DRAGONIQUE Aimen
67 posts


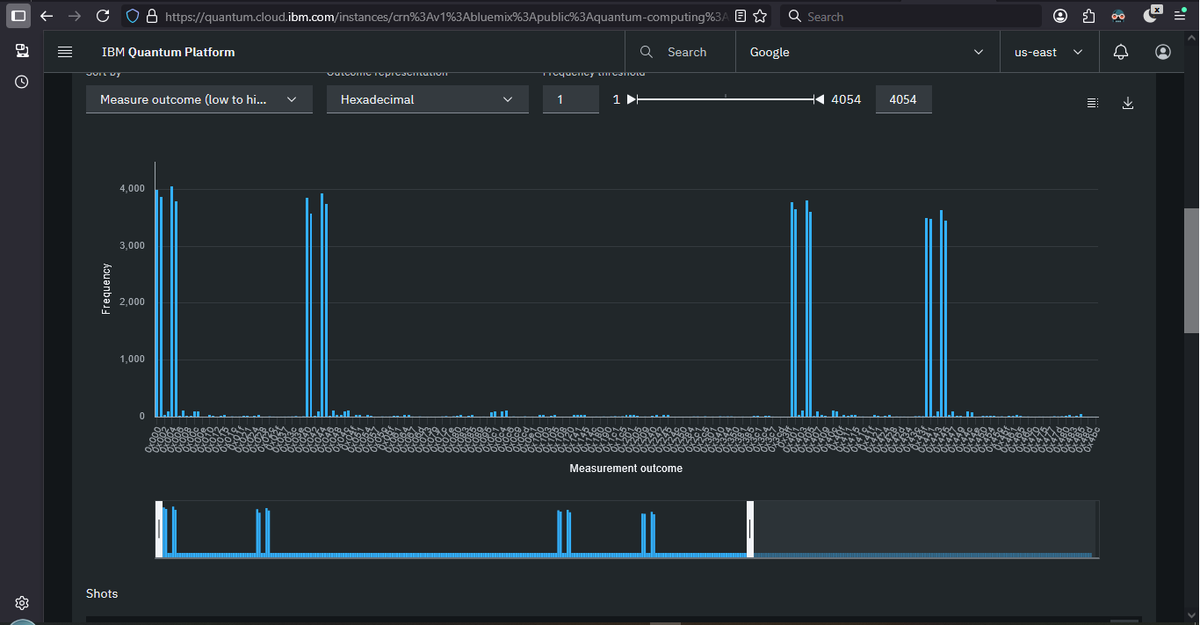
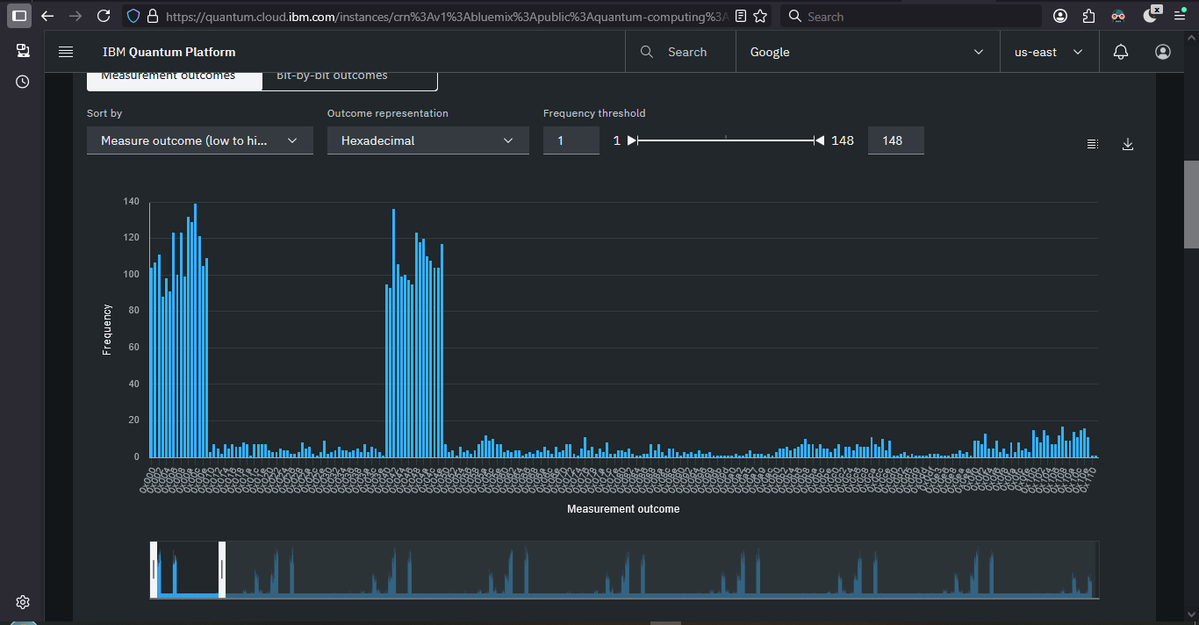
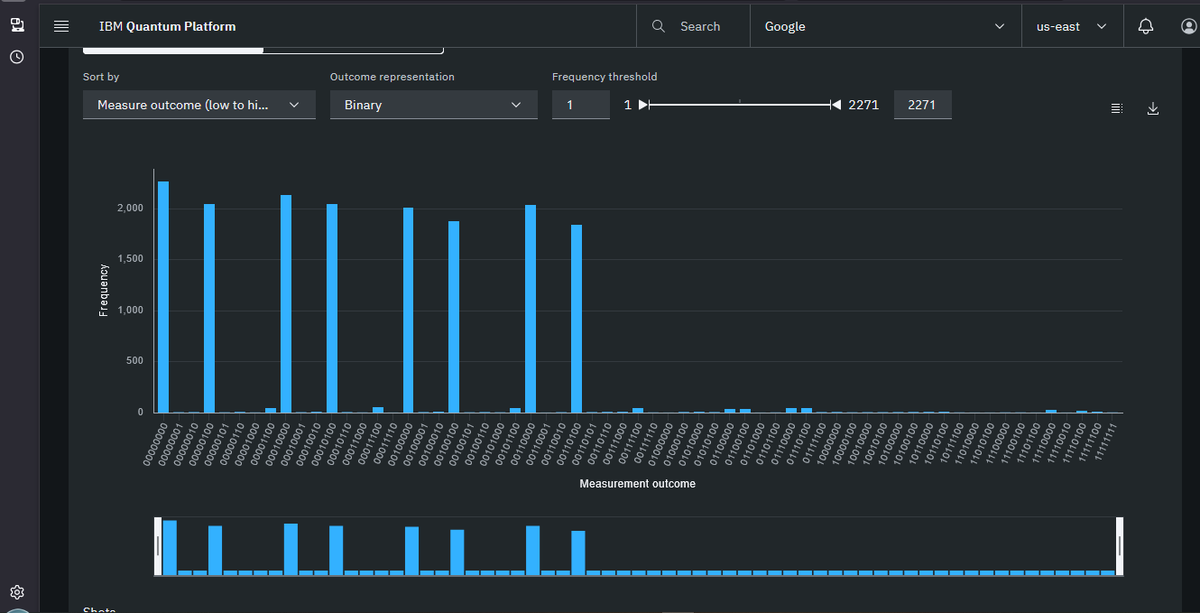
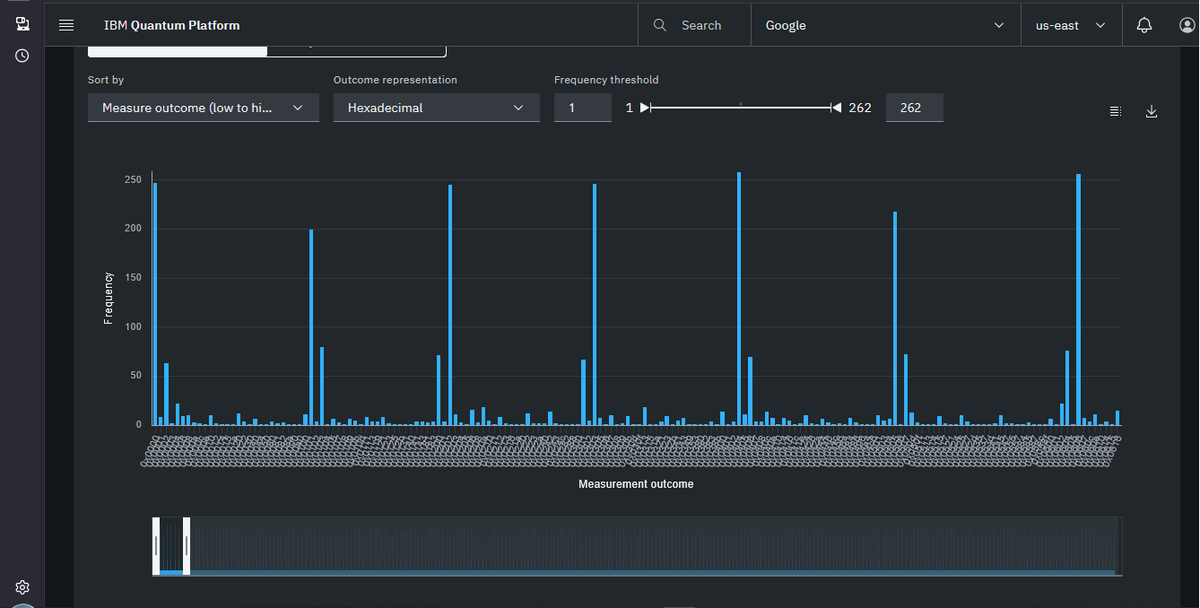


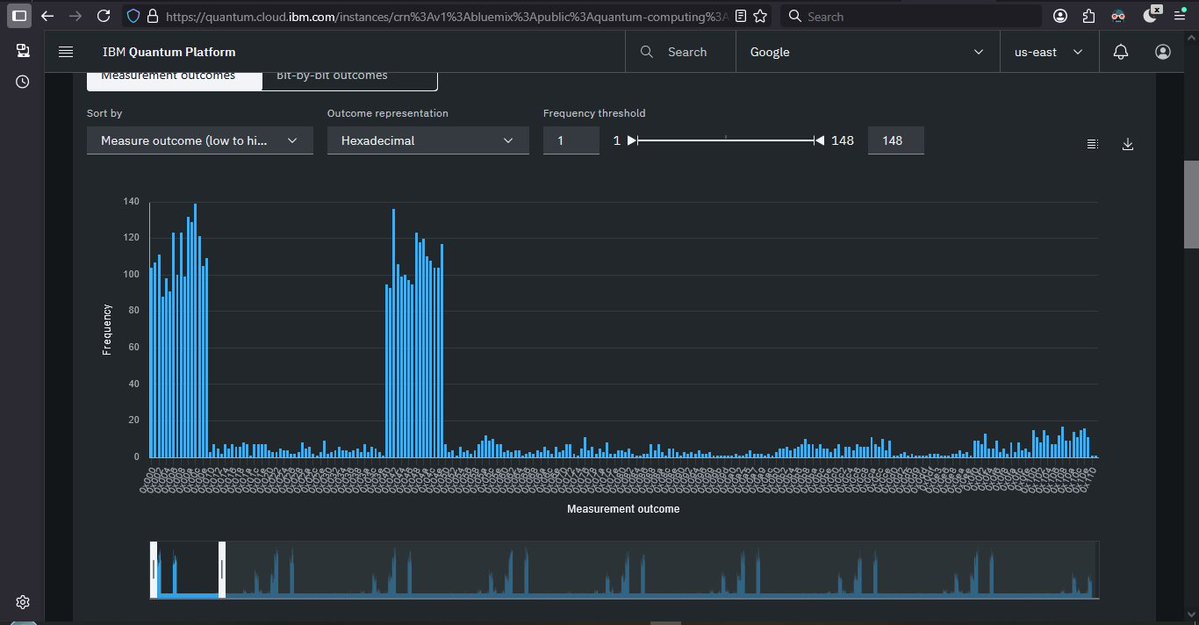
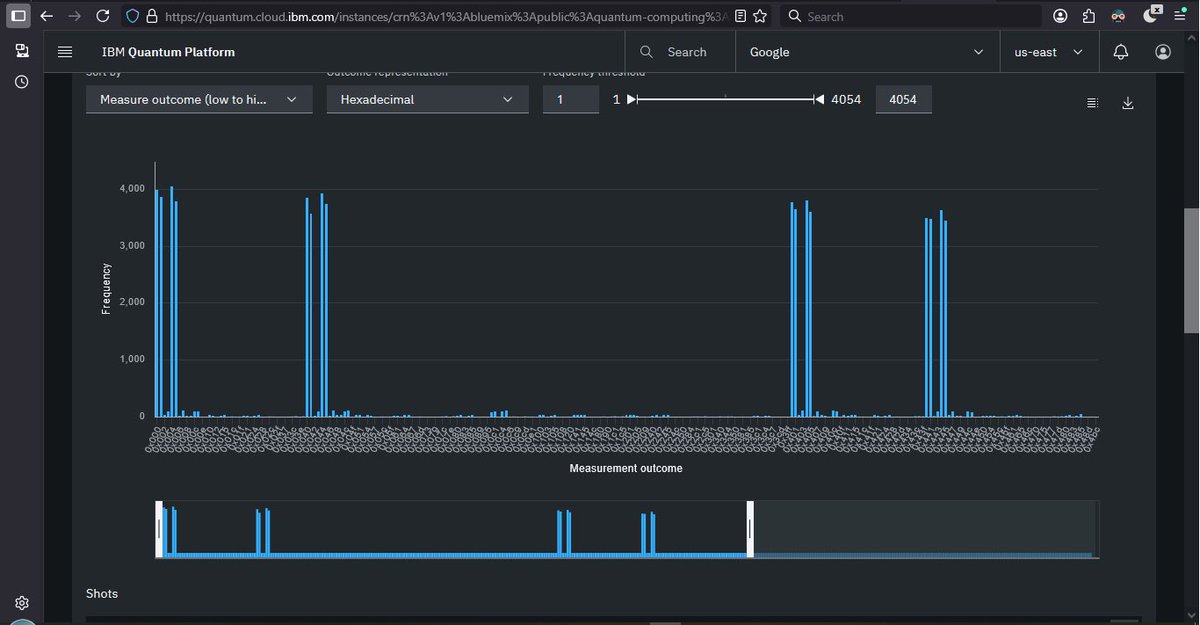
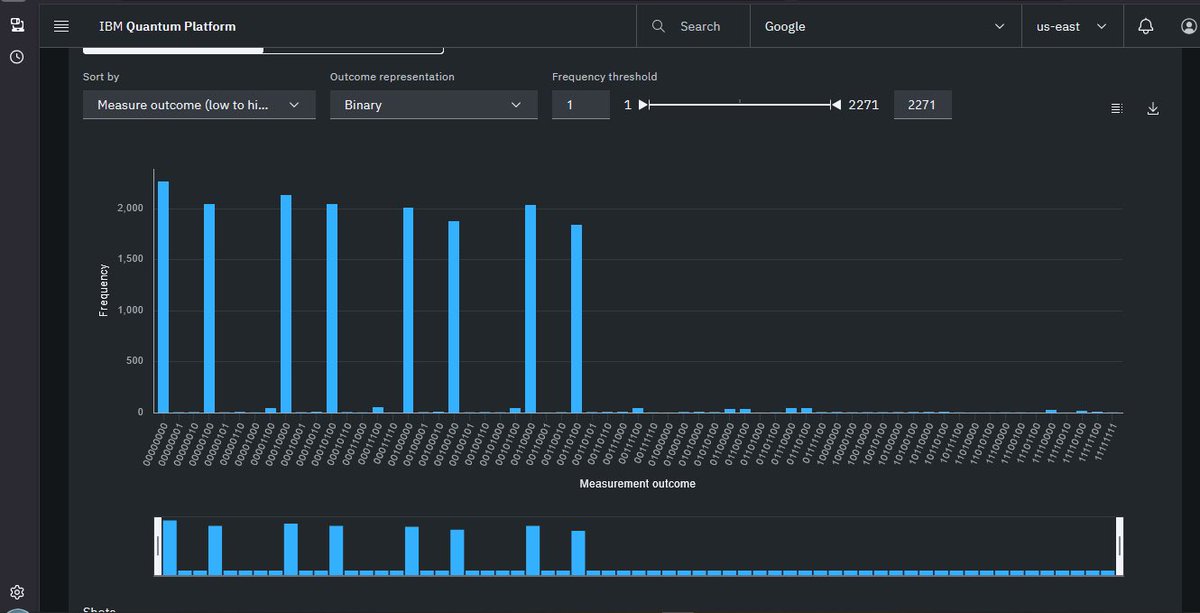

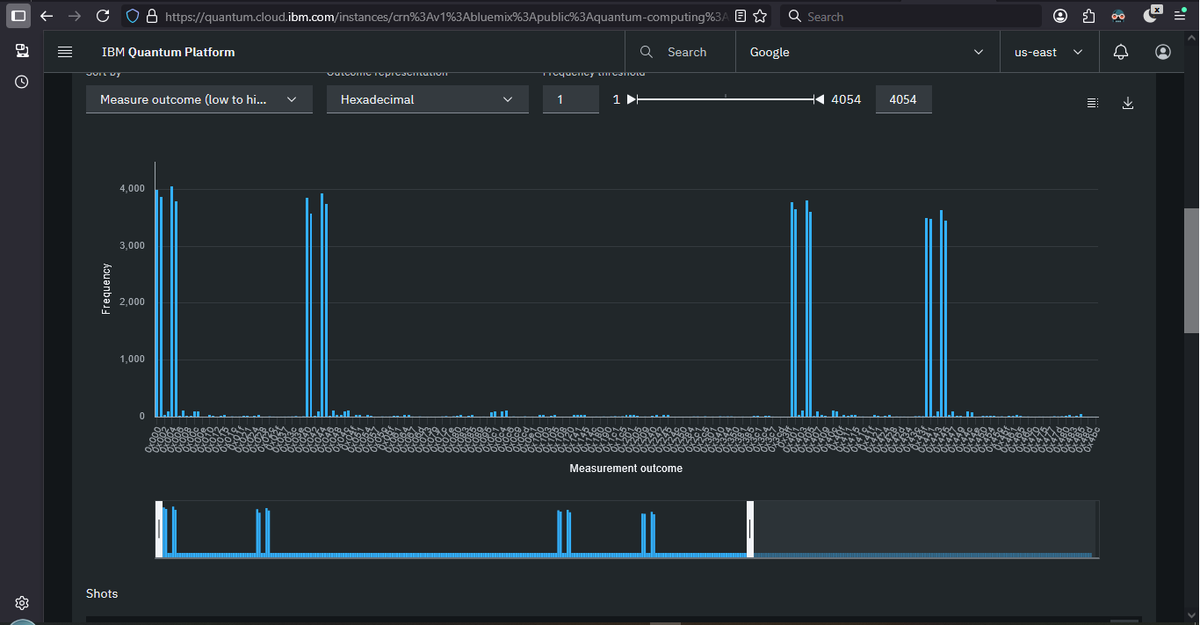
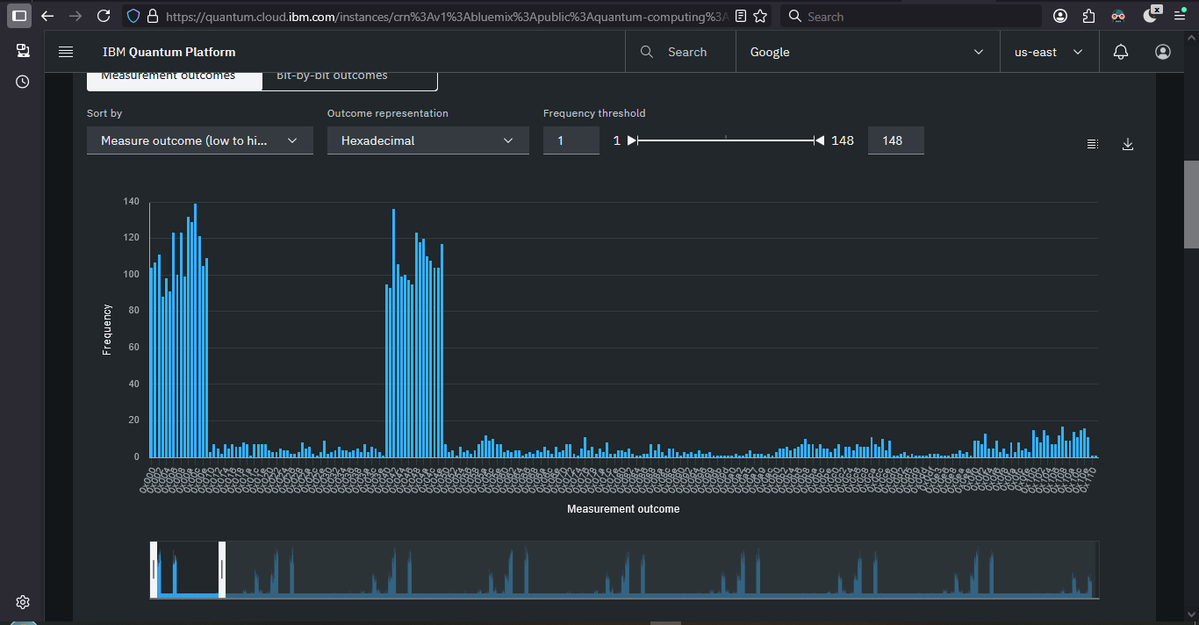
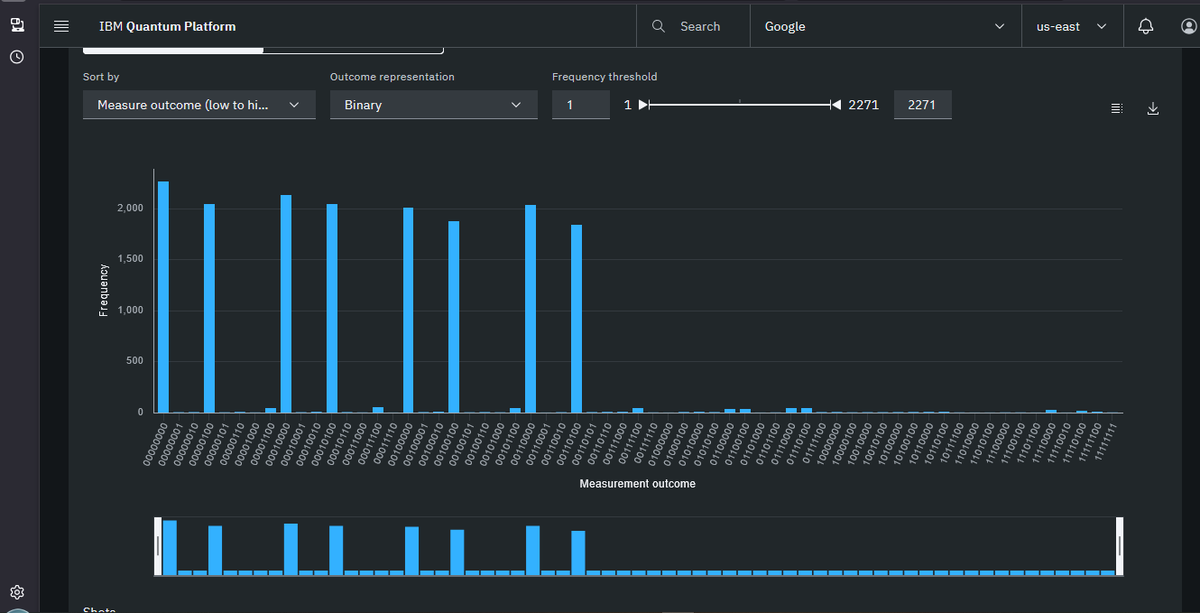
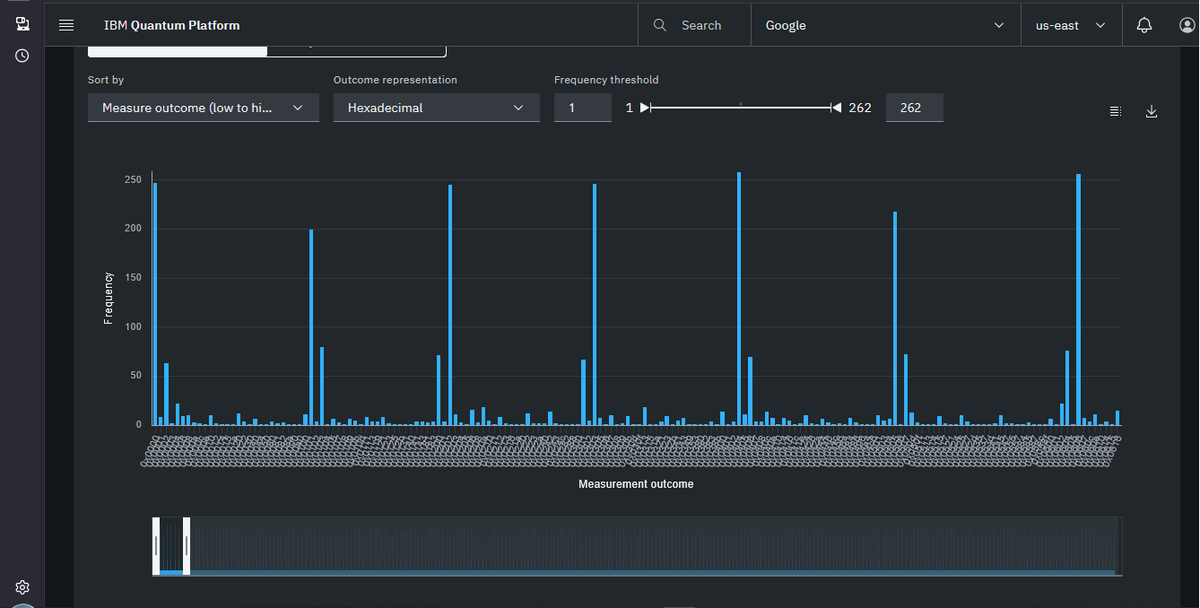

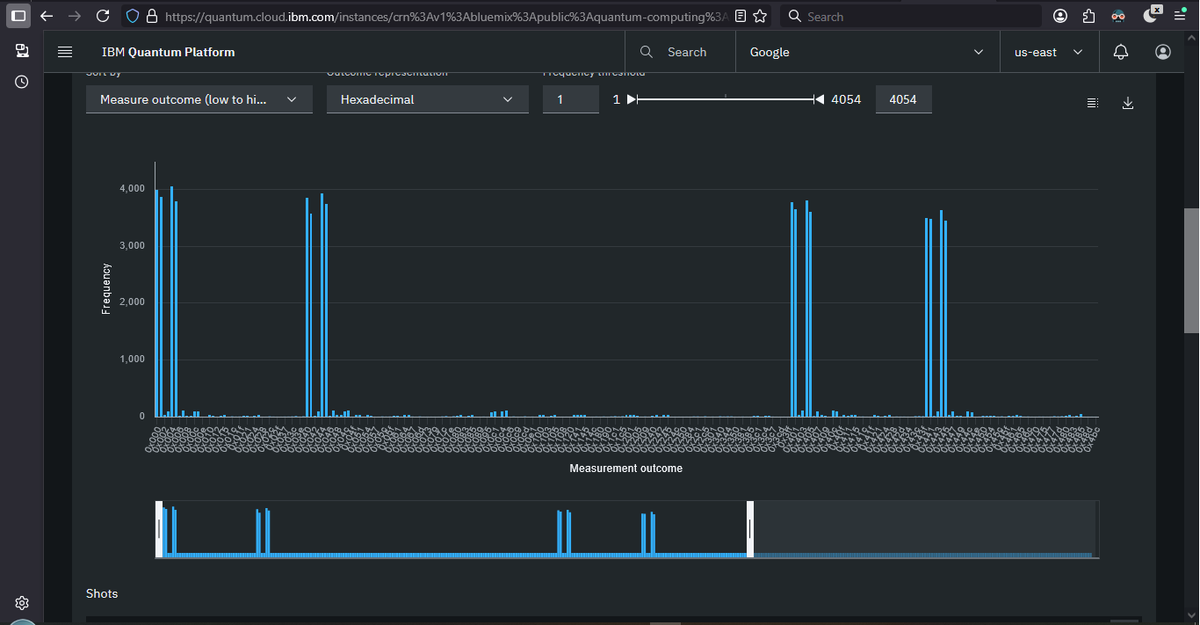
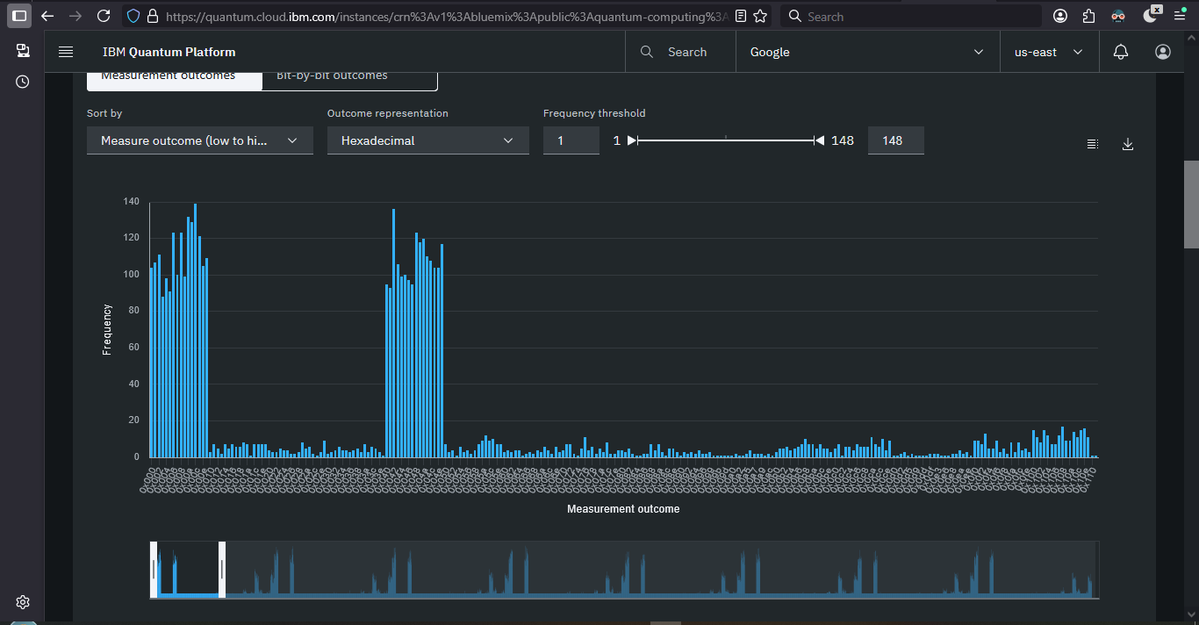
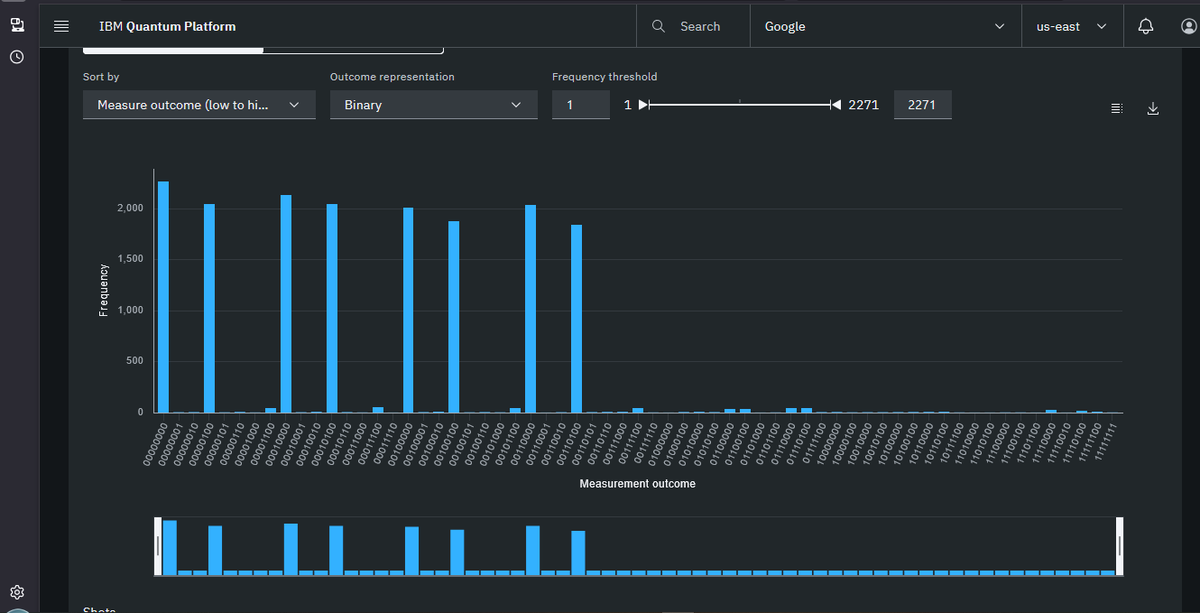
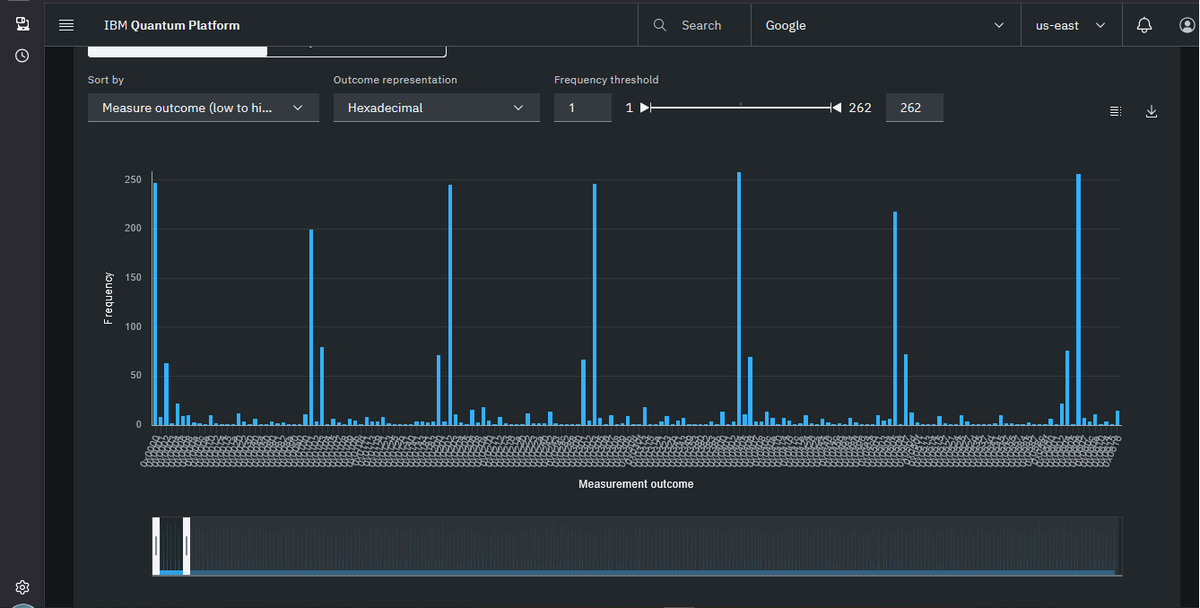
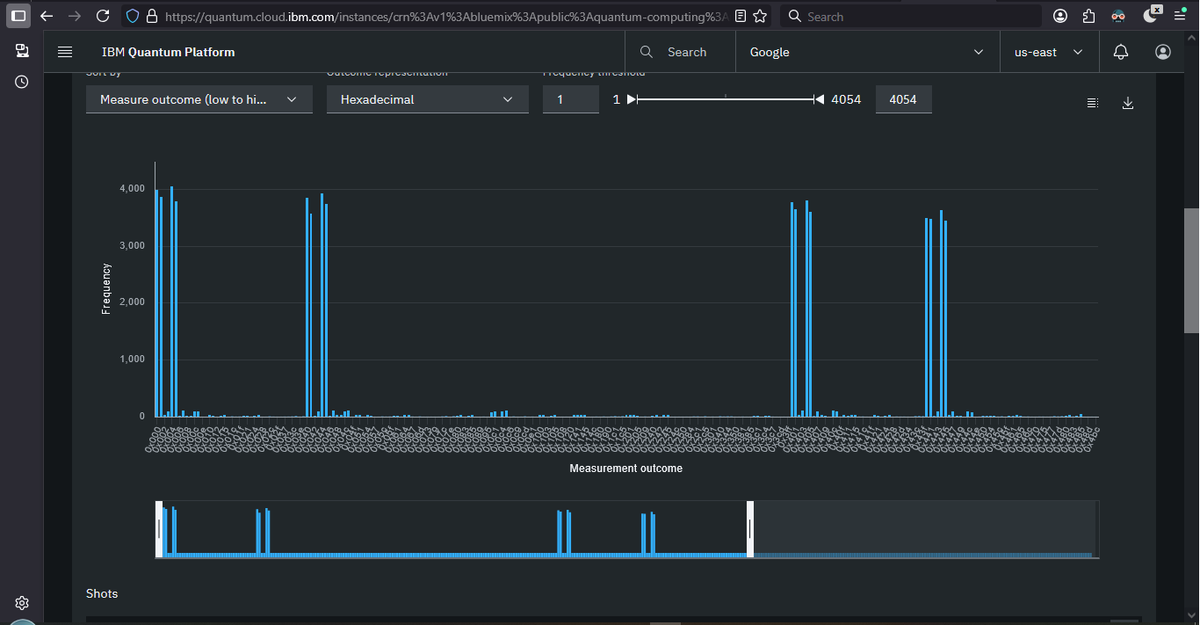
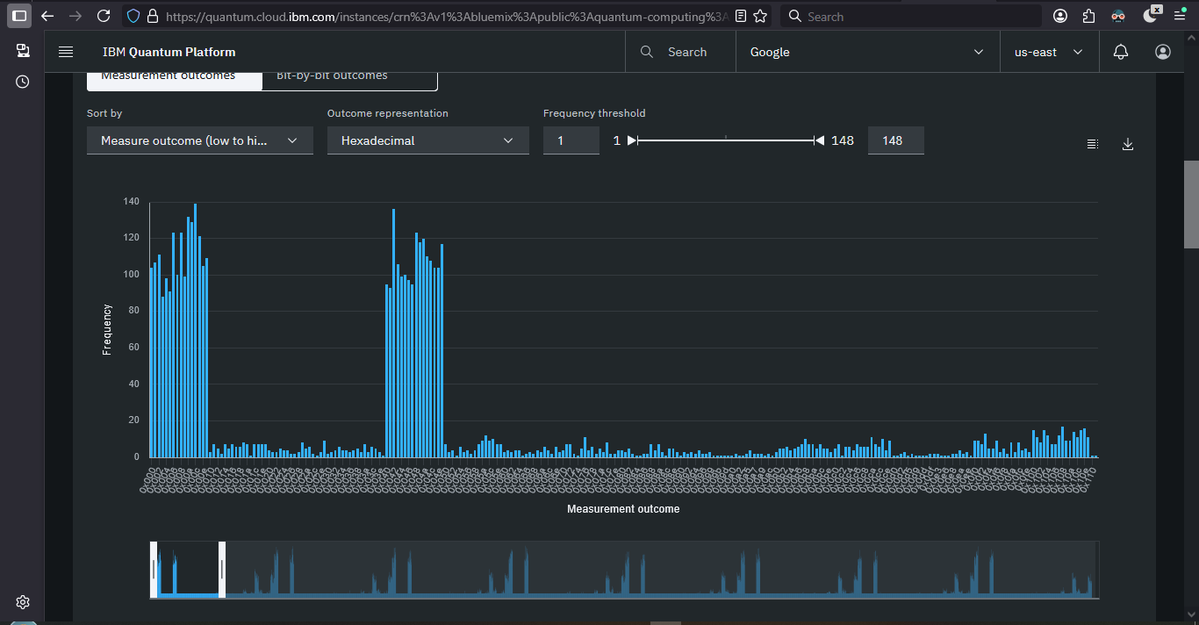
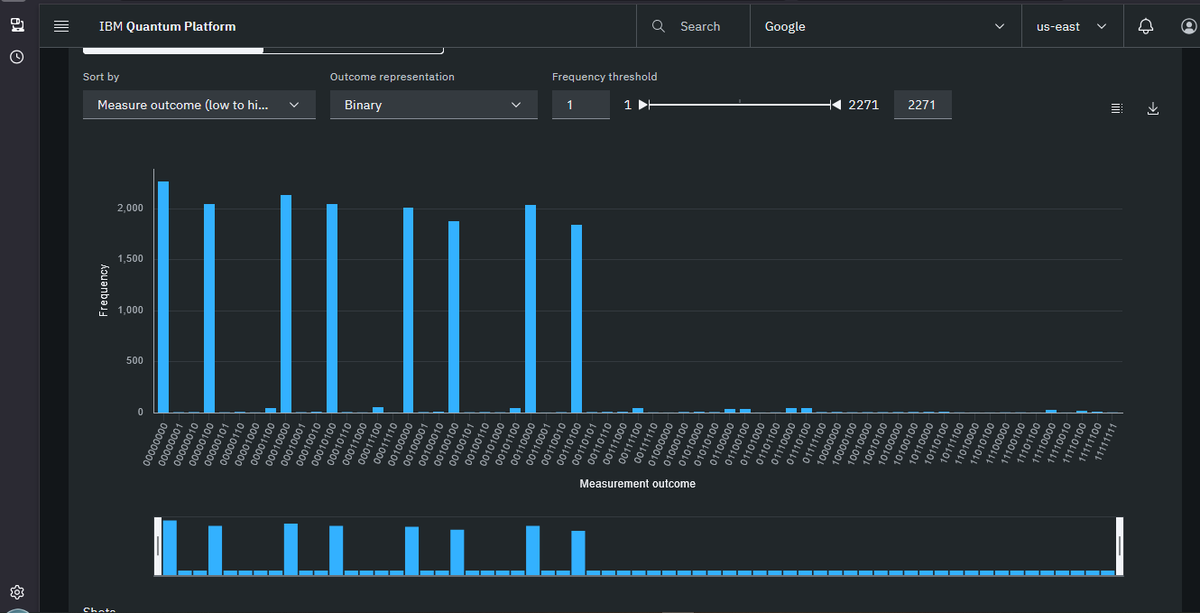
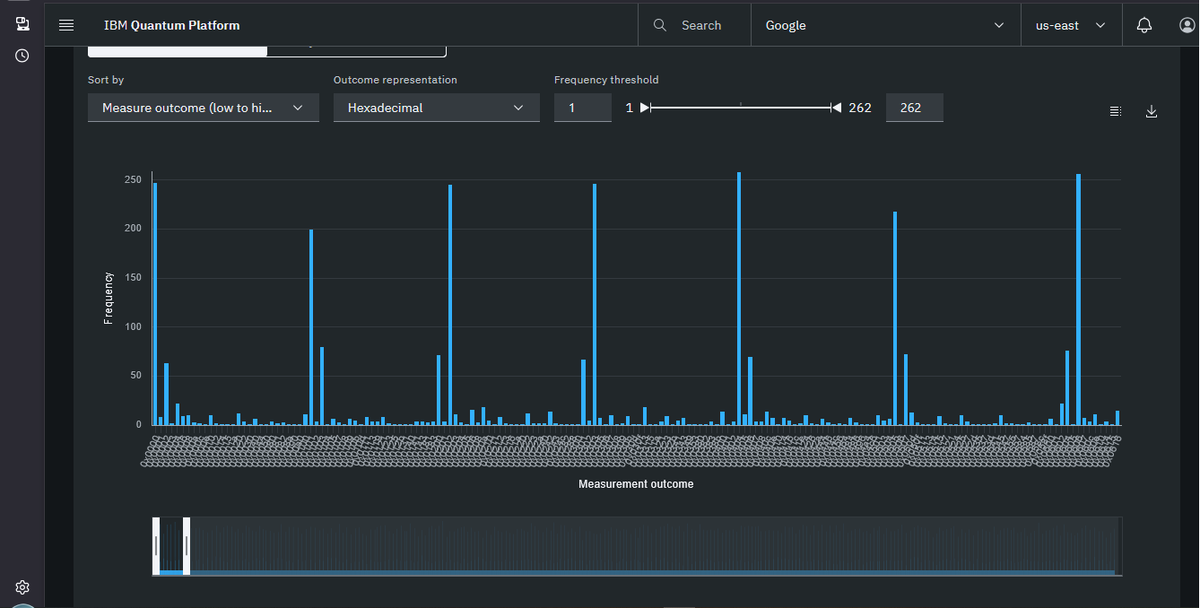
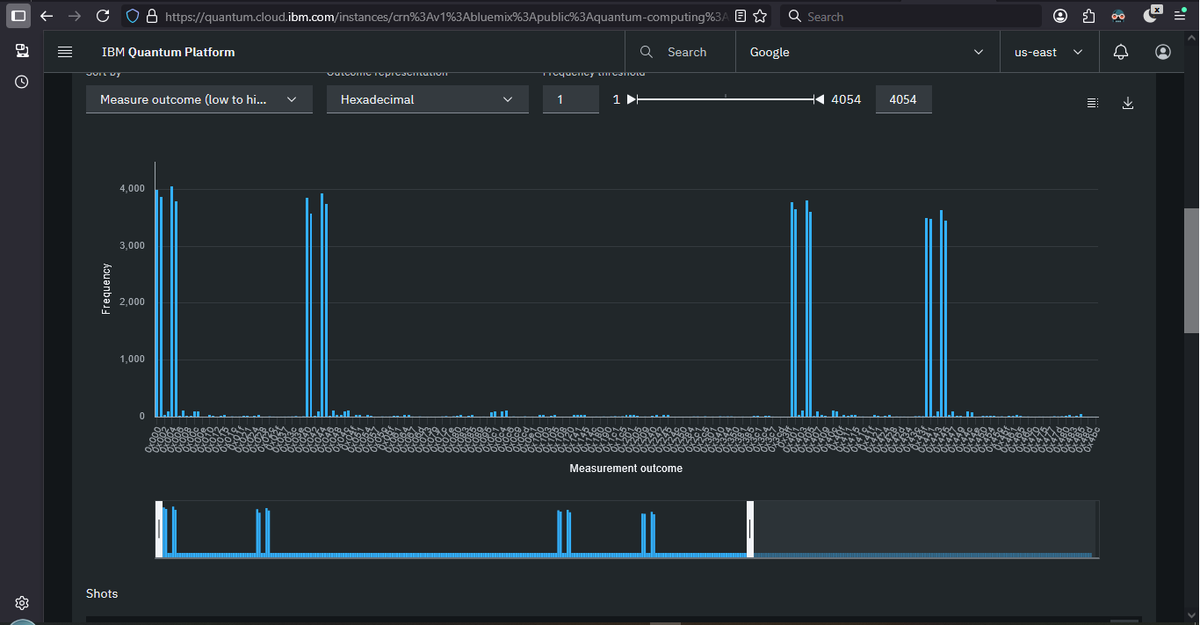
