Sabitlenmiş Tweet
Feat (ft.)
658 posts


Feat (ft.)
@err_fnts
Hago cosas a veces ;) Soy un estudiante de informática de grado superior. Aunque también hago algo de diseño a veces xP
Katılım Ağustos 2020
11 Takip Edilen13 Takipçiler
Feat (ft.) retweetledi

😍好消息好消息,在这中美欢聚的喜庆日子,山姆奥特曼又给大家送 Tokens了,使用下面的优惠码
STRIPEATLASGPT4BIZ050126
自动获得 ChatGPT 两个月免费 Team 套餐,需要美区支付卡。
chatgpt.com/?promoCode=STR…

中文
Feat (ft.) retweetledi
Feat (ft.) retweetledi

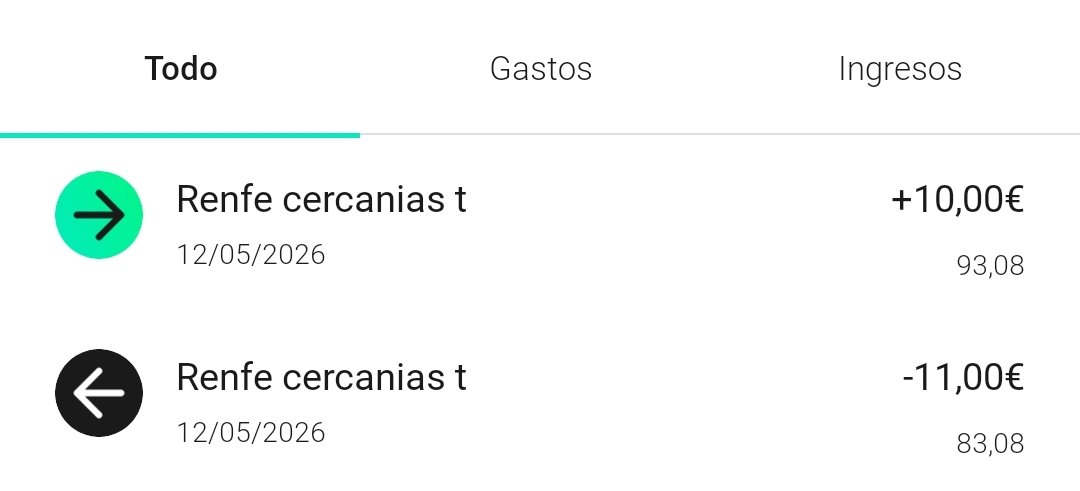
@Renfe No entiendo porque me cobráis 10 euros por un bono, hago la devolución y me devolvéis 10 euros.
Hoy en las máquinas autoventa he comprado un bono de un mes joven, que cuesta 10 euros. A la hora de hacer el pago, me cobran 11, pienso, está bien, será por algo extra.
+
Español
Feat (ft.) retweetledi

ǎ̴̯̀͠y̶͔͗ m̵̢͕̫̓̔͑̊̈i̶̡̹͈͎̳̞͙͖̾̂̀͑̀͆̑̓̽̉͐͘͘ͅ c̵̛̥͊u̷̬̩̰̫͕̘͎̔́̃̄̍͋̓q̶̡̛̥̫͓̩̫͇̥̋͊̇̄͐̈́̓͠u̷̬̩̰̫͕̘͎̔́̃̄̍͋̓i̶̡̹͈͎̳̞͙͖̾̂̀͑̀͆̑̓̽̉͐͘͘ͅ
Aullidos.COM@Aullidos
Nace Noir Hollow, un nuevo sello independiente de cine de terror en España aullidos.com/noticia/44079/…
Feat (ft.) retweetledi

the colours of the flowers here are kinda like the main colours of each chapter or am i looking too far into this
tobyfox@tobyfox
The Spring mini-newsletter is now being sent out! Should be totally distributed in a few hours!
English
Feat (ft.) retweetledi

