“Transhumanism: The End Game” Short clip of my speech at the ‘Better Way Conference’ held by the World Council for Health earlier this year.
Nathan Petty
103.2K posts


“Transhumanism: The End Game” Short clip of my speech at the ‘Better Way Conference’ held by the World Council for Health earlier this year.

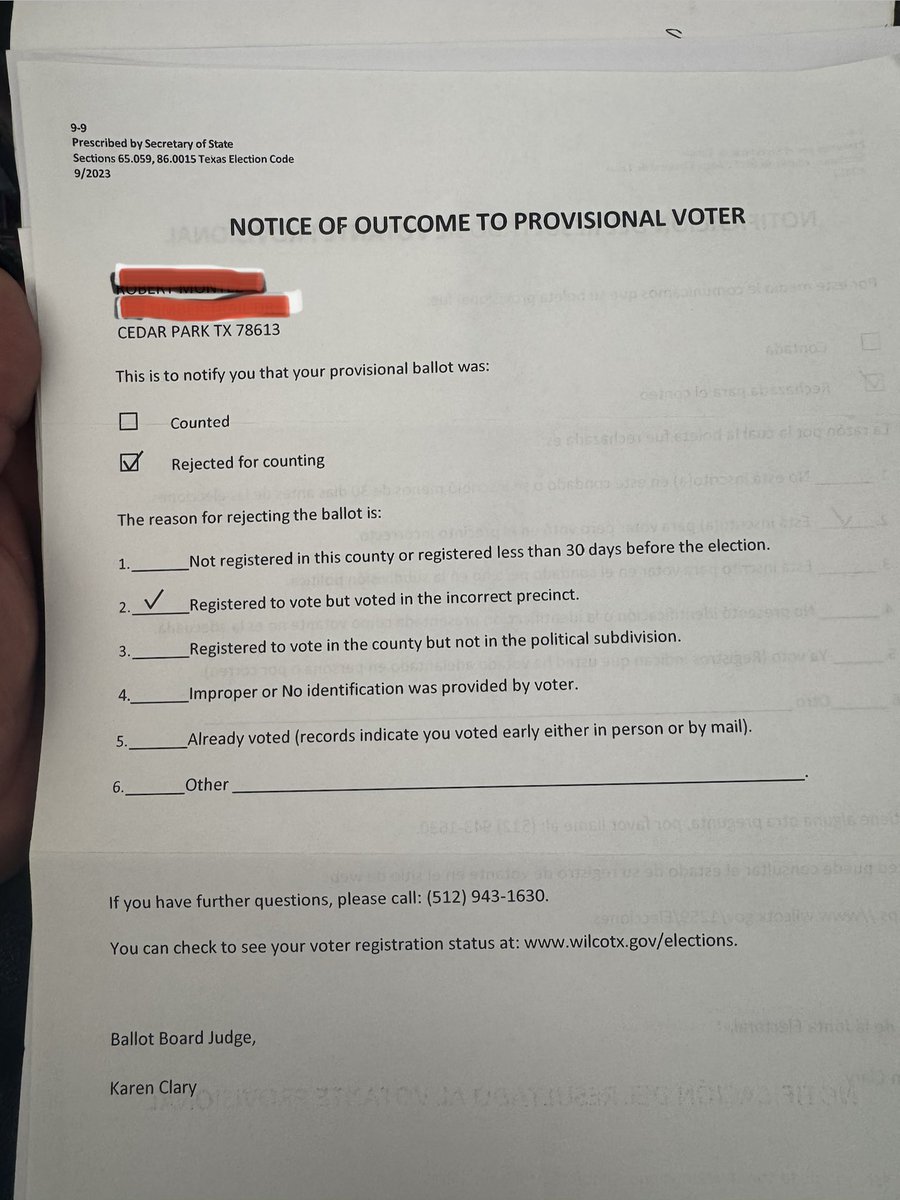
This was one of the many that voted for me in Williamson County. He went to the location he has always voted and was turned away because it was now a Democrat only location. He was told that his location was a few miles away. He went to that location and was allowed to vote. He called me a little after 8 AM on March 3rd, Election Day, asking why he was turned away from the polling place he had always used. I urged him to file a complaint through the @KenPaxtonTX’s office. Apparently his ballot was classified as a provisional even though he cast his ballot in the mid morning hours. I’m just curious if anyone else has received a letter like this. If you have, let me know! My team will be submitting a FOIA to the Secretary of State’s office to determine the number of letters sent out for this reason. If you received a letter like this, dm me on here or email info@matlock4rrc.com.