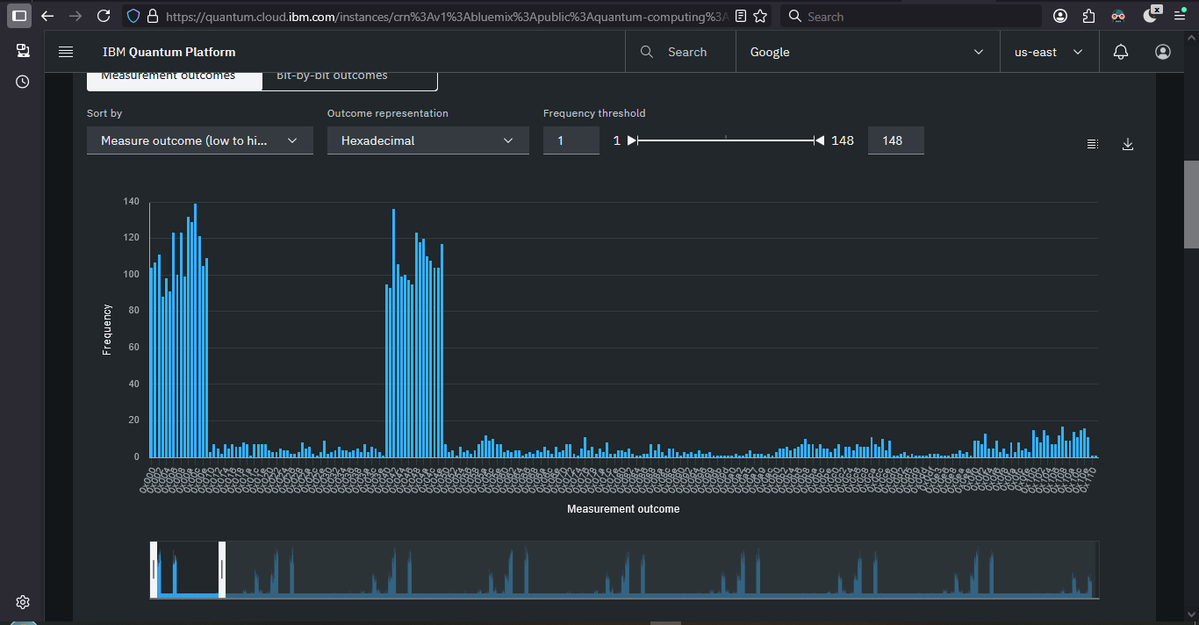
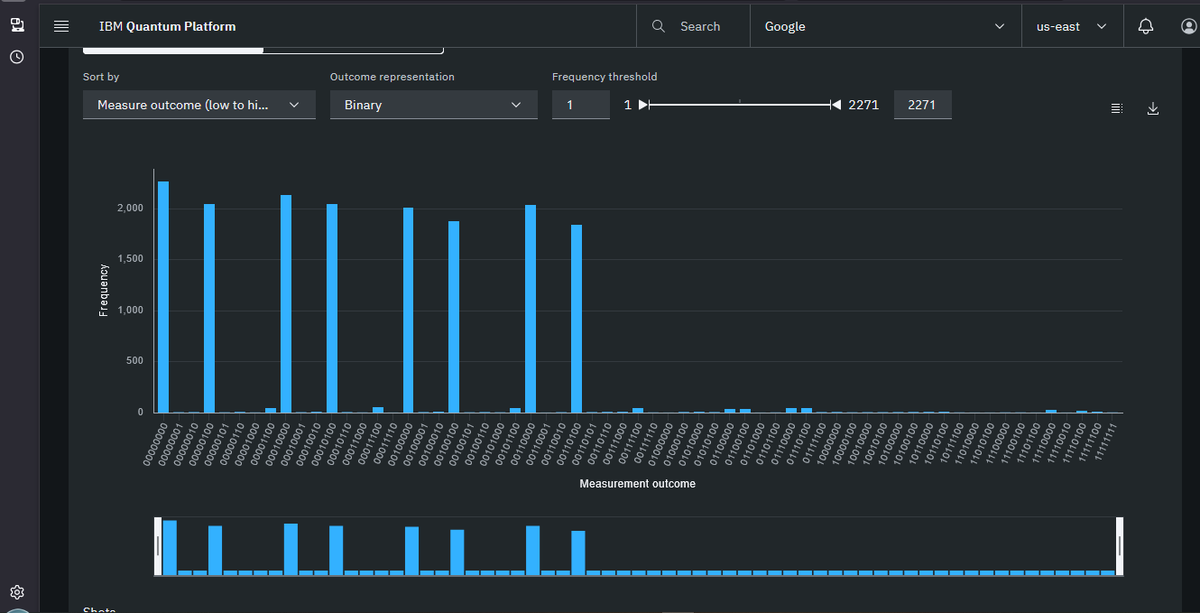
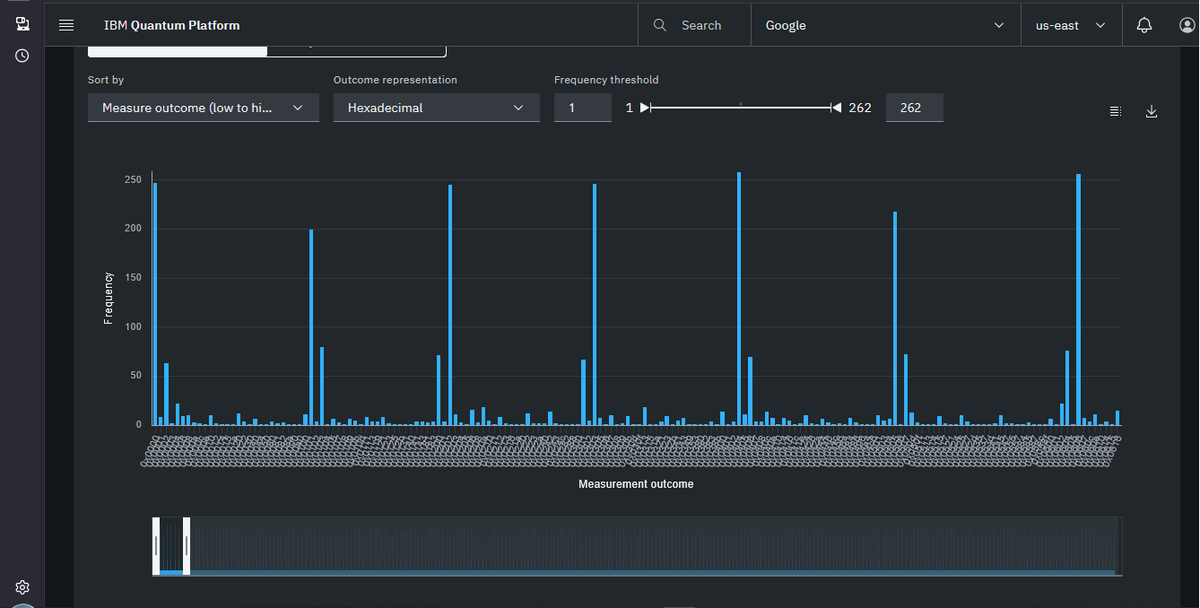
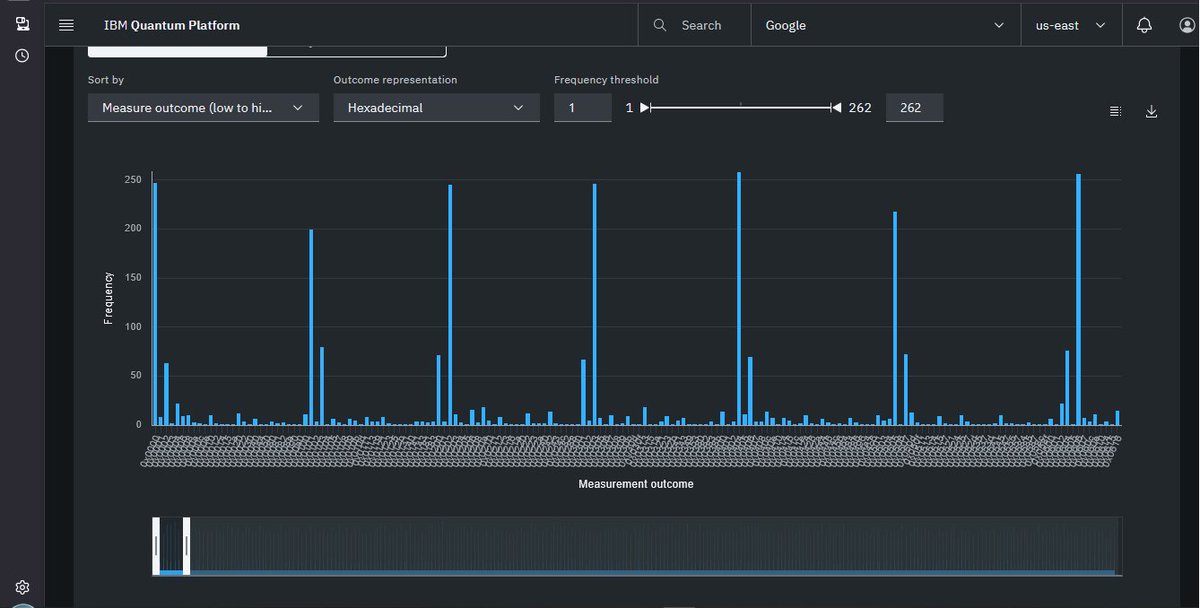
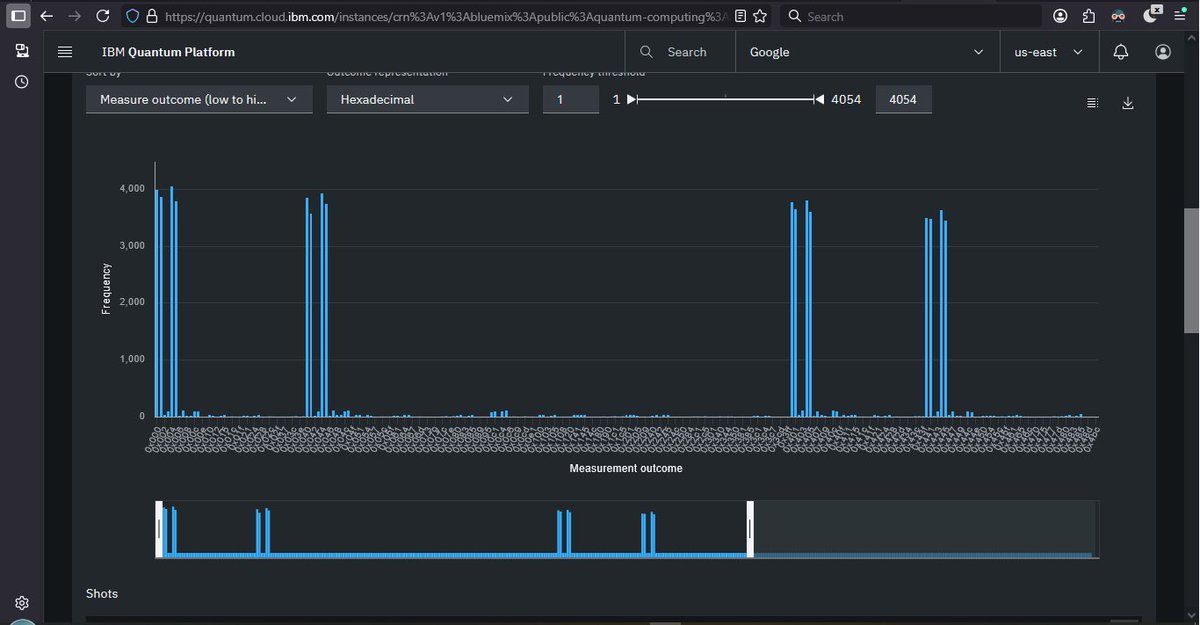
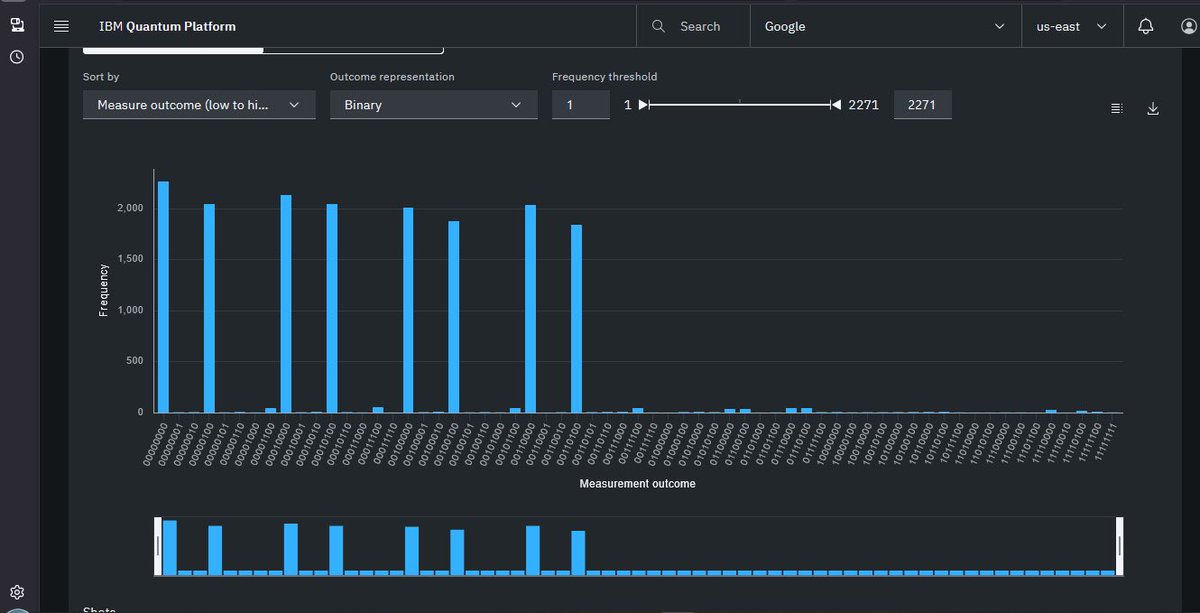
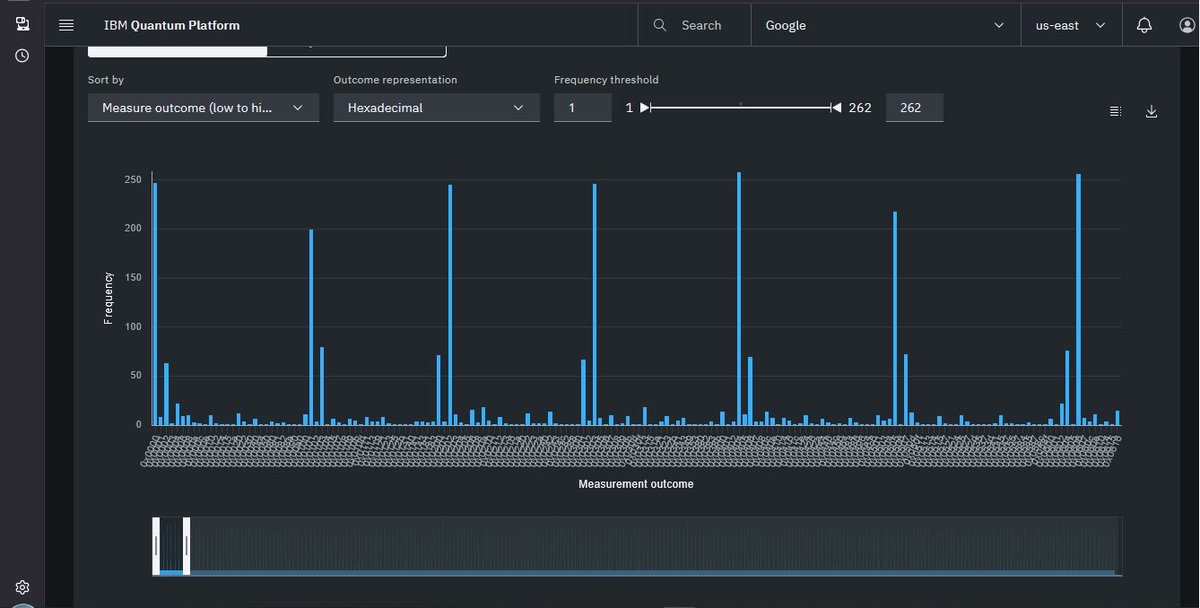
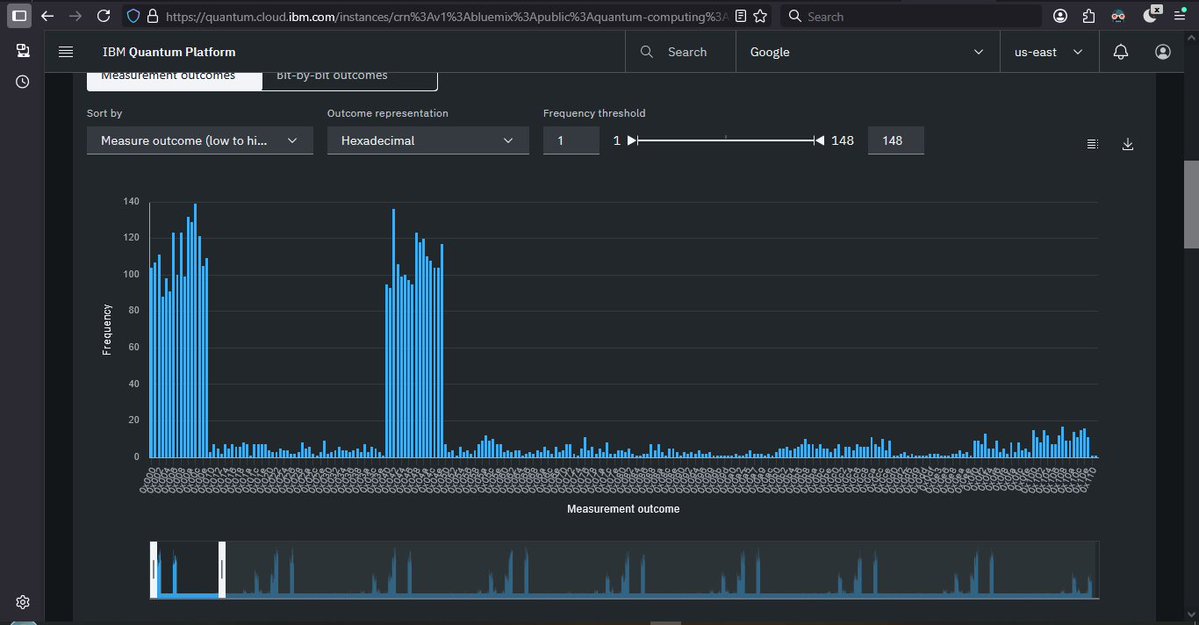
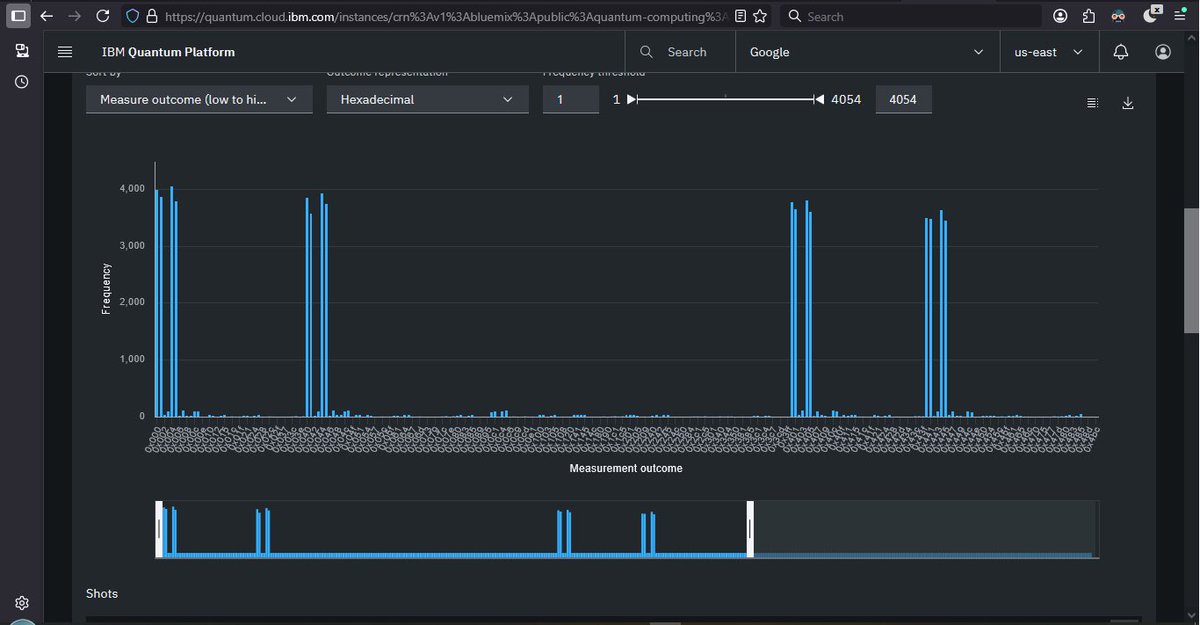
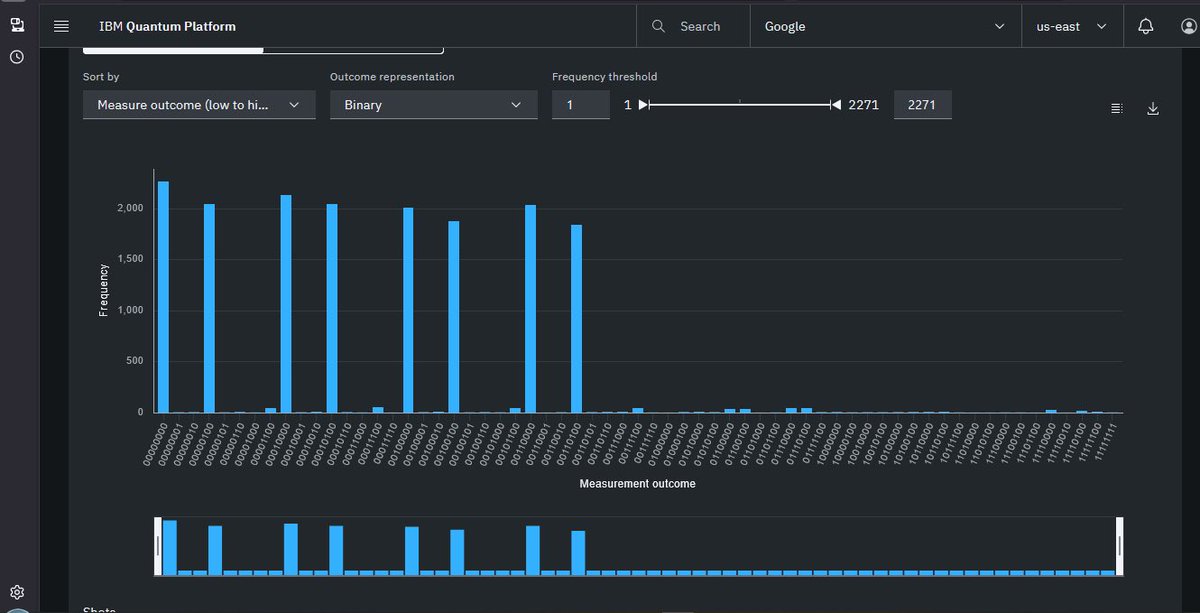
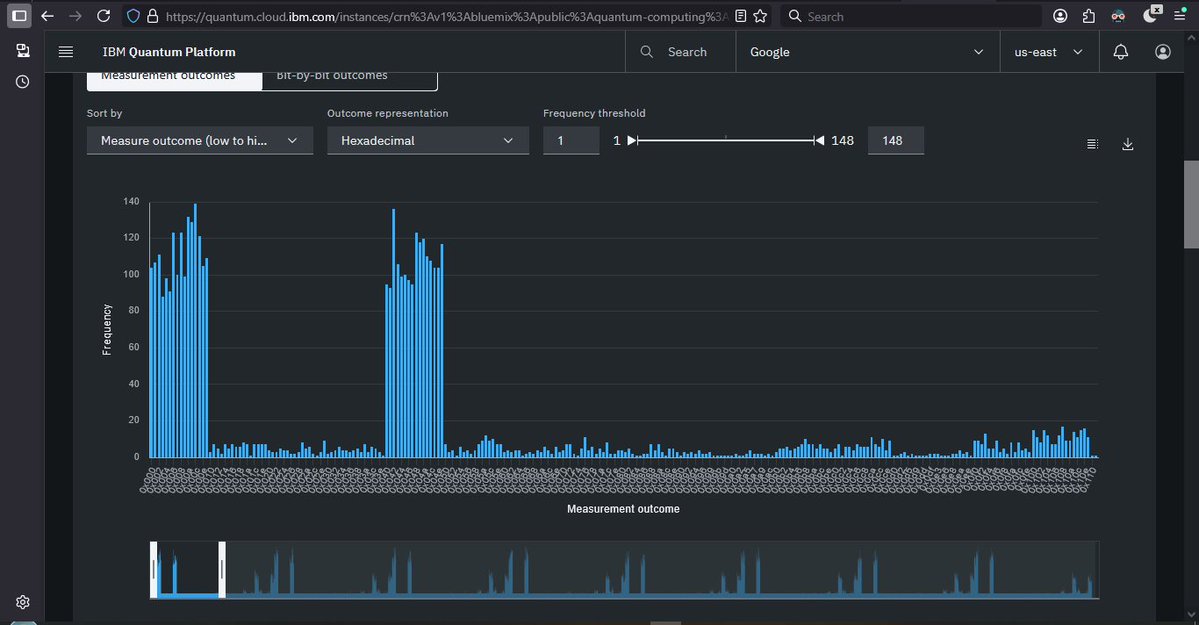
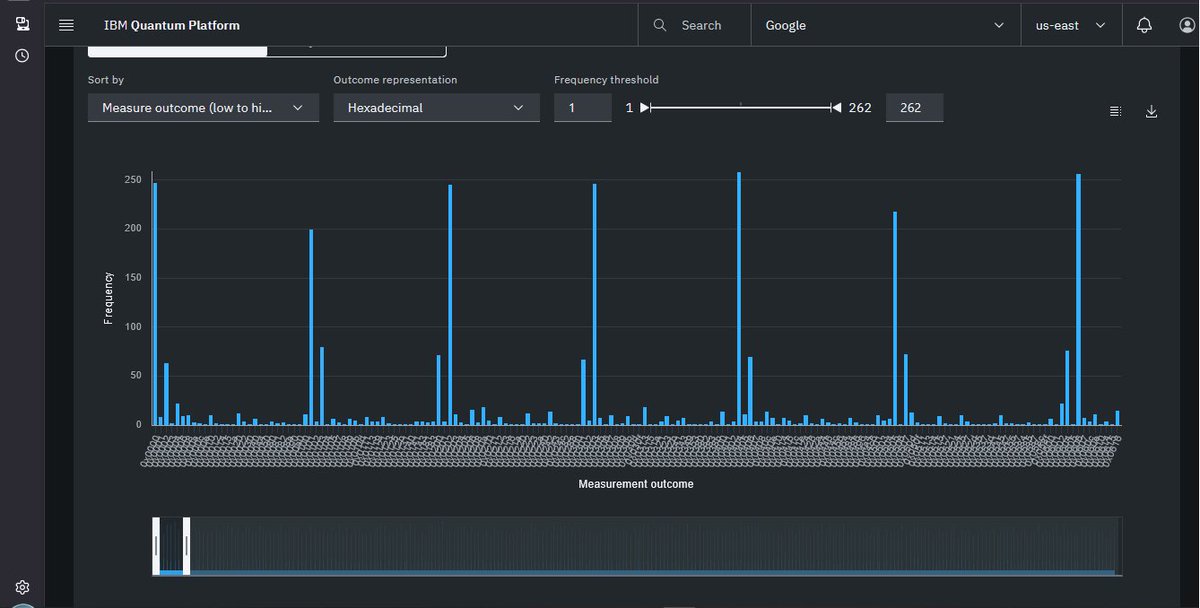
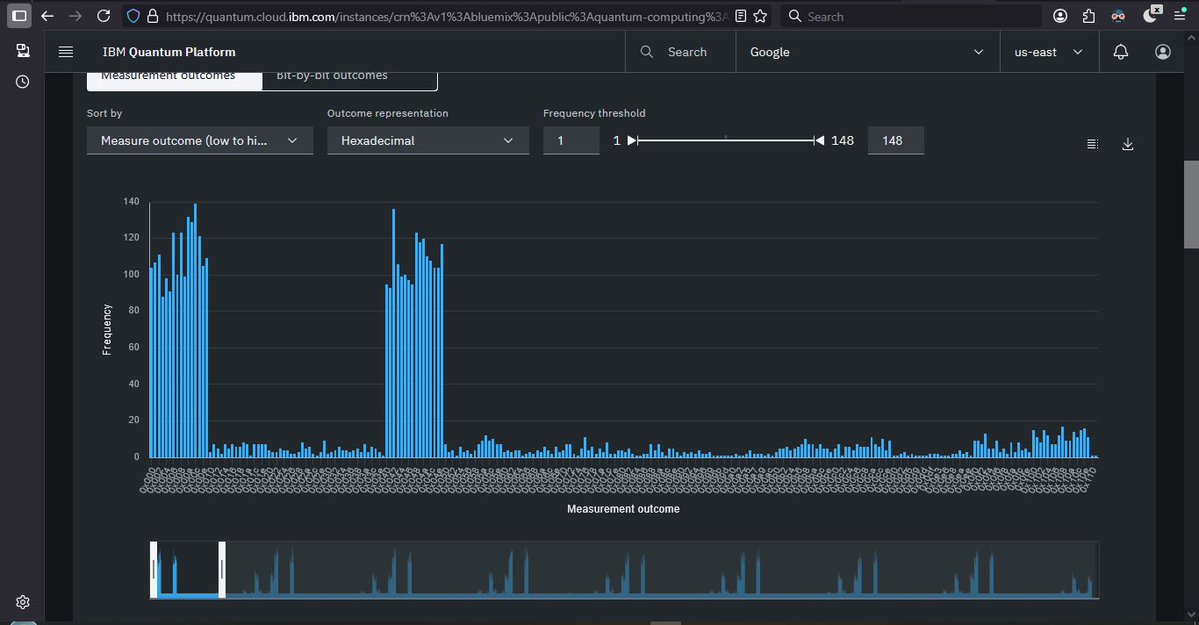
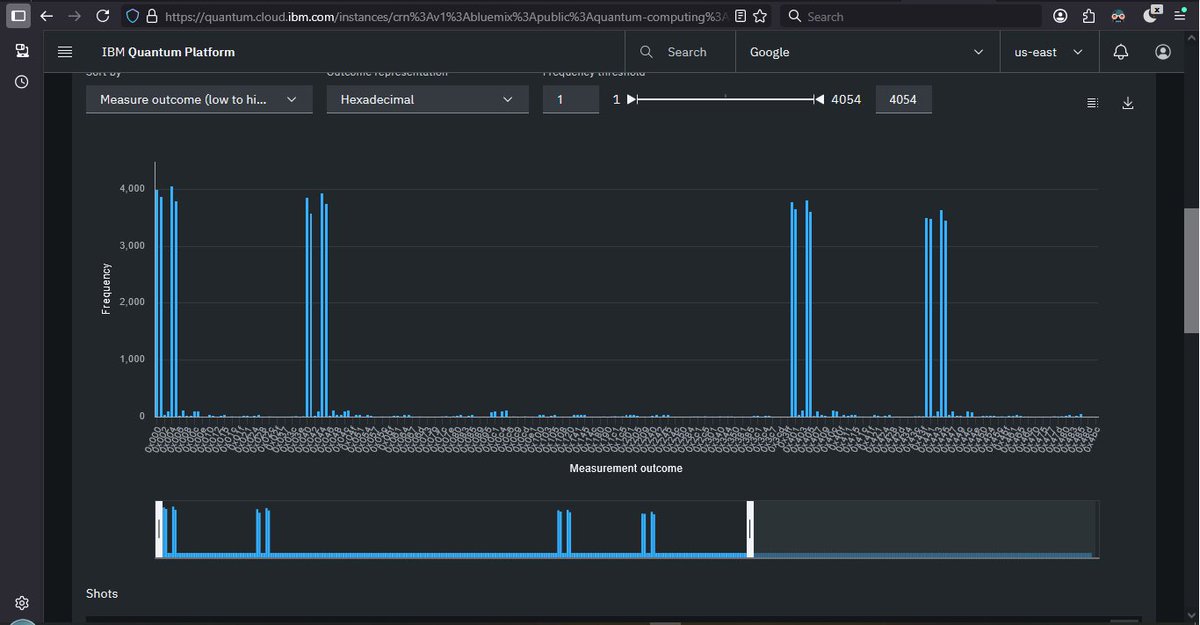
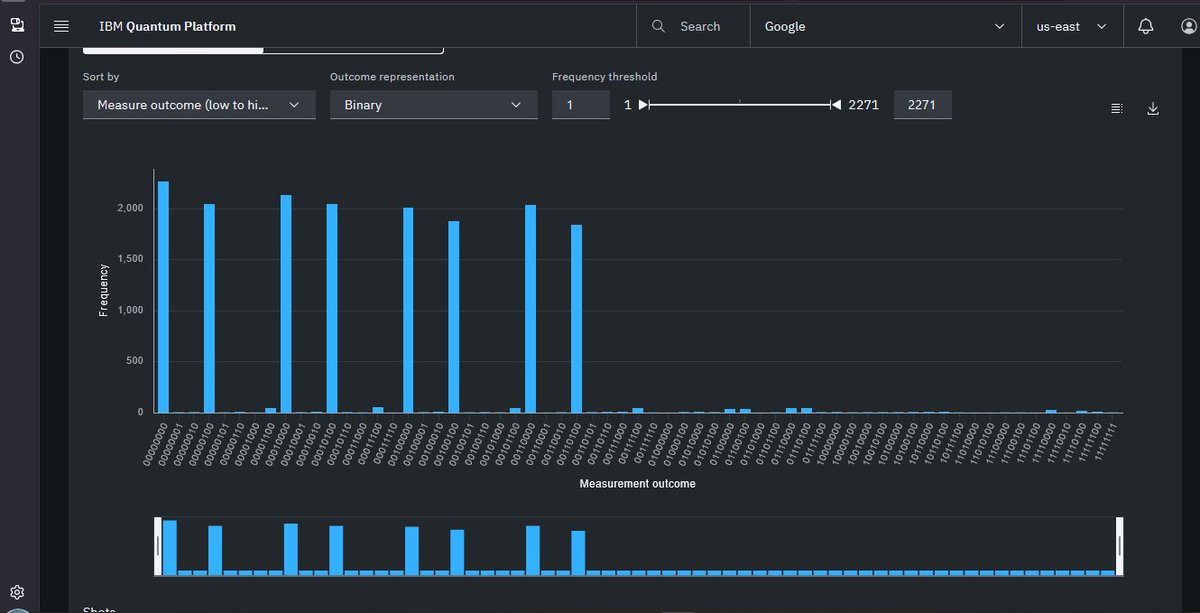
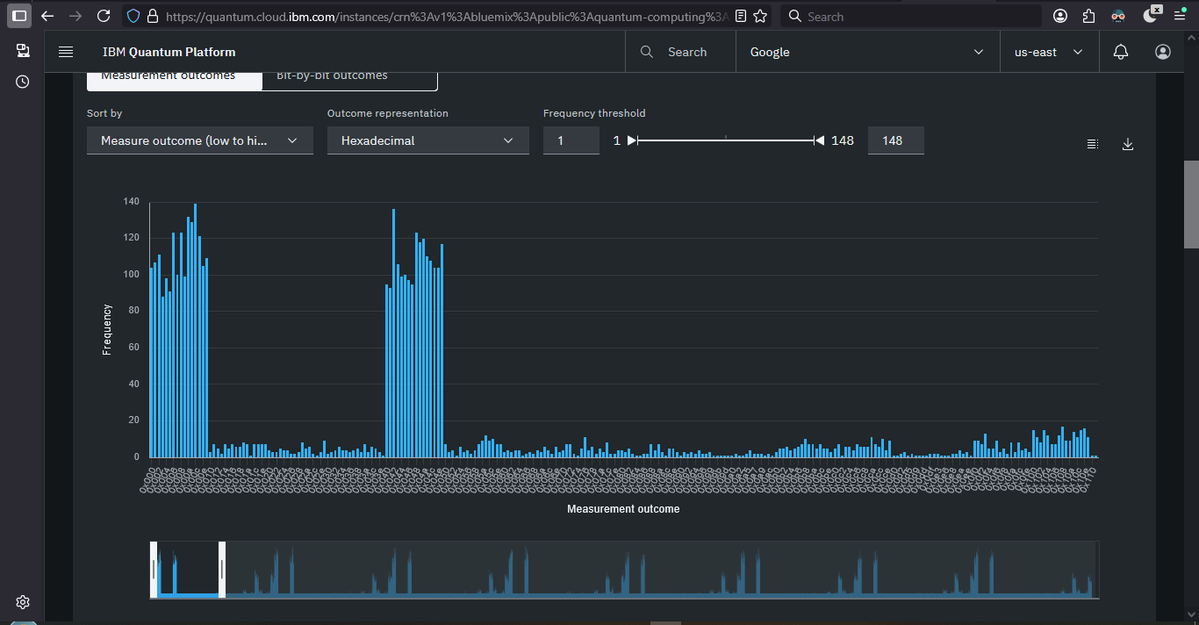
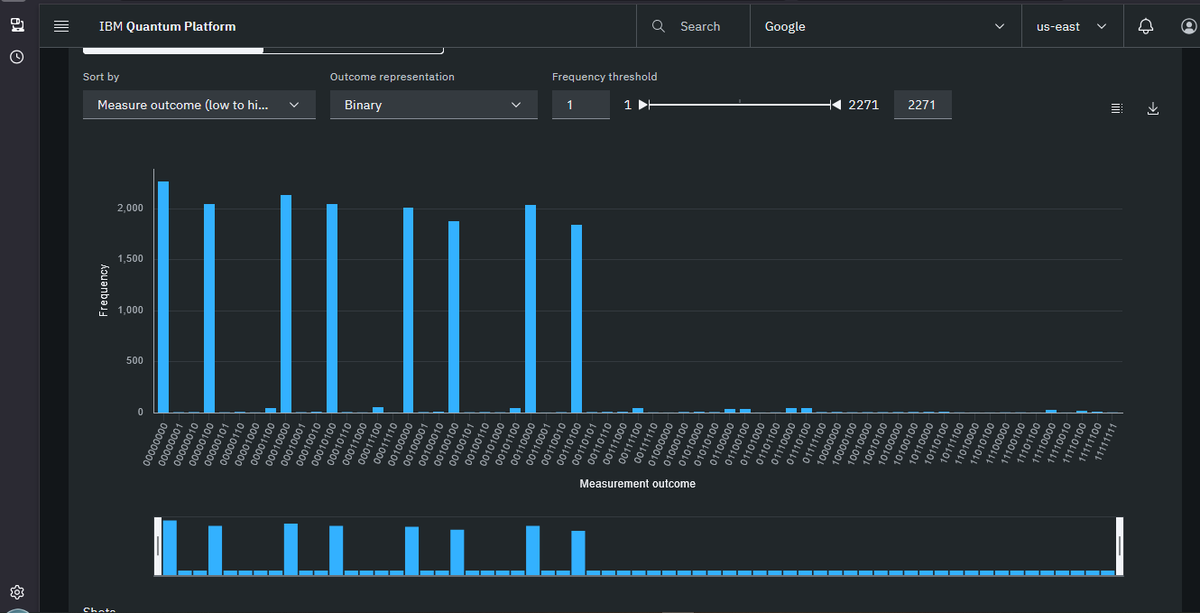
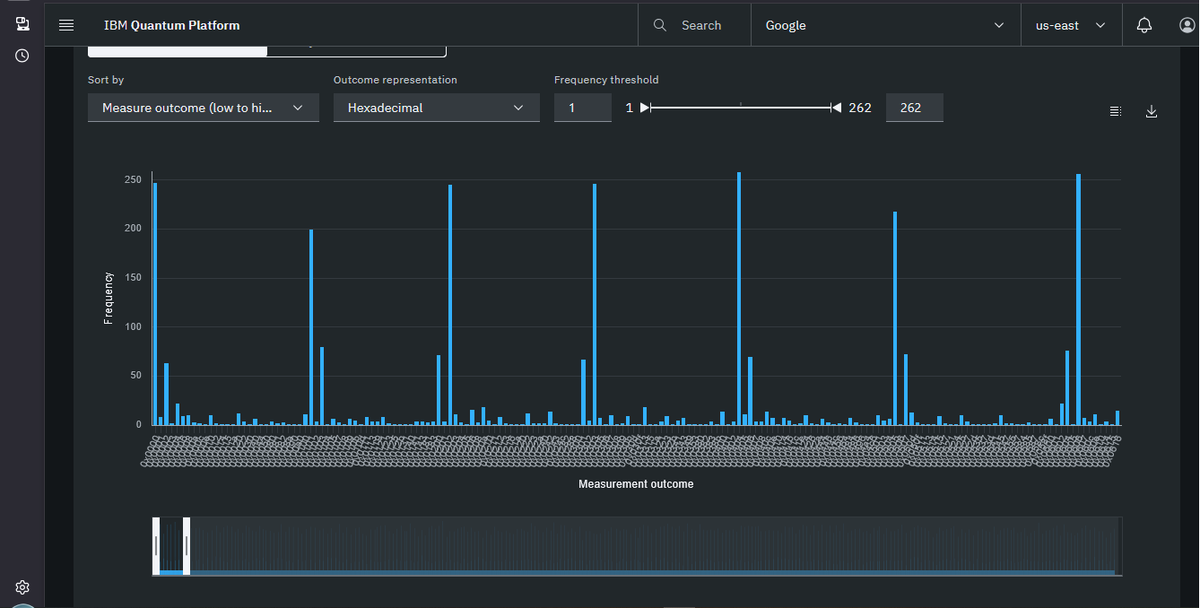
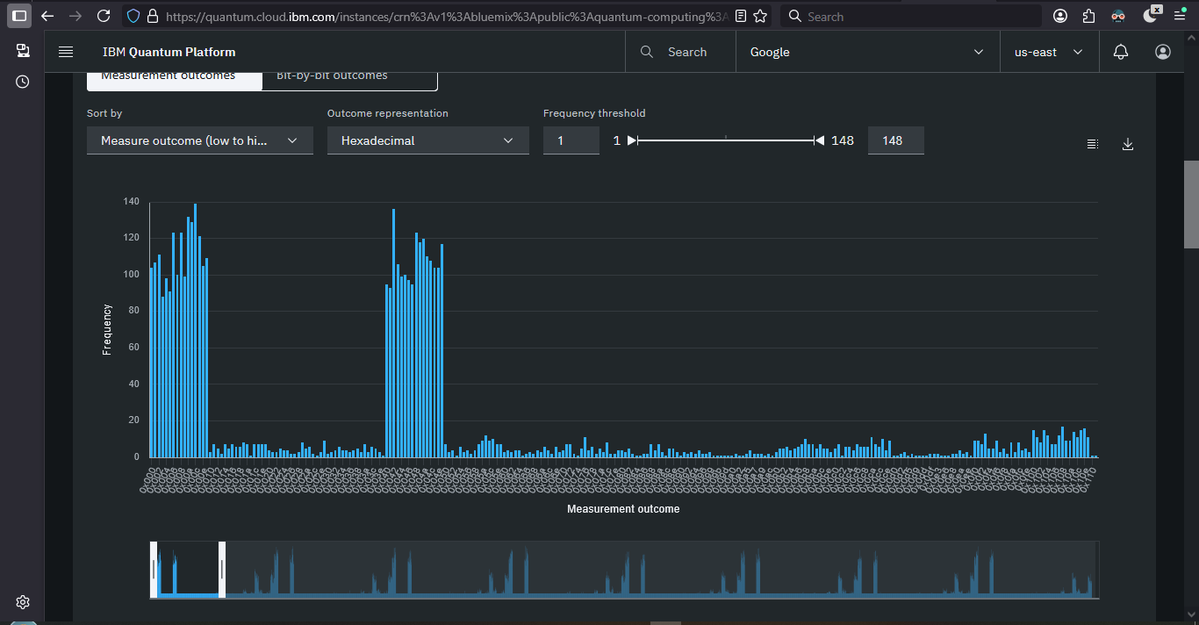
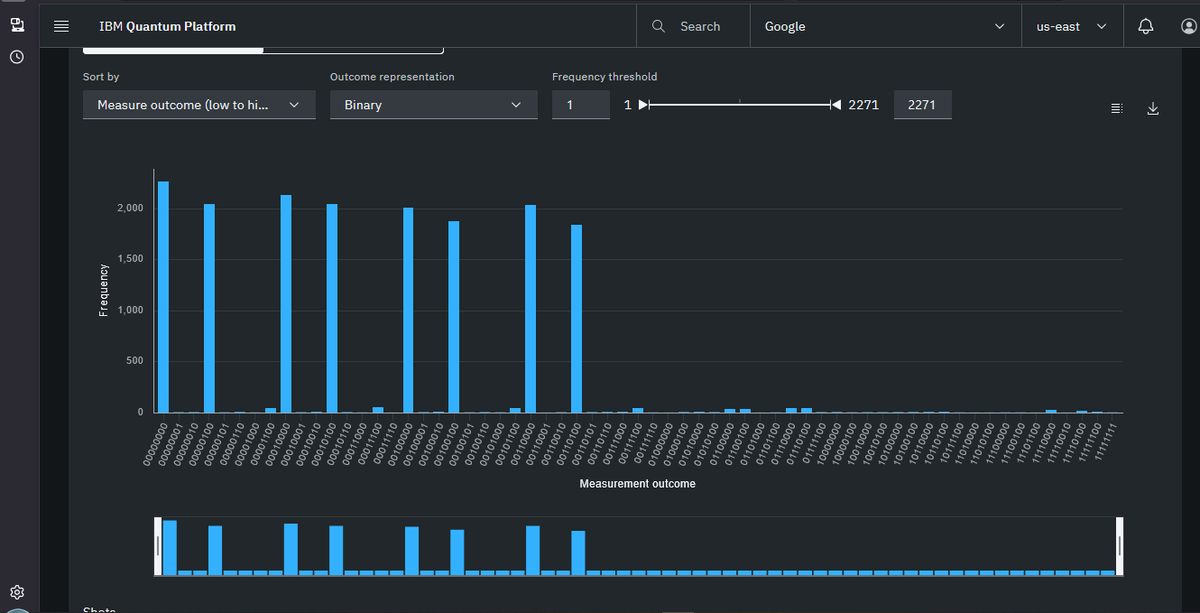
