ColoradoCassandra
5.9K posts


ColoradoCassandra
@ColoradoCa38720
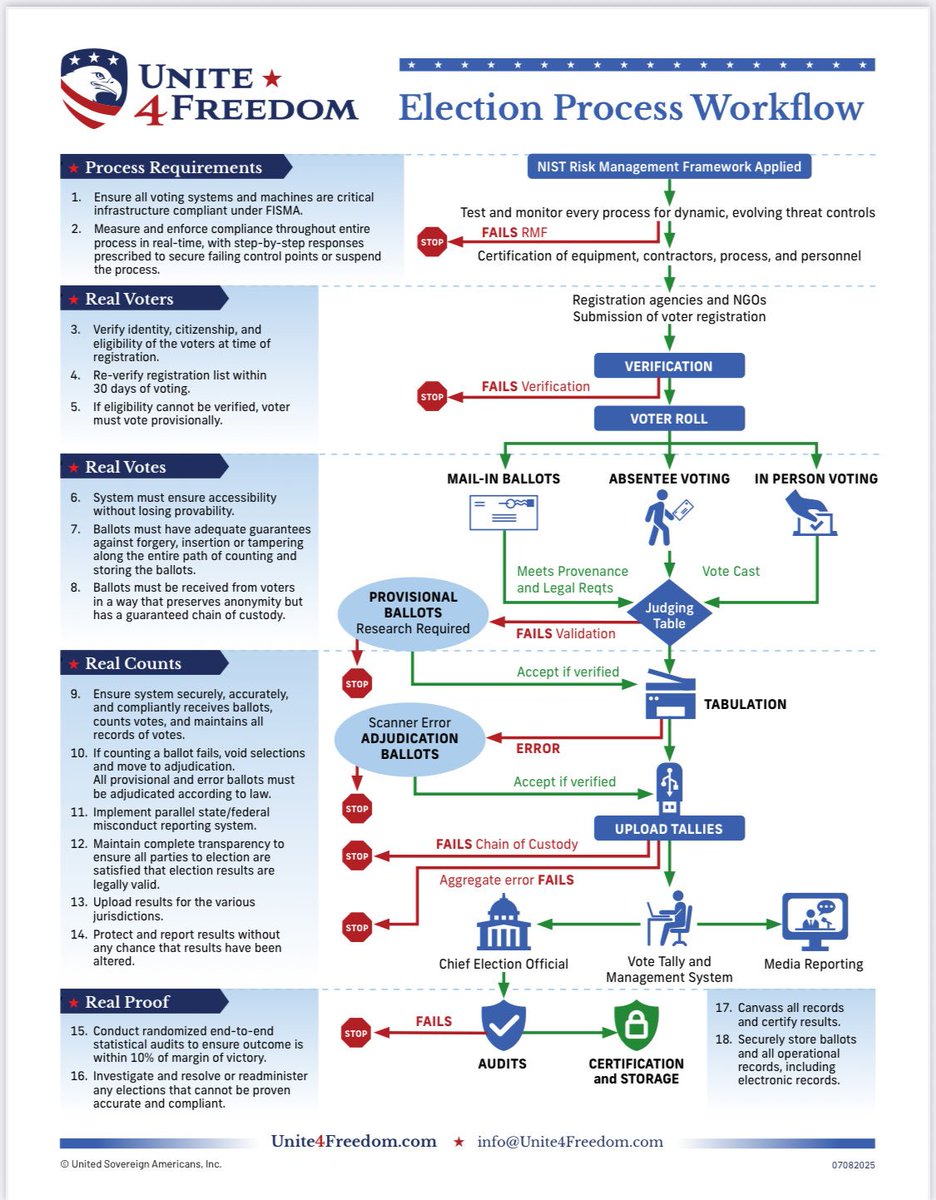
Make elections transparent again! Paper ballots hand counted where cast at the precinct level, one day, ID verified, fully auditable....



