

ICPsimp ☁️∞
8.6K posts


@ICPsimp
Just love me some good tech and innovation. $ICP But I don't know shit about shit. Just here to provide out of touch takes.





THORChain incident update #1 THORChain contributors shared a new update in the dev discord regarding the ongoing incident. TLDR - Current evidence points toward a newly churned node linked to the attack, likely operated by a single malicious actor - The leading theory is an exploit in the GG20 TSS implementation, allowing vault key material to leak over time. The attacker may have reconstructed the vault private key and executed unauthorized outbound txs - Current network status: -- The network is paused after multiple node operators executed make pause -- RUNE transfers and chain observation may resume within ~12h unless decided otherwise by the nodes. -- Trading, LP actions, signing, and sensitive operations remain paused for now - Recovery discussions currently include slashing affected node bonds, using POL to absorb losses, or other community-driven solutions The investigation is still ongoing alongside THORSec and Outrider Analytics. ## Full Announcement ## Developers and THORSec have been investigating today’s incident continuously throughout the day. While new information may still emerge, I want to provide the community with an update based on what we currently know. The goal of this update is to clarify the current understanding of the situation as accurately and transparently as possible. A newly churned node, thor16ucjv3v695mq283me7esh0wdhajjalengcn84q, which entered the network several days ago, is currently believed to be associated with the attack. Developers have identified links between Ethereum addresses used to acquire and bond RUNE for this node, and Ethereum addresses that later received the stolen funds. Based on current evidence, it is believed this was conducted by a single malicious operator, though the investigation remains ongoing. At this time, the leading theory is the attacker exploited a vulnerability within the GG20 TSS implementation which allowed sensitive key material from vault participants to leak over time. By accumulating enough leaked information, the attacker was ultimately able to reconstruct the vault’s TSS private key and execute unauthorized outbound transactions. The Treasury is actively collecting forensic data and coordinating with Outrider Analytics and relevant law enforcement agencies in an effort to identify the attacker and pursue recovery of stolen funds where possible. Due to multiple node operators executing make pause, the network is currently paused. Unless further action is taken, the pause state will automatically expire in approximately 12 hours. At this time, the development team is comfortable allowing the pause to expire in order to restore RUNE transfers and chain observation activity. However, trading, signing, LP actions, and other sensitive operations will remain paused until the network and community align on a comprehensive recovery and remediation plan. The recovery process will likely require node governance decisions regarding how losses are ultimately handled. Several potential approaches are already being discussed, including: Slashing the bond of nodes participating in the affected vault Allowing Protocol-Owned Liquidity (POL) to absorb the loss Additional recovery proposals that may emerge from the broader community At this stage, no final decisions have been made. The team is continuing to work on a complete recovery and restart plan for the network. Bringing trading and full functionality back online will likely take several days, and potentially longer depending on the complexity of the chosen remediation path. We will continue to provide updates as more information becomes available. Finally, I want to thank the developers, node operators, security contributors, and the broader THORChain community for the enormous amount of work done today. One of THORChain’s greatest strengths has always been the community’s ability to come together under pressure, collaborate quickly, and solve difficult problems together.


ASP.NET Core + Blazor Static SSR running on the Internet Computer mainnet with .net 10. The .wasm file is at the limit with 11mb. The /post take a second or two, but hey, it's working 4dcfc-hyaaa-aaaas-qdqbq-cai.icp0.io Let see how long will the 8T cycles last :D $ICP $Microsoft


Nearly every solopreneur, startup, SME, enterprise or government department, will want to become an agentic organization (or "cybernetic org"). They will be vastly smarter, faster and more efficient. Internet Computer Protocol (ICP) helps enable this brave future. But how? 🧵