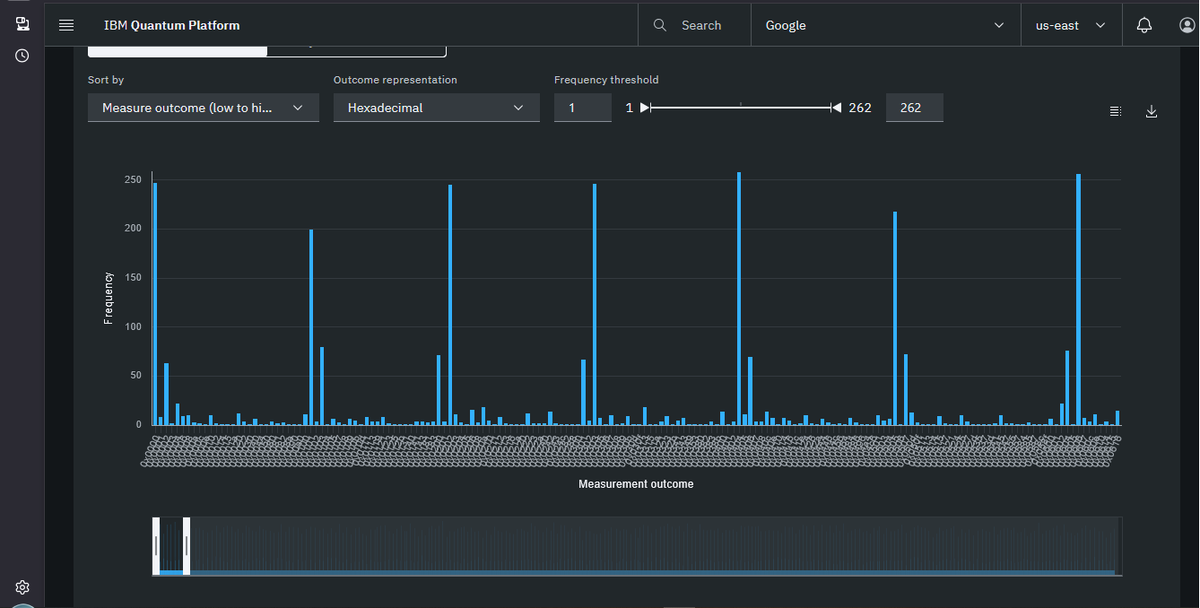
@Dragonique91 @stevetipp This is exactly right. real quantum patterns ARE visible at small bit sizes. The histograms show genuine period structure. The problem with the awarded submission is specifically at 16-17 bit where circuit fidelity is 10^(-214) — the signal is completely destroyed by noise at that scale. /dev/urandom produces identical results. Real signal exists. Just not at the scale that won the prize.

@stevetipp @SilkForgeAi Yes The Patterns Are 100% Realistic i Tryed Both Algos Shor & RegeV They Both Shows Clear Pattrens for Small Sized Bits Mybe Until 18-bit But The Post-Processing of Finding Period == Continued Fractions Hard to Detect it Due To Noize Quantum Machines .



"They can't break 16 bits" is the new "They can't factor 21." Looking forward to skeptics moving the goalposts.









