Michael Dietz
341 posts


@KLoaec If I understand you correctly, 110 will break this type of miniscript decaying multisig? And this integration test in bitcoin core will fail on 110 code fork github.com/bitcoin/bitcoi…?
English
For context, for the 110 fork people:
Miniscript uses things called fragments. Some of these fragments use op_if, that your fork disables for some reason.
A user defines what their wallet should be, for example "a 2-of-5 multisig". Miniscript will output a Bitcoin Script (a wallet basically) that is the best and safest way currently known to do this policy in Bitcoin.
Disabling an opcode that is very much a building brick for safe Bitcoin wallets is dumb, but also has a big engineering cost on:
- the engineers who build the Miniscript engine
- the devs that implemented it, in Core and in multiple libraries like Rust-Miniscript
- wallet devs
- wallet users who may unknowingly have such a policy.
This cost cannot just be denied or ignored by "there is a 2 weeks window" it'll take a lot more than 2 weeks to do (took 3 years to get Miniscript anywhere), and users may be impacted without knowing so.
Bip 110 is all about virtue signaling and ignoring real costs on the ecosystem, including potential loss of coins for users who did nothing wrong, just used a good wallet software.
English

My understanding is mitigating mining centralization vectors was the reason core loosened mempool policy in first place, but I don't know if I’ve seen it clearly articulated. The strong push (off brand) makes me curious if there are responsibly disclosed vulnerabilities more serious than the obvious one:
- large pool collects non-standard transactions via private channels (eg Slipstream)
-packs block with them causing compact block reconstruction failures on nodes and increasing propagation delay
-uses delay to get head start on next block, extends hidden chain, then releases it (built with standard txns for fast relay), gaining selfish-mining advantage
-boosts pool's profitability and hash power efficiency which creates feedback loop
I haven’t paid close attention to this, have you seen this case made? And do you agree that widely adopted v30 would nip it in the bud?
English

@SaniExp @nunchuk_io I agree! #L5" target="_blank" rel="nofollow noopener">github.com/bitcoin/bitcoi…
English

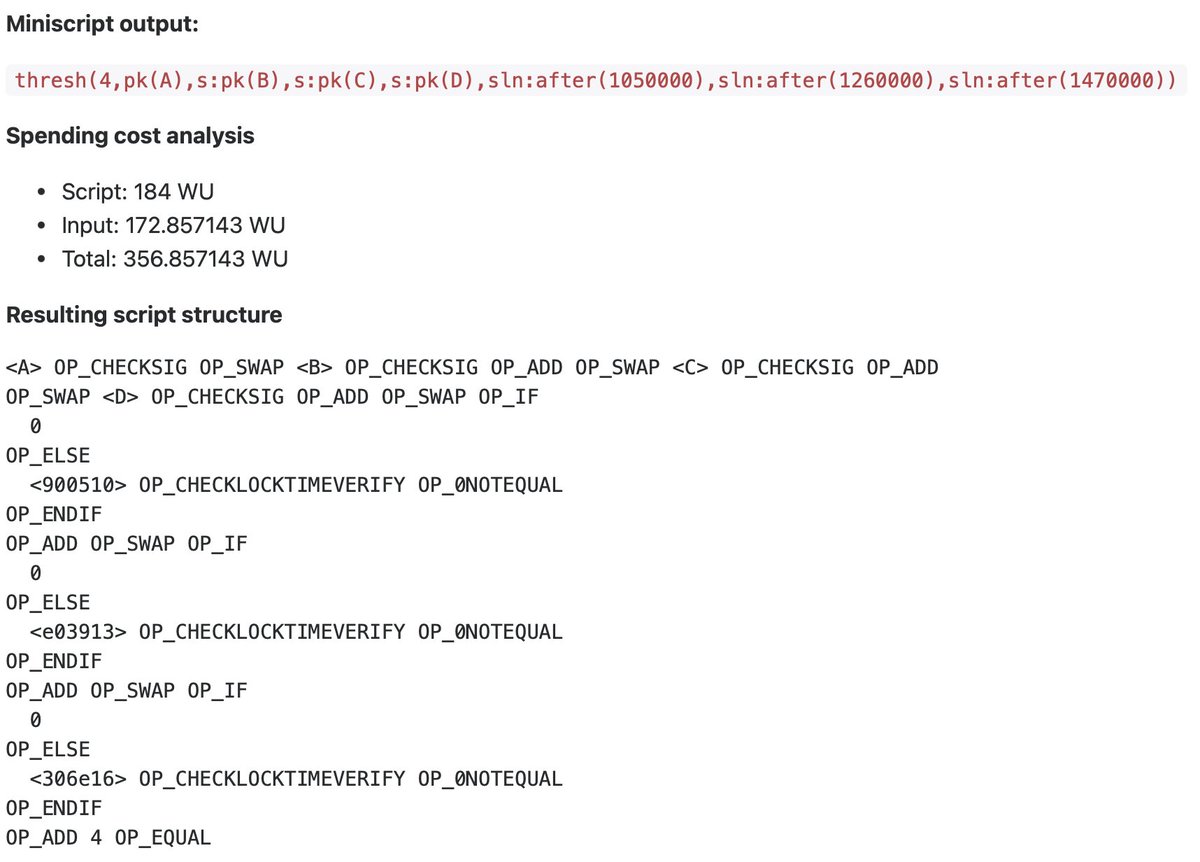
I think this is the optimal setup for individuals:
• 3 out of 4 keys can spend at any time.
• If you lose 2 keys, you can still spend with the remaining 2 keys after 6 months.
• If you lose 3 keys, you can still spend with the last 1 key after 1 year.
Setup can be reduced to 2/3 keys and 1 time-lock.
Miniscript:
thresh(
3, pk(key_1), s:pk(key_2), s:pk(key_3),
s:pk(key_4), sln:older(4224679),
sln:older(4255054)
)
@nunchuk_io your thoughts?

