varlock.dev
137 posts

varlock.dev
@varlockdev
Building the future of configuration for humans and non-humans
The internet Katılım Şubat 2024
234 Takip Edilen231 Takipçiler

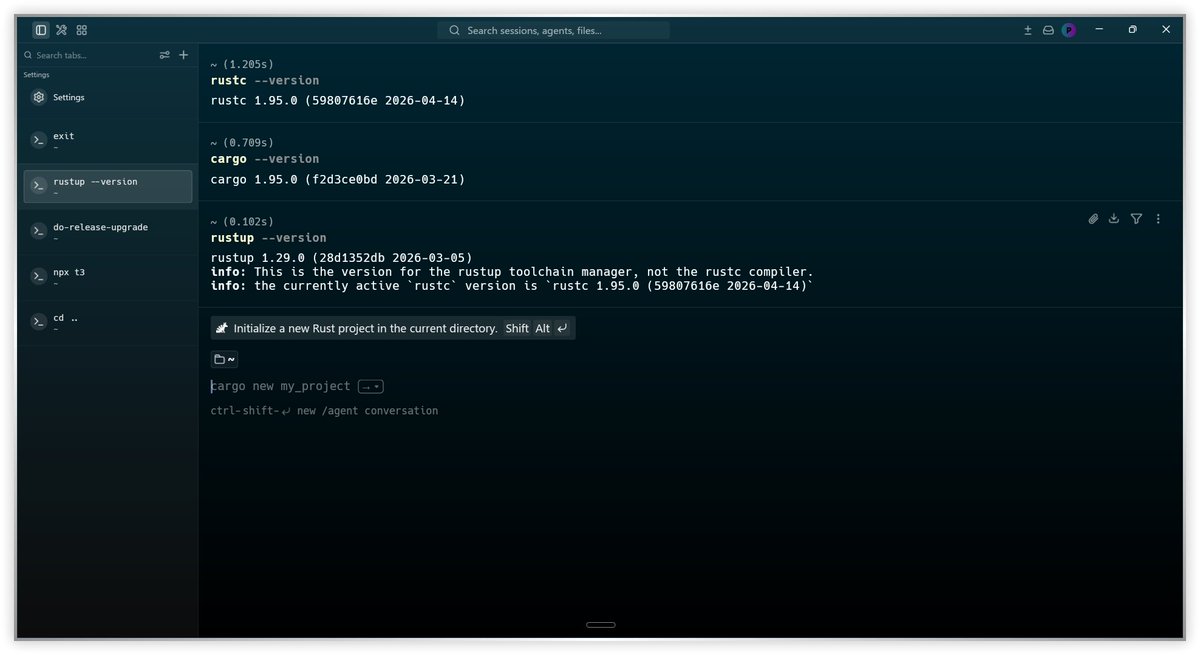
Well I did a thing, and I'm pretty sure @FrancescoCiull4 is going to be pumped about it 🦀
Needed to vibe code a @varlockdev extension for @zeddotdev
And it almost works!!
English
varlock.dev retweetledi

@tambo_ai @InsForge_dev @agentscope_ai #32 Eigent AI ships the open-source cowork desktop for multi-agent productivity, a local and free alternative to cloud-based platforms @Eigent_AI
#31 DMNO builds Varlock, AI-safe .env files with schemas for agents and secrets for humans @varlockdev
English

Thanks for the shout out @SoftwareDefTalk
softwaredefinedtalk.com/571 (~47:00)
English
varlock.dev retweetledi

@DhravyaShah portless, varlock, agent-browser has made dev a lot simpler
English
varlock.dev retweetledi

@theozero @AWS @Azure @googlecloud @HashiCorp @infisical @akeylessio @vercel @github @gitlab @flydotio Understand. Yes varlock made our DX and security way better with worker! Thanks for building
English
varlock.dev retweetledi

Today we launched OIDC workload identity in varlock.
If you are pulling secrets from @AWS|@Azure|@googlecloud|@HashiCorp vault|@infisical|@akeylessio into @vercel|@github|@gitlab|@flydotio|@googlecloud - then you dont need any api keys at all.
varlock.dev/guides/oidc
English
varlock.dev retweetledi

