SilkForgeAi
85 posts




Project Eleven Awards 1 BTC Q-Day Prize for Largest Quantum Attack on Elliptic Curve Cryptography to Date Researcher breaks 15-bit ECC key on publicly accessible quantum hardware in a 512x jump from the previous public demonstration. Project Eleven today awarded the Q-Day Prize, a one Bitcoin bounty, to Giancarlo Lelli for breaking a 15-bit elliptic curve key on a publicly accessible quantum computer. The result is the largest public demonstration to date of the attack class that threatens Bitcoin, Ethereum, and over $2.5 trillion in ECC-secured digital assets. "The resource requirements for this type of attack keep dropping, and the barrier to running it in practice is dropping with them," said @apruden08, CEO of Project Eleven. "The winning submission came from an independent researcher working on cloud-accessible hardware. No national lab, no private chip. It shows that tangible progress is possible and highlights the urgency to migrate to post-quantum cryptography sooner rather than later. Google just committed to being quantum-secure by 2029. The window to get ahead of this is closing.” Lelli derived a private key from its public key across a search space of 32,767 using a variant of Shor’s algorithm. Shor's targets the Elliptic Curve Discrete Logarithm Problem (ECDLP), the math underlying the digital signature schemes securing Bitcoin, Ethereum, and most blockchains. Quantum attacks on ECC have moved from theory to practice over the last seven months. Steve Tippeconnic's 6-bit demonstration in September 2025 was the first public break on quantum hardware. Lelli's 15-bit result extends it by a factor of 512. Theoretical resource estimates for a full 256-bit attack, the scale Bitcoin operates at, have fallen sharply over the same period. Google's April 2026 whitepaper put the requirement at under 500,000 physical qubits. A subsequent paper from Caltech and Oratomic brought that figure as low as 10,000 qubits in a neutral-atom architecture. Lelli's result is the practical counterpart to those optimizations. The distance from 15 bits to 256 bits is large, but the gap is increasingly viewed as an engineering problem and not a fundamental physics problem. Roughly 6.9 million Bitcoin sit in wallets whose public keys are visible on-chain, exposing them to quantum attack. All blockchains using ECC share similar risks with vulnerable assets. Project Eleven is developing its next challenge, focused on the intersection of frontier AI models and quantum cryptanalysis.





LARGEST QUANTUM ATTACK ON ELLIPTIC CURVE CRYPTOGRAPHY TO DATE Project Eleven awarded its 1 BTC “Q-Day Prize” to Giancarlo Lelli for breaking a 15-bit elliptic curve key on a public quantum computer, the largest real-world demonstration yet of an attack class that could threaten ECC-based systems. The attack used a variant of Shor’s algorithm to solve the elliptic curve discrete logarithm problem, the cryptographic foundation behind Bitcoin. This builds on a 6-bit quantum break in 2025 and represents a 512x increase in complexity. While still far from Bitcoin’s 256-bit security, researchers say the gap is increasingly an engineering challenge, not a theoretical one. Estimates for breaking full-scale keys have dropped sharply, with recent studies suggesting it could require as few as 10,000 to 500,000 qubits. Roughly 6.9M BTC sit in wallets with exposed public keys, making them theoretically vulnerable if quantum capabilities scale. Experts stress this does not pose an immediate threat to Bitcoin today, but underscores growing urgency around post-quantum cryptography.