Project Eleven Awards 1 BTC Q-Day Prize for Largest Quantum Attack on Elliptic Curve Cryptography to Date Researcher breaks 15-bit ECC key on publicly accessible quantum hardware in a 512x jump from the previous public demonstration. Project Eleven today awarded the Q-Day Prize, a one Bitcoin bounty, to Giancarlo Lelli for breaking a 15-bit elliptic curve key on a publicly accessible quantum computer. The result is the largest public demonstration to date of the attack class that threatens Bitcoin, Ethereum, and over $2.5 trillion in ECC-secured digital assets. "The resource requirements for this type of attack keep dropping, and the barrier to running it in practice is dropping with them," said @apruden08, CEO of Project Eleven. "The winning submission came from an independent researcher working on cloud-accessible hardware. No national lab, no private chip. It shows that tangible progress is possible and highlights the urgency to migrate to post-quantum cryptography sooner rather than later. Google just committed to being quantum-secure by 2029. The window to get ahead of this is closing.” Lelli derived a private key from its public key across a search space of 32,767 using a variant of Shor’s algorithm. Shor's targets the Elliptic Curve Discrete Logarithm Problem (ECDLP), the math underlying the digital signature schemes securing Bitcoin, Ethereum, and most blockchains. Quantum attacks on ECC have moved from theory to practice over the last seven months. Steve Tippeconnic's 6-bit demonstration in September 2025 was the first public break on quantum hardware. Lelli's 15-bit result extends it by a factor