Marcin Szewczyk
1.1K posts
@PUsiadek Całkiem przyzwoity materiał o tym, jak może dojść na drodze ewolucji do sytuacji, gdy finalny efekt jest złożony z kilku współpracujących ze sobą również dość skomplikowanych elementów:
youtube.com/playlist?list=…
Polski
@donald_PL_ Wspaniały prezent dla PiS-u w temacie wymiaru sprawiedliwości. Najpierw dostaje 2 lata, potem 1.5 roku i mówi się o wolnościowych środkach, a na koniec po prostu ucieka, jak kilku poprzednich mistrzów kierownicy...
Polski

@BartoszScheuer Będzie polonez z Pana Ateusza, bo kotek odkopał prezent.
Polski
@rustaceans_rs You're giving him too much credit. Wolverine is a badass character.
English

Rust, Ubuntu and Lunduke moment!

The Lunduke Journal@LundukeJournal
Remember the security firm that Ubuntu hired to audit the (ill-advised, highly buggy) Rust-rewrites of all of the GNU Coreutils? Turns out that security firm is run by @gf_256, who: - Appears to be a man who thinks he's a woman ("trans"). - Uses an anime cartoon of a girl as his avatar. - Appears to have an OnlyFans page. I repeat: Ubuntu hired a "Trans" man, with an anime girl avatar and an OnlyFans page... to audit Rust code. It's hard to get more on-the-nose than that.
Indonesia
@LukeDashjr @brian_pak Yeah. When the trivial exploit code dropped I asked on #debian-security what was the projected timeline. There was none as there were no patches upstream for 6.1 and 6.12.
English

@brian_pak You claim you "waited for the patch to land", but it didn't actually exist or land until April 30th!
Mainline Linux is not what people actually use.
English
@brian_pak That does not seem to match Greg KH's statement:
> Why do you think that we knew this was "imminent"? The CVE team has no such knowlege as no one is obligated to tell us that they are about to let loose a trivial exploit.
openwall.com/lists/oss-secu…
English
@brian_pak You're omitting at least one important fact. Greg KH:
> Why do you think that we knew this was "imminent"? The CVE team has no such knowlege as no one is obligated to tell us that they are about to let loose a trivial exploit.
openwall.com/lists/oss-secu…
English

Thank you for making Linux more secure.
Disclosures like this one have serious real-world implications when downstream distros are still lagging behind on patches.
Did you also share the details with the linux-distros mailing list (or equivalent) under embargo so vendors could prepare backports? How come they weren’t ready upon your disclosure?
English

@xint_official @theori_io Am I safe just because I use a python version does not support os.splice ?
English

Patch your Linux boxes!
Copy.Fail is a trivially exploitable logic bug in Linux, reachable on all major distros released in the last 9 years. A small, portable python script gets root on all platforms.
Found by the teams at @theori_io and @xint_official
More details below
xint.io/blog/copy-fail…
English

@xint_official @theori_io Why tell people to patch when you know their distros don't have fixes because you enabled upstream to obfuscate the vulnerability fix?
The CVE (copy+pasting the fix description, as all Linux CNA CVEs do): @gregkh/" target="_blank" rel="nofollow noopener">lore.kernel.org/linux-cve-anno… makes no mention of any vulnerability.
English
@retrocvnty I enjoyed that one very much. Much more than the Jude Law version.
English
@ErikExplains @kmcnam1 Or a couple of lost bytes indicating we're going into graphics mode now.
English

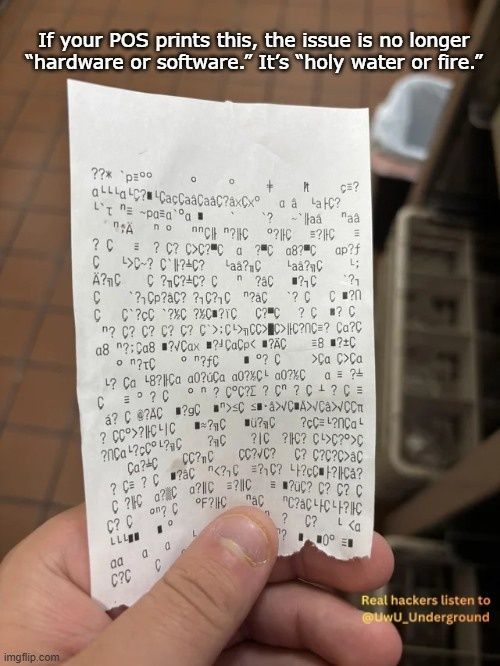
@kmcnam1 Consdering how much of that stuff still runs over RS232 to this day, (or USB pretending to not be RS232 but in reality is emulating RS232, or an Ethernet and TCP/IP stack that winds up feeding RS232), it's probably just a wrong baud rate / word size / partity setting somewhere.
English