English
Michael Dietz retweetledi
Michael Dietz retweetledi
Michael Dietz retweetledi

We’re proud to share A Bird’s Eye View, our film produced for Bird Buddy by @BBCStoryWorks Commercial Productions as part of The Human Component series.
Bird Buddy started as a smart feeder.
Now it’s a daily ritual for families, a window into nature, and a growing source of insight for conservation.
🎥 Watch the film here: mybirdbuddy.com/bbc/
#TheHumanComponent #BirdBuddy
English

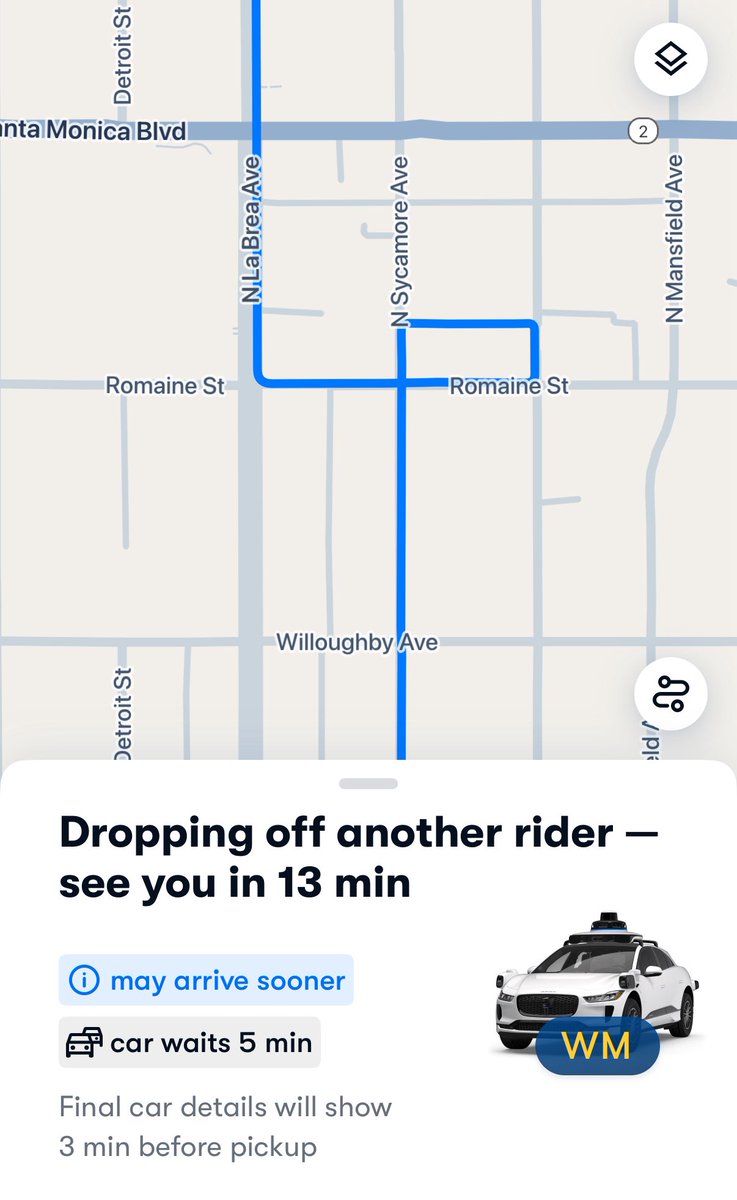
@wholemars It takes rights on red to skip waiting for green to take a left
English