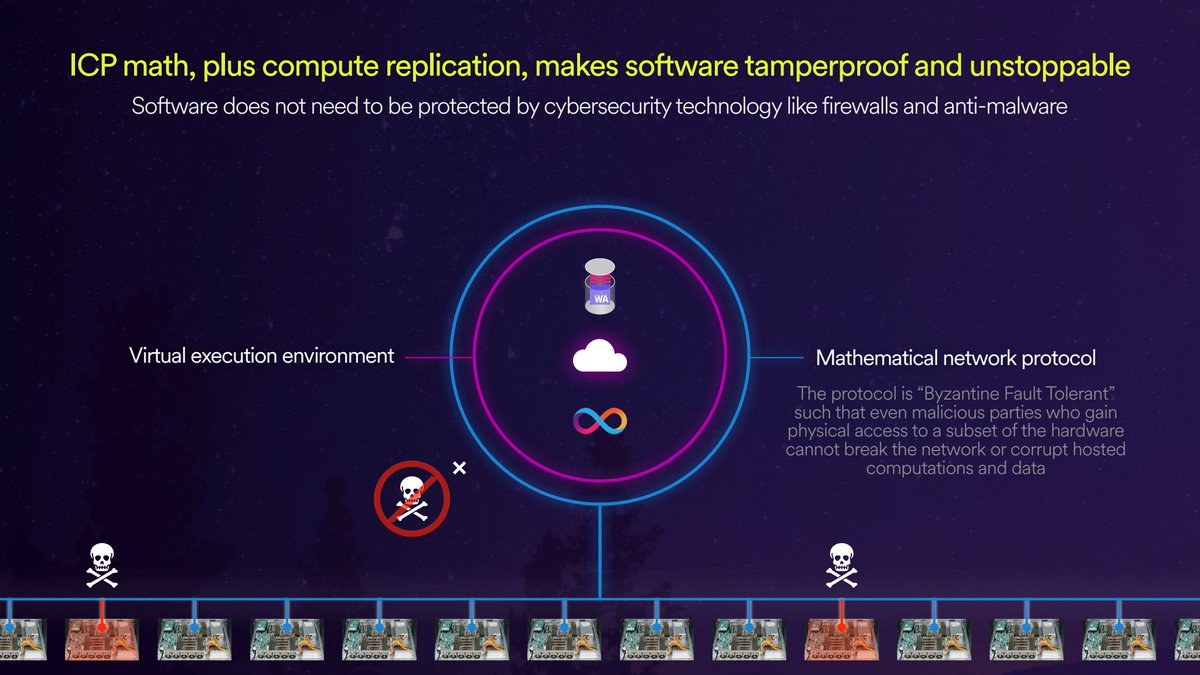
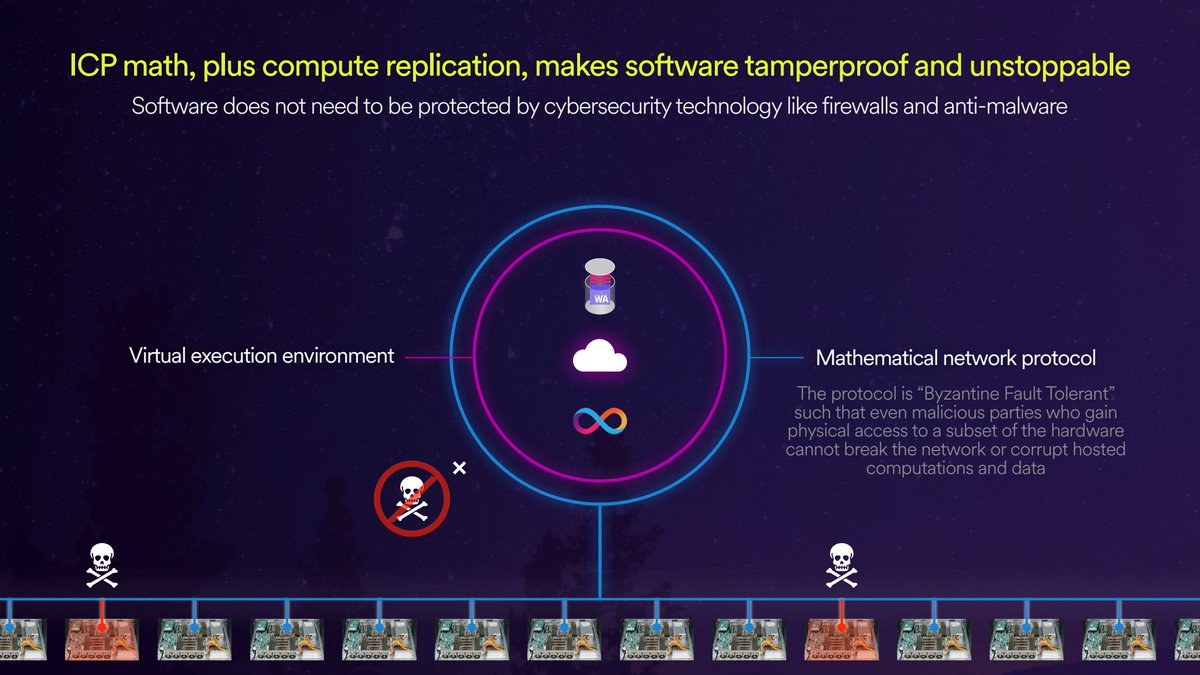
A cloud engine is a sovereign frontier cloud. Tamperproof. Fault-tolerant. Yours. → No vulnerable OS → No firewall to maintain → No sysadmin required Protocol math keeps your app running even when nodes fail. opencloud.org