🚨Mr President @realDonaldTrump: please order for the full content of the "burn bags" that senior FBI officials tried to destroy on Comey/Wray orders, to be published ASAP. Including: the CIA referral of the Hillary plan to destroy you, and Comey's receipt of this plan plus any notes or accompanying docs; Crossfire Hurricane documents, documents from the Durham criminal investigation; J6 documents; the Mar-a-Lago Raid documents. The people deserve to know what Christopher Wray and the FBI leaderships attempted to hide from them and destroy.

🚨 Tweet #17: This email attached was written at midnight. March 30, 2020. Professor Manos Antonakakis was still working. He wrote this to his Defense Advanced Research Projects Agency handlers Christopher Schneck and Ian Crone: "Despite all that, we still have more than enough evidence of what looks to be Russian and Iranian command and control activities from state, local, tribal and territorial government networks that we have analysis that potentially makes them election related." Read that sentence one more time. --Russian command and control activity. --Iranian command and control activity. --Inside state and local government networks. --Networks his own analysis identified as potentially election related. Command and control is not passive observation. It is not reconnaissance. It is not probing. Command and control means a foreign adversary had established an active operating presence inside those networks. Sending instructions. Receiving data. Running operations. From inside networks connected to American elections. And Professor Antonakakis was not uncertain about it. He wrote "more than enough evidence." Not "possible evidence." Not "indicators suggesting." More than enough. Then he wrote something that should make every American stop cold. He compared the people questioning his findings to a doctor who refuses to diagnose a patient because the doctor lacks the right instrument. His exact words: "If they think this is not worth worrying about because they do not have an Albert sensor, then their argument is similar to this statement: I do not have Covid-19 because the doctor didn't have a way to diagnose it." Translation: Someone in the government was telling him his evidence was not valid because it did not come from their own official sensors. He was pushing back. He was telling them: the disease is there whether your instrument sees it or not. Russia and Iran were operating inside election related government networks. Georgia Tech could see it. The government's own sensors could not. Or would not. Now add what Defense Advanced Research Projects Agency Program Manager Ian Crone wrote in the same chain: "That is probably needed to get the Department of Homeland Security to believe us." The Department of Homeland Security. The agency responsible for protecting American elections. The agency that declared 2020 "the most secure election in American history." Defense Advanced Research Projects Agency was struggling to get the Department of Homeland Security to believe their own findings about foreign adversary activity in election networks. And later in the same email chain Antonakakis wrote this: "There is a group that has successfully penetrated these networks." Successfully penetrated. Not attempted. Not probed. Successfully penetrated. The names of who penetrated those networks are hidden behind black redaction bars. To this day nobody outside a classified setting knows whose names are under those bars. Here is the timeline you now have from this thread alone: February 2020 - Defense Advanced Research Projects Agency plans surveillance of voting machine manufacturers. March 2020 - Russian and Iranian command and control confirmed in election related networks. A foreign group confirmed to have successfully penetrated those networks. September 2020 - Defense Advanced Research Projects Agency employee writes "I know who to talk to if we find anything." October 21, 2020 - Dominion Voting egress points found in network data. Same day the man who found them is named to Georgia's official election security task force. November 3, 2020 - You voted. May 2023 - Special Counsel Durham refers the Defense Advanced Research Projects Agency and Georgia Tech contract to the Department of Defense Inspector General for potential criminal investigation. Today: No findings. No charges. No public report. Complete silence. Russia and Iran were inside election related networks. Georgia Tech found them. The Department of Homeland Security declared the election the most secure in history. Durham referred the contract for criminal investigation. Washington went silent. Durham referred the Defense Advanced Research Projects Agency and Georgia Tech contract to the Department of Defense Inspector General for potential criminal investigation in May 2023. It has now been nearly two years. No findings. No charges. No public report. Someone needs to explain that silence. Tag your Senator. @SenRonJohnson @ChuckGrassley More in the morning. Thanks again to @TheAndersPaul for his tenaciousness in obtaining records for five years!



La vidéo de la presse chinoise montrant l’explosion du meeting privé présidé par @netanyahu qui indique sa probable mort à d’abord été interdit du @X aux États Unis et vient d’être interdit sur @XFrance et Europe ! Jusqu’à Quand nos dirigeants vont continuer à nous mentir?