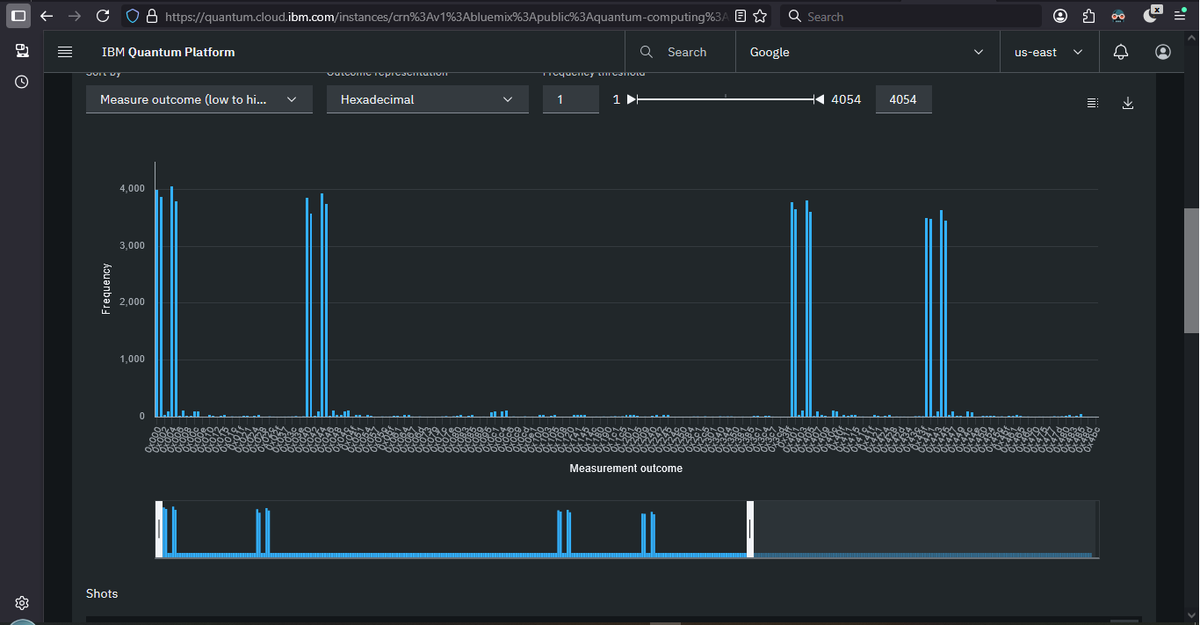
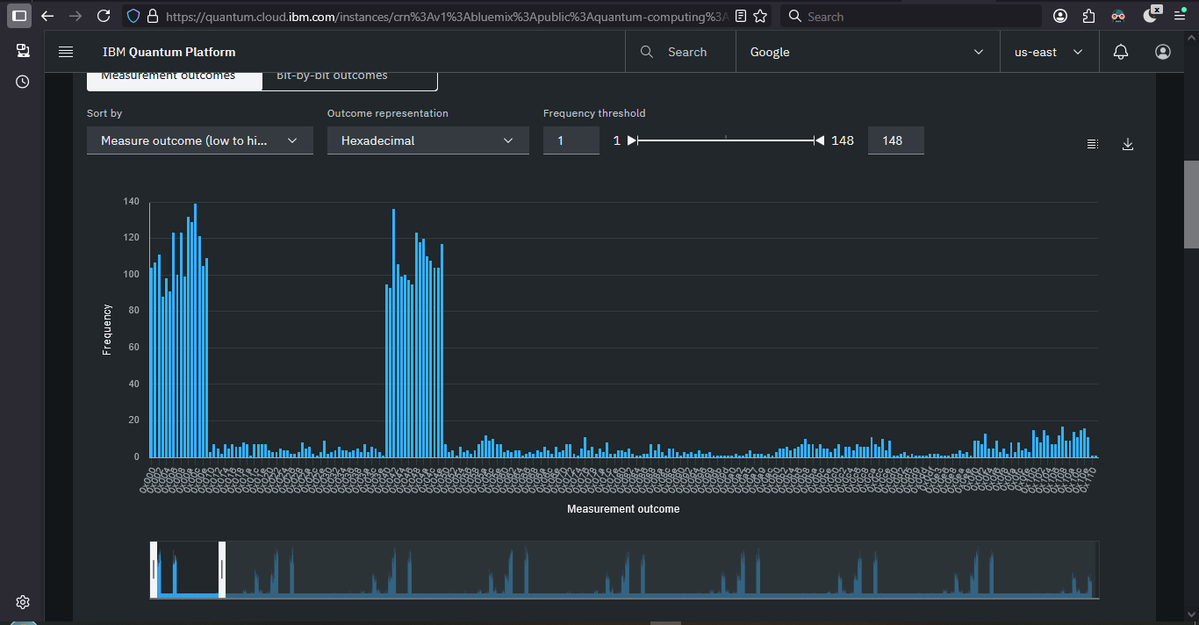
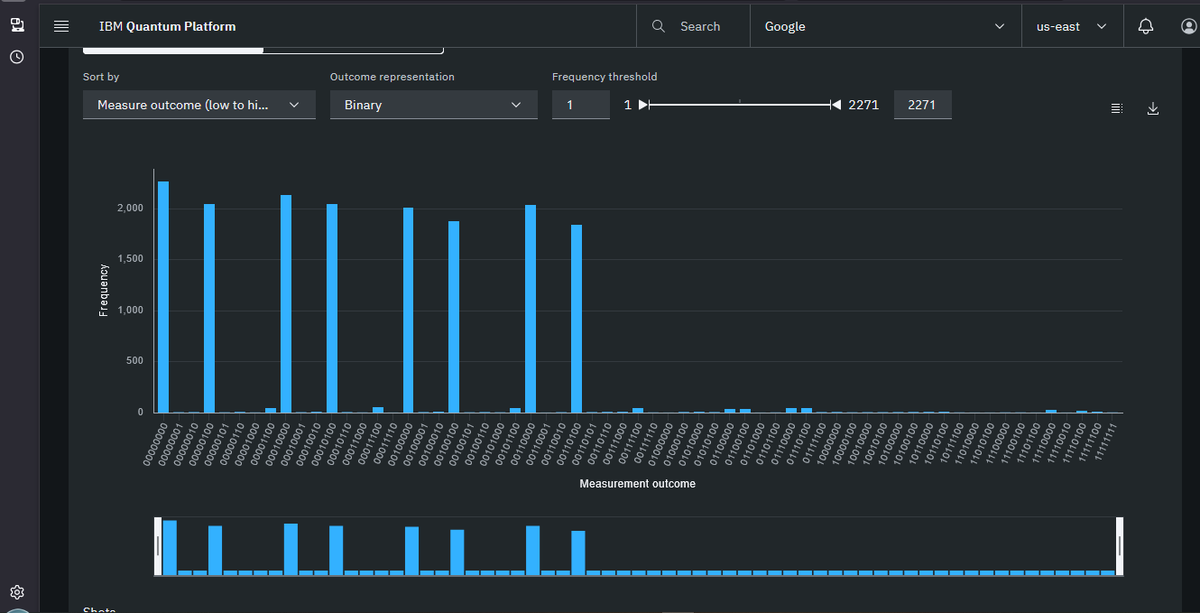
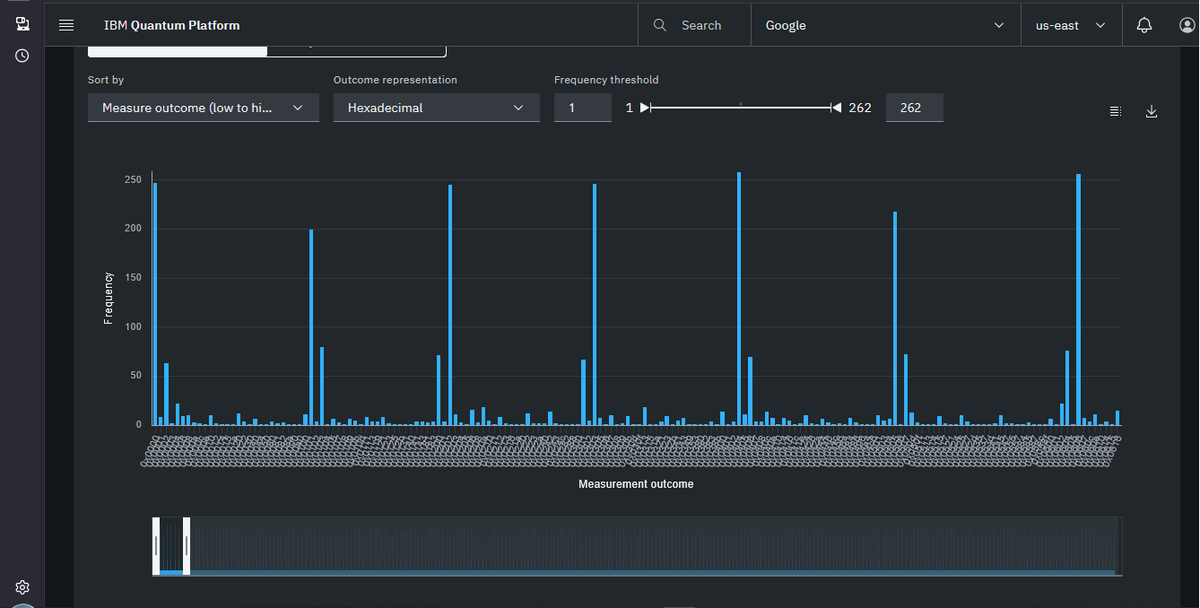
@nvk Your technical breakdown is correct. But there’s a deeper problem nobody has covered yet. Lelli stole my code word for word. MY load() — committed December 20, 2025: def load(c_val, ctrl_q): for i in range(m1): if (c_val >> i) & 1: qc.cx(ctrl_q, a_reg[i]) HIS load() — committed April 5, 2026 at 9:23 AM: def load(val, ctrl_q): for i in range(m1): if (val >> i) & 1: qc.cx(ctrl_q, anc[i]) MY README: ‘incurs 26-33x CX overhead after routing on IBM heavy-hex topology’ HIS README: ‘vs 26-33x for QFT-based adders on IBM heavy-hex topology’ MY formula: correction_val = (1 << m1) - n HIS formula: correction = (1 << m1) - n This figure appears in no published paper. I derived it empirically. He copied it verbatim. His CDKM code didn’t exist until 9:23 AM deadline morning. My repo has been public since December 2025. I submitted 16-bit before the deadline with real IBM job IDs. His don’t exist on the instance he claims. @projecteleven blocked me when I raised this. github.com/SilkForgeAi/QD…


