Sabitlenmiş Tweet
Oste
10.2K posts

Oste
@oste_ke
ᴄʏʙᴇʀꜱᴇᴄᴜʀɪᴛʏ | ᴅꜰɪʀ 🛡️. ᴄᴛꜰ ᴘʟᴀʏᴇʀ @fr334aksmini | ꜰᴏᴜɴᴅɪɴɢ ʙᴏᴀʀᴅ ᴍᴇᴍʙᴇʀ @hih_community | #OpenSource ᴛɪɴᴋᴇʀᴇʀ | 𝕏 |
127.0.0.1 Katılım Mart 2020
5.9K Takip Edilen6.6K Takipçiler
Oste retweetledi

Exposing Data Exfil: LOLBins, TTPs, and Binaries…Oh, My!
huntress.com/blog/exposing-…
English
Oste retweetledi

GitHub repos for bug bounty hunters:
1. github.com/0xmaximus/Gala…
2. github.com/coffinxp/nucle…
3. github.com/0xKayala/Custo…
4. github.com/HackTricks-wik…
5. github.com/cipher387/Dork…
6. github.com/techgaun/githu…
7. github.com/s0md3v/Awesome…
8. github.com/TakSec/google-…
9. github.com/arainho/awesom…
10. github.com/0xInfection/Aw…
11. github.com/0xMrNiko/Aweso…
12. github.com/Lissy93/web-ch…
13. github.com/jakejarvis/awe…
14. github.com/swisskyrepo/Pa…
15. github.com/m14r41/Pentest…
16. github.com/ayoubfathi/lea…
17. github.com/streaak/keyhac…
18. github.com/devanshbatham/…
19. github.com/SecShiv/OneDor…
20. github.com/Hari-prasaanth…
21. github.com/djadmin/awesom…
22. github.com/Az0x7/vulnerab…
23. github.com/nahamsec/Resou…
24. github.com/daffainfo/AllA…
25. github.com/fuzzdb-project…
26. github.com/qazbnm456/awes…
27. github.com/infoslack/awes…
28. github.com/enaqx/awesome-…
29. github.com/reddelexc/hack…
30. github.com/tomnomnom/hacks
31. github.com/danielmiessler…
Drop the ones I'm missing or the ones you find most useful in your hunting workflow.
#BugBounty #BugBountyTips #WebSec
English
Oste retweetledi
Thread: Deep analysis of the axios npm supply chain compromise
All 5 payloads downloaded from VT, reversed in an isolated VM. Full report + detection rules:
gist.github.com/N3mes1s/0c0fc7…
What's in the gist (8 files):
1. Verified Threat Intel Report (all hashes VT-confirmed)
2. Full RE of every payload (source code recovered for all 3 RATs)
3. C2 protocol specification (complete JSON schema, state machine)
4. 8 YARA rules (tested, 100% detection)
5. 8 Sigma rules (Win/Mac/Linux)
6. 11 Suricata/Snort IDS rules (including Base64 beacon patterns)
7. Machine-readable IOC bundle (JSON, 14 SHA256 + network + MITRE)
8. Extension.SubRoutine research (see below)
Novel findings not in any vendor report:
- Extension.SubRoutine.Run2() — the .NET process injection DLL is completely undocumented. Zero results across all public
sources. Custom-built injector, not from any known tool.
- Linux RAT (ld.py, 0/76 detection) has a bug — peinject command references undefined variable b64_string. Binary injection
crashes on Linux.
- macOS RAT has zero hardcoded IPs/domains. C2 is runtime-only via argv[1]. Compiled with SDK 26.2.0 (latest Xcode). Build
UUID: c848257813983360905d7ad0f7e5e3f5.
- C2 server confirmed as Express.js via URLScan X-Powered-By header.
- packages.npm.org in the POST body is not an npm URL — it's the National Association of Pastoral Musicians. Designed to look
legit in network logs.
- Hostwinds AS54290 has confirmed Lazarus infrastructure in the same /18 subnet (Hunt.io research).
- macOS RAT classified as NukeSped by 4 AV engines. JA3 fingerprint 773906b0... mimics Safari 15.5 — nation-state TLS
tradecraft.
- All 3 RATs share identical 4-command protocol: kill, peinject, runscript, rundir with status codes "Wow"/"Zzz".
- Zenbox memory dump (47MB) downloaded and analyzed — 12 PE files extracted. Extension.SubRoutine DLL not recoverable (C2 was
offline during sandbox run).
Setup.js fully deobfuscated — all 18 XOR-encoded strings decoded including full VBScript and AppleScript payloads.
macOS binary reversed with radare2 — main(), Report(), DoWork(), DoActionIjt(), DoActionScpt(), RunProcess() all
reconstructed. Uses fork+execv (not system()), CurlGuard RAII pattern, nlohmann/json v3.11.3.
English
Oste retweetledi