@reardencode @KLoaec @Wizardsardine Surely "proper" vaults can be implemented on Etherium? Why do you think that hasn't that happened (or at least gained traction), and instead whatever "custody solutions" they use get exploited eg $1.5b bybit hack?
English

@KLoaec @Wizardsardine Without consensus enforced reactive security, it doesn't count.
This is like saying "see, nobody wants cars" when people won't buy hand-cranked, open air, wooden tire cars.
Even Purrfect vaults are probably not good enough to earn wide adoption. Maybe CCV or VAULT ones are.
English
It seems a lot of "we need vaults now" on x.
Reminder that @Wizardsardine created Revault, a vault architecture using presigned transactions and watchtowers. No deleted private keys are involved, low risk to deploy.
Nobody cared.
I want vaults too, but seems a lot of noise for no real traction.
Have these businesses even looked at Revault?
English
Michael Dietz retweetledi
Michael Dietz retweetledi

Ready for something Wonderful?
Unveiling on January 7th at @CES . Sign up here to be the first to know. experiencewonder.com
English

I understand this, the core of what I outlined is the bonded btc. As I typed all this out it made me wonder if something like this would have product market fit or be something organization would actually want to adopt. I'm not sure but Lowery's ideas have always been interesting to me this is what I came up with trying to imagine practical applications
English

none of that is made better with Bitcoin. Bitcoin is NOT the only system with threshold signatures. It's not the only system that can require cooperation between parties.
Also, None of this requires PoW. You're conflating signing and key management with PoW.
If you want to require that multiple parties authorize an action, then you do that. We do that today. There are systems deployed in the wild today that require authorization from multiple people (different people, departments, different managers, etc) and check things cryptographically. I've personally worked on several of them. You're using services secured by them right now
None of this requires Bitcoin.
English

Right now we're in a world where "some dev manager" maybe does have the power and ability to send out an OTA update to the entire fleet (and maybe it comes down to a single sig and a trusted server). Which kinda makes Lowery's point. And in the near future think Optimus, Neuralink, etc... I expect this won't cut it for the most critical "control authority" in the near future. The dev manager may coordinate the update and form the transaction, but I expect other entities will need to sign-off in critical cases like these. And the funding of this transaction will not come from the signers (some SIGHASH flag and involvement from another entity to fund)
English

you're not going to have some tesla dev manager have to pony up 1000 BTC. You're going to have a wallet that the firmware team (or whomever) uses to do this transaction.
If an attacker can compromise those keys, then they can either just steal the 1000 BTC, or push malicious firmware with tesla's coins.
So we're back to... you have to protect the keys that are used to publish firmware.
English