of 512. Theoretical resource estimates for a full 256-bit attack, the scale Bitcoin operates at, have fallen sharply over the same period. Google's April 2026 whitepaper put the requirement at under 500,000 physical qubits. A subsequent paper from Caltech and Oratomic brought that figure as low as 10,000 qubits in a neutral-atom architecture. Lelli's result is the practical counterpart to those optimizations. The distance from 15 bits to 256 bits is large, but the gap is increasingly viewed as an engineering problem and not a fundamental physics problem. Roughly 6.9 million Bitcoin sit in wallets whose public keys are visible on-chain, exposing them to quantum attack. All blockchains using ECC share similar risks with vulnerable assets. Project Eleven is developing its next challenge, focused on the intersection of frontier AI models and quantum cryptanalysis.






@Pledditor @projecteleven As I understand they are still figuring that out. One floated idea people under an altcoin you claim airdrop and use PQ sigs. Basically try to do something like NYA contentious fork, but by migrating to a claimable airdrop and then try to FUD a lot and claim it's the new Bitcoin.


Alright, some clarification on the Q-Day prize — it seems like it's getting misconstrued. Let's lay down the facts 👇🧵



The difference: when they factored 21, the quantum computer actually did the factoring. Here, the quantum computer output pure noise and a classical verifier found the answer. A JOKE!


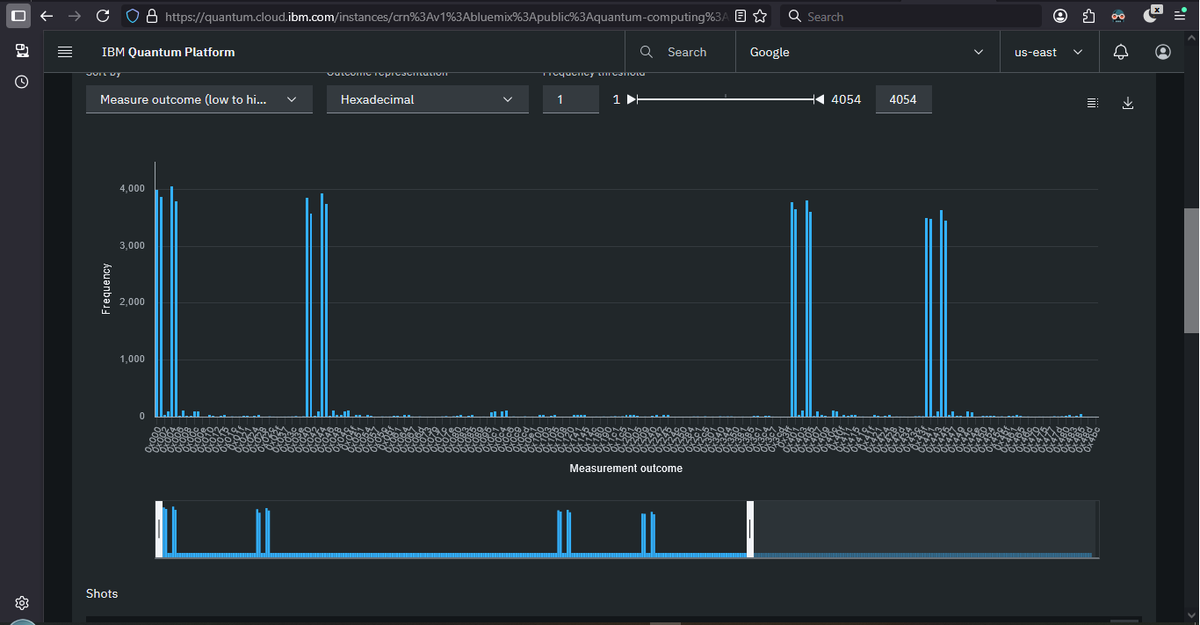

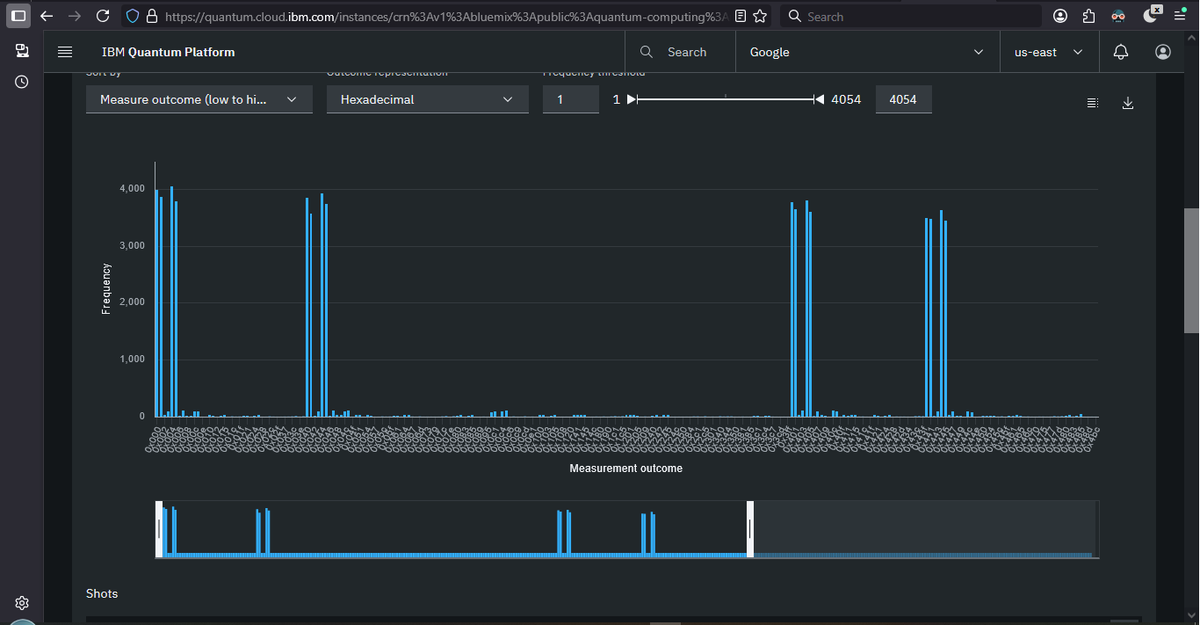


We awarded the Q-Day Prize today to Giancarlo Lelli for breaking a 15-bit elliptic curve key on a publicly accessible quantum computer. They derived a private key from its public key using a variant of Shors across 32,767 candidates on cloud-accessible hardware. This is the largest public demonstration of this attack class to date.
The reason we created this prize a year ago was that there has never been an objective public measurement of where quantum attacks on ECC actually stand. The state of the art has been inferred from whitepapers, conference slides, and whatever could be triangulated from rumour or private disclosures. What we know publicly is now grounded in a reproducible result on real hardware. Whatever comes next has to exceed 15 bits under those same conditions, and anyone can verify it.
The most common response to a result at this scale is that 15 bits is nowhere near 256 bits and therefore