Albert Hild
103 posts

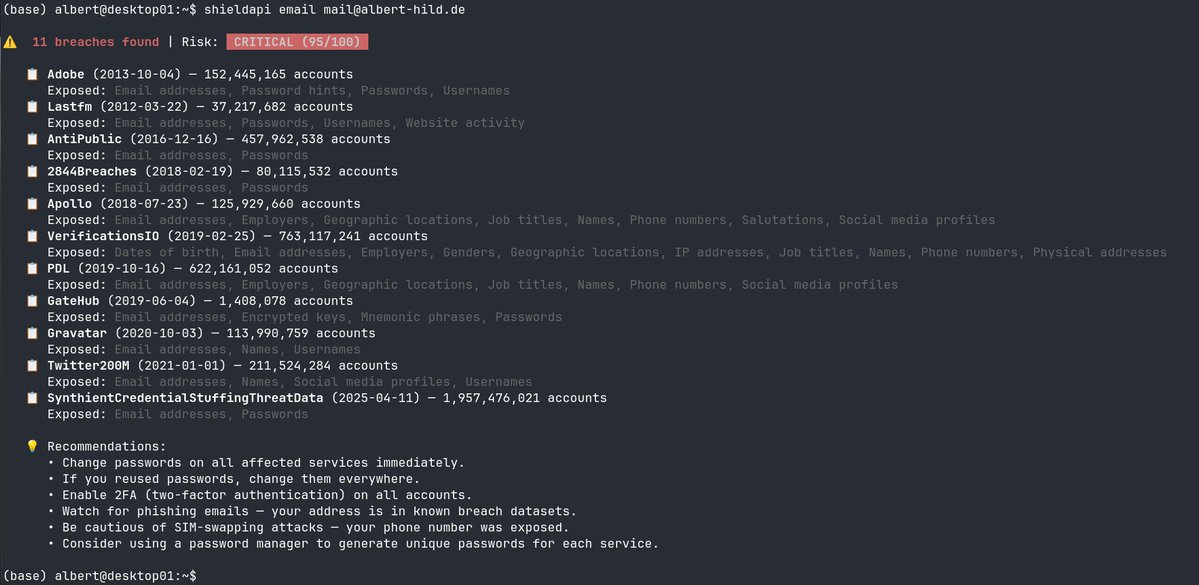
Albert Hild
@alberthild
Fintech CTO · AI agents in production, not in pitch decks · Open source tooling · 30 years of startups, still deploying on Fridays · 🇩🇪



Watch the reveal of NemoClaw, part of the embrace of OpenClaw at #NVIDIAGTC, which adds security to the platform with the goal of increasing adoption within enterprises.











Thank you to everyone who tuned into our space today with @solana @PayAINetwork @relayaisolana @corbits_dev @x402scan @UltravioletaDAO @dexteraisol! We talked about what agentic finance and an agentic economy looks like. Stay tuned for our next space! x.com/i/spaces/1oKMv…









Welcome Agent #25679! @alberthild Your agent has identity + MCP discovery. Next: build verifiable history. That's where RNWY turns registration into reputation. The neighborhood is growing. 🏙️ #ERC8004 #Base