The core security improvement you can't get "traditionally" comes from staking a significant bond with this transaction. In this example the device requires a large fraction of Tesla's bitcoin reserves, 1k BTC, to be staked with the transaction to consider the associated OTA package "valid". If a malicious entity gets access to the signing keys they must control enough BTC, which they are forced to sacrifice because Tesla will claim it. For Tesla this is a lossless process. Practically speaking leveraging bitcoin infrastructure and tooling for the signing, multi sigs, financial stakes, etc... is a major benefit because at the end of the day you have devs implementing all of this. Integrating bitcoin core and watching for certain transactions in the device's OTA manager to check a hash is simple, reasonable, and transparent. I'm being brief and leaving a lot of room to fill in gaps (eg custody of Tesla's bitcoin reserves is a different entity than the signers of this transaction even though it funds it)
English

keep pulling on that thread:
> This node watches a multi-sig of defined entities (can include regulator(s) and entities external to Tesla in this example) that must sign and stake a significant bond with the transaction that includes a hash of the update package. Now each device checks the hash of the update package it downloads from the trusted server against the hash included in the transaction (that meets all requirements enforced by device) as an additional layer of security before applying the update
The hash of the update being in a transaction doesn't mean it's valid. It just means that someone made the transaction. If you want to make sure that only tesla, or tesla + the local highway safety board are the only ones that can make that transaction, then you need to protect those signing keys. Because if someone compromises those keys, then they can make the malicious transaction.
So we're right back to: we have to ensure that an attacker can't get the firmware signing keys.
That's already a problem that we have to solve. Attaching a payment to it doesnt change anything.
English

How does Tesla "secure" an over-the-air software update to their fleet of autonomous vehicles? At minimum the update package is signed with a private key and checked by each vehicle before being applied. But if this key leaks and access is gained to server(s) can a malicious update be pushed to the fleet that enables "kamikaze mode" at a specific time for all cars? And in x years when there are millions of Optimus robots among us capable of "defense"? Given nation-state level attackers, are current security practices enough? Now imagine a lightweight bitcoin node runs independently on each device. This node watches a multi-sig of defined entities (can include regulator(s) and entities external to Tesla in this example) that must sign and stake a significant bond with the transaction that includes a hash of the update package. Now each device checks the hash of the update package it downloads from the trusted server against the hash included in the transaction (that meets all requirements enforced by device) as an additional layer of security before applying the update
English

I disagree with your points about the broad application of bitcoin to cybersecurity, but I’m more than happy to be proven wrong!
You should go start a company that uses Bitcoin to do the things you claim it can do. If it really is as broadly applicable as you claim, you should have no problem proving that in the market.
Once you do that, itll be a lot easier to convince DoD that they need a version of it. Hell, you can be their first prime.
English
Michael Dietz retweetledi

Bird Buddy introduced the Smart Bird Feeder.
It lets you experience nature with an AI-powered camera feeder that captures photos of local birds and notifies you of visitors.
@mybirdbuddy features a high-resolution camera, recyclable plastic housing, and weather-resistant design.
You can receive photo postcards on your phone and get real-time alerts.
English
Michael Dietz retweetledi

We got a @mybirdbuddy: a bird feeder that photographs and identifies the locals when they drop by, quietly assembling a compendium of cheery avian mugshots. Strong contender for mantle of "favorite AI product".

English

@rodarmor Who is “they” that’s trying to activate CSV in doge? Seems to me node runners don’t care or want this, and why should they? Not being changed on a whim is a feature not a bug. Of course more centralized alts have no problem changing and upgrading
English
Sometimes I like to check in on the dogecoin GitHub repo. This time I noticed that they're still trying to activate CSV. Think about the fact that coins like Avalanche, Cardano, and Tron are all have a lower market cap than doge, which is struggling to ship upgrades that bitcoin activated in 2016. Cryptocurrency is a joke 😅

English

@alextoussss Woah, that’s amazing! What’s your reasoning for not doing a vision based approach?
English

Update: It works!!!
We’re able to see a 2mm wide plastic ball at 30 centimeters, with only 1/1300th of our planned transmitting power.
This validates our SNR budget and gets us closer to our final goal: tracking and killing mosquitoes at a 3meters range
Alex Toussaint@alextoussss
Currently working on a 3D ultrasonic sonar for mosquito tracking. Prototypes are in the factory right now!
English