

stuxf
45 posts

@stuxfdev
co-founder and ceo @verialabs (yc f25) | hack things @smiley_ctf



Startup School is back! Hear from Jensen Huang, @sama, @alexandr_wang, @JeffDean, and more. Join a hand-selected group of top CS students, researchers, and engineers for two days of talks, sessions with YC partners, and hands-on robotics demos, right here in San Francisco.

I would like to purchase a handful of code problems that modern LLMs can’t solve. Requirements: - programmatically verifiable (can be tested without human interaction) - “before” state (repo before the commit that implements the solution) - example code that actually solves the problem I am willing to pay up to $500 per problem that I can easily test locally and confirm current models (gpt-5.3-codex, opus 4.6) are unable to solve. If you can’t tell, I’m running out of “too hard for LLM” code tasks 🙃🙃🙃








just did another HBOT session 2 atm for 2 hrs the best I've felt in the last few days!




man linux with opencode is so fun everything in linux is cli/api first which means you can configure and automate every little detail too tedious before but very easy now
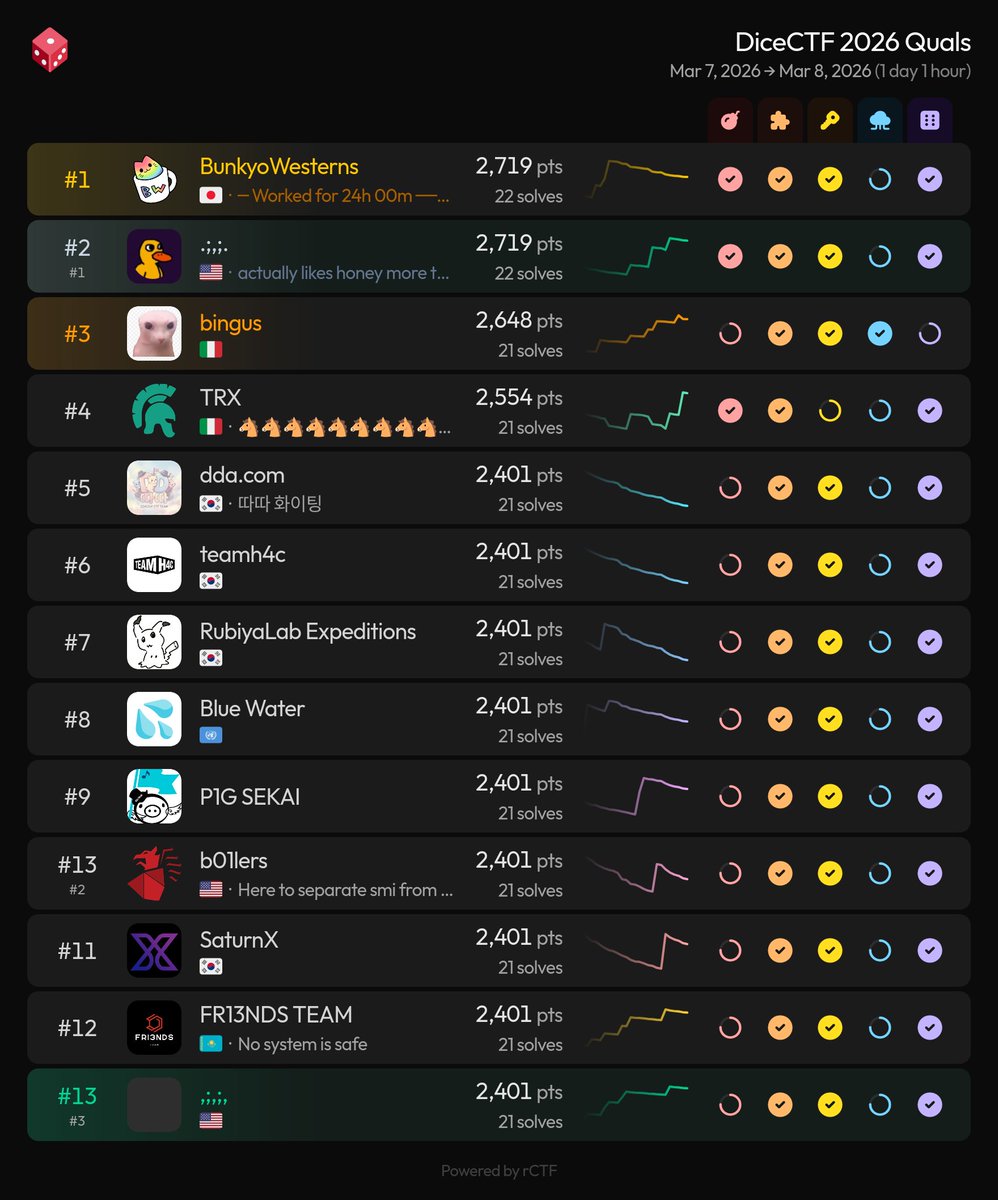
We're officially top 3 in the world on CTFtime for 2025, up from 13th last year! yay This year, we also: - hosted the first ever smileyCTF, with 1,000+ teams playing - went to in-person CTFs in Switzerland, Las Vegas, NYC * 2 - qualified for SECCON and LakeCTF 2026 finals




XBOW sells assessments. CAI builds security capability. Same space. Different model. news.aliasrobotics.com/xbow-vs-cai-as… #Cybersecurity #AI #SecurityAutomation