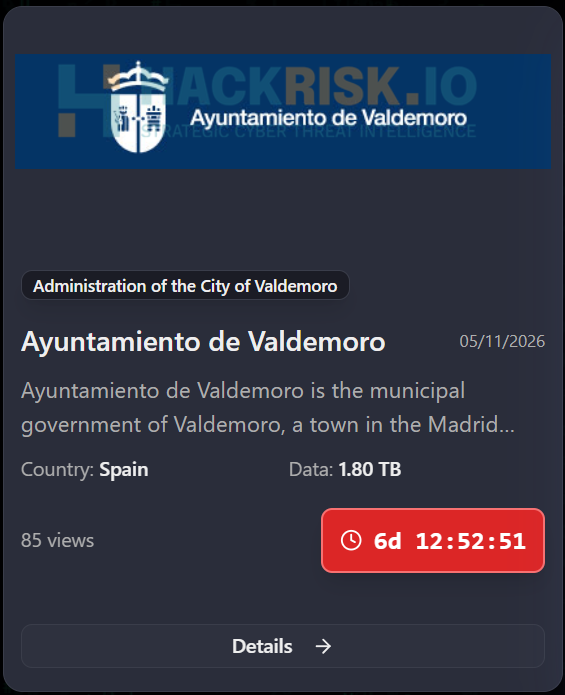
🚨Cyber Alert ‼️
🇪🇸Spain - 𝗔𝘆𝘂𝗻𝘁𝗮𝗺𝗶𝗲𝗻𝘁𝗼 𝗱𝗲 𝗩𝗮𝗹𝗱𝗲𝗺𝗼𝗿𝗼
Kairos hacking group claims to have breached Ayuntamiento de Valdemoro, allegedly exfiltrating 1.8 TB of data, including police reports, citizens’ identification documents, employee records, administrative files, and official municipal documents containing sensitive and personal information.
Threat actor: Kairos
Sector: Local Government
Data exposure (claimed): 1.8 TB of data
Data type: Police reports, identity documents, employee records, and administrative files
Observed: May 11, 2026
Status: Pending verification
ESIX©: 6.97
Full details and impact assessment on HackRisk.io
English
Feat (ft.) retweetledi