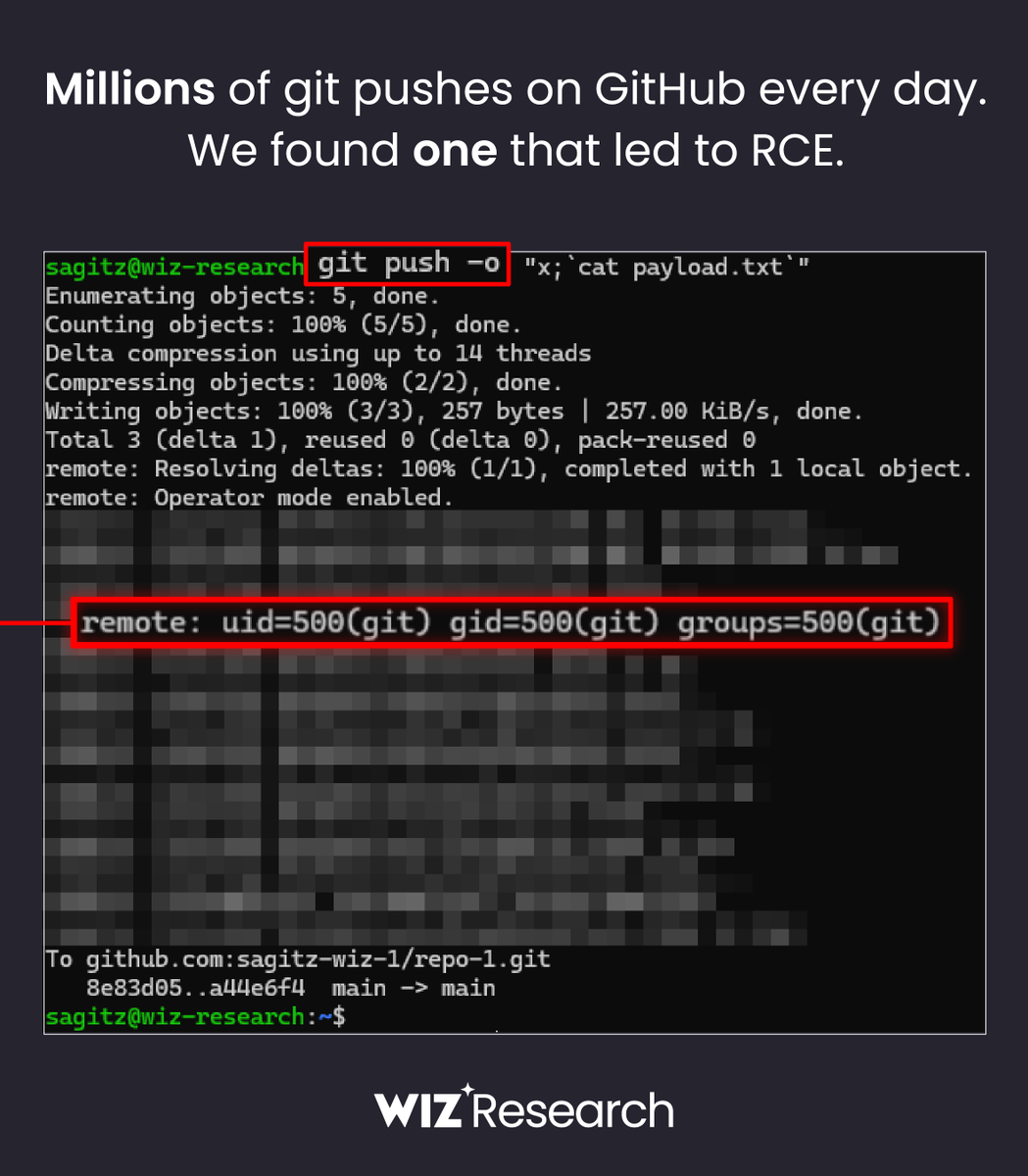
🚨 BREAKING: Wiz Research discovered Remote Code Execution on GitHub.com with a single git push
The flaw in @github allowed unauthorized access to millions of repositories belonging to other users and organizations 🤯
English