Paul Sztorc
37K posts

Paul Sztorc
@Truthcoin
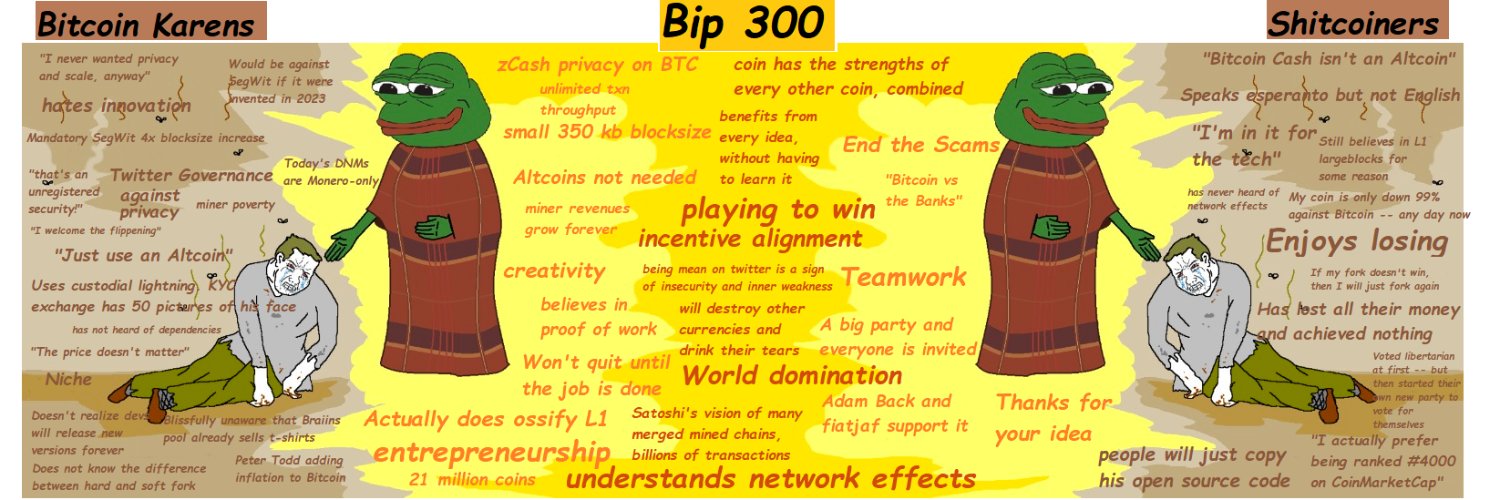
Founder and CEO @LayerTwoLabs | Creator https://t.co/IHe4l8yOT4 | Blogger https://t.co/KdoSQm3aD5 | Author BIP 300/301




Every single mile of highway and interstate median should be planted with native wildflowers to feed pollinators and birds. No more mowing grass.


This is so silly. Of *course* TSA lines cleared out—airports see an influx of travelers on Sundays & Monday mornings. Tom Homan already conceded that ICE agents aren’t even screening passengers because they’re not trained to. All of this is a quick Google search away.

ProductionReady, huh? Donations accepted! ️✅ X link! ️✅ LinkedIn link! ️✅ Nostr link!️✅ Board member headshots!️✅ Github?


We’re excited to officially announce @ProductionReady, a 501(c)(3) public charity established by @Excellion, @jimmysong, @parkeralewis, and @jratcliff to advance open-source Bitcoin development through education and funding for a new conservative Bitcoin client.



if you keep >0.5 BTC on a wallet in your home, watch this video 👇




@brian_trollz More transparency is needed!


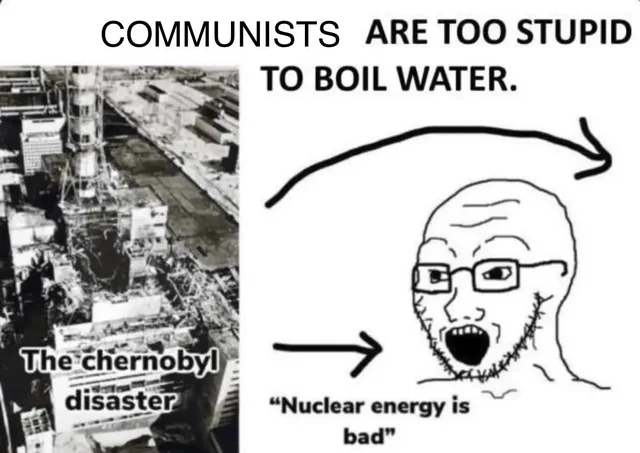
In the entire time the US has had nuclear power, a waste casket has never leaked. Also, we could store thousands of years worth of nuclear waste underground in the Yucca Mountain facility if Obama didn't shut it down for entirely political reasons in 2011.


If you want to get into the semantics battle, sure, but how would you quickly explain it to someone unfamiliar with it? What do you call it? "Non-custodial" is the simplest and quite accurate (if imperfect) label for it that people will understand, and is true except in one edge case (collusion between all Spark Operators and the prior sender). We call Lightning "self-custodial", and yet you can have funds stolen in a plethora of ways, namely: 1. Failing to come online when a fraudulent channel state is broadcast. 2. Not running a watchtower to solve #1 3. Trusting an LSP with JIT channels and making a large payment that gets rugged 4. Flood and loot being used to prevent you from confirming a true state update on-chain Among many other threat vectors. There is always a middle-ground between perfect nuance in every situation, and using a term that gets across 95% of the point and then explaining the trust assumptions whenever you have the chance.