uhmm what's going on at @Microsoft, their login experience has been broken for over 24 hours now. The comms team seems to have declared victory and moved on? Am I overreacting, or is this unusually long? I don’t recall problems like this dragging on in the past.
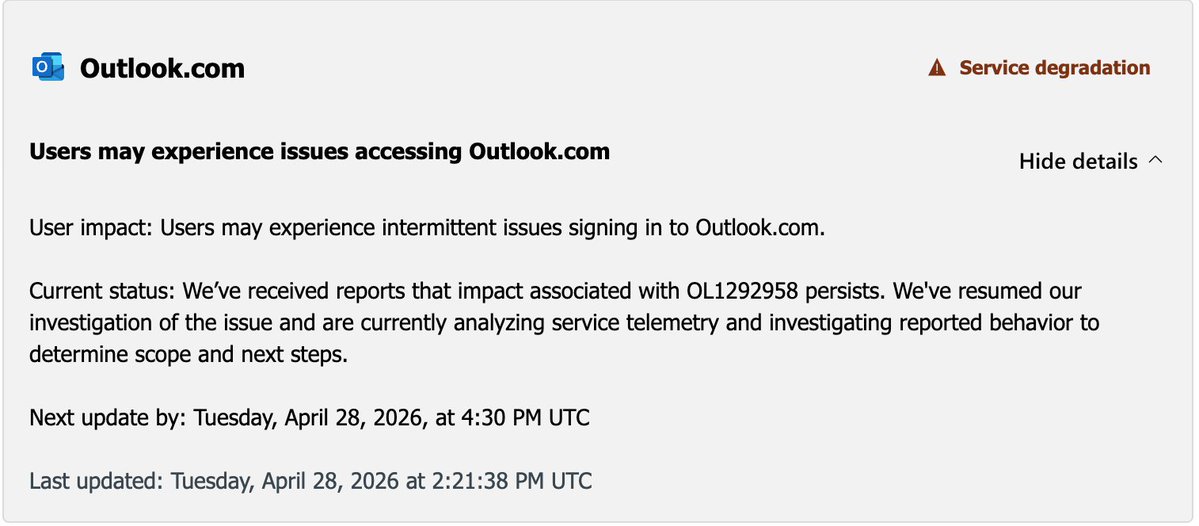
Microsoft 365 Status@MSFT365Status
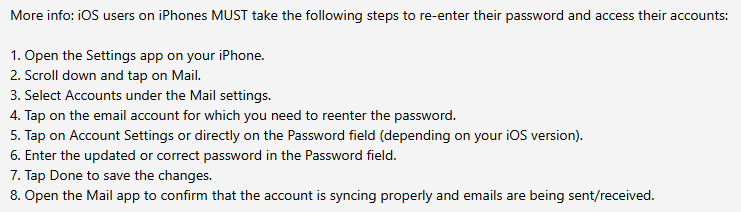
We’ve confirmed service health has returned to normal and reporting users that have completed the additional steps are able to access Outlook and Hotmail. For the list of mitigation steps and more information, please review the attached screenshot or visit status.cloud.microsoft > Microsoft consumer products > Outlook.com.
English