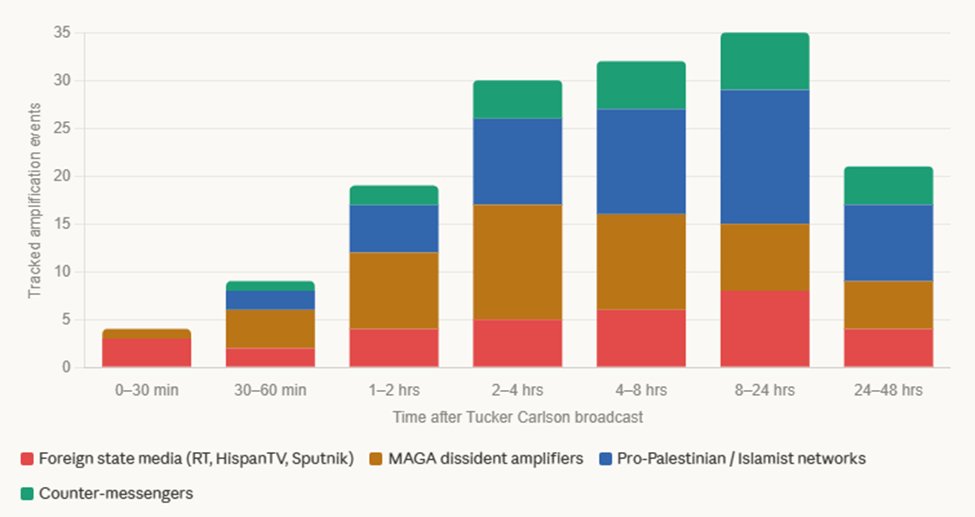
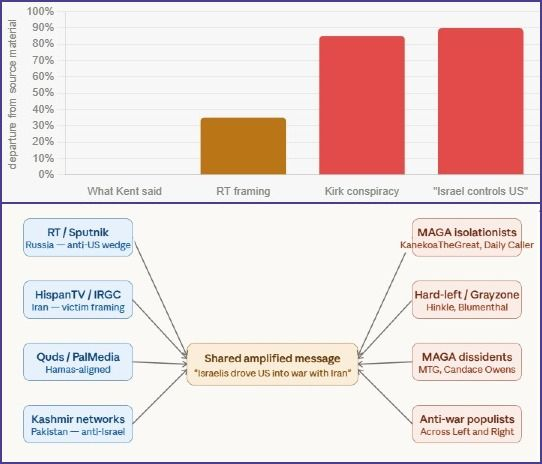
🧵 THREAD: This was coordinated. Joe Kent goes on Tucker Carlson. Within minutes, the exact same clip, same caption, same outrage floods the internet. Not organic. Not coincidence. HonestReporting.ai Labs tracked it in real time. What we found will shock you.