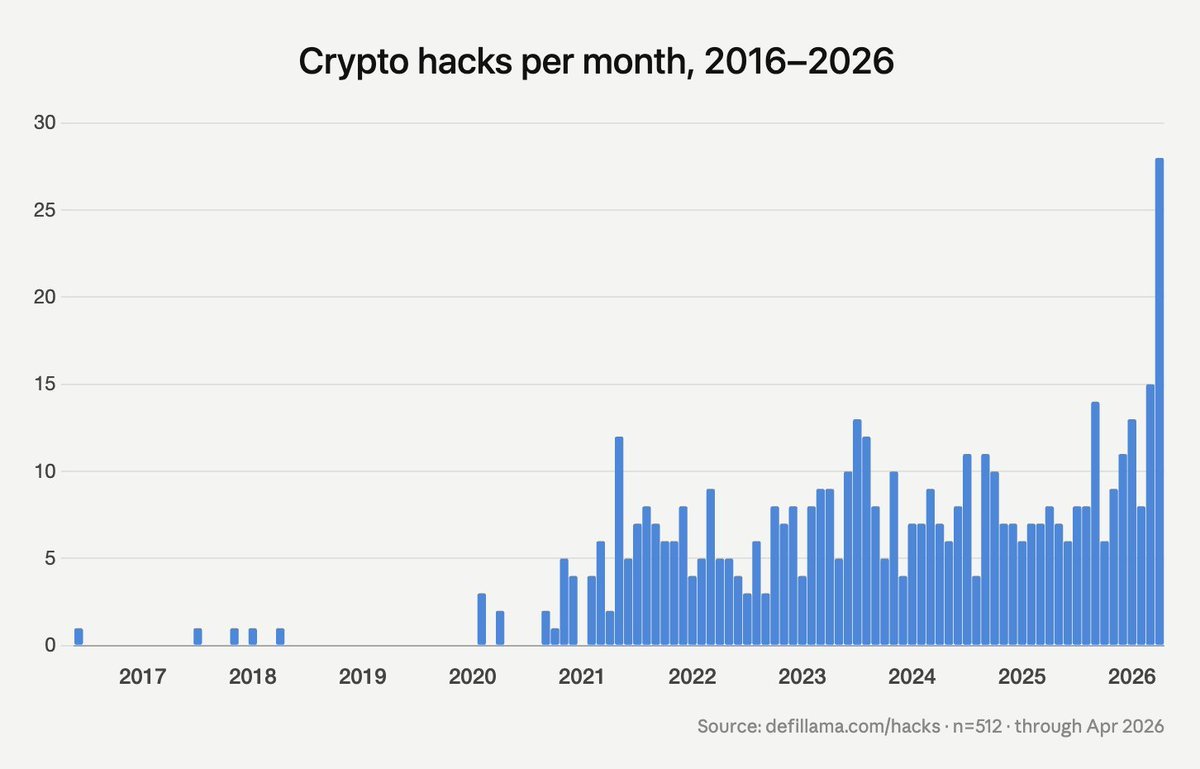
The future of DeFi is bright

DNS hijacks are spiking in crypto. CoW Swap and eth (dot) limo were both hit. You visit a frontend, everything looks normal, you sign a transaction and funds go to an attacker's wallet. The defense isn't better detection. It's frontends that STRUCTURALLY can't be cracked. Two approaches already exist: > IPFS + ENS: Your frontend lives on a distributed file network instead of a server. Point your web3 domain (ENS) at that file. No DNS, no central server to compromise > Fully onchain (ERC-4804): The app itself lives inside smart contracts. The frontend is served directly from Ethereum Sadly though, regular browsers can't load either. That’s why we have web3 browsers like: > Freedom Browser: open-source browser that loads ENS domains and IPFS sites natively, the same way Chrome loads (dot) com addresses > EVM Browser: built around the web3:// protocol, loads apps served directly from smart contracts on Ethereum or any EVM chain The proof of concept is already live. @z0r0zzz built zSwap is a DEX frontend deployed ENTIRELY into Ethereum contract bytecode for under $5. Anyone can load it through EVM Browser. In other words: No servers, No DNS, Nothing to hack. Every DeFi project should ship a permanent onchain frontend as a fallback. Best security is just to go straight to the contract. The tools exist. Build toward it.