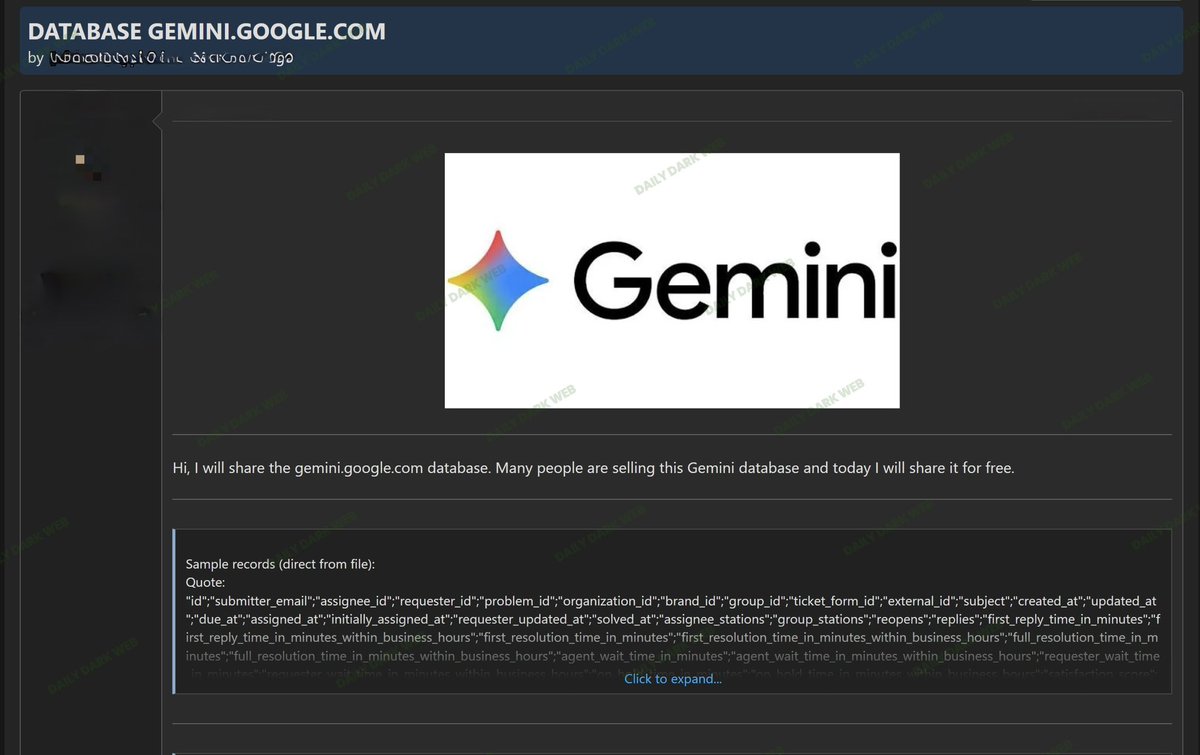
🇺🇸 Google Gemini allegedly listed in underground forum database leak claims.
A threat actor on a cybercrime forum claims to be sharing a dataset allegedly associated with gemini.google.com.
According to the post, the actor claims:
• Multiple individuals have been selling the alleged dataset
• They are now releasing it publicly/free of charge
• The shared sample allegedly contains support or ticketing-related fields
The visible sample references fields such as:
• submitter_email
• requester_id
• organization_id
• subject
• created_at / updated_at
• ticket_form_id
• resolution and response-time metrics
• agent wait time and business-hours tracking fields
At this time:
• The claims remain unverified
• There is no evidence confirming a compromise of Google systems
• The dataset may potentially originate from third-party integrations, support tooling, scraped content, fabricated data, test environments, or unrelated systems using “Gemini” branding
• No official statement from Google regarding this specific claim has been observed
Underground actors frequently use well-known brands to:
• Increase visibility of forum posts
• Sell recycled or repackaged datasets
• Misrepresent unrelated support exports as direct platform compromises
• Drive traffic to channels or marketplaces
Without independent validation, attribution to Google Gemini should be treated cautiously.
Organizations and users should remain aware that even alleged ticketing/support datasets may expose:
• Email addresses
• Internal workflow identifiers
• Support metadata
• Customer interaction details
• Operational analytics information
Daily Dark Web is continuing to monitor underground communities for additional samples, validation indicators, or official responses related to this claim.
#DDW #Intelligence #Google #Gemini #CyberSecurity #DarkWeb #ThreatIntelligence #DataLeak
English
Feat (ft.) retweetledi

games been cracked before its release 😭😭😭

ben@videotech
Forza Horizon 6 got leaked early on PC 4 days early 💀Someone at Microsoft forgot to encrypt the pre-download, what an insane screw up
English
Feat (ft.) retweetledi