🚨 Tweet #19: In Tweet #18 you saw this line from DARPA Program Manager Ian Crone to Georgia Tech Professor Manos Antonakakis: "Would you, quietly, run an [REDACTED] job and grep for recent state/local/election targets?" The redacted words? Based on every other document in this collection - the DARPA planning agenda, the election devices email, the Army Cyber email chain - the redacted term is almost certainly: "Active DNS" Here is why that matters. And here is why it should terrify us all. Most people think of the internet as a series of protected tunnels. Your data goes in one end encrypted and comes out the other end safely. (And yes, there are numerous configurations) That assumption is wrong when Active DNS Pythia is involved. Let us explain what this tool actually does in plain language. The internet runs on something called the Domain Name System. Think of it as the internet's phone book. Every single device - your phone, your computer, a voting tabulator or EMS in Fulton County Georgia or Milwaukee County Wisconsin - must look up an address before it connects to anything. That lookup is a Domain Name System query. There is no way to use the internet without making Domain Name System queries. None. Probably why communist Nellie Ohr used a ham radio instead of any internet with her Fusion GPS work. Active DNS Pythia was built to capture and analyze every single one of them. Here is what makes it extraordinary - and terrifying. Normal surveillance tools sit at one point and watch traffic pass by. Active DNS Pythia does something fundamentally different. It proactively asks the Domain Name System: "What does every known domain on the entire internet resolve to right now?" -Every day. -Continuously. Building a complete, living map of the entire internet's infrastructure updated daily. Not just what passes one sensor. Everything. Then comes Reverse Mode. This is the capability Defense Advanced Research Projects Agency wanted deployed inside the Department of Homeland Security. Normal mode: Start with a known threat and map its infrastructure outward. Reverse Mode: Pick any target network - a voting machine company, a state election system, a political party - and map every single connection going into it and coming out of it. Who is accessing it. From where. At what time. Through what pathway. On what devices. In a single overnight job Professor Antonakakis identified 292 hand-verified networks linked to the Republican National Committee, the Democratic National Committee, and state and local party committees. He then proposed running Reverse Mode against all of them. Now add the layer that makes encryption irrelevant. Most people believe encryption protects their data. It does to a point - unless the data is being hidden inside Domain Name System queries themselves. This is called Domain Name System tunneling. It works like this: A normal Domain Name System query asks: "What is the address of google . com?" A Domain Name System tunnel query asks: "What is the address of [this-is-actually-stolen-tally-data-encoded-in-the-address-field].server.com?" The actual data is hidden inside the address field of the query itself. Firewalls never block it because it looks like a normal address lookup. Encryption never protects it because the data never gets encrypted — it is smuggled inside the query. The SolarWinds attack used exactly this method. And the documents confirm the Georgia Tech team was specifically analyzing SolarWinds exfiltration using their Active DNS datasets. Meaning they had tools purpose built to detect Domain Name System tunneling - decode it - and read what was inside it. A system designed to detect tunneled data necessarily reads what is being tunneled. You cannot identify it without decoding it. Now add Rodney Joffe's company Neustar. Neustar operated authoritative Domain Name System resolution for large portions of the entire internet. Meaning when a Dominion voting tabulator in Fulton County Georgia made a Domain Name System query to reach an external server - that query very likely physically passed through Neustar's infrastructure before reaching its destination. At that junction Neustar could see: ✅ The full query - source device, destination address ✅ Complete data payload if unencrypted ✅ Traffic patterns and timing if encrypted ✅ Any data encoded inside Domain Name System queries ✅ The exact timing synchronized to election night tally transmission This is not hypothetical. This is the designed function of backbone Domain Name System infrastructure. Now put it all together. Defense Advanced Research Projects Agency funds Georgia Tech to build Active DNS Pythia. Active DNS Pythia gets deployed inside the Department of Homeland Security - the agency that declares elections secure. Voting machine manufacturers are listed as authorized Reverse Mode targets eight months before the election. Ian Crone asks Manos to quietly run an Active DNS job on state and local election targets. Thirteen days before the election egress points are found in Dominion Voting network data. Rodney Joffe - Durham Report "Tech Executive One" - sits in the blind copy field of emails about the same datasets. And Joffe's company Neustar sat at the exact backbone junctions where that election night traffic traversed. This was not a research project. This was the most powerful internet surveillance tool ever built by an American university - pointed directly at the infrastructure of American elections. And the raw data it collected? Still exists. -In the Georgia Tech datasets. -In Neustar's systems. -Waiting to be subpoenaed. ACRONYM DECODER for "To talk about today" email shown here: Defense Advanced Research Projects Agency / Georgia Tech February 26, 2020 EA - Enhanced Attribution. The Defense Advanced Research Projects Agency program funding Georgia Tech to track and identify cyber attackers using internet traffic data. APT 28 - Advanced Persistent Threat 28. The United States government code name for Russian Military Intelligence hacking unit. Also known as Fancy Bear. Delphi - Georgia Tech's surveillance platform. Used to run reverse mode reconnaissance against target networks. NSA - National Security Agency. United States signals intelligence agency. Rev mode - Reverse Mode. Picks a target network and maps every connection going in and out of it. IPv4 - Internet Protocol Version 4. The addressing system that identifies every device connected to the internet. GT LOE - Georgia Tech Level of Effort. Georgia Tech's own separately funded work stream outside standard Defense Advanced Research Projects Agency program oversight. FSARC - Financial Systemic Analysis and Resilience Center. A financial sector cybersecurity organization. ADNS - Active Domain Name System. Georgia Tech's internet-wide surveillance system that maps every domain and connection on the entire internet daily. Pythia - The intelligence and attribution engine built on top of Active Domain Name System. Can identify, track, and decode network connections on any target. DDS - Defense Digital Service. The Pentagon's own internal technology unit. CIS - Center for Internet Security. Connected to the Department of Homeland Security. Responsible for protecting state and local election infrastructure. DHS - Department of Homeland Security. The federal agency that declared the 2020 election "the most secure in American history." CNMF - Cyber National Mission Force. The United States military's offensive and defensive cyber warfare unit. The cyber equivalent of Special Forces. TF Raider - Task Force Raider. A United States military cyber task force designation. Dodin - Department of Defense Information Networks. The entire military's internal computer and communications infrastructure. AR - Active Reconnaissance. Proactive scanning of target networks to identify connected devices, open pathways, and network activity. TTPs - Tactics, Techniques and Procedures. Operational methods used in cyber surveillance and attack operations. PF - Passive Fingerprinting. Identifying devices and systems by observing their network behavior without actively probing them.