🚨 In re Wernick App. for Writ of Mandamus Filing Submitted. This action was made necessary by the determination of former @DallasGOP Chair Allen West to ignore his duty to the Party, and the dedication of @DallasElections Elections Administrator Paul Adams to accept what he knew to be an invalid contract. All we are asking is for Adams to perform his unambiguous duty. But since he's refused thus far, we're asking the court of appeals to order Adams accordingly. @StanMWoodward @wnorred @NorredLaw norredlaw.com/blog/2026/apri…






These are a few. Plus Richer’s wife using 2 different gmail accounts, which I did not put on this list. You’ll have to tap to expand to see the full photo. There are a total of 63 gmail accounts that were “required attendees” on the states United first “all hands on deck” meeting. I have not looked them all up. That’s in addition to the 93 with govt email addresses (from AZ, CA, CN, DE, HI, IA, IL, KY, NV, Maine, MA, MD, MN, OR, RI, VT, WI, DC - see video on other post below) & the 69 listed by name with no email reference.




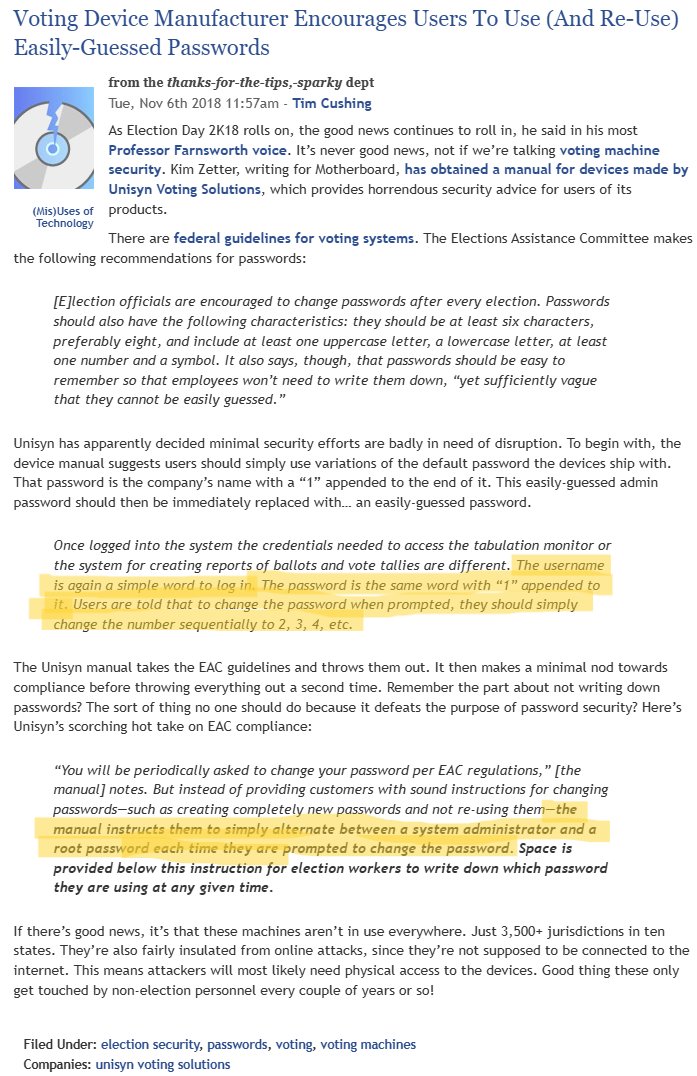
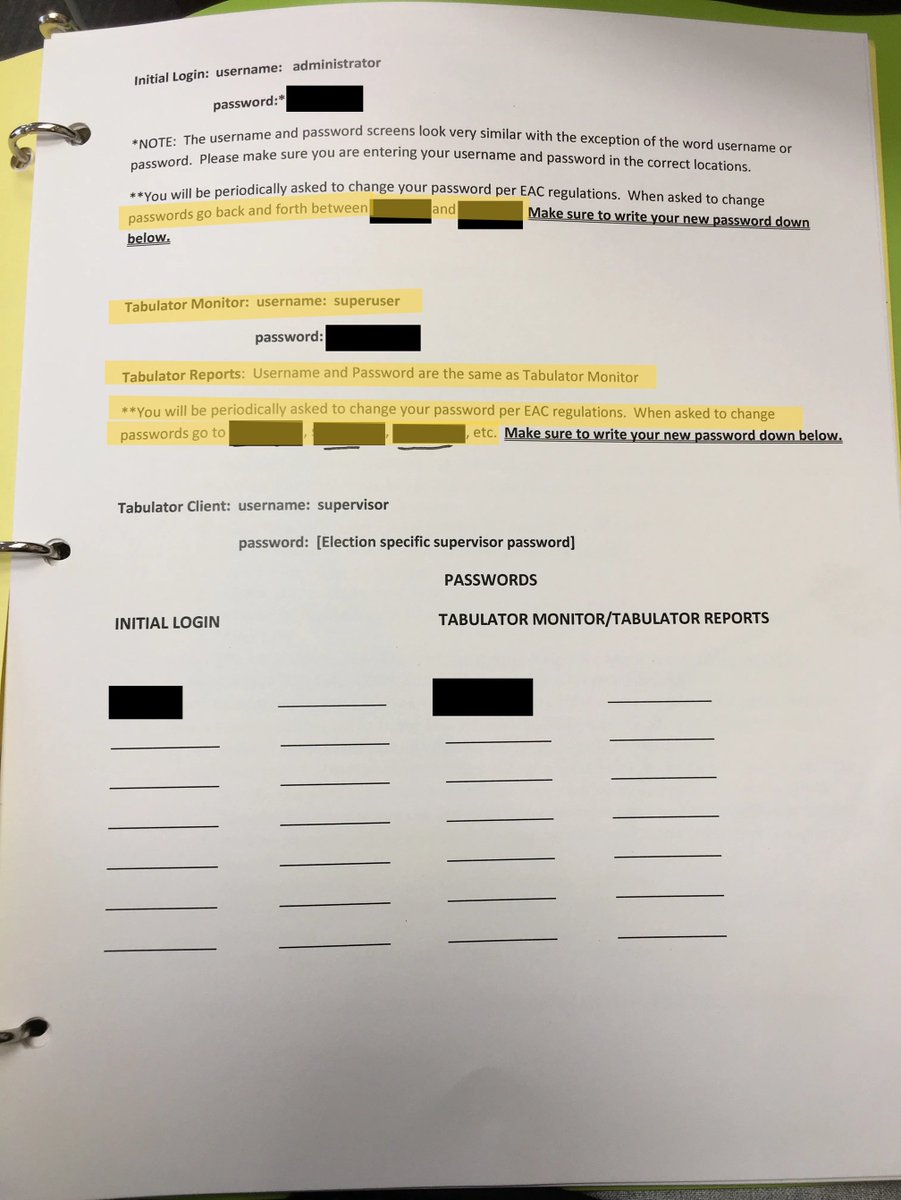
@ZoomWalter @amuse @SidneyPowell1 @KenPaxtonTX @GregAbbott_TX @TXAG @SecJaneNelson @TXsecofstate @Rasmussen_Poll @honestpollster @realJoeHoft @Bannons_WarRoom @EmeraldRobinson @PatriotMarkCook @DrazhaS @ParikhClay @DebbieCanWeTalk @theprofsrecord @MarlyHornik @elonmusk @ColonelReynolds @laralogan Also, my first peek at Hart Intercivic Vanguard 1.0; I read their EAC VSTL test report. I swear to God, it says the VSTL security verification "included consideration of supply chain attacks." This is the EMS motherboard; what "consideration," that it was guaranteed?