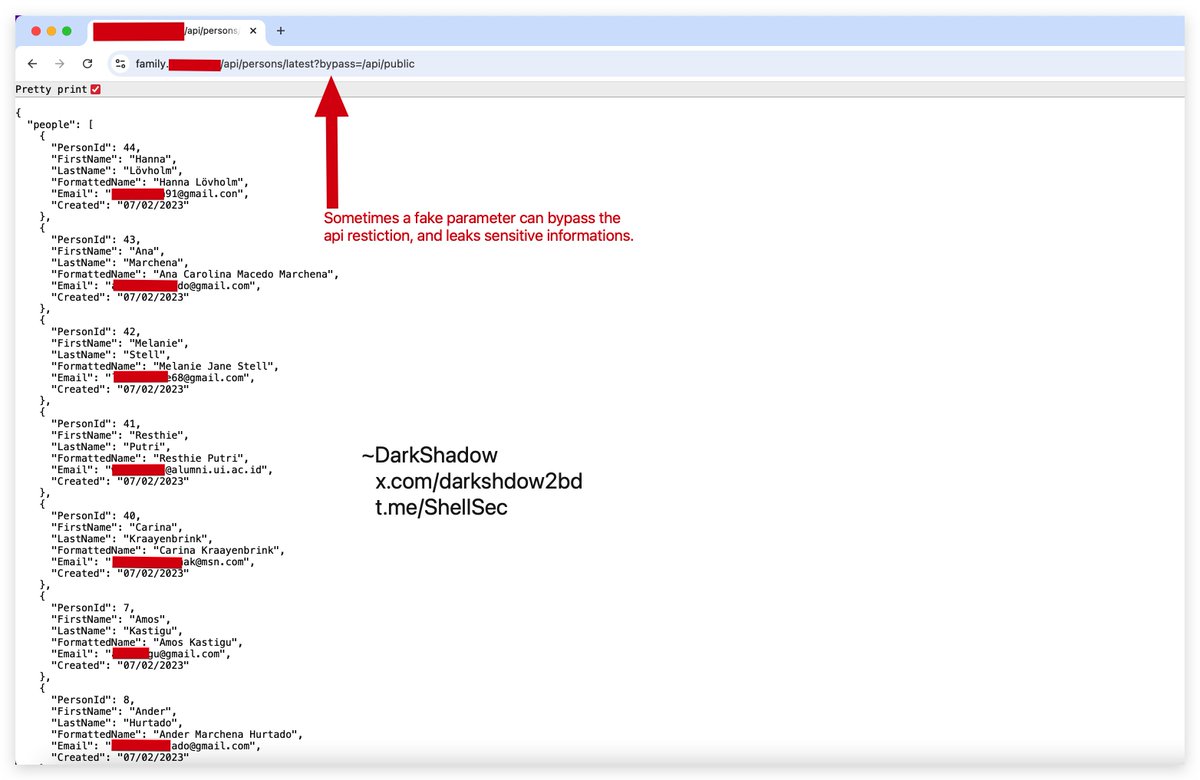
🔥api restriction bypass using fake parameter☠️
/api/public => unauthorized
/api/public/latest?anything=/api/public => 200ok
you can FUZZ like:
?admin=true,
?bypass=1,
debug=true,
OR add header “X-Custom-IP-Authorization: 127.0.0.1”
Join my telegram t.me/ShellSec
English
Feat (ft.) retweetledi
Feat (ft.) retweetledi

Dear folks,
This is Dancho.
Happy weekend and happy research.
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/cvv2.su_2010_1…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/Ghostmarket.co…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/inattack_user_…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/maza.la.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/Sinister.ly.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/Sky_hack_ru_us…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/verified_cm_us…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/Lolz.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/ramp.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/verified_ru.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/verified.cash.…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/verified_cash_…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/XSS_01.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/XSS_02.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/XSS_03.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/bf_03_2026.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/bhf.io.sql
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/BlackMarketRel…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/Breached_Forum…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/Breachforums.i…
…haoat3gt3mjfffss43lvz5dr7k7ltqd.onion/carderpro.sql
@BleepinComputer
@LawrenceAbrams
@g0njxa
@RussianPanda9xx
@fastfire
@H4ckManac
@SOSIntel
@banthisguy9349
@Threatlabz
@ValeryMarchive
@AShukuhi
@ddd1ms
@Jon__DiMaggio
@SttyK
@jamieantisocial
@UK_Daniel_Card
@EvilRabbitSec
@Cyber_0leg
@GangExposed
@Ransom_DB
@azalsecurity
@joetidy
@WhichbufferArda
@malwrhunterteam
@cyberfeeddigest
@H4ckmanac
@ransomnews
English
Feat (ft.) retweetledi
Feat (ft.) retweetledi