Warden 🛡️ | Protecting Your Crypto Systems
2K posts


Warden 🛡️ | Protecting Your Crypto Systems
@Warden_Secure
Warden: 100% Auto-Contain Cybersecurity ⚡ Stopping all known/unknown Malware Threats Instantly. Before they can Steal Your Bag! Focus here is Crypto Security




⚓️🇫🇷 FLASH - Le porte-avions français Charles de Gaulle a été localisé par des journalistes du Monde grâce à… l'application de sport Strava d'un officier qui fait son jogging sur le pont du navire.


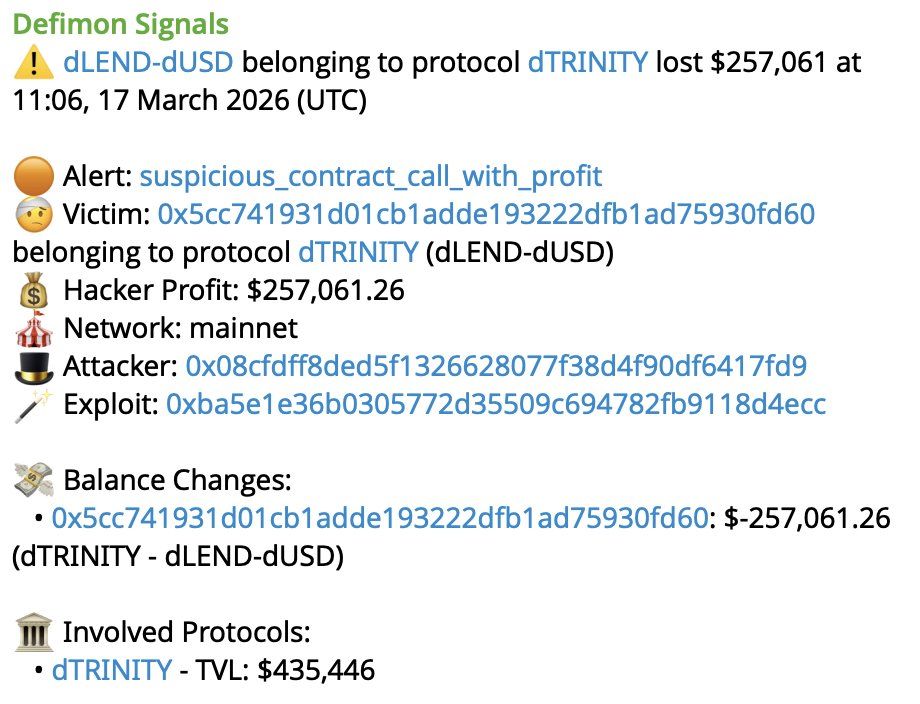
Approval phishing is one of the most common ways crypto wallets get drained. The UK's National Crime Agency just named revoking wallet permissions as a key defence in their Operation ATLANTIC fraud guidance. Check yours today at revoke.cash.


Next on the Rekt Security Stage: @LewellenMichael Head of Solutions Engineering, @turnkeyhq. The attack surface has moved to the signature layer. He'll be on the panel examining exactly how.





