Sabitlenmiş Tweet
simulx4
11.7K posts


simulx4
@simulx4
bioinformatics, the corn & otherwise broadly popular and content that everyone should enjoy. mweb is fine. fintechbro on bsky
Los Angeles, CA Katılım Ekim 2025
281 Takip Edilen687 Takipçiler

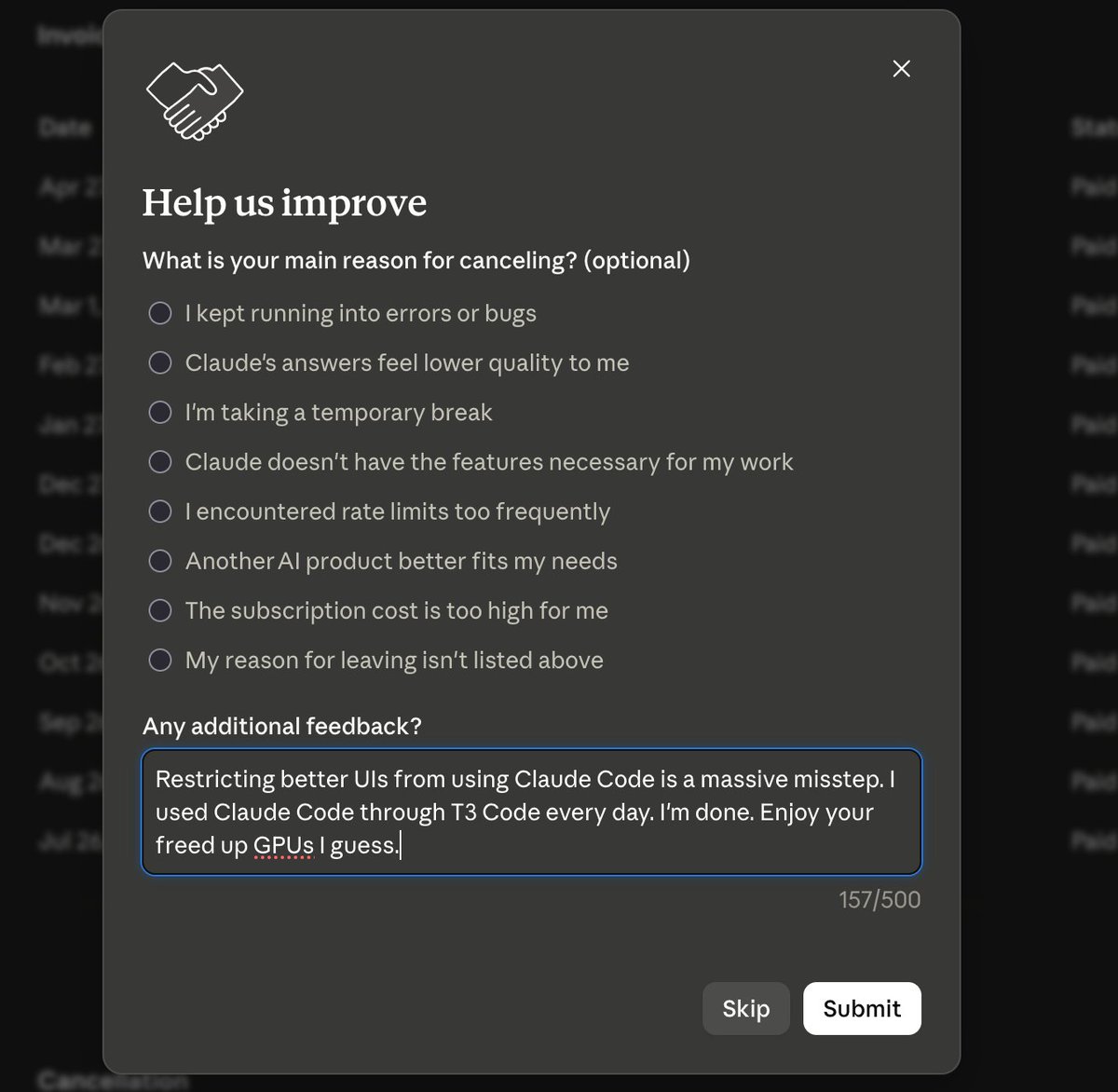
I can't help but feel personally burned by the Claude Code changes announced today.
We put so much work into wrapping the (atrocious) Claude Agent SDK in T3 Code. It was the ONLY path they supported, so we made it work. It was hell.
Now our users are getting their rate limits cut by 40x, despite us doing everything right.
I listened to the Claude Code team. I had my issues with their direction, but I trusted them and took them at their word.
I will never make that mistake again.
Until we see significant change, it is safe to assume any statement from an Anthropic employee is a lie on a timer.
The rug will be pulled, no matter how many promises are made beforehand.
English

If you have this weird gut feeling that the rich pay little tax in the US, your gut is spot on... Source: nytimes.com/interactive/20…
English
simulx4 retweetledi

If you’re an offer owner running your operation with paid ads
You are a G
Few understand or have the balls
To slap your Amex on the table
And attempt to flip $1 into $4 every day
While every natural force is working against you
Trying to tear you down
Yet you prevail
And earn the chance to keep playing the best game there is
Of turning strangers into buyers in 72 hours or less
English
simulx4 retweetledi

@TheChiefNerd he just told everybody what to invest in and nobody is making the move yet
English

@Matthew51045289 @saylor that doesn't explain why I can get a better loan than he can
English

@jarredsumner ask claude to rewrite claude code in rust. we've seen the source. not actually that hard.
English

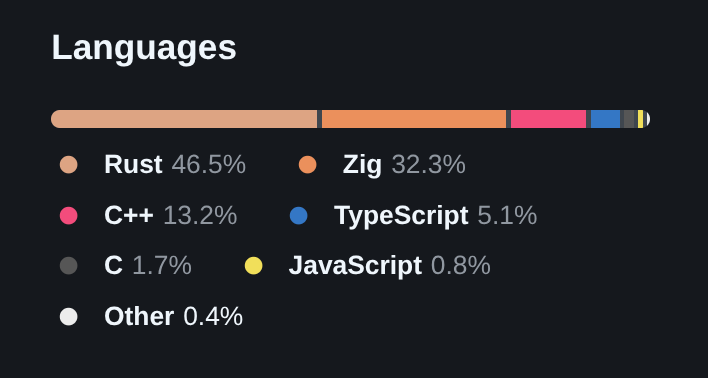
My team is hiring to make Bun and Claude Code faster.
Runtime internals, epoll/kqueue, parsers, JS engine work, long-running agent loop perf. Years of production C/C++/Rust required.
$320k - $485k salary. SF in-person.
job-boards.greenhouse.io/anthropic/jobs…
English