan Chamberlain retweetledi

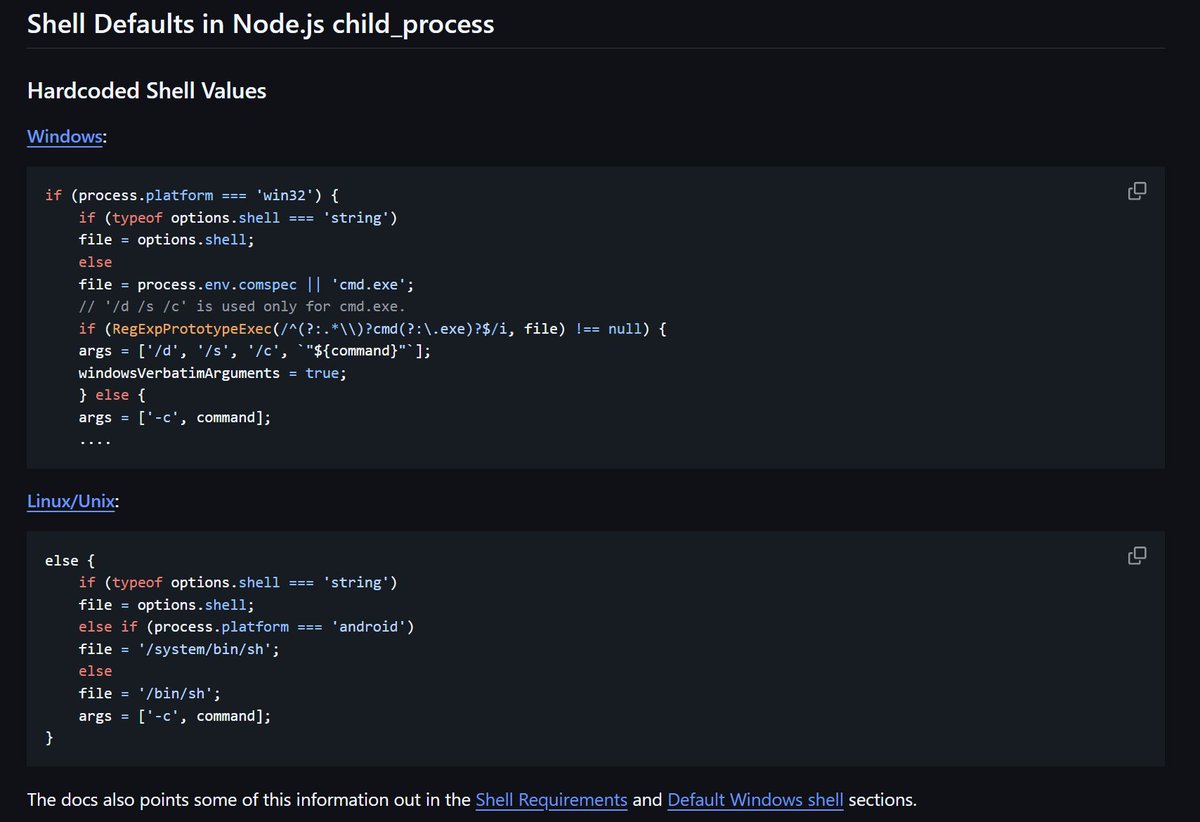
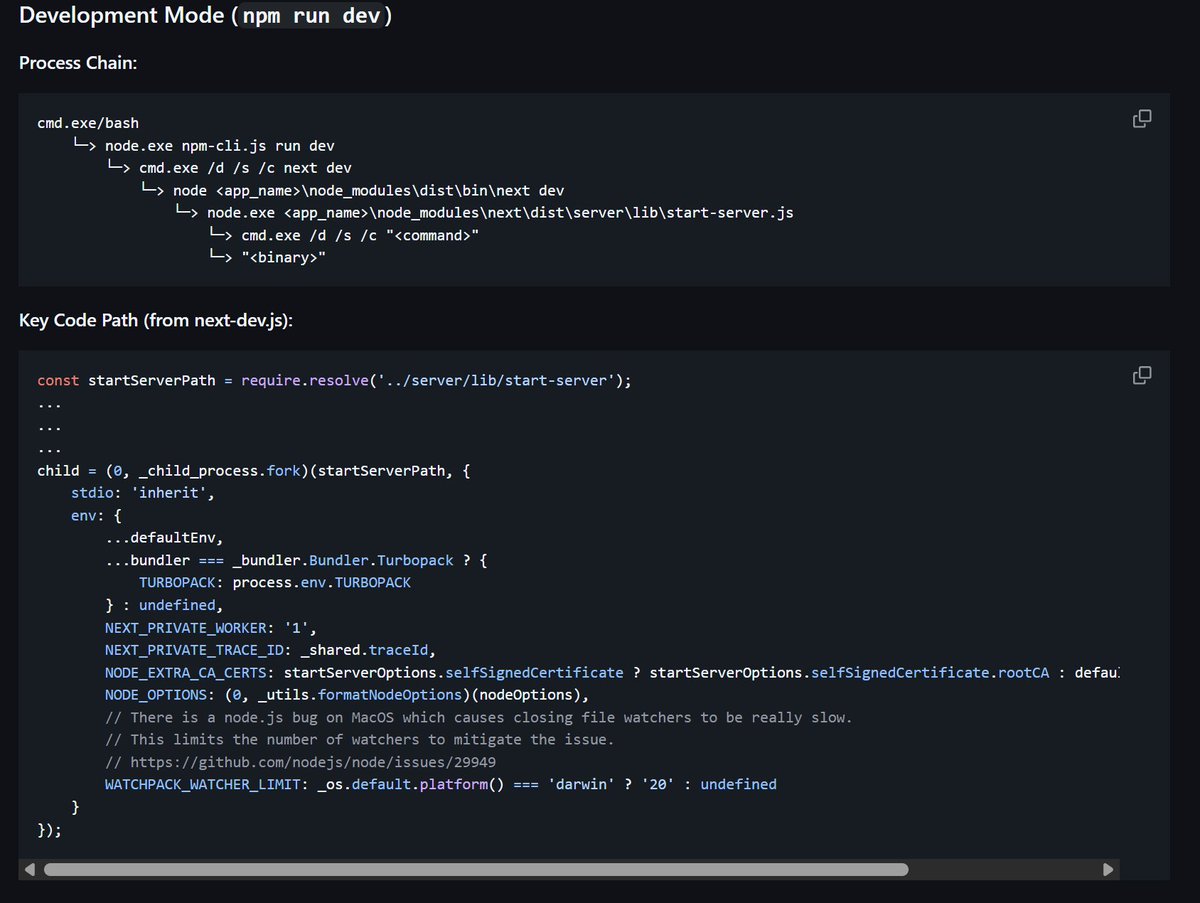
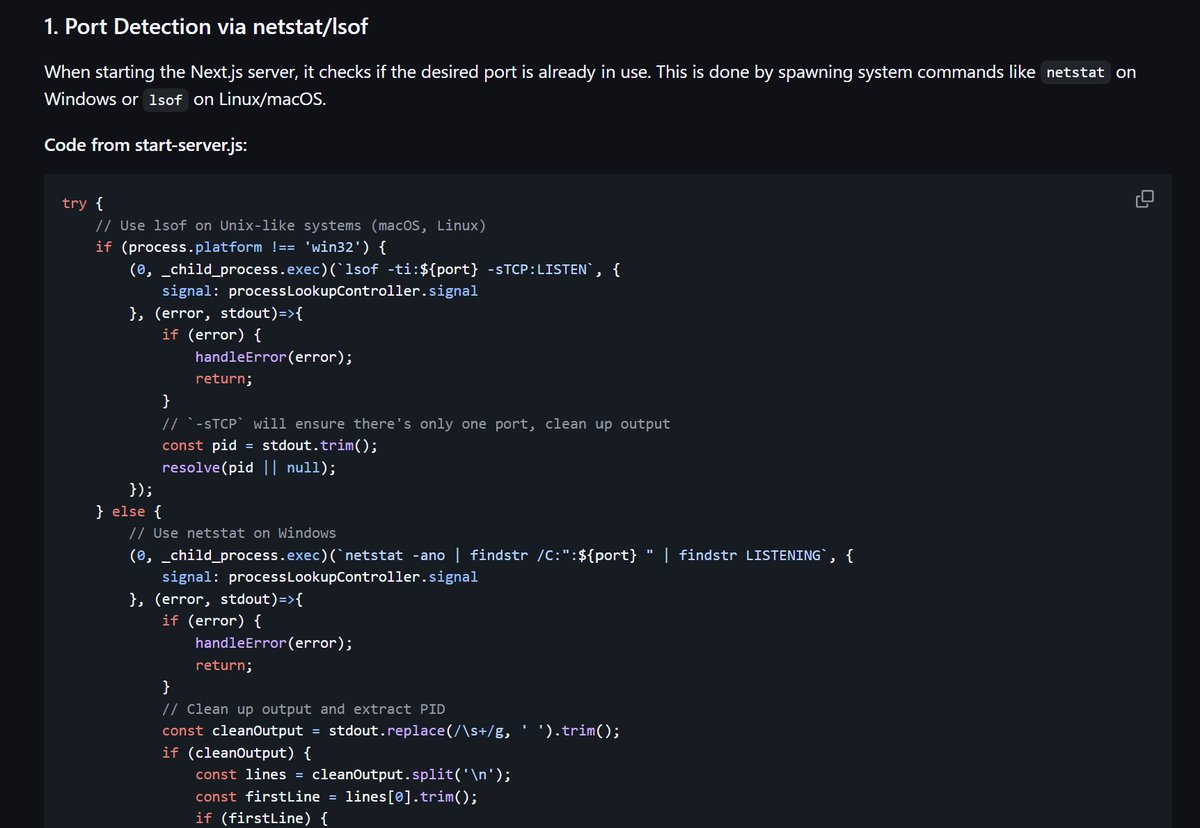
I have spent some time this past day to investigate NodeJS source code and how a typical process tree from a react/next.js app will look like.
If you are building detections for React2Shell give this a read. as it'll help you identify the right strings to use to filter down FPs and what anomalous look might like.
github.com/nasbench/Misc-…
English
Brendan Chamberlain retweetledi

