Sabitlenmiş Tweet

Very excited to announce our open-sourcing of Access!
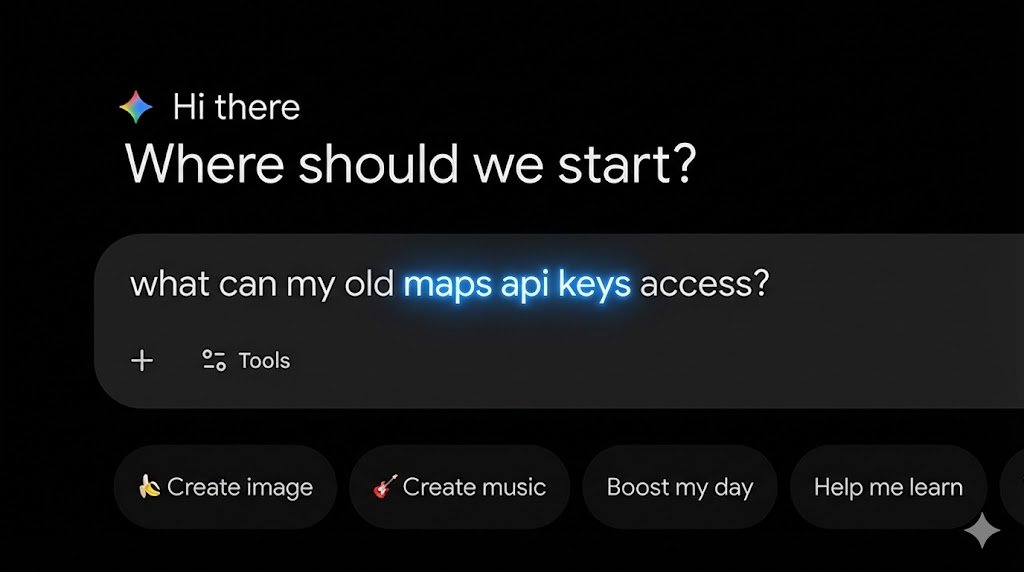
A centralized portal for Discord employees to transparently discover, request, and manage their access for all internal systems needed to do their jobs
discord.com/blog/access-a-…
English