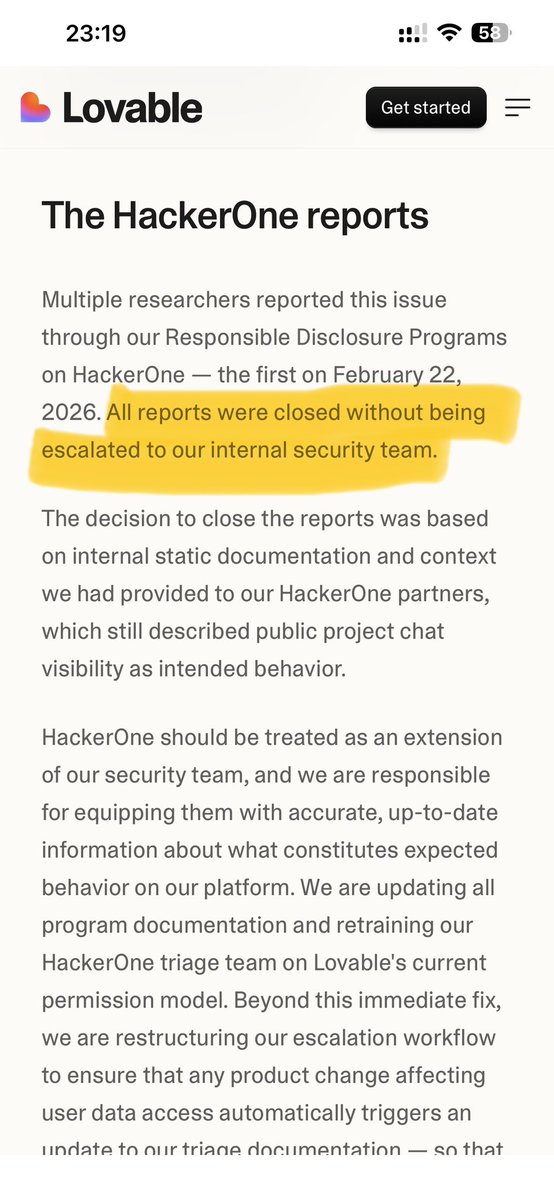
Checklist: - OSCP (Got CTIA & CHFI instead) - 1 CVE (currently in discussion with the company, not that easy but a good start) - 10 legit bugs (Not specific so I got bugs in small companies 😂 need to change the azam) - Talk (Achived talk in 10 local universties last year)