Nick Cerny retweetledi

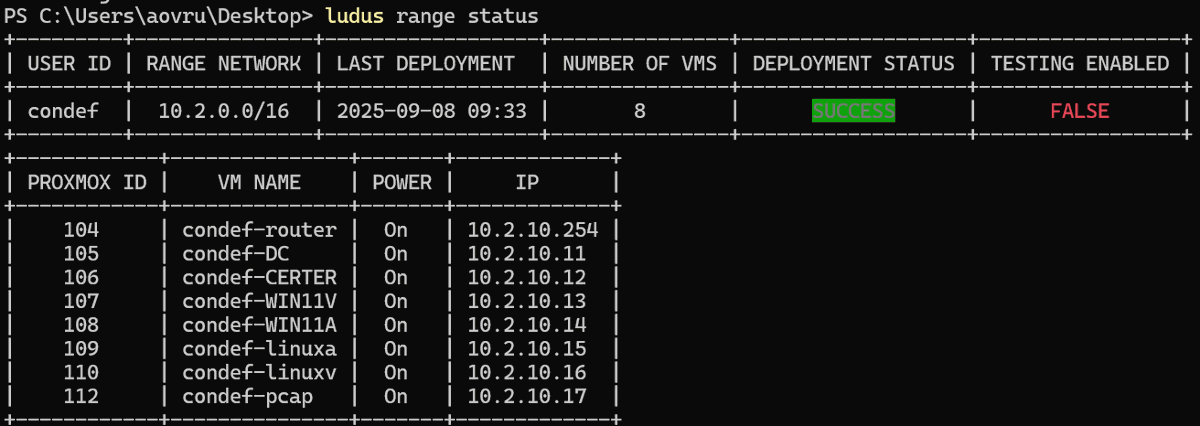
And it's done, coming next week for folks signed up for Constructing Defense - this new Ludus lab build now provisions all of the following:
- AD environment (including ADCS) with custom logging GPO & Sysmon
- Linux auditd configured and setup with Laurel for easier to read logs
- Local Minikube K8s cluster with logging enabled
- All the above telemetry forwarding to a local Splunk instance
- Full PCAP including Zeek logs via Malcolm
All set up with one ludus range deploy command!
Anton@Antonlovesdnb
Been working really hard on this, and it's almost done - fully automated Malcolm deploy via Ludus for Constructing Defense 👀 Coming soon! ™️
English