Sabitlenmiş Tweet

We getting griddy! Pushed a minor update to print a nice grid emulating excel sheets in console output. #redteam
github.com/OG-Sadpanda/Sh…
English
SadPanda
1.8K posts


@sadpanda_sec
#RedTeamer #MMAJunkie #CarGuy #F1... Opinions are my own.



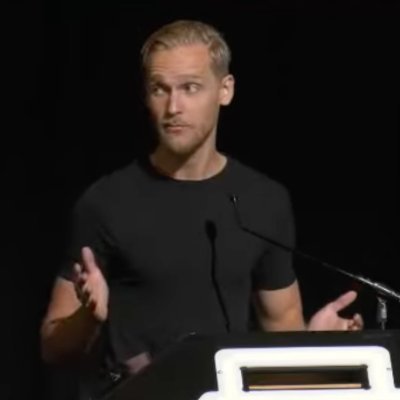
Never been happier to have a mouse in the house. 🐭 @_RastaMouse of @_ZeroPointSec has officially joined @Fortra! The mind behind Red Team Ops, one of the most respected training courses in offensive security, is now building what's next with us. fortra.com/resources/pres…




🔥🤖Excited to share a new blog I co-authored with @h4wkst3r and @kulinacs - Automating the Operator: Integrating LLMs into Offensive Security armadin.com/blog-posts/aut… We show how LLMs make offensive work more operationally useful, introduce 2 new MCP servers, and an NTLM relaying Gemini extension POC