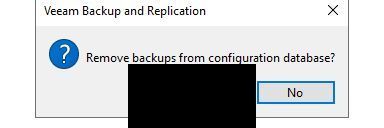
RDP bitmap cache artifacts revealed the threat actor opening the Veeam Backup & Replication console, reviewing backup jobs, tape & storage infrastructure — and removing backups from the configuration database.
Full report 👇
thedfirreport.com/2025/12/17/cat…
English
Oste retweetledi
Oste retweetledi

🚨‼️ MAJOR SUPPLY CHAIN ATTACK: npm package axios is compromised after the maintainer's npm account was hijacked.
Malicious versions contain a Remote Access Trojan. axios has 100M+ weekly downloads — it's in practically everything.
If you have installed axios@1.14.1 or axios@0.30.4, assume compromise.

English
Oste retweetledi

🚨 ZERODAY: ImageMagick 🚨
Our autonomous pentester pwn.ai just dropped multiple zeroday chains in ImageMagick that achieve RCE and File Leak from a single .jpg or .pdf file, bypassing EVERY security policy (Default, Limited, AND Secure). 🤯
💥 Affects Ubuntu, Debian, WordPress & millions of servers globally. Happy Monday and Happy Hunting! 🥰
pwn.ai/blog/imagemagi…

English
Oste retweetledi
Oste retweetledi

🚨 Big news: New TH Book 🏹
After years in Threat Hunting, I wrote the book I always wanted when I started.
The Art of Threat Hunting, practical, technical, no fluff.
⚡Hypothesis generation, queries & adaptation stuff, CTI-driven programs, documentation, team alignment. The full lifecycle.
🦖Full breakdown on the blog: rexorvc0.com
🔗Available on Amazon: amazon.com/Art-Threat-Hun…
#ThreatHunting #BlueTeam #Cybersecurity #Research #CTI #Malware #threat

English
Oste retweetledi

Just Uploaded the CTFd plugin I came up with to generate Player Certs during @p3rf3ctr00t CTF.
Feel free to check it out.....
github.com/LordSudo/CTFd-…
English
Oste retweetledi
Oste retweetledi