.@varlockdev is amazing. Please run "varlock encrypt --file .env" on your files.
English

I deleted all our .env files from our disc and moved everything to @infisical
Wish I did it sooner. Now...
- Secrets never touch disk
- Secrets auto-shared between developers
- Edit in one place, propagate to prod, GitHub actions, staging env etc
English
varlock.dev retweetledi

@euboid @mickey_bayram @infisical I have been using Varlock recently and pretty happy with it. It has a 1Password integration and many others.
varlock.dev/plugins/1passw…
English
varlock.dev retweetledi
@zodchiii Go varlock + self-hosted Infisical. No excuse for leaving secrets in .env and trusting tool to pinkyswear it's won't look.
Reduces the risk of AI seeing secrets or humans accidentally committing. Not perfect. (runtime agent exposure, centralized attack point) - helps a lot.
English

@cr1msonb0lt @theozero @feross @tannerlinsley @tan_stack we'll take it, if you change your mind we're here 🧙
English

@theozero @feross @tannerlinsley @tan_stack Even though unsolicited promo, and I’m not going to use it, varlock is a sick name!
English

RT @feross: A brand-squatting npm package impersonating TanStack shipped malicious versions that exfiltrate environment variables from developers’ machines during install.
We spoke to @tannerlinsley, creator of @tan_stack, who confirmed that the maintainer of the unscoped tanstack…
English

🇨🇦 I'm *finally* visiting Vancouver in 2 weeks for Web Summit – will be speaking too
Anyone want to meet up and talk coding agents, @modemdev, developer tools, etc?
English
varlock.dev retweetledi