Introducing the DRAPE Index! 🚀
Have you ever thought about _systematically_ ranking detections given their outcome but backed up by data? Now, you can.
I've been experimenting with this one for a while and now it's time to share with the #DetectionEngineering community.
The index is a composite measure of the individual true-positive (TP) and false-positive (FP) data points per detection rule/model.
The formula rewards detections that spot a decent amount of threats (TP) with good precision, while penalizing noisy ones, especially those that haven’t yet “proven” themselves with enough TPs.
DRAPE reveals whether a rule is signal-dominant (+) or noise-dominant (–) by inspecting the number of its TP and FP alerts over a period of time.
Implementations in #Python and #Splunk are available in a Github repo! 💙
Full blog post (memes included): detect.fyi/introducing-th…
English
Brendan Chamberlain retweetledi

If you ever wondered what goes into merging a Sigma rule in the @sigma_hq repo, check out the latest blog.
SigmaHQ Quality Assurance Pipeline -
blog.sigmahq.io/sigmahq-qualit…
We delve into the process we go through to ensure the community contributed rules are up to par.

English

Thanks to a poorly timed nor’easter, my flight to #OBTS was canceled. Bummed to be missing it but I hope to try again next year!
Brendan Chamberlain@infosecb
After many failed attempts, I’m thrilled to share that I’ll finally be attending #OBTS this year! See you in Ibiza 😎🏝️
English
Brendan Chamberlain retweetledi
Brendan Chamberlain retweetledi

My heart goes out to all the families and individuals anxious over their futures following the abrupt and chaotic announcement of H-1B visa changes.
America should be working to attract more skilled talent, not create uncertainly that turns them away. To all legal immigrants and H1-B holders: I support and appreciate you.
English

I spent some time with Spec Kit today to bootstrap a small side project and I’m impressed. It’s worth a look if you want to take vibe coding to the next level.
Has me thinking about how a framework like this could be applied to Detection Engineering.
github.blog/ai-and-ml/gene…
English
Brendan Chamberlain retweetledi

Not unexpected
“Velociraptor incident response tool abused for remote access”
news.sophos.com/en-us/2025/08/…
English

@cyb3rops This is the best kind of detection engineering work
English

I’m excited. This week I started working on a new rule set for a very specific, non-mainstream use case. Haven’t put this much thought and research into a handcrafted set in quite a while.
Some of these rules will still catch malicious stuff 5 years from now. And no one else would’ve written them that way.
Sometimes I create 3 variants of a rule, benchmark them all, and pick the one with the best coverage vs. false positive ratio.
They’re meant for a new project that looks into areas others struggle to cover - not because they don’t care, but because they’re using the wrong tools and the wrong mindset.
There will be a benefit for the community, and an added one for our customers.
English
Brendan Chamberlain retweetledi

After many failed attempts, I’m thrilled to share that I’ll finally be attending #OBTS this year! See you in Ibiza 😎🏝️
English
Brendan Chamberlain retweetledi

Brendan Chamberlain retweetledi