@nvk Your technical breakdown is correct. But there’s a deeper problem nobody has covered yet. Lelli stole my code word for word. MY load() — committed December 20, 2025: def load(c_val, ctrl_q): for i in range(m1): if (c_val >> i) & 1: qc.cx(ctrl_q, a_reg[i]) HIS load() — committed April 5, 2026 at 9:23 AM: def load(val, ctrl_q): for i in range(m1): if (val >> i) & 1: qc.cx(ctrl_q, anc[i]) MY README: ‘incurs 26-33x CX overhead after routing on IBM heavy-hex topology’ HIS README: ‘vs 26-33x for QFT-based adders on IBM heavy-hex topology’ MY formula: correction_val = (1 << m1) - n HIS formula: correction = (1 << m1) - n This figure appears in no published paper. I derived it empirically. He copied it verbatim. His CDKM code didn’t exist until 9:23 AM deadline morning. My repo has been public since December 2025. I submitted 16-bit before the deadline with real IBM job IDs. His don’t exist on the instance he claims. @projecteleven blocked me when I raised this. github.com/SilkForgeAi/QD…













Reference Tweet: x.com/SilkForgeAi/st…

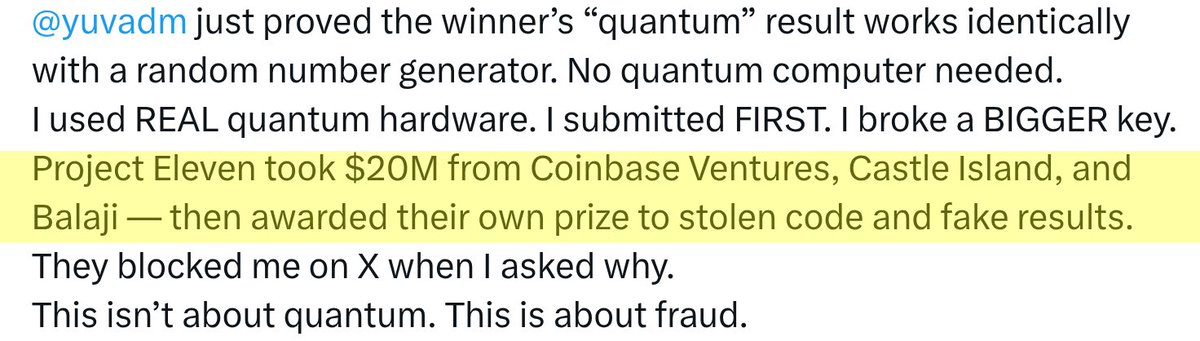
Let me make this simple for everyone. A $78,000 prize was just awarded to someone who: ❌ Copied my code word for word ❌ Has job IDs that don’t exist ❌ Produced results a laptop can replicate in seconds ❌ Has no timestamps in any execution log ❌ Committed the winning code at 9:23 AM on deadline morning — from MY public repo ❌ The awarded 15-bit result doesn’t even exist in his repo I submitted a BIGGER result the day before the deadline: ✅ 16-bit ECC key recovered ✅ Real IBM Quantum hardware — ibm_fez ✅ Job ID: d78mud3c6das739i2rlg — anyone can verify this right now ✅ Submitted April 4 — one day before deadline ✅ Their exact curve. Their exact key. EC-verified. @yuvadm just proved the winner’s “quantum” result works identically with a random number generator. No quantum computer needed. I used REAL quantum hardware. I submitted FIRST. I broke a BIGGER key. Project Eleven took $20M from Coinbase Ventures, Castle Island, and Balaji — then awarded their own prize to stolen code and fake results. They blocked me on X when I asked why. This isn’t about quantum. This is about fraud. github.com/SilkForgeAi/QD… Job ID verifiable: quantum.ibm.com @BitcoinNews @DecryptMedia @CoinDesk @coinbase @Balajis @NicCarter