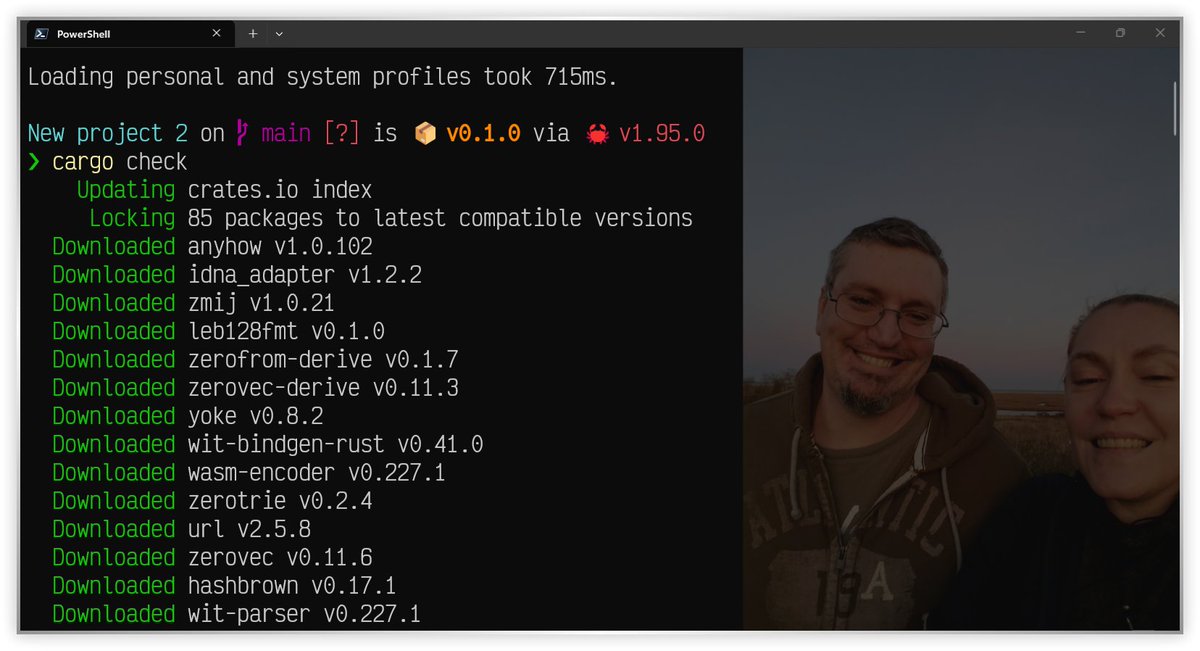
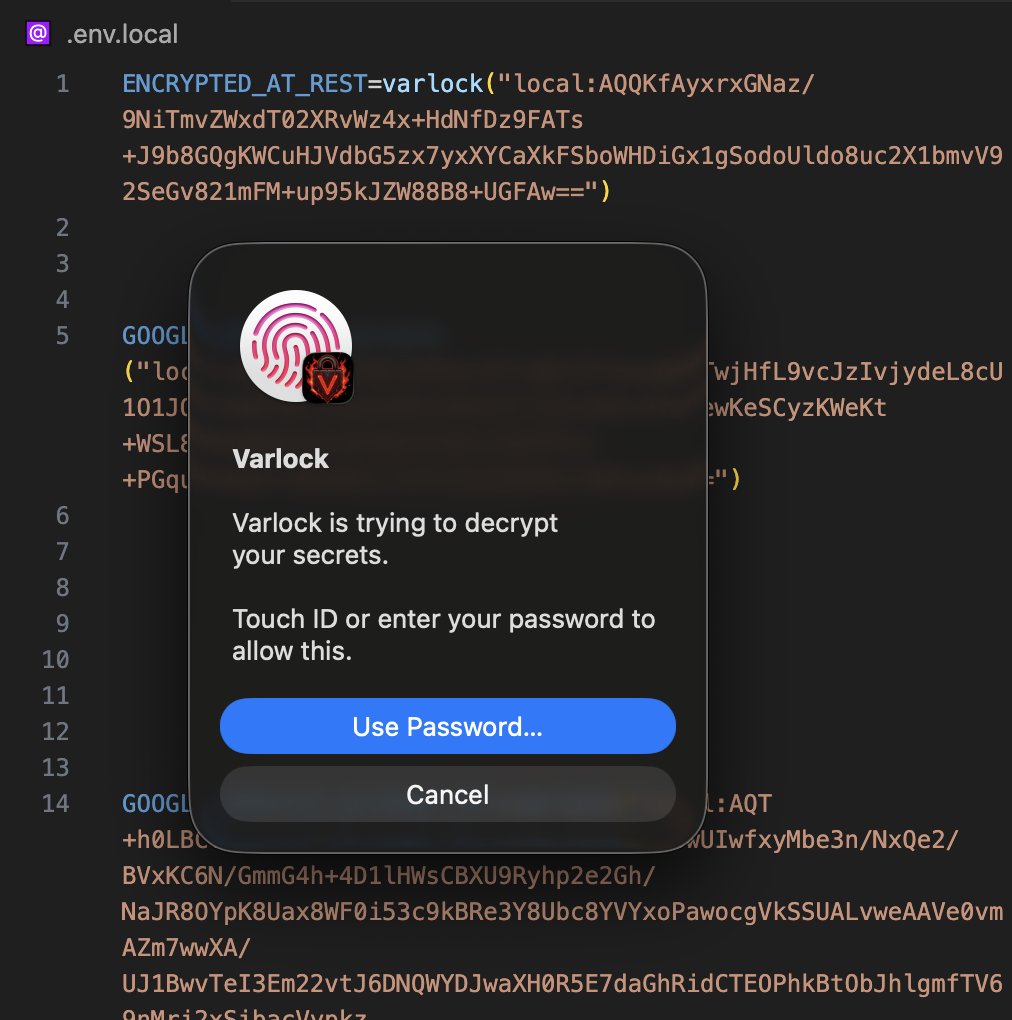
HUGE varlock@v1 update featuring built-in local encryption via native binaries.
No extra setup, and you get native DX to decrypt using biometrics. This is for local git-ignored values, and acts as foundation for future caching + team vaults.
Get EVERY secret out of plaintext!
English
varlock.dev retweetledi

varlock.dev retweetledi

Introducing bumpy 🐸 - a new version/release/changelog tool (carefully crafted slop fork of changesets 🦋)
Fixes 100s of open issues, much simpler, more flexible.
We use it to release @varlockdev and 25+ linked plugins/libs.
bumpy.varlock.dev
English