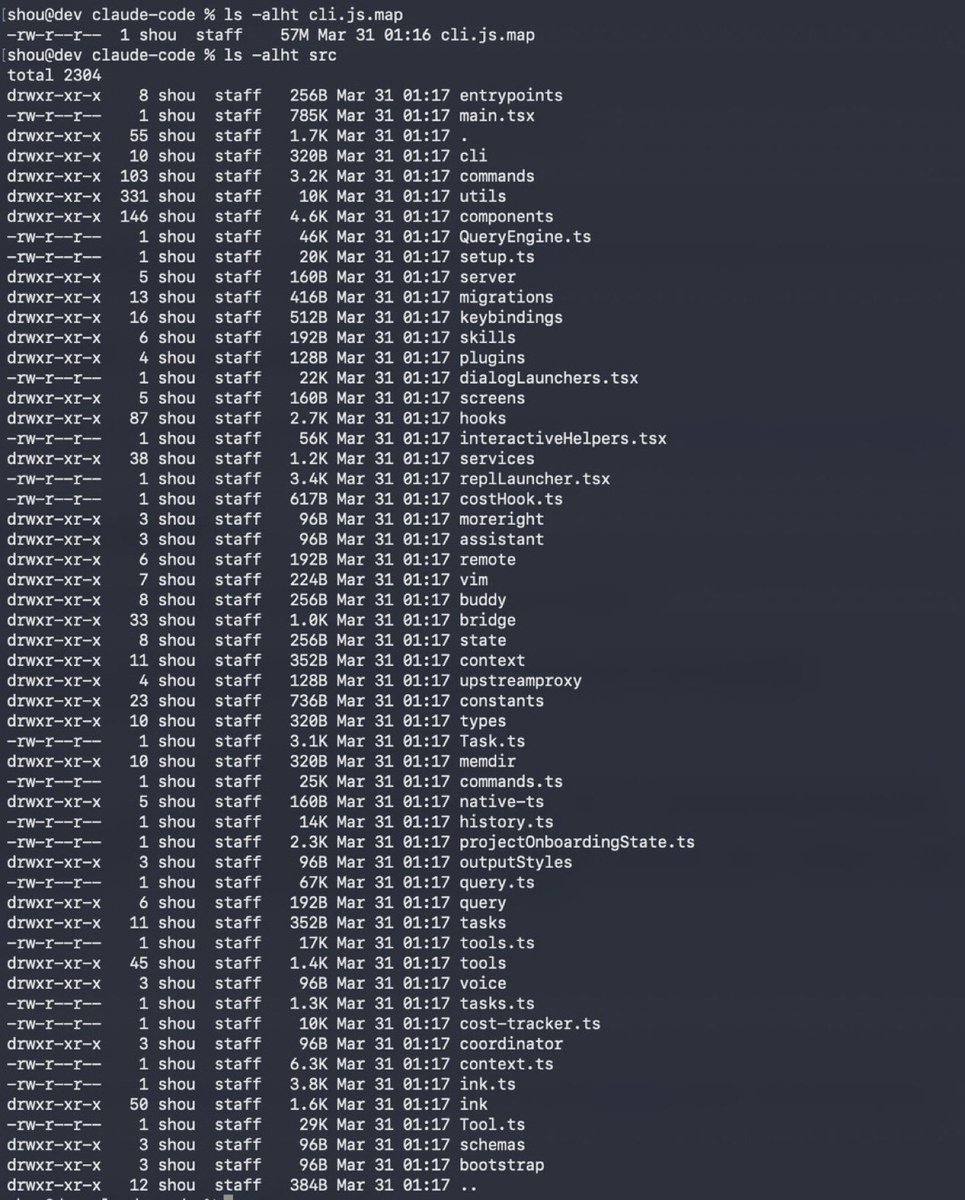
Claude code source code has been leaked via a map file in their npm registry!
Code: …a8527898604c1bbb12468b1581d95e.r2.dev/src.zip
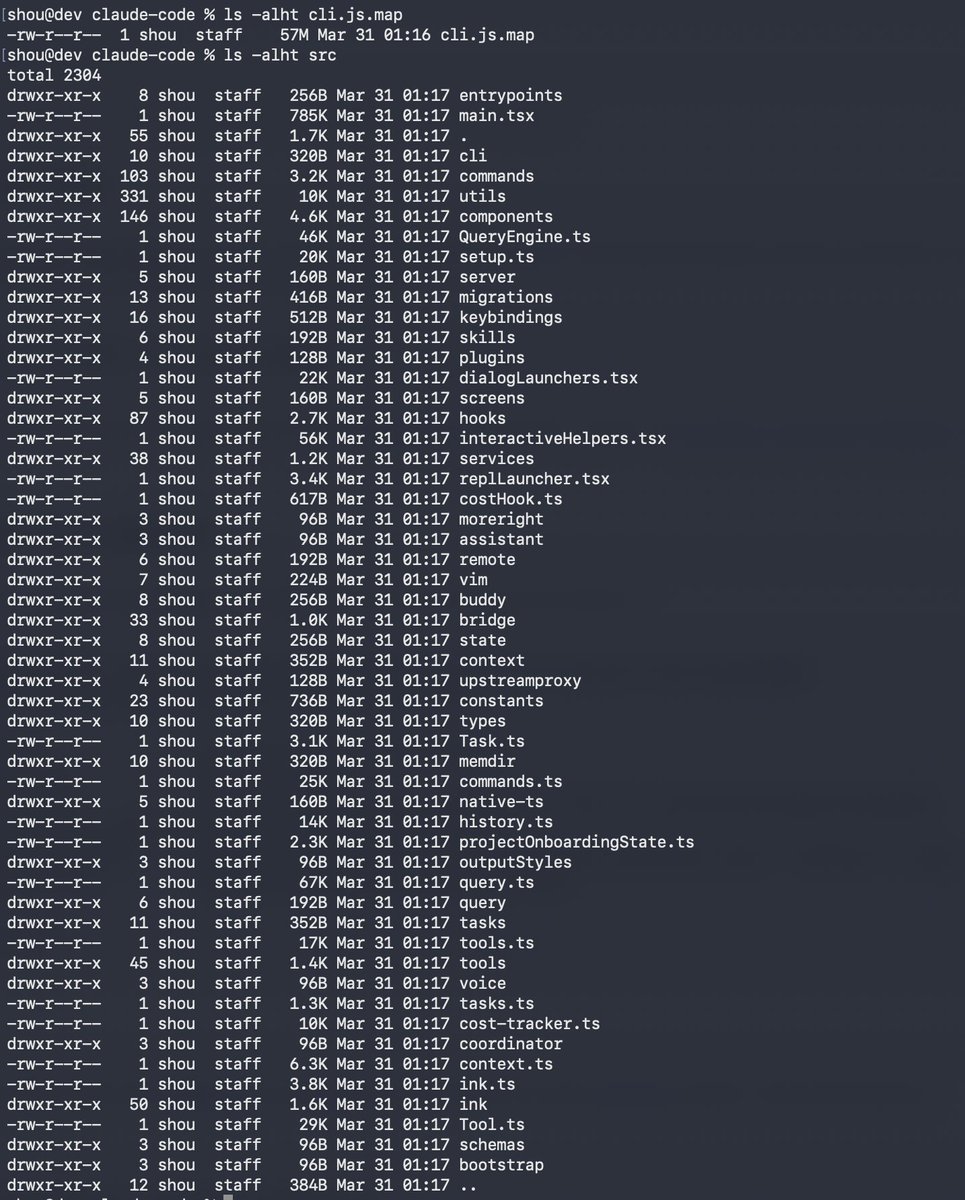
English
Oste retweetledi

🚨‼️ BREAKING: Adobe has been breached by threat actor Mr. Raccoon, leaking 13 million support tickets with personal data, 15,000 employee records, all HackerOne submissions, internal documents and more.
Mr. Raccoon gained access through an Indian BPO, first deploying a remote access tool on an employee, then phishing their manager.
Mr. Raccoon told us: "They allowed you to export all tickets in one request from an agent."


English
NIST updates its DNS security guidance for the first time in over a decade helpnetsecurity.com/2026/03/23/nis…
English
Oste retweetledi

Copy and paste to google learn-anything.xyz
Thank me later
English
Oste retweetledi
Oste retweetledi

SockTail - connecting target via a Tailscale network
Red Team Operators should find it useful.
A tool by @Yeeb_
Source: github.com/Yeeb1/SockTail
#redteam #blueteam #maldev #malwaredevelopment
English
Oste retweetledi