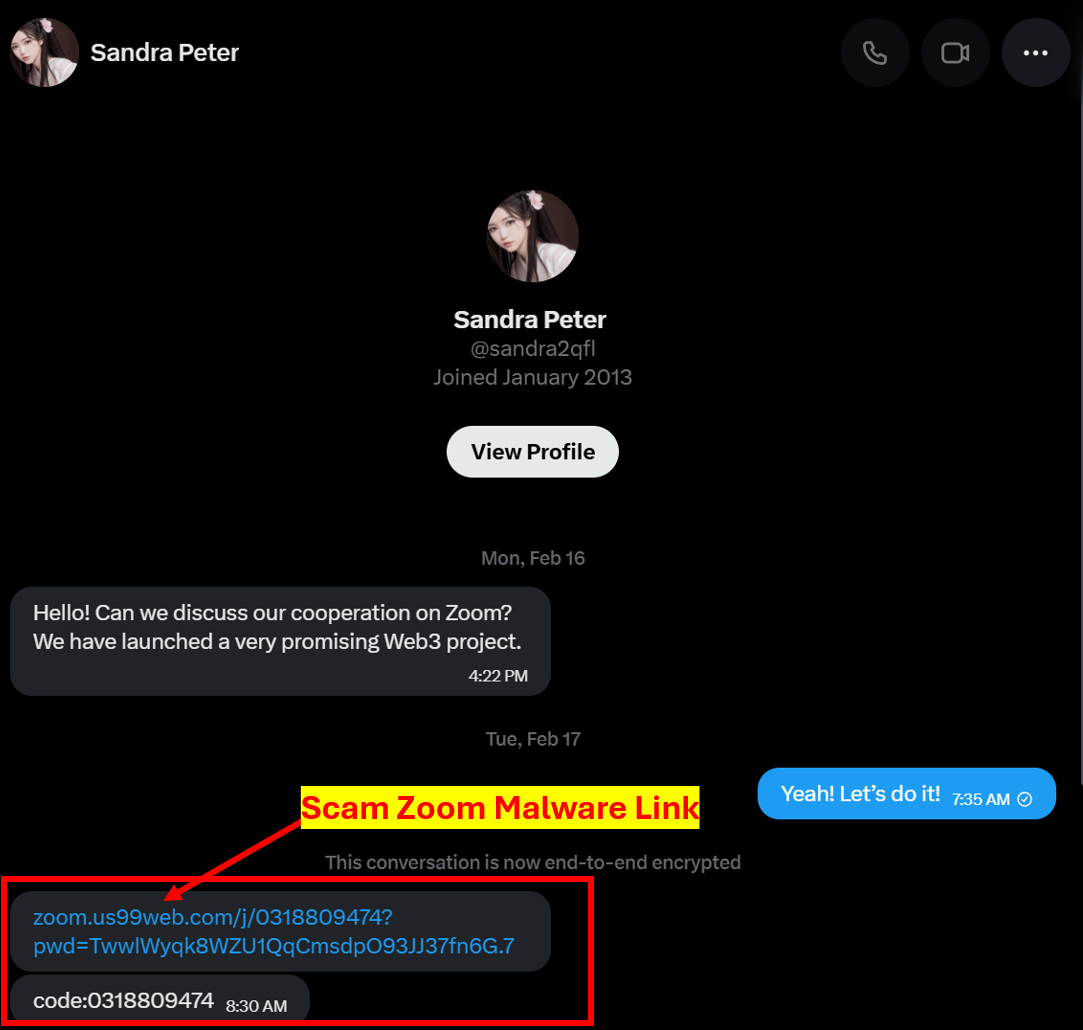
Magic Eden Shutting Down Support: What does this mean for you? With @MagicEden shutting down support for all NFTs except SOL and discontinuing their wallet, there are steps EVERYONE should take ASAP, Let’s review them below ⤵️ 1/ EVM Marketplace and Approvals 2/ Magic Eden Wallet 3/ Stay Safe from Scams



CatalystOG 🤝 Upshot Prediction culture just got an upgrade. @upshot_cards mixes prediction markets with TCG-style pack openings. High-stakes cards. Internet narratives. Fire art. Through our partnership, Split Decision is now making predictions in style. Episode 7 is live now on YouTube.







AI is making CEOs delusional

✅Most people securing AI agents are protecting Human → Agent prompts. But the real problem starts when agents start spawning agents. 1⃣ to many (🔟+) Now the threat model becomes: Agent → Agent (A2A) A compromised sub-agent inside a swarm can: ✅ escalate privileges ✅ poison memory ✅ impersonate peers ✅ exfiltrate orchestrator data So this is how we frame sub-agent defense today: 1️⃣ Hard privilege boundaries Sub-agents spawn with fixed authority (leaf vs orchestrator) They cannot restore sessions or escalate roles later. 2️⃣ Strict context isolation Child agents cannot inspect parent session metadata or override workspace policies. 3️⃣ Spawn integrity controls Agent IDs validated at creation → prevents ghost agents / fake sessions. 4️⃣ Treat A2A as hostile input Agent messages get the same injection filtering as human prompts. 5️⃣ Privilege-separated architecture Strategic orchestrator = private data External tactical agents = no filesystem access 6️⃣ Swarm anomaly detection Watch for: • abnormal A2A traffic • API spikes • rogue agent behaviors 7️⃣ Mandatory A2A red-teaming We regularly run sub-agent impersonation exercises. Where we think this goes next: • agent trust graphs • quorum memory writes • collective alignment scoring • swarm cascade containment But I’m convinced we’re still missing pieces. If you’re running multi-agent systems or agent swarms: What are you doing for sub-agent security that isn’t on this list?


🚨 Released: The AI SAFE² × SlowMist Security Overlay for OpenClaw! Academic tests show OpenClaw’s native defense rate against sandbox escapes is only 17%. To fix this, we merged the @SlowMist_Team Practice Guide (v2.7) with the AI SAFE² Framework. Neither framework alone is sufficient. Together, they build a 3-layer unified architecture: 🧠 Cognitive Layer: SlowMist Red/Yellow lines + AI SAFE² Memory Vaccine. 🌐 API Gateway: Real-time risk scoring & circuit breakers via Control Gateway. 🏢 Org Layer: 13-metric audits + Vulnerability Scanner for fleet visibility. Stop managing an AI and start governing a digital workforce. Check out the step-by-step deployment runbook and threat models in the /examples/slowmist-overlay/ directory today!