marzelina.eth aka KahLess
1.4K posts


marzelina.eth aka KahLess
@Marzycha
Looking to the Future, I'm Passionate About Pushing the Boundaries of What's Possible in Tech 💥 Let's Create the Next Big Thing!









looks like yet another exploit in the wild, 0x7E5433F02F4bf07C4f2a2D341C450E07d7531428 contract just stole 14 bored apes and 36 pudgy penguins

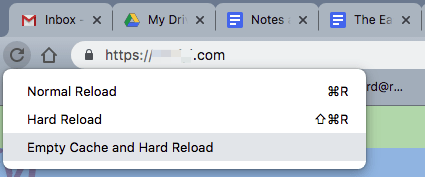
FINAL TIMELINE AND UPDATE TO CUSTOMERS: 4:49pm CET: Ledger Connect Kit genuine version 1.1.8 is being propagated now automatically. We recommend waiting 24 hours until using the Ledger Connect Kit again. The investigation continues, here is the timeline of what we know about the exploit at this moment: - This morning CET, a former Ledger Employee fell victim to a phishing attack that gained access to their NPMJS account. - The attacker published a malicious version of the Ledger Connect Kit (affecting versions 1.1.5, 1.1.6, and 1.1.7). The malicious code used a rogue WalletConnect project to reroute funds to a hacker wallet. - Ledger’s technology and security teams were alerted and a fix was deployed within 40 minutes of Ledger becoming aware. The malicious file was live for around 5 hours, however we believe the window where funds were drained was limited to a period of less than two hours. - Ledger coordinated with @WalletConnect who quickly disabled the the rogue project. - The genuine and verified Ledger Connect Kit version 1.1.8 is now propagating and is safe to use. - For builders who are developing and interacting with the Ledger Connect Kit code: connect-kit development team on the NPM project are now read-only and can’t directly push the NPM package for safety reasons. - We have internally rotated the secrets to publish on Ledger’s GitHub. - Developers, please check again that you’re using the latest version, 1.1.8. - Ledger, along with @Walletconnect and our partners, have reported the bad actor’s wallet address. The address is now visible on @chainalysis. @tether has frozen the bad actor’s USDT. - We remind you to always Clear Sign with your Ledger. What you see on the Ledger screen is what you actually sign. If you still need to blind sign, use an additional Ledger mint wallet or parse your transaction manually. - We are actively talking with customers whose funds might have been affected, and working proactively to help those individuals at this time. - We are filing a complaint and working with law enforcement on the investigation to find the attacker. - We’re studying the exploit in order to avoid further attacks. We believe the attacker’s address where the funds were drained is here: 0x658729879fca881d9526480b82ae00efc54b5c2d Thank you to @WalletConnect, @Tether_io, @Chainalysis, @zachxbt, and the whole community that helped us and continue to help us identify and solve this attack. Security will always prevail with the help of the whole ecosystem.


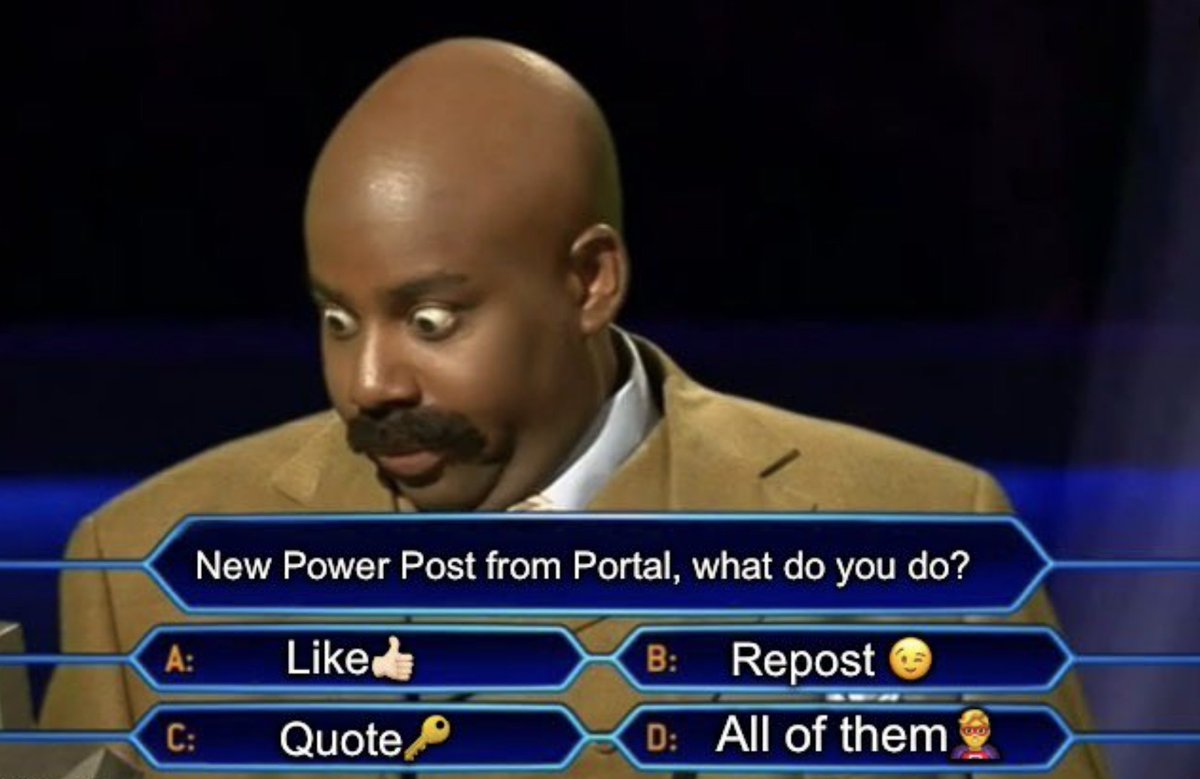
Portal is connecting all games on all chains, then bringing them to the mainstream. Our integrations with @Solana, @0xPolygon, @Avax, and @Klaytn are crucial steps to uniting Web3 gaming with a single cross-chain gaming platform. 🧵1/3



Portal is connecting all games on all chains, then bringing them to the mainstream. Our integrations with @Solana, @0xPolygon, @Avax, and @Klaytn are crucial steps to uniting Web3 gaming with a single cross-chain gaming platform. 🧵1/3


Portal is connecting all games on all chains, then bringing them to the mainstream. Our integrations with @Solana, @0xPolygon, @Avax, and @Klaytn are crucial steps to uniting Web3 gaming with a single cross-chain gaming platform. 🧵1/3

Portal is connecting all games on all chains, then bringing them to the mainstream. Our integrations with @Solana, @0xPolygon, @Avax, and @Klaytn are crucial steps to uniting Web3 gaming with a single cross-chain gaming platform. 🧵1/3