Trump tells us every day: the 2020 election was stolen. So why not use military tribunals? It's a major mistake by Trump to treat the COUP as a routine law enforcement matter. It can't be investigated by DOJ/FBI. Why? Because DOJ/FBI was the CENTER OF THE COUP.




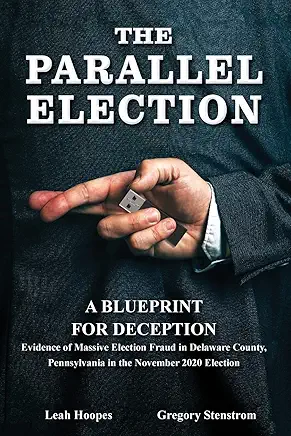
Delaware County, PA election officials CAUGHT on secret video SHREDDING 2020 ELECTION EVIDENCE & plotting a cover-up, with 327K alleged fraudulent votes. - Ripping up voting machine proof/result tapes and tossing them in the trash. - Destroying mail-in ballot envelopes, scanners, hard drives, and other chain-of-custody items required by law. - Planning to fabricate missing certified return sheets, USB V-drives and other records using blank drives to respond to Right-to-Know requests. - Unreconciled votes across dozens of precincts, with claims this hid massive irregularities, lawsuit alleged 327k fraudulent votes in the county. - Explicitly saying “It’s a felony” while discussing getting rid of ballot pads and second scanners — then continuing anyway and shushing talk in front of other staff. - Joking about making a "campfire" to burn the shredded election materials so no one can recover them.

