mappy
190 posts





Calling all security researchers. @Anthropic’s bug bounty program is now public on HackerOne. The community has already helped strengthen Anthropic’s products through private testing. Now, anyone can help secure the future of AI. 🔐

JUST IN: Cloudflare lays off 1,100+ employees through email as it restructures for the “agentic AI era.”




Our security bug bounty program is now public on HackerOne. We've run the program privately within the security research community, and their findings have strengthened our products. Now anyone can report vulnerabilities and get rewarded. Read more: hackerone.com/anthropic



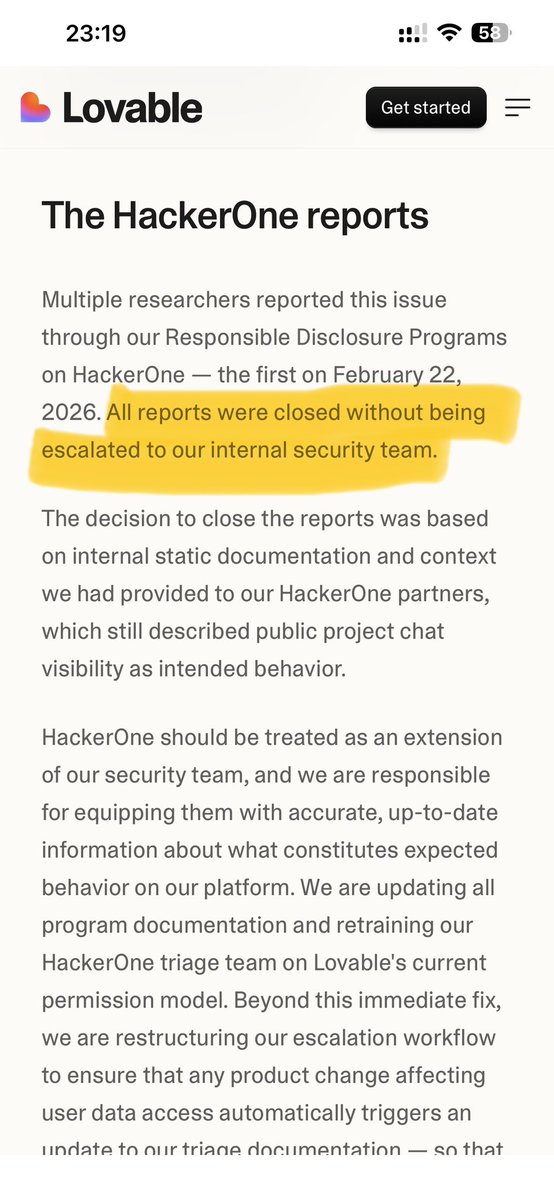
Regarding the recent public disclosure vs private email debate… Here’s what I’ve actually experienced as a security researcher: - A company quietly removed its public self-hosted bug bounty program (that had safe harbour) and the ciso personally threatened me with “no safe harbour” after I submitted a valid report. (minimal testing was done) I’ve emailed hundreds of companies. a) Most open the email and completely ignore it. b) Some silently patch and ghost so they don’t have to pay a bounty. The worst part? Some of these companies run critical infrastructure and hold massive amounts of PII. Even when the security team replies, they’re friendly and responsive… right up until you ask, "Do you offer any bounty?" Full report submitted = instant ghosting. Companies that do have a bug bounty program still try to weasel out of paying by saying "this is out of scope", even when the vuln literally exposes their entire source code or production database. This piggybacking behaviour has to stop. So… should I just start calling out the names publicly? Is that how issues need to be fixed right now? Because the current system is broken #hackerone #bugcrowd #bugbounty


Introducing SubQ - a major breakthrough in LLM intelligence. It is the first model built on a fully sub-quadratic sparse-attention architecture (SSA), And the first frontier model with a 12 million token context window which is: - 52x faster than FlashAttention at 1MM tokens - Less than 5% the cost of Opus Transformer-based LLMs waste compute by processing every possible relationship between words (standard attention). Only a small fraction actually matter. @subquadratic finds and focuses only on the ones that do. That's nearly 1,000x less compute and a new way for LLMs to scale.



Microsoft confirms Windows Run dialog is getting a modern look on Windows 11! - Modern design: A refreshed look that matches Fluent Design and Windows 11, with dark mode support. - Faster than before: Perf was top-of-mind when rewriting Run, and with a **94ms median time-to-show time it’s faster than ever before. - Quick user directory access: You can now type ~\ to jump to your user directory, then keep navigating just like you would from the command line. The modern Run dialog is slowly rolling out in current Insider builds of Windows as an opt-in feature, ensuring we are collecting your feedback. To enable the new Run dialog, you’ll need to: - Be on Windows Insider Experimental Channel. - Enable to Settings -> System -> Advanced and toggle on the new experience with the “Run Dialog” option at the top of the screen.