CONCLUSION: Pete Hegseth named the institutions in 37 seconds. The institutions responded with: - Pre-positioned oppo research activated in 72 hours - A regime change planning document citing him by name - A legal predicate for military disobedience published the same week as the Seditious Six video - A pipeline that produced the cohort - A grand jury they couldn't win - A replacement they CAN co-opt - Braver Angels and MWEG sitting at the same table as the color revolution coordinators - A physical barricade at the building where the playbook was written They're not trying to get rid of a bad SecDef. They're trying to remove the one obstacle that makes their entire methodology fail.



This is our sting operation in Delaware County, PA. I was a contributor to Project Veritas after I reached out to them directly. I was working directly with Spencer Meads. This operation was developed by Gregory Stenstrom, Leah Hoopes and we brought in the whistleblower directing her at every point. FORMAL POSITION STATEMENT The issue is being deliberately mischaracterized. This is not about recognition, ego, or attribution in the colloquial sense. This is about evidentiary integrity and credibility of source material. Where individuals with first-hand knowledge and direct involvement in the development of evidence are omitted, misidentified, or dismissed, the consequences are not superficial they are fatal to the reliability of the record. 1. Authorship establishes foundation. Evidence does not exist in a vacuum. It must be tied to a competent witness or originating party who can authenticate its creation, methodology, and accuracy. 2. Misattribution undermines admissibility. When third parties republish, summarize, or distort investigative findings without proper identification of the original source, they sever the evidentiary chain. That is not a social slight—it is a legal defect. 3. This is not “credit”—it is chain of custody. Labeling originators as “seeking attention” is a deliberate tactic used to avoid engaging with the substance of the evidence. It reframes a structural legal requirement as a personality flaw. That argument is frivolous and should be rejected outright. 4. Anger is not disqualifying—it is contextual. When individuals invest substantial time, resources, and risk exposure to develop evidence of serious wrongdoing, objection to its misuse or misrepresentation is not “jealousy.” It is a rational response to the degradation of the evidentiary record. 5. Unauthorized use creates liability. Any party leveraging investigative work while stripping attribution or altering context assumes risk, including: Misrepresentation of facts Inability to authenticate evidence Exposure in any proceeding where foundation is challenged. CONCLUSION The position is simple: If you intend to use the work, you identify the source. If you cannot identify the source, you cannot validate the evidence. If you cannot validate the evidence, it collapses. Attempts to reduce this to personality attacks or accusations of ego are not only irrelevant—they are indicative of a lack of substantive rebuttal. If you strip out the people who developed it, you destroy the chain of custody and the ability to prove it. Labeling that concern as “jealousy” is a deflection tactic used by people who don’t want to deal with the facts. You don’t get to use the work and erase the source. I have been blocked by Patrick Byrne—an individual who has used evidence developed through our work, obtained through our former attorney Stefanie Lambert, and then leveraged that material to raise money. That is not advocacy. That is exploitation. Stop reframing this as an issue of “credit.” That characterization is false and it is being used to dismiss a far more serious problem. This conduct: Misappropriates investigative work developed through substantial time, risk, and resources Breaks the chain of custody of critical evidence Distorts underlying facts, including timelines, participants, and third-party involvement Places the original investigators at risk while removing their ability to authenticate the record Those are not minor issues. Those are defects that can destroy the evidentiary value of the work entirely. And yet, the public is being told this is acceptable—as long as the information “gets out.” No. That standard is reckless. Evidence that cannot be properly sourced, verified, and authenticated is compromised. Once compromised, it is vulnerable to attack, dismissal, and exclusion. That does not advance any cause—it undermines it. Being told to “eat crow for the sake of the movement” is not strategy. It is complicity in misconduct. My standard is not negotiable: If you use the work, you identify the source. If you alter the facts, you disclose it. If you raise money on the back of that work, you answer for it. Anything less is dishonest and corrosive to the integrity of the record. If anyone believes this conduct is defensible, then take the position publicly. I am inviting an open